
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
Loading...
A quick guide on getting started with Authgear
Authgear makes it easy to add user authentication and authorization to any application. In this guide, we'll show you how to get started with Authgear in 5 minutes.
To start using Authgear in your application, create a free Authgear account on .
After you sign up, you'll see the onboarding screen that will guide you through the process of creating your first Authgear project.
An Authgear project is similar to a container that holds all your users, settings, and client applications. You need an Authgear project before you can start signing users up.
You can create multiple projects under one account based on your needs. When you create multiple projects, each project is isolated from the others. For example, you can create Project 1 for your e-commerce business and Project 2 for a fitness club you organize. Project 1 and Project 2 will not share the same users or settings.
To create an additional project, log in to your Authgear account then click on the "Create Project" button.
Now that you have created a project in Authgear, you're ready to integrate Authgear into your applications for your customers/users to sign up and log in. See our documentation for adding Authgear to your application or website for your favourite framework and programming language.
Before any integration, you can try out the signup flow for your project from the "Getting Started" page.
You should be greeted with the AuthUI Login/Sign-up page. Use the form to create a new user account under your project.
After logging in from the previous step, you can check out the Pre-Built User Settings Page. This page is the default page where users of your project can edit their profile and manage security settings.
Click on the Edit Profile to edit and view profile attributes such as first name, last name, photo, etc.
Users can manage the identities (email address, phone number, or social media account) linked to their account under the My Account section of the User Settings page.
The Security section of the User Settings page has the following options:
Password: users can change their password from here.
2-step verification: users can click on this option to view and manage 2-step authenticators for their account. The option is only available when you enable 2FA for your project in Authgear Portal > Authentication > 2FA.
Signed-in device: from this page, the user can view browsers and devices that their account is currently signed in on.
You can learn more about the User Settings page .
To get more from Authgear and use Authgear to add user authentication to your web or mobile application, you should integrate Authgear to your application or website.
Authgear has official SDKs for integrating Authgear with React, React Native, ionic, Native Android, iOS, and Flutter applications. See the section of Authgear documentation for detailed instructions for each SDK and using other frameworks without the official SDK.
Authgear offers multiple options for viewing and managing all users who sign up for your project. These options include:
Authgear Portal
The quickest way to manage your users is from the Authgear Portal. To open the user management page in the Authgear Portal, click on the User Management link in the navigation bar on the left side.
Click on Users to view a list of all the users in your project. Click on a user from the list to view their complete profile and perform administrative operations like modify profile details, suspend/unsuspend user, delete account, etc.
You can also add new users to your project from the User Management page. To do that, click on the Create User button on the right.
Continue to navigate around the Authgear Portal to see all the features and settings available for your project.
You can also check out any of the following guides to learn more about Authgear:
login and sign-up page to match your branding needs using the Design tool
guides on how to .
how to .
Choose the integration approach based on application type
There are 3 different high-level approaches to integrating Authgear with your applications:
Mobile apps or single-page web applications: The frontend clients integrate with Authgear's SDKs, which handle full login flow and session management. It's important to validate the session in your backend server.
You need to protect a JavaScript SPA application that runs entirely in a browser





Regular Web Applications: Traditional server-side rendered web apps that run on the server can use OIDC protocol to authenticate with Authgear. The application server has full control over the session storage.
Software built by others: Integrate with other OIDC/SAML compatible applications like WordPress, Salesforce for Single Sign-On.
Client-side SDKs are designed for developers to quickly implement authentication with Auth UI on your web and mobile applications. After login, it returns the user data for your apps. It can open a hosted pre-built account settings page for the user to manage their own account. The SDKs manage session token storage automatically and have built-in token ownership protection (DPoP) against stolen refresh tokens.
Check out the following guides for your specific framework:
After the frontend integration is complete, every request sent from your application to the backend server should include the Authgear session in its header. JWKS should be used to validate the requests and decode user information from the JWT access token. See Validate JWT in your application server for details and code examples.
You can customize the look and feel of Authgear prebuilt UI to match your branding. Events and hooks can be used to stay notified and add functionality during the authentication process.
The Authgear Admin API enables comprehensive user management via a GraphQL endpoint for your backend server. The server can perform operations including searching for users, updating user details, deleting user accounts, and disabling user access.
For detailed implementation instructions and API capabilities, refer to the Admin API guide.
If you wish to use a custom UI instead of the pre-built UI for signup and login, you need to deploy another server and complete the signup/login process using Authentication Flow API. See Custom UI for in-depth instructions.
If your application is a traditional web app running on a server, you can leverage the OpenID Connect (OIDC) protocol to authenticate users via Authgear. A wide range of plug-and-play libraries can be found that simplify the integration process. These libraries handle crucial tasks such as authentication requests, session management, and redirecting users back to your application seamlessly.
See the following tutorials for your specific application framework:
You can customize the look and feel of Authgear prebuilt UI to match your branding. Events and hooks can be used to stay notified and add functionality during the authentication process.
The Authgear Admin API enables comprehensive user management via a GraphQL endpoint for your server. The server can perform operations including searching for users, updating user details, deleting user accounts, and disabling user access.
For detailed implementation instructions and API capabilities, refer to the Admin API guide.
If you wish to use a custom UI instead of the pre-built UI for signup and login, you need to deploy another server and complete the signup/login process using Authentication Flow API. See Custom UI for in-depth instructions.
When implementing identity management for your enterprise software, Authgear provides robust single sign-on (SSO) capabilities that seamlessly connect your workforce. Enterprise applications typically support standard authentication protocols like OpenID Connect (OIDC) and Security Assertion Markup Language (SAML)
Provide a seamless user experience across multiple applications with the single sign-on feature.
Single sign-on (SSO) is defined as login once, logged in all apps. If you have multiple mobile apps or websites that wants to streamline the user experiences. You can configure your apps to turn on the SSO feature, so the end-users only have to enter their authentication credentials once.
There are multiple ways to achieve Single Sign-on, with various pros-and-cons:
How to pass the Apple Store review process if your app uses passwordless login.
When you try to publish a mobile app on the Apple AppStore, there will be an . You need provide a demo user account for the reviewers to access the features of the app.
However, passwordless login via email/phone OTP cannot be used in the review because the reviewer do not have access to the email inbox or phone number of that demo account.
To work around this, you can enable "test mode" for a specific phone number or email address that allows the account to authenticate with a fixed OTP (e.g. 000000).
By default, only the sub field of the UserInfo is included in the SAML assertion. To include other fields like users' email address, phone number, etc., you can set up SAML Attribute Mapping for the fields.
SAML Attribute Mapping allows you to configure your Authgear client application to include additional fields in the SAML assertion. This is a great way to pass additional data from Authgear to your SAML application that depends on Authgear as an Identity Provider.
Authgear supports using SAML attribute mapping to include additional fields in the SAML assertion using any field in the user profile attributes (UserInfo).
There's also support for a template that can be used to customize the values of the fields before including them in the SAML assertion. For example, the template {{.preferred_username}}@example.com will return the preferred_username field from the UserInfo prepended to '@example.com'.
Force Authgear to always show login page even if the user have already logged in.
When user login / signup to Authgear, it usually starts with your application making a request to the authorization endpoint, which leads to a login or signup screen.
If the user is already signed in on the browser, the Single Sign On feature will show a "Continue Screen" instead as follows.
If your application do not want to utilize the Single Sign On feature, and always show the login / sign up screen instead, you can force Authgear to show login page by using prompt="login" at the authorize endpoint.
For many business applications, it's important to restrict who can register for your platform. By disabling public signups in Authgear, you can ensure that new users are only added through your internal processes, such as the Admin API or the Authgear Portal.
Disable public signup if you want to:
Control user access and approval for your application.
Use the Phone Number Validation Settings to configure your app to check the phone number your users enter without depending on SMS or WhatsApp for validation and verification.
Under the hood, the Phone Number Validation Settings uses the library. The library can parse, format, and validate phone numbers for all countries/regions in the world.
To access Phone Number Validation settings in your Authgear project, navigate to Authentication > Login Methods in the Authgear Portal.
Next, select a login method that uses mobile phone number as login ID (e.g., Mobile, Mobile/Email, or Custom with phone number enabled as login ID). Then, scroll down to the Phone Number Validation section. Select validate phone number with libphonenumber or validate only the country code and phone number length.
Learn how to integrate Authgear with mobile apps using SDKs and advanced configurations
This section covers mobile-specific integration patterns and configurations for Authgear.
Note: The phone number validation logic may become outdated due to recent changes in the numbering style in certain countries/regions. In such a case, you can disable the Phone Number Validation feature to enable users to register new numbers that the logic is unable to recognize.

Implement Authgear to control access to your applications
Authgear simplifies the use of open industry standards like OAuth 2.0, and OIDC. Users can log into your applications with a variety of user login options. This set of how-to guides provides you with detailed instructions, code snippets, and configuration examples for each type of login method.
The prompt="login" parameter which is defined in the OIDC spec can force AuthUI to show the login page. Authgear SDKs have a prompt parameter that can be used to set prompt="login". Once the prompt parameter is set to login Authgear will always show the login screen when your application calls the SDK's authenticate method.
The following code shows how to set prompt: "login" in Authgear SDKs:

Provision users only via admin tools.
Prevent the general public from self-registering.
To turn off public registration:
Navigate to Portal > Advanced > Edit Config.
Find or add the following configuration in your YAML file:
authentication:
public_signup_disabled: true
# other configurations...Save your changes
Navigate to Advanced > Edit Config
paste the following to the yaml:
In this example,
+85291231234 and [email protected] will not recieve any messages.
They can log in using the fixed OTP 000000.
All other users will continue to receive OTPs normally.
test_mode:
oob_otp:
enabled: true
rules:
- fixed_code: "000000"
regex: (\+85291231234$|me@example\.com$)
sms:
enabled: true
rules:
- suppressed: true
regex: \+85291231234$
whatsapp:
enabled: true
rules:
- suppressed: true
regex: \+85291231234$
email:
enabled: true
rules:
- suppressed: true
regex: me@example\.com$To enable SAML Attribute Mapping for your Authgear project, please contact support.
The above example creates three SAML attributes (family_name, given_name, placeholder_email) that will be added to the SAML assertion.
The value for pointer refers to a user profile attribute in the UserInfo object.
From an attribute that uses a template, the value in between the {{}} also refers to a user profile attribute in the UserInfo object.\
attributes:
definitions:
- name: family_name
- name: given_name
- name: placeholder_email
mappings:
- from:
user_profile:
pointer: /given_name
to:
saml_attribute: given_name
- from:
user_profile:
pointer: /family_name
to:
saml_attribute: family_name
- from:
text_template:
template: '{{.preferred_username}}@example.com'
to:
saml_attribute: placeholder_emailauthgear
.startAuthentication({
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: PromptOption.Login,
})authgear
.authenticate({
redirectURI: 'com.reactnativeauth://host/path',
prompt: PromptOption.Login,
})AuthenticateOptions options = new AuthenticateOptions("<AUTHGEAR_REDIRECT_URI>");
List<PromptOption> promptOptions = Arrays.asList(PromptOption.LOGIN);
options.setPrompt(promptOptions);
mAuthgear.authenticate(options, new OnAuthenticateListener() {
@Override
public void onAuthenticated(@Nullable UserInfo userInfo) {
}
@Override
public void onAuthenticationFailed(@NonNull Throwable throwable) {
Log.d(TAG, throwable.toString());
}
});authgear?.authenticate(
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: "login"
)_authgear.authenticate(
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: "login",
);

SSO between two independent mobile apps
Based on OIDC App2App
SSO from a Mobile App to Website
Open a URL from Mobile App and pass the user session along, based on OIDC Token Exchange
SSO between Mobile Apps from the same publisher
Keychain Sharing / Android Account Manager ( if you need it)
Requires both apps published by the same publisher from App Store.
SSO between Websites with the same apex domain
Requires all of the websites with the same "root domain" (e.g. app1.example.com and app2.example.com)
SSO between Mobile Apps and Browsers
Requires the use of ASWebAuthentication and Custom Tab on iOS/Android respectively
Sign in Microsoft Azure.
Create a B2C tenant by following this tutorial.
Enable self-service sign-up for the tenant by following
Go back the main page of and search for "Azure AD B2C"
Create a app registration for Authgear by following .
Configure "Redirect URI" with https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/azureadb2c.
Follow to create a sign-up and sign-in user flow.
After creating the user flow, configure it
Open "Application Claims".
Make sure "Email Addresses" is checked.
If you have finished the above prerequisite, you should have the following information:
The Tenant Name, obtained in Step 2
The Application (Client) ID, obtained in Step 5
The Policy (User flow) Name, obtained in Step 7
Then in Authgear portal, do the following:
In the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with Microsoft Azure AD B2C.
Fill in Client ID with the Application (Client) ID above.
🎉 Done! You have just added Azure AD B2C Login to your apps!
Azure AD B2C automatically logs in to the same account without requiring a username and password. To prevent this behaviour, you can use the prompt=login parameter to force Azure AD B2C to show the login page. See our in Authgear SDKs to learn more.
Configure password reset/account recovery processes.
The Forgot/Reset Password settings tab allows you to configure the behaviour of the account recovery process for your Authgear project.
Select a login method and navigate to the password settings tab. The login method chosen controls how the user can reset their password:
Phone (OTP only)
Email (link or OTP)
Both
If both options are available, the user will be able to choose between using phone or email for account recovery.
You can choose how you want the OTP to be delivered. In the following example, the user will receive an OTP via "WhatsApp or SMS". This means the user can select their preferred method during reset.
The valid duration (in seconds) for the OTP or reset link can also be customized. This duration does not determine the minimum delay before resending OTPs or links.
As an example, if OTP is enabled as the recovery method, users will see the following screen to verify their identity during password reset:
Once you're done, save your changes to enable the new configuration.
Follow the official guide to create a OAuth App.
In "Authorization callback URL", use https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/github.
After the creation, click "Generate a new client secret". Remember the client secret.
In the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with GitHub.
Fill in Client ID.
Fill in Client Secret
🎉 Done! You have just added GitHub integration to your apps!
Recommended practices for setting password for a user account created on the Authgear Portal
For creating accounts and sending users their passwords using Admin API, see createUser in the Admin API documentation.
In this post, we'll cover a few options and describe examples of automating the process of sending passwords to new users using the Authgear Portal or webhooks.
At this moment, Authgear only sends passwords to email accounts.
Navigate to User Management > Users. From the Users page, click on the Create User button in the top right corner.
Enter the user's credentials and input a secure password you wish to set for the user, or click on Generate to have Authgear automatically create a new password.
Users can still log in to their new account if they lose the password you set for them. They can click Forgot Password during login, and an OTP or link will be sent to the user. The user can then set a new password.
Generative AI powered by large language models (LLMs) has revolutionized software development, giving rise to a new paradigm called “Vibe Coding.” This approach empowers individuals with ideas—regardless of their coding expertise—to create software quickly and intuitively. For developers, generative AI automates repetitive tasks, boosts productivity, and even enhances code quality in some cases.
While vibe coding is undeniably exciting, there’s one area where caution is essential: security. AI-generated code can sometimes be buggy or incomplete, and when deployed in real-world applications, critical aspects like user authentication and data protection cannot be left to chance.
To bridge this gap, Authgear offers a plug-and-play authentication solution that ensures your AI-generated applications are enterprise-grade secure. With the right prompts, developers can integrate robust security features into their projects in seconds. These features include:
: Add an extra layer of security to user accounts.
Email/Phone Verification with OTP: Ensure user identities are verified during sign-up or login.
: Safeguard against unauthorized access attempts.
: Keep malicious bots at bay.
By incorporating Authgear into your vibe coding workflow, you can focus on building innovative applications while ensuring top-notch security for your users.
Passwordless login with email links
Email Login Links, also known as "magic link", is a passwordless authentication method that allows users to log into a website or application without using a traditional password. Instead, it relies on a unique link sent to the user's email address.
Here's how it works:
User initiates the login process by entering their email address on the login page.
Authgear generates a unique, time-limited login link associated with the user's email address.
The link is sent to the user's email inbox, with a button prompting them to click on it to log in.
The user clicks on the link, and approve the login
The user is securely logged in to the app or website.
Magic link login offers several advantages. It eliminates the need for users to remember and manage passwords, reducing the risk of weak or reused passwords. It also simplifies the login process and reduces friction, as users only need to access their email to authenticate.
To enable Email Login Links:
In the Authgear Portal, go to "Authentication" > "Login Methods"
Select "Email" or "Mobile/Email" as login methods
Go to the "Verification and OTP" tab
Traditional web app that runs on the server
If your application is a traditional web app running on a server, for example, Java EE, Express, PHP, GO, Laravel, or ASP.NET Core MVC, you can leverage the OpenID Connect (OIDC) protocol to authenticate users via Authgear. A wide range of plug-and-play libraries can be found that simplify the integration process. These libraries handle crucial tasks such as authentication requests, session management, and redirecting users back to your application seamlessly.
ExpressNext.jsPython Flask AppJava Spring BootASP.NET Core MVCLaravelPHPAllow users to log into your app via OTP with WhatsApp, as a secure alternative to SMS
Authgear let your users login passwordlessly with WhatsApp OTP.
To enable this feature from the Portal:
Go to Authentication > Login Methods, we are going make few changes on this page.
In the top section of Select Login Methods, select Mobile.
In Authentication of Select Login Methods, select Passwordless.
In the tabs section below, switch to the tab Verification and OTP.
In the dropdown Verify phone number by, select either WhatsApp or SMS or WhatsApp only.
Press Save on the top left corner.
When the user login with their phone number, a WhatsApp message with an OTP and the app name will be received. They can copy the code by tapping on the "Copy code" button and log in by the code.
If "Verify phone number by WhatsApp or SMS" is enabled, the user can switch to receive the OTP via SMS instead in the login page.
Guide on resetting a user's password via the Authgear Portal or AdminAPI
In your project, navigate to User Management > Users. Then click on the user whose password you would like to reset.
Go to the user's Account Security tab, and click on Change Password. You can also require the user to change their password on login by enabling the Ask to change password on login toggle.
You can either enter a secure password you wish to set for the user in the Password field, or click on Generate to have Authgear automatically create a new password for the user.
Check the "Send the password to user's email" box to enable Authgear to send the password entered in the Password field to the user.
If you wish to force users to change their password upon logging in with the password you set for them, enable "Ask user to change password on login". Otherwise, users can continue using the password you set for them.
Finally, remember to click Change to save your changes.
See under Reference > APIs > Admin API > API Queries and Mutations.
Users can still log in to their new account if they lose the password you set for them. They can click Forgot Password during login, and an OTP or link will be sent to the user. The user can then set a new password.
Integrate Authgear on the client side in mobile apps without SDK
Authgear is built based on OIDC 2.0 standard, you can integrate it into any application framework without SDK.
Authorization Code Flow with Proof Key for Code Exchange (PKCE)
For public clients like mobile apps and SPAs, PKCE flow should be used. It uses code_challenge_method & code_challenge
An API or service protected by Authgear
If your API or backend service needs authentication, you can validate the session in your application server code. Each request from the client to your application server should contain an access token or a cookie. Your backend server should validate them for each HTTP request.
There are different approaches to verify the requests based on whether you validate JWT (JSON Web Tokens) in your server, or forward authentication to Authgear Resolver Endpoint.
Allow users to authenticate with a custom flow.
In Authgear, you can build your own custom login and sign-up pages instead of using the built-in ones.
In Authentication > Login Methods, if Email and phone number are both enabled, the user will be able to choose between their preferred method during login.
In the example above, the user can choose to signup/login with either an email address or a phone number, but they cannot register with both at the same time.
If you are developing mobile or desktop applications, choose from one of these SDKs for your platform to get started.
Use OIDC prompt parameter to force OAuth providers to show login screen.
The prompt="login" parameter which is defined in the can prompt Social/Enterprise Login Providers to always show their login screen. As a result, you can use the prompt="login" parameter to allow users to switch accounts when their previous authentication session on the provider is still stored.
In this post, you'll learn how to use prompt: "login" in Authgear SDKs to force OIDC providers to always show your users their login screen. You can also use prompt: "login" to allow users to switch accounts with a Social/Enterprise Login provider on the same device (or browser).
Save the changes.
Fill in Tenant with the Azure AD B2C Tenant Name.
Fill in Policy with the Policy (User Flow) Name. Normally it starts with b2c_.
Save the changes


Check the "Send the password to user's email" box to enable Authgear to send the new password to the user.
If you wish to force users to change their password upon logging in with the password you set for them, enable "Ask user to change password on login" as well. Otherwise, users can continue using the password you set for them.








This endpoint serves as a JSON document containing the OpenID Connect configuration of your Authgear project. That includes the authorization endpoint, the token endpoint, and the JWKs endpoint. The URL looks like:
To singup or login, redirect the user to the /authorize endpoint. The URL should look like this:
Code Example
“S256” is supported in code_challenge_method.
The code_verifier is a string of length between 43 and 128 generated on the client side. It should be unique for each authorization request. The code_challenge is a SHA-256 hash of the verifier.
The state parameter is optional. Authgear will include the value of the state parameter when redirecting the user back to the client application. Learn more at Use the OAuth 2.0 State Parameter
After login, the user will be redirected to [redirect_uri]?code=[AUTH_CODE], the AUTH_CODE is needed in the next step
See the supported scopes at
After receiving the AUTH_CODE in your application, make a POST request to the /token endpoint.
Include the code_verifier used for generating the code_challenge to prove both requests come from the same client.
The response may contain the ID token, the access token and the refresh token depending on the scope supplied by the previous step.
When the user logs out, revoke the refresh token by making a POST request to the revocation_endpoint with the refresh token in the body in application/x-www-form-urlencoded as content-type. The endpoint looks like https://AUTHGEAR_ENDPOINT/oauth2/revoke, it can be found in OpenID Connect configuration document.
Then clear the access token and refresh token stored locally in your app.
Include the access token in the Authorization headers of the frontend requests to verify your user’s identity. Follow this guide to learn about validating the JWT in your application server Validate JWT in your backend
Integration difficulties
Easy You only need to add code in your application to validate and decode JWT
Medium Need to setup extra reverse proxy to resolve authentication information
Transportation of session
Access Token in Authorization header
Session ID in Cookies or
Access Token in Authorization header
Authgear uses JSON Web Token (JWT) for secure data transmission, authentication, and authorization.
Authgear returns the access token and refresh token to the client app after authentication. Your client app should call the backend with the access token in the Authorization header. The tokens should be parsed and validated in the backend server to ensure they are not compromised and the signature is authentic.
Request example:
Read more on Validate JWT in your application server guide.
Forward Authentication is a process where an intermediate reverse proxy or API Gateway is responsible for authenticating a request before it reaches the intended application or service. This can add an extra layer of security and centralize the authentication logic. An intermediate service forwards each incoming HTTP request to the Authgear Resolver Endpoint to verify the access token or cookie in the HTTP header.
Read more on Forward Authentication to Authgear Resolver Endpoint guide.
Instead of validating the access token in the backend, a reverse proxy forwards the request to an Authgear Resolver Endpoint. This endpoint resolves and verifies the access token in the Authorization Header of the request.
In this approach, instead of validating the token in authorization header, Authgear returns Set-Cookie headers and sets cookies to the browser. The cookies are HTTP only and share under the same root domains. So you will need to setup the custom domain for Authgear, such as identity.yourdomain.com.
If you have multiple applications under yourdomain.com, all applications would share the same session cookie automatically. After that, you can verify the cookies using the Resolver Endpoint.
Request example:
Reliability
Medium JWT only updates when expire. That means before the token expiry, your application may see the user is valid even they has been disabled
High Update near real-time, based on your reserve proxy cache setting
One popular signup flow is to require the user to verify both their email and phone during signup, allowing them to log in with either in the future. This can be enabled by adding the following configuration to the YAML in Portal > Advanced > Edit Config.
The two main steps of this signup process are setup_email, then setup_phone. The action type of both steps is identify.
Each step has allowed identification methods (e.g. email, phone)
Each identification method has steps defining actions to perform, which are:
verify: confirms ownership of the credential
create_authenticator: registers the credential as a valid login method
authentication defines how the user will be authenticated. For example, using the primary_oob_otp_sms
target_step: The YAML structure requires certain nested steps to explicitly reference the parent step.
one_of is used in some steps to define branching options. To adhere to the syntax, one_of must be included even if there is only one option available.
In this example, a sign up flow is defined without the login steps (see Line:2), the "Automatically signup a new user if a login ID is not found during login" option should be disabled in the portal.
To further modify the authflow to your needs, you can refer to the specification of Auth Flow, and the API reference for Auth Flow API.

Log in to the LinkedIn Developers Portal and create a new app or update the configuration for an existing one.
Go to the Auth tab of your LinkedIn app and take note of the "Client ID" and "Client Secret".
Also, add https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/linkedin to "Authorized redirect URLs" under "OAuth 2.0 settings" section.
Next, open the Products tab of your LinkedIn app, and request access to "Sign In with LinkedIn using OpenID Connect."
In the Authgear Portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with LinkedIn.
Then fill in the Client ID. and Client Secret from your LinkedIn app.
Save the settings.
🎉 Done! You have just added LinkedIn Login to your apps!
Authgear SDKs have a prompt parameter that you can set in your application. The value of the prompt parameter will be passed to the Social/Enterprise Login provider. Hence, if you set prompt: "login" in the SDK, your Social/Enterprise Login provider will receive a prompt="login" parameter. The following code examples show how to use the prompt parameter in Authgear SDKs.
authgear
.startAuthentication({
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: PromptOption.Login,
})authgear
.authenticate({
redirectURI: 'com.reactnativeauth://host/path',
prompt: PromptOption.Login,
})AuthenticateOptions options = new AuthenticateOptions("<AUTHGEAR_REDIRECT_URI>");
List<PromptOption> promptOptions = Arrays.asList(PromptOption.LOGIN);
options.setPrompt(promptOptions);
mAuthgear.authenticate(options

Add Facebook Sign in to your apps in less than 5 minutes.
This guide shows how to connect your Authgear application to Facebook so users can log in using the Login with Facebook feature.
If you are using Authgear in your existing Facebook Apps, you may skip to the next step to set up the OAuth client.
You will need a Facebook developer Account. Register as one by clicking Get Started in the website.
To create a new app, go to the Facebook Developers panel then click the Click Create App button.
On the next screen, select Other as your app use case then, click Next.
In the app type selection screen, pick the option that best meets your requirements. For our example, we'll select the Consumer app type.
Enter your app name on the next screen and finish the app creation process.
In the app panel, click Add Product next to Products in the sidebar.
Click the Set Up button in Facebook Login.
Go to Settings of Facebook Login.
After setting up the Facebook Login product, go to App settings > Basic in the sidebar.
You will need the App ID and App Secret to configure Facebook Login so, note them down.
In the portal, go to Authentication > Social / Enterprise Login.
Enable Login with Facebook.
Fill in the Client ID with the App ID obtained from the Facebook Developers portal in the previous step.
🎉 Done! You have just added Facebook Login to your apps!
Your end-users can now sign in with Facebook on Authgear's pre-built Log In and Sign Up page. Existing end-users can connect their account to Facebook in the page.
Guide on the different ways you can modify the profiles of the users of your application.
Authgear offers multiple ways for you (the admin) and your users to update user profiles. As an admin, you can modify profile attributes for any of the users of your Authgear project. End users on the other hand can modify their own profile using the Profile settings UI provided by Authgear or using a custom logic you implement in your code.
In this guide, we'll walk through all the options for updating user profiles.
To follow along, you need to have the following:
An Authgear Account. You can create one for free .
At least one registered user on your Authgear Project.
At the end of this post you'll be able to do the following:
Update a user profile as an admin from the Authgear Portal or using Admin API.
Update a user profile as an end user via the profile settings page.
You can update the profiles for your users as an admin using either the Authgear Portal or the Admin API. Below are guides on how to use both options.
This option provides an easier way to manage your users within the Authgear Portal.
To update user profiles using this method, first, log in to the , then select your project.
Next, Navigate to User Management section to view all the users currently registered under your project.
Click on the ID (name, email, or phone number) for the user you wish to update their profile to open the edit user details page.
From the edit user details page, you can edit the selected user's standard attributes such as Given Name, Family Name, Birthday, etc. If you scroll down on the edit user details page, you'll find more fields like the custom attributes that you can also update.
Once you're done, click the Save button to keep your update.
The second option available for updating user profiles is the Admin API. The Admin API is a GraphQL API that you can use to manage your users. You can access Admin API from the or by making requests to the API from your code or a client like Postman.
To update a user profile via the Admin API, you need to create a mutation like the following:
First, create a variable with all the existing profile attributes for the user, then include new fields or update the value for the fields you wish to update. Note that omitting an existing attribute in your variable will cause Authgear to delete that attribute.
Variable
Mutation
For a detailed guide on making a GraphQL query to update user profiles, see our dedicated post on updating.
Also, see the to learn how to update custom attributes of a user profile.
Authgear provides a user settings page in addition to the default Auth UI for user registration and login.
Your users can update their profile from this settings page by following the steps below:
First, within your application, provide a link to the user settings page for your Authgear project. The URL should look like this: https://<YOUR_AUTHGEAR_ENDPOINT>/settings. Note that users can not access this link directly without logging in first.
After a user logs in and visits the settings page, they can view their profile photo and other details.
Users can click on the Edit Profile button to update profile details such as name, gender, photo, and more.
To edit a profile attribute, the user should click on that attribute.
Guide on how to use Authgear as a SAML IdP for Dropbox
Security Assertion Markup Language (SAML) is a standard that allows an Identity Provider (IdP) and a Service Provider (SP) to perform user authentication and authorization without exchanging a user's password.
In this post, you'll learn how to set up Authgear as an Identity Provider and Dropbox as a Service Provider.
An Authgear account. Sign up for free.
A Dropbox Business Advanced account.
You need an Authgear client application of type OIDC/SAML Client Application to use Authgear as a SAML identity provider.
To create a new client application, log in to Authgear Portal, select your project then click on the Applications link from the navigation menu.
Next, click on Add Application to create a new client application. Alternatively, select an existing application of type OIDC/SAML Client Application and skip to step 2.
On the New Application page, enter Name and select OIDC/SAML Client Application as the Application Type.
Click Save to proceed.
By default, SAML 2.0 is not enabled for the client application.
To enable SAML for your client application, click on the SAML 2.0 tab then toggle the SAML 2.0 Support switch on.
Next, change NameID Format to urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress.
Add the following URL (Dropbox post-back URL) in Allowed Assertion Consumer Service URLs (ACS URLs) field:
Click on Save to keep your changes.
Scroll down to the Configuration Parameters section of your Authgear client application's SAML 2.0 tab. Note the value for the login URL.
Also, download the Identity Provider Certificate for the client application to your computer.
You'll use the Login URL and certificate later in the Dropbox Admin console.
Log in to your Dropbox Business Advanced account then click on Admin console in the navigation menu.
In the Dropbox Admin console navigate to Settings > Single sign-on.
Now in the Dropbox Single sign-on settings page, set Single sign-on to Required. Then, configure the following:
Paste the value for your Authgear client application's Login URL in the Identity provider sign-in URL field.
Under X.509 certificate, click on the Certificate upload button, then upload the Identity Provider Certificate you downloaded from your Authgear client application in the previous step.
To test your SAML implementation, you need to add a new user to your Dropbox with an email address that is associated with a user account in your Authgear project.
To add a new user to your Dropbox, navigate to Admin console > People > Members > Invite member.
Accept the invite for the new user, and try to log in to Dropbox using the registered email address for the new user. You should be redirected to the Authgear SAML login page. On successful login to the Authgear account, you should be redirected and signed in to Dropbox.
To configure "Sign in with Apple" for Authgear, you will need to fulfil the following:
Register an Apple Developer Account. Apple Enterprise Account does not support "Sign in with Apple"
Register your own domain.
Your domain must be able to send and receive emails.
Set up (SPF) for your domain.
Set up (DKIM) for your domain.
Create an "App ID" by adding a new "Identifier" , choose app IDs, enable "Sign in with Apple" enabled.
Create a "Services ID" by adding a new "Identifier" , choose service IDs, enable "Sign in with Apple".
Click "Configure" the Next to "Sign in with Apple". In "Primary App ID" field, select app ID created above.
Fill in and verify the domain created above, add https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/apple to Return URLs
Create a "Key" following with "Sign in with Apple" enabled. Click "Configure" next to "Sign in with Apple" and select "Primary App ID" with app ID created above. Keep the private key safe, you need to provide this later.
In the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with Apple.
In Client ID, add the identifier of the Services ID you created in Apple. Not the ID of the App ID or the Client ID of your Authgear Application.
🎉Done! You have just added Sign in with Apple to your apps!
Suppress message delivery and fix OTP for testing purposes
Test mode allows for control over how OTPs are handled during development and testing.
Common use cases include:
Internal testing (e.g. Allowing specific accounts to authenticate with fixed codes for ease of testing).
Testing SMS, WhatsApp, or email login via OTP, but don't want to rely on the actual OTP delivery.
App Store Reviewers. See Tips for Apple App Store Review with Passwordless Login.
In your portal, navigate to Advanced > Edit Config
Then add the following to the yaml:
How this works
regex: Defines target emails/phone numbers the rule applies to using a regular expression
fixed_code: A 6-digit code accepted as the OTP for targets
suppressed: false by default. If true, messages will not be sent to the target
In development, you may want to use a fixed code for testing.
In this case,
The rule in oob_otp matches all target so a fixed OTP 000000 will be used.
SMS is not suppressed for +85291231234 only. They will receive 000000 via SMS so the SMS sending capability can be tested.
No messages will be sent to WhatsApp or email channels
If the rules in sms were reversed in the example above, the .* regex would match all accounts first, making more specific rules unreachable.
During app review, you can enable "test mode" for a specific phone number or email address that allows the account to authenticate with a fixed OTP. So this account can be shared with the app reviewer to complete the passwordless login flow
In this example,
Only +85291231234 can be passed with the fixed code 000000 and other accounts should use real OTP.
SMS and WhatsApp are suppressed for +85291231234
Authgear is a highly adaptable identity-as-a-service (IDaaS) platform for web and mobile applications
Authgear is an authentication & user management solution which makes it very easy for developers to integrate and customize their consumer applications, it includes these features out of the box:
Zero trust authentication architecture with OpenID Connect (OIDC) standard.
Easy-to-use interfaces for user registration and login, including email, phone, username as login ID, and password, OTP, magic links, etc for authentication.
Support a wide range of identity providers, such as , , and (AD).
Support biometric login on mobile, Passkeys, and Multi-Factor Authentication (MFA) such as SMS/email-based verification and authenticator apps with TOTP.
A user management portal, like password resets, account locking, scheduled deletion or anonymization, and user profile management.
Single Sign-On (SSO) provides a single unified experience for your customers to log into multiple web/mobile apps, including Web2Web, Web2App, and App2App SSO.
Enable for your users to log into multiple web applications easily.
Session management with Authgear Portals, and a pre-built setting page for users to control concurrent sessions.
Customizable UI with a user-friendly low-code dashboard.
Various security features such as audit logs, brute force protection, smart account lockout, password policy, etc.
APIs for further integration and customizations. For example, build your own custom login and sign-up pages from the ground up powered by .
Most importantly, you can with Authgear for free.
Authgear contains the following high-level components:
Client App SDKs - for developers to quickly implement authentication with Auth UI on your web and mobile applications. Check out for tutorials and API References.
Auth UI - is the default batteries included UI for login, signup and setting page. You can customize the style via the Portal, including the CSS and HTML of each page.
- for developers to implement their own login, signup and reauthenticate UI (e.g. a mobile native view); or to define a customized login, signup and reauth flow.
- explain the common approach of using Access Token or Cookies (JWT or random string) to authenticate an API or HTTP Requests.
- allow your backend to interact directly with Authgear for user management purpose.
- call external web endpoint or use the hosted type-script to customize the behaviour of Authgear. E.g. blocking certain type of sign up, or call external endpoint for each login.
Authgear Portal - You can configure your projects, manage users, check out , or customize the AuthUI. See the for Authgear Portal.
Analytics Page - View reports of all users and active users over a specific time interval on the .
- Set account Lockout Policy to safeguard a user account from brute-force login attempts.
- Bot protection tools to block automated attackers.
- Learn how to set password strength and how the password strength is calculated.
- Add biometric login to your application.
- Enable 2FA in your Authgear project.
- Allow users to log in without a password using a magic link.
- Set up passkey for your project.
- Customize the look and feel of AuthUI to match your branding.
- Change the language for display texts.
Features for managing your users via Authgear Portal
- Create a new account for a user from Authgear Portal.
- Delete a user account from your project.
- Detailed guide on how to use Roles and Groups.
- Guides on how to view and manage user profile information.
If you are building token-based websites or mobile apps, you can enable the SSO feature via the SDK.
When SSO-enabled is ON, the end-user will need to enter their authentication credentials when they login to the first app. Later on, when they login to the second app, they will see a continue screen so that they can log in with just a click, without authenticating themselves again.
When the end-user logout the SSO-enabled app, all the apps will be logged out at the same time.
You can turn on this feature when you configure the SDK by setting the is sso enabled option to true.
These type of SSO requires sharing the cookies between mobile apps and the system browsers on mobile, hence underlying it use ASWebAuthenticationSession on iOS and Custom Tab on Android, which will show a popup box like this:
If you want to avoid the said popup box, you will need to use WKWebView on iOS and WebKitWebView on Android for UIImplementation instead; And use for sharing login session between mobile apps, and between mobile and web instead.
Learn how to add custom attributes to user profiles and manage existing custom attributes
In Authgear, a user's profile includes two types of attributes.
The first is the standard attributes which are basically common profile fields such as Primary Email, Primary Phone, Username, Name, Birthday, etc that are present by default.
The second type is the custom attributes an Authgear user can set for their project. This allows you to add custom fields to the profiles of your users. For example, you can add a Post Code custom attribute to your Authgear so users can provide this data for their profile.
All custom attributes are returned in the UserInfo response under the custom_attributes field.
In this post, you'll learn how to add new custom attributes to your Authgear project. You'll also learn how to manage existing custom attributes.
You can add new custom attributes to your project from the Authgear Portal. To do this, first, navigate to User Profile > Custom Attributes. Then, click on the Add New Attribute button to open the Add Custom Attribute page.
Enter the Attribute Name, a valid attribute name should consist of lowercase letters (a-z), digits (0-9), and underscore () only, must start with lowercase letters (a-z), and NOT end with an underscore (_).
Select the appropriate Attribute Type based on the type of data you expect users to enter in the custom attribute. The option you select will affect the type of input field (text field, dropdown, etc) users will see in their profile settings UI.
Once you're done, click the Save button to add the new custom attribute.
Usually, the next key action to take after adding a new custom attribute will be to set the access right. An attribute's Access Right is a configuration that determines who can see (Read-only) or add or modify (Editable) the value of an attribute's field.
You can set the Access Right for an attribute under the following groups:
Portal Admin: Access control for the user profile attributes in Admin Portal > User Management.
Token Bearer: Access control for the user profile attributes in the UserInfo endpoint.
End-user: Access control for the user profile attributes in the End-user settings page.
To set the access right for an attribute, navigate to User Profile > Custom Attributes in the Authgear Portal. On the Custom Attributes list, click the Access Right dropdown for the group and custom attribute you wish to update. Click Save when you're done to keep the changes.
Note: Selecting the Hidden access right, for any group will hide the field for the attribute from that group. For example, selecting Hidden for the post_code attribute for the Token Bearer group means the post_code field will be hidden (not included) in the UserInfo endpoint response.
From the Custom Attributes list, click on the pencil icon to open the Edit Custom Attribute page.
Note: You can't modify the Attribute Type for an existing attribute. The alternative will be to create a new custom attribute with the new Type and migrate data from the old attribute to it. Also, rename and change the access right for the old attribute to make it obsolete.
You can set the order of how custom attributes appear in the UI.
To do that, in the Custom Attributes list, click and drag the stacked icon next to an attribute up or down to move the position.
Delete is not supported. Instead, you should change the name and access right to make the attribute obsolete.
If your mobile app has security requirements similar to that of mobile banking applications, you may want the end-users to authenticate themselves every time they use your app.
By default, the SDK stores the refresh token in a persistent storage specific to your app. The end-user signs in once and their session lasts for a long period, even if they quit the app.
You can alter this behavior by switching to a transient storage by setting the tokenStorage option to TransientTokenStorage() when configuring the SDK. The refresh token will be removed after the app is cleared, therefore authentication will be required on every app launch.
import authgear, { TransientTokenStorage } from "@authgear/react-native";
authgear.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
tokenStorage: new TransientTokenStorage(),
final authgear = Authgear(
clientID: CLIENT_ID,
endpoint: ENDPOINT,
tokenStorage: TransientTokenStorage(),
);var authgearOptions = new AuthgearOptions
{
ClientId = CLIENT_ID,
AuthgearEndpoint = ENDPOINT,
TokenStorage: new TransientTokenStorage(),
};
#if __ANDROID__
Enable secure, automated authorization for your backend systems, microservices, and IoT devices, ensuring only trusted apps and devices can access your APIs.
Machine-to-machine (M2M) applications enable backend services, CLIs, scheduled jobs, and smart devices to obtain access tokens and interact with APIs using dedicated credentials. Instead of human user authentication, these apps use their own credentials to securely access resources, streamlining automation and integration across your stack.
Perform faster authentication flow via another app installed on the same device.
This may be familiar for users from UK, which many neobanks are using the app2app mechanism to authorize the money transfer from 1 bank app to another.
The App2App mechanism allows one app to authenticate the user using another apps connected to the auth server installed on the same device. This is achieved by universal links and the apps do not need to share the session via the system browser or the refresh tokens via the token storage.
Please note that this is not the Single Sign-on feature, if your are offering multiple apps under the same brand and wish the users to use a shared login session among their apps in the device, you may want to use instead. App2app should be used when:
A guide on how to use Authgear as a SAML Identity Provider IdP in Salesforce
Security Assertion Markup Language or short is a standard for exchanging security information between businesses. In SAML, one party acts as the Identity Provider (IdP) and the other party is the Service Provider (SP).
The Service Provider (SP) trust the Identity Provider to handle the process of user authentication. The Identity Provider handles user authentication and notifies the Service Provider once the user is authenticated.
In this guide, you'll learn how to set up SAML with Authgear as an Identity Provider (IdP) and Salesforce as the Service Provider (SP) in SAML.
Setting format and strength requirements for passwords
Authgear allows you to set a password policy for your project. This page walks through setting password requirements, password strength, keywords to exclude, and password expiry from the Authgear Portal.
You can configure your password policy in password settings.
Choose a minimum character length, and use the checkboxes provided to include one or more requirements for a valid password.
To ensure your updated password policy applies to both existing and new users, toggle on "Force password change on next login". All users will be required to update their passwords if their current passwords do not meet the newly configured policy.
Guides on how to use Authgear as a SAML Identity Provider for Single Sign-On
Security Assertion Markup Language or short is a standard for exchanging security information between businesses. In SAML, one party acts as the Identity Provider (IdP), and the other party is the Service Provider (SP).
SAML allows the Identity Provider and Service Provider to authenticate and authorize without exchanging a user's password.
The Service Provider (SP): In SAML, this is the service that trust the Identity Provider to handle the process of user authentication.
The Identity Provider (IdP): handles user authentication and notifies the Service Provider once the user is authenticated.
Use the pre-authenticated URLs feature to open a website from a native app in an authenticated state.
Pre-authenticated URLs is a feature that enables single sign-on (SSO) from a mobile application to a website. It allows users who are authenticated on a mobile application to open a website in an authenticated state.
An example use case for a pre-authenticated URL is opening a web application in a WebView.
To use pre-authenticated URLs, you must have the following:
Passkeys give users a simple and secure way to sign in to your apps and websites across platforms without passwords.
Passkeys replace passwords and other passwordless login methods. It is built on the WebAuthn standard (also known as FIDO Sign-in), which uses public key cryptography to authenticate the user. With 1 click, Authgear upgrades your app to support this cutting-edge auth technology.
The passkey standard is supported on the latest versions of Chrome, Safari, and Firefox browsers. On iOS 16 and macOS 13 (Ventura), to the iCloud Keychain service. Passkeys are also (API level 28) or higher. A passkey is synchronized and relayed with an iCloud account and can be used across a user's devices.
Users can log in to their accounts using their biometrics easily. On Apple devices, Touch ID and Face ID authorize the use of the passkey which then authenticates the user on the app or website.
Configure settings for both Primary and Secondary passwords
In Authgear, a password can be Primary or Secondary. Secondary passwords can be enabled as part of Two Factor Authentication (2FA).
The password policies for Primary and Secondary passwords are not configured independently. Password policy settings apply to both types.
To configure your project's password policy, simply navigate to the password settings, and follow the corresponding guides.
curl -X GET 'https://AUTHGEAR_ENDPOINT/oauth2/authorize' \
--data-urlencode 'response_type=code' \
--data-urlencode 'client_id=CLIENT_ID' \
--data-urlencode 'redirect_uri=REDIRECT_URL' \
--data-urlencode 'scope=openid offline_access https://authgear.com/scopes/full-userinfo' \
--data-urlencode 'code_challenge_method=S256' \
--data-urlencode 'code_challenge=CODE_CHALLENGE' \
--data-urlencode 'state=abc'const randomData = secureRandomBytes(32); // (1)
const code_verifier = base64url(randomData); // (2)
const hash = await sha256(utf8(code_verifier));
const code_challenge = base64url(hash);
// (1) A 32-byte long secure random data using secure random number generator
// (2) this string must be between 43 and 126 bytes long
const params = new URLSearchParams();
params.set("response_type", "code");
params.set("client_id", "CLIENT_ID");
params.set("redirect_uri", "REDIRECT_URL");
params.set("scope", ["openid", "offline_access", "https://authgear.com/scopes/full-userinfo"].join(" "));
params.set("code_challenge_method", "S256");
params.set("code_challenge", code_verifier);
params.set("state", "abc");
const endpoint = new URL("https://AUTHGEAR_ENDPOINT/oauth2/authorize");
const authorizationURL = endpoint.toString() + "?" + params.toString();curl -X POST 'https://AUTHGEAR_ENDPOINT/oauth2/token' \
-H 'Content-Type: application/x-www-form-urlencoded' \
-d 'grant_type=authorization_code' \
-d 'client_id=CLIENT_ID' \
-d 'code=AUTH_CODE' \
-d 'redirect_uri=REDIRECT_URL' \
-d 'code_verifier=CODE_VERIFIER'const tokenEndpoint = new URL("https://AUTHGEAR_ENDPOINT/oauth2/token");
const form = new URLSearchParams();
form.set("grant_type", "authorization_code");
form.set("client_id", "CLIENT_ID");
form.set("code", AUTH_CODE); //Authorization code returned from authgear server
form.set("redirect_uri", "REDIRECT_URL");
form.set("code_verifier", code_verifier);
const response = await fetch(tokenEndpoint.toString(), {
method: "POST",
headers: {
"Content-Type": "application/x-www-form-urlencoded",
},
body: form,
});
const responseJSON = await response.json();https://AUTHGEAR_ENDPOINT/.well-known/openid-configurationhttps://AUTHGEAR_ENDPOINT/oauth2/authorize
?response_type=code
&client_id=CLIENT_ID
&redirect_uri=REDIRECT_URL
&scope=openid+offline_access+https://authgear.com/scopes/full-userinfo
&code_challenge_method=S256
&code_challenge=CODE_CHALLENGE
&state=abc> GET /api_path HTTP/1.1
> Host: yourdomain.com
> Authorization: Bearer <AUTHGEAR_ACCESS_TOKEN_IN_JWT>> GET /api_path HTTP/1.1
> Host: yourdomain.com
> cookie: session=<AUTHGEAR_SESSION_ID>authentication_flow:
signup_flows: # signup_flows, login_flows, signup_login_flows, reauth_flows, or account_recovery_flows
- name: default # the flow that is shown first to the user
steps:
- name: setup_email
type: identify # action type: verify, identify, create_authenticator
one_of:
- identification: email
steps:
- type: verify
target_step: setup_email
- type: create_authenticator
name: authenticate_primary_email
one_of:
- authentication: primary_oob_otp_email
target_step: setup_email
- name: setup_phone
type: identify
one_of:
- identification: phone
steps:
- type: verify
target_step: setup_phone
- type: create_authenticator
name: authenticate_primary_phone
one_of:
- authentication: primary_oob_otp_sms
target_step: setup_phone authgear?.authenticate(
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: "login"
)_authgear.authenticate(
redirectURI: "<AUTHGEAR_REDIRECT_URI>",
prompt: "login",
);Authgear(
clientId: CLIENT_ID,
endpoint: ENDPOINT,
tokenStorage: TransientTokenStorage()
)Use Authgear as OpenID Connect Provider - for developers to use Authgear with other software that already support OIDC login, you can use Authgear as an OpenID Connect Provider.
Export User API - Export user data from Authgear into a CSV or ndjosn file.
Link OAuth Provider using Account Management API - Link an OAuth provider to a user's account without AuthUI.
Social Login / Enterprise Login - Allow users to log in to your application using their existing account with a social media site or enterprise login provider.
Besides the built-in support of all major desktop and mobile platforms, passkeys can also be stored in hardware security keys such as YubiKeys, which provide the highest security against attacks.
Authgear adds a passkey feature to your apps and websites instantly. To enable it:
In your project portal, go to Authentication > Login Methods.
In the Select Login Methods section, turn on the Enable passkey support for compatible devices. toggle.
Press "Save" and your app now supports passkey login!
See the list of Passkey support via Authgear on different platforms.
macOS 12: Passkey is supported on major browsers. However, the credentials are deleted when clearing browser data.
iOS 15.5: Passkey is supported on Safari and stored locally a the device. Credential will be deleted by "Settings > Safari > Clear History and Website Data"
iOS 16 Beta 3: Passkey is synced with iCloud Keychain. The individual credentials can be viewed and managed in "Settings > Passwords"
Android 9 (API level 28) or higher: Supported.
Jot down the Key ID and download the key text file (.p8 file).
Copy the content in the key text file to Client Secret text area in Authgear Portal..
Fill in Key ID field using the Key ID obtained from step 5.
In Apple Developer Portal, click username on the top right corner, click View Membership.
Find the Team ID from Membership Information, fill in Team ID field in Authgear portal.
Save the settings.









Add https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/facebook to Valid OAuth Redirect URIs and save the changes.



















enabled
Set to true to enable test mode
false by default. This means the OTP flow will work as expected, and fixed codes will not be accepted for the channel.

authgear.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
sessionType: "refresh_token",
isSSOEnabled: true,
});authgear.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
isSSOEnabled: true,
});final authgear = Authgear(
clientID: CLIENT_ID,
endpoint: ENDPOINT,
isSsoEnabled: true,
);var authgearOptions = new AuthgearOptions
{
ClientId = CLIENT_ID,
AuthgearEndpoint = ENDPOINT,
IsSsoEnabled = true,
};
// Android
#if __ANDROID__
var authgear = new AuthgearSdk(GetActivity().ApplicationContext, authgearOptions);
#else
#if __IOS__
var authgear = new AuthgearSdk(UIKit.UIApplication.SharedApplication, authgearOptions);
#endif
#endifApplication Backends: Facilitates secure transfer of data, files, or logs between microservices or external systems.
CLI Tools: Allows tools running on developer or deployment machines to access APIs with short-lived tokens.
Scheduled Jobs & Daemons: Empowers background tasks (e.g., cronjobs, queuing systems) to access protected resources safely.
IoT Devices: Enables each smart device to authenticate independently and send data securely to cloud APIs.
Go to the API Resources page in the Authgear portal:
Create the API resource your apps/devices will access.
When registering the resource, specify its identifier—this acts as the unique URI representing your API (for example, https://myapi.com/api).
This identifier will be set as the aud (audience) claim in the JWT access tokens issued for this resource.
Define scopes for granular permissions, such as read:data, write:data, or manage:config.
Scopes specify exactly what operations clients can perform on your API.
In the Applications page:
Create a client application for each backend service, CLI tool, job, or device that needs API access.
Assign the relevant API resources and scopes to the application, ensuring least-privilege access.
After creating the application, you’ll be able to view its Client ID and Client Secret in the portal. Keep the Client Secret secure. It should never be exposed in client-side code or public repositories.
The Client Credentials Flow defined in OAuth 2.0 RFC 6749, section 4.4 is designed for non-user, automated access.
To obtain an access token in your backend, use the Client ID and Client Secret from your registered application in the portal:
You’ll receive an access token that includes only the permitted scopes for the client.
For details on token structure and claims, see M2M Tokens.
Send requests to your API by including the access token in the Authorization header:
Your backend can now verify the token and authorize the permitted operations.
Always validate incoming JWT tokens in your API servers:
Verify issuer, audience, scopes, expiration, and signature.
Reject requests with invalid or expired tokens.
Find sample code and best practices at Validate JWT in your backend.
{
"standardAttributes": {
"family_name": "John",
"given_name": "Doe",
"gender": "male"
}
}mutation ($standardAttributes: UserStandardAttributes) {
updateUser(input: {userID: "<ENCODED USER ID>", standardAttributes: $standardAttributes}) {
user {
id
standardAttributes
}
}
}https://www.dropbox.com/saml_logintest_mode:
oob_otp: # rules defined below apply to all OOB channels (email, sms, whatsapp)
enabled: true
rules:
- regex: .*
fixed_code: "000000"
sms: # channel specific rules defined here
enabled: true
rules:
- regex: .*
suppressed: truetest_mode:
oob_otp:
enabled: true
rules:
- regex: .*
fixed_code: "000000"
sms:
enabled: true
rules:
- regex: ^\+85291231234$ # SMS not suppressed for +85291231234
- regex: .*
suppressed: true
whatsapp:
enabled: true
rules:
- regex: .*
suppressed: true
email:
enabled: true
rules:
- regex: .*
suppressed: truetest_mode:
oob_otp:
enabled: true
rules:
- regex: ^\+85291231234$
fixed_code: "000000"
sms:
enabled: true
rules:
- regex: ^\+85291231234$
suppressed: true
whatsapp:
enabled: true
rules:
- regex: ^\+85291231234$
suppressed: trueAuthgear(
clientId: CLIENT_ID,
endpoint: ENDPOINT,
isSSOEnabled: true,
)new Authgear(
getApplication(),
CLIENT_ID,
ENDPOINT,
new PersistentTokenStorage(getApplication()),
true // isSsoEnabled = true
);new Authgear(
application,
CLIENT_ID,
ENDPOINT,
new TransientTokenStorage() //tokenStorage
);curl --request POST \
--url https://myproject.authgear.cloud/oauth2/token \
--header 'Content-Type: application/x-www-form-urlencoded' \
--data grant_type=client_credentials \
--data resource=IDENTIFIER_OF_API_RESOURCE \
--data client_id=CLIENT_ID \
--data client_secret=CLIENT_SECRETimport urllib.parse
import urllib.request
import json
url = "https://myproject.authgear.cloud/oauth2/token"
headers = {
"Content-Type": "application/x-www-form-urlencoded"
}
data = {
"grant_type": "client_credentials",
"resource": "IDENTIFIER_OF_API_RESOURCE",
"client_id": "CLIENT_ID",
"client_secret": "CLIENT_SECRET"
}
encoded_data = urllib.parse.urlencode(data).encode('utf-8')
req = urllib.request.Request(url, data=encoded_data, headers=headers, method='POST')
with urllib.request.urlopen(req) as response:
response_status = response.getcode()
response_body = response.read().decode('utf-8')
print("Response Status Code:", response_status)
print("Response Body:", json.loads(response_body))
package main
import (
"fmt"
"io/ioutil"
"net/http"
"net/url"
"strings"
)
func main() {
data := url.Values{}
data.Set("grant_type", "client_credentials")
data.Set("resource", "IDENTIFIER_OF_API_RESOURCE")
data.Set("client_id", "CLIENT_ID")
data.Set("client_secret", "CLIENT_SECRET")
req, _ := http.NewRequest("POST", "https://myproject.authgear.cloud/oauth2/token", strings.NewReader(data.Encode()))
req.Header.Add("Content-Type", "application/x-www-form-urlencoded")
resp, _ := http.DefaultClient.Do(req)
defer resp.Body.Close()
body, _ := ioutil.ReadAll(resp.Body)
fmt.Println("Response Status Code:", resp.StatusCode)
fmt.Println("Response Body:", string(body))
}
async function makeRequest() {
const url = "https://myproject.authgear.cloud/oauth2/token";
const data = new URLSearchParams();
data.append("grant_type", "client_credentials");
data.append("resource", "IDENTIFIER_OF_API_RESOURCE");
data.append("client_id", "CLIENT_ID");
data.append("client_secret", "CLIENT_SECRET");
const response = await fetch(url, {
method: "POST",
headers: {
"Content-Type": "application/x-www-form-urlencoded",
},
body: data,
});
const responseBody = await response.json();
console.log("Response Status Code:", response.status);
console.log("Response Body:", responseBody);
}
makeRequest();
Authorization: Bearer <access_token>The session cannot be shared via the browser cookies
The session cannot be shared via a common token storage
An app can start the authentication flow by opening a link to another app, instead of using the authorization endpoint. The app which handles the link should validate the authentication request, then could return a valid authorization code. The valid code is then transferred to the original app using universal link. The initiating app can use that authorization code to perform code exchange for tokens with Authgear.
A detailed explanation on the technology can be found in this specification.
Go to the Application detail page of the authorizing app, i.e. the app which handles the app2app authentication requests.
Scroll to the bottom and you will see the App2App config panel.
Select Enable App2App login for this Application"
Migration mode offers a less secure mechanism which helps older user sessions to participate in App2App. DO NOT enable it unless there is migration problem.
Go to the Application detail page of the initiating app, i.e. the app which initiates the app2app authentication requests.
In the redirect URIs, a universal link that's capable of opening this app should be set.
Define and set up the universal links for both apps, for example:
https://a.example.com/authorize should open the authorizing app (App A)
https://b.example.com/redirect should open the initiating app (App B)
In App B, call startApp2AppAuthentication(options: App2AppAuthenticateOptions) to initiate the app2app login
App2AppAuthenticateOptions.authorizationEndpoint should be an url of an universal link pointing to App A, i.e. https://a.example.com/authorize
App2AppAuthenticateOptions.redirectUri should be an URI for the authorizing app to return the authentication result. It must be an universal link which opens the current app. i.e. https://b.example.com/redirect
In App A, upon receiving the app2app login request
Call parseApp2AppAuthenticationRequest(url: URL): App2AppAuthenticateRequest?
The result will be null if the url is not a valid app2app request.
You can approve or reject the app2app request in App A
Approve: approveApp2AppAuthenticationRequest(request: App2AppAuthenticateRequest)
Approves an app2app request returning the result through the redirect URI.
When it's back to App B, call handleApp2AppAuthenticationResult(url: URL)
This method should be called by the app which initiate the app2app authentication flow, and when received the result through the universal link, url should be the URL of the universal link received.
An Authgear account. Sign up for free.
A Salesforce account.
An Authgear Client application is required to set up Authgear as a SAML Identity Provider. To create an Authgear application, login to the Authgear Portal and navigate to the Applications in your project.
Click on Add Application to create a new application. Or, select an existing application that is of type OIDC/SAML Client Application and skip to step 2.
Now on the New Application page, enter a name for your application (e.g. My App) and set the Application Type to "OIDC/SAML Client Application".
Click Save to continue.
If prompted to view a tutorial, click Next to proceed to the application configuration page.
On the configuration page of your Authgear client application, switch to the SAML 2.0 tab. Toggle the SAML 2.0 Support switch on to enable SAML for the application.
Next, change NameID Format to urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress.
Enter your Salesforce domain in the Allowed Assertion Consumer Service URLs (ACS URLs) field under SSO Settings. You can get value for your Salesforce domain from the My Domain page on the Salesforce Setup page.
Click on Save to keep your changes.
Still, on the SAML 2.0 tab, scroll to the Configuration Parameters section and click on the Download Metadata button to download the Identity Provider Metadata XML file for your Authgear application to your computer.
Next, scroll to the Identity Provider Certificates section and click Download Certificate to download the certificate to your computer.
You will use the downloaded metadata file and certificate in later steps.
To enable SAML in Salesforce, login to your Salesforce account, click on the Settings icon on the top right corner then select Setup. This will open the Salesforce Setup page.
On the Setup page, type "single sign-on" in the Quick find search box on the left. Select Single Sign-On from the result to open the Single Sign-On Settings page.
Next, click on the Edit button under Select Single Sign-On Settings then check the SAML Enabled box under Federated Single Sign-On Using SAML. Click Save to keep your changes.
To add Authgear as a SAML Identity Provider, return to the main page of Single Sign-On Settings.
Next, click on the New from Metadata File button. Then, click Choose file, and select the Metadata XML file you downloaded in Step 3. Click on Create to continue.
On the next screen, you should see configurations for your new SAML IdP, including the details from the metadata file. Edit the Name field to Authgear SAML. The value for the Name field will be visible on your Salesforce login page.
Next, click on the Choose file button next to Identity Provider Certificate then select the SAML IdP Certificate file you downloaded in Step 3 from your computer.
Once you're done with the above configurations, click Save to finish.
In order to log in with a specific SAML IdP, you must first enable the provider in Salesforce.
To enable your new SAML IdP (Authgear SAML) search for "my domain" in Quick find. Click on My Domain from the result. On the My Domain page, scroll to Authentication Configuration then click on the Edit button.
You should find your Authgear SAMP IdP under Authentication Service. Check the box next to Authgear SAML to enable it. Click Save to keep changes.
Once you have enabled your SAML Identity provider in this step, it will be visible on your Salesforce login page the next time you attempt login.
Force you can log in to your Salesforce project using Authgear SAML, you need to create a user using an email address that is linked to a user account in your Authgear project.
To create a user in Salesforce, use type "users" in the Quick find search box, then select Users > Users from the result. This will take you to the All Users page.
From the All Users page, click on New User. Create a new user with an email address that's linked to an account on your Authgear project.
Now, to test your SAML implementation, log out of Salesforce and attempt logging in again. This time, you should see a Login with Authgear SAML button.
When you click on Login with Authgear SAML, you should be redirected to Authgear Login page. Login to the account on your Authgear project that has the same email address as the new user you created earlier in this step. You should be successfully logged in to your Salesforce project.
Password strength is simply a measure of how difficult it is to guess or crack a password.
Authgear currently uses the zxcvbn password strength estimator library, which goes beyond basic requirements (like length or character variety) and uses pattern matching to recognize common insecure passwords.
Scroll down to the Advanced sub-section of the Password tab, then click select your preferred option from the Min. password strength level dropdown.
Toggle on Prevent Password Reuse to ensure a new, unique password is set during password changes.
In the following example, the new password cannot match any password used within the 90 days, or any last 3 previously used passwords.
You can also disallow specific keywords in the user's password. Simply add them to the "Keywords to be excluded" field, and the admin or user will not be able to set a password containing the listed keywords.
See Password Expiry
Once you're done, remember to hit Save to keep your changes.

Authgear supports the SAML protocol. Hence, you can set up third-party services like Salesforce, Dropbox, Figma, etc. to trust Authgear with the user authentication process.
See the following guides for some popular service providers:
To set up SAML in Authgear, you need to create an Authgear client application with the Application Type: OIDC/SAML Client. Then use the configuration for the Authgear client application to configure a SAML IdP on the Service Provider's platform.
The following steps show more details on how to set up an OIDC/SAML Client Application in Authgear Portal.
Log in to Authgear Portal, then click on Applications from the navigation menu.
Click on Add Application to create a new client application. Or select an existing client application with the OIDC/SAML Client type.
Enter a Name for the application and select OIDC/SAML Client Application as the Application Type.
Click Save to proceed.
By default, the SAML 2.0 Configuration is disabled for the client application.
Click on the SAML 2.0 tab then toggle SAML 2.0 Support switch to enable SAML 2.0.
You'll be required to enter at least one Allowed Assertion Consumer Service URLs (ACS URLs) before you can save your changes. Hence, get an ACS URL from the Service Provider you plan to use.
Visit the portal for the Service Provider you plan to use and add Authgear as an Identity Provider using the SAML configuration from your Authgear client application.
Refer to the following instructions for a generic SP:
Configuration on SP:
Enter the Identity Provider Metadata URL provided by Authgear if it's supported by the SP. e.g. https://[AUTHGEAR_ENDPOINT]/saml2/metadata/[CLIENT_ID]
If the SP does not support uploading an IDP metadata file, you can manually enter the parameters into the SP. These values can be copied from the application settings page:
Issuer: urn:[AUTHGEAT_ENDPOINT]
Login URL: https://[AUTHGEAR_ENDPOINT]/saml2/login/[CLIENT_ID]
Logout URL: https://[AUTHGEAR_ENDPOINT]/saml2/logout/[CLIENT_ID]
Identity Provider Certificates in PEM format: Download from the application settings page
Configuration on Authgear
Upload the Metadata XML file provided by your client application into the Authgear Portal
You may also manually enter the parameters into the application settings page in the Portal:
NameID Format
urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified , or
When the format is unspecified, you can choose to use the User ID, Email, Phone, or Username as the attribute value
urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
Allowed Assertion Consumer Service URLs (ACS URLs)
Response Destination (Optional)
Subject Recipient (Optional)
Assertion Audience (Optional)
Assertion Valid Duration (seconds), Default: 1200
Enable/Disable Single Logout (SLO)
SLO Callback URL
Callback Binding
urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect, or
Enable/Disable message signature verification
Upload the SP's certificate in PEM format
You may find more detailed guides for adding IdP on the Service Provider's documentation.
Online Base64 decode/encode: https://www.authgear.com/tools/base64-decode-encode
Create a project on Google Cloud Platform through console. If you are adding Authgear to your existing Google Cloud Platform projects, you may skip to the next step to create the OAuth client.
After creating a new project, you will need to configure the OAuth consent screen. Press the button on the top-left and go to APIs & Services -> OAuth consent screen and follow the instruction to create the consent screen.
Go to -> APIs & services -> Credentials
Click Create Credentials -> OAuth client ID
Choose Web application in Application type and assign a name as reference. You should always choose Web application here regardless of the platform of the app you are creating. It is because this OAuth Client ID is used by your Authgear services, which is a web application in Google’s classification.
In Authorized JavaScript origins, add your Authgear endpoint, e.g. https://myproject.authgear.cloud
In Authorized redirect URIs, add https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/google. For example, https://myproject.authgear.cloud/sso/oauth2/callback/google
After creating a client ID, you will see the client ID under the OAuth 2.0 Client IDs section of the Credentials page.
You can find more details in official Google Cloud Platform doc
After creating an OAuth client, click the name of OAuth client to view the details.
You will need the values of Client ID, Client secret to configure Google Sign In.
In the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with Google.
Fill in the Client ID and Client Secret with the values obtained from the previous step.
Save the settings.
🎉Done! You have just added Google Sign In to your apps!
Your end-users can now sign in with Google on Authgear pre-built Log In and Sign Up page. Existing end-users can connect their account to Google in the User Settings page.
A web application using the same Authgear project as authentication
First, ensure your mobile application uses an Authgear application with the Native App. Enable "preAuthenticatedURL" to allow pre-authenticated URLs to work.
authgear
.configure({
clientID: '<CLIENT_ID>',
preAuthenticatedURLEnabled: true
})Next, add an allowed origin to the web application client in Authgear.
Navigate to Advanced > Edit Config in the Authgear Portal, find the web application client and add the origins you wish to use for Pre-authentication URLs in the x_pre_authenticated_url_allowed_origins key. Also set x_pre_authenticated_url_enabled to true.
Note that the origin should be of the format "protocol (scheme) + domain + port". For example, if the mobile application wants to open https://www.mywebapp.com/home?key=value, the origin must be https://www.mywebapp.com.
The Pre-Authenticated URL is a link that the Authgear SDK can generate for a mobile client that has the Pre-Authenticated URLs feature enabled. Your mobile application can open the Pre-Authenticated URL in a web view for users to start browsing the origin in an authenticated state.
To generate the Pre-Authenticated URL, call the makePreAuthenticatedURL() method of the Authgear SDK as shown below:
The makePreAuthenticatedURL() method accepts an object as a parameter. Inside the object, you should provide your web application's client ID and web app URI.
After the makePreAuthenticatedURL() return the URL, your mobile application should open the URL in a WebView. From there, users should be able to continue their current authenticated session (from the mobile app) on the web application.
The following code sample shows how to open the pre-authenticated URL using the Browser.open() method in Ionic.
The following code sample shows how to open the pre-authenticated URL using the Linking.openURL() method of React Native.
The pre-authenticated URL is opened in the browser via the native app. In the web application, trigger authentication with the injected SSO session and get the authenticated state.
In the web application, enable SSO to allow pre-authenticated URLs to work. You can initialize the SDK as following
And in the web application URI, trigger authentication as following. Note here prompt: PromptOption.None is used to skip the SSO continue screen.
In a normal login flow, for example the user browses the web page in the browser rather than from a link in the native app, the prompt should not be used because it will hinder the user from opening the login page. Only use this prompt when an SSO session is surely set in the browser, for instance in conjunction with this Pre-authentication URL feature.
Register a WeChat Open Platform account (微信开放平台账号).
Register a Web Application (网站应用).
See Appendix: Create web app on WeChat Open Platform for more details.
Once your mobile app is approved on the platform, you will see the word "✅ 已通过" in the app details page.
Get the appid (Client ID)
Get the appsecret (Client Secret). It will only be shown once. You need to re-generate if you lose it.
Get the 原始ID (Account ID) of your WeChat Open Platform account.
Sign in to the Authgear portal.
Select your project.
In the navigation menu, go to Authentication > Social / Enterprise Login.
Click Add Connection.
Select WeChat Web / 网站应用.
Fill in Client ID with the appid.
Fill in Client Secret with the appsecret.
Fill in Account ID with the 原始ID.
Save.
No further changes are needed. The Sign in with WeChat button should be shown in the signup / login page now.
After logging into the Open Platform, go to the "网站应用" (Web App) and click "创建网站应用" to create a new web app
The following information are needed:
网站应用名称
Web app name
The app name shown to the end-user when they login
英文名称
Web app name in English
The app name shown to an English end-user when they login
网站应用简介
Web app description
A description for the approver to understand the app
英文简介
Mobile app description in English
Register an application by completing Quickstart: Register an application with the Microsoft identity platform
Choose "Supported account type", the following options are supported:
Accounts in this organizational directory only (Contoso AD (dev) only - Single tenant)
Accounts in this organizational directory (Any Azure AD directory - Multitenant)
Accounts in this organizational directory (Any Azure AD directory - Multitenant) and personal Microsoft accounts (e.g. Skype, Xbox)
"Personal Microsoft accounts only" is not supported yet. Remember the account type chosen as this affects the configuration on Authgear portal
Configure "Redirect URI" with https://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/azureadv2
Follow this section to add a client secret. Remember to record the secret value when you add the client secret, as it will not be displayed again. This will be needed for configure OAuth client in Authgear.
In the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with Microsoft
Fill in Client ID with Application (client) ID of your just created Azure AD application.
Fill in Client Secret" with the secret you get after creating a client secret for your Azure AD application.
For Tenant field:
If single tenant (first option) is chosen, fill in the Directory (tenant) ID of your Azure AD application.
If multi tenant (second option) is chosen, fill in the string literal organizations.
Save the settings.
🎉 Done! You have just added Azure Active Directory (Azure AD) Login to your apps!
Azure Active Directory automatically logs in to the same account without requiring a username and password. To prevent this behaviour, you can use the prompt=login parameter to force Azure Active Directory to show the login page. See our guide on using the prompt=login parameter in Authgear SDKs to learn more.
Navigate to Authentication > Login Methods.
Select your Login Method. The login method selected determines the options available to customize.
Click on the Passwords tab to reveal the settings.
Note: Make sure the login method you select has password enabled (you can not view the password settings screen if you only enable Passwordless login).
Navigate to Authentication > 2FA. You will be able to view the password settings if you enable "Additional Password" as a 2nd-factor authentication.
Please note that it is not recommended to use a password for both primary and secondary authentication at the same time.
AI-assisted IDEs like Cursor and Windsurf are increasingly popular among developers for enhancing productivity. These tools offer LLM-based agents for code suggestions, debugging, and understanding codebases.
Now, you’ve created an innovative software project consisting of a frontend application and a backend server. By leveraging generative AI with the right prompts, you can integrate robust security features into your project within seconds.
First, create an account and a project in the the Authgear portal.
In the project creation wizard, choose how your users will perform signup and login. For example:
By email with a password
By receiving OTP via SMS or WhatsApp
Next, navigate to the “Applications” page and create an application of the type Single Page Application.
There are two values you will need for the subsequent steps:
Client ID: An ID to identify your application application with Authgear
Endpoint: The URL to identify your Authgear project and allow your application to connect to it.
Under “Authorized Redirect URIs,” add the URL of your local environment with /auth-redirect appended. For example, if your frontend application runs on port 4000, use: http://localhost:4000/auth-redirect there.
Save your changes.
To integrate login functionality into your frontend code, follow the corresponding documentation based on your framework:
React:
Vue:
Angular:
In the chat, select the documentation as context and put in the following prompt.
To show the login status in the home page, use the following prompt to change the appearance of the logged in status and add a button to the .
Run the SPA with this prompt to verify the result.
In the backend, add the following documentation as context:
Validate JWT in your application server:
Run the backend server with this prompt to verify the result.
Similarly you can prompt the chat to protect any API endpoints in the backend.
Now you have the a protected API in the backend, add a button in the frontend to test it out.
Include the corresponding frontend SPA docs to the "context" added in the previous step. Then use the following prompt to add a button the test the API call:
Run both the frontend and backend servers simultaneously. Your frontend should now feature a button that calls the protected API. Logged-in users will see their user ID retrieved successfully, while logged-out users will encounter an error message.
Using Authgear as an OpenID Connect Provider for any OIDC compatible applications for Single Sign-On.
If your application supports logging in using an OpenID Connect provider, you can use Authgear as the provider.
Go to Applications on the left menu bar.
Click ⊕Add Application in the top tool bar.
Input the name and select the application type OIDC Client Application. Click "Save".
You will see a link to this guide that can help you for setting up, then click "Next".
In the URIs section, fill in the Authorized Redirect URIs with your application's redirect uri.
Obtain the OpenID Connect configuration:
You can obtain the Client ID and Client Secret from the Basic Info section.
You can obtain the OIDC Endpoints from the Endpoints section.
Provide the OpenID Connect configuration to your application.
🎉 Done! You should be able to use Authgear to log in to your application.
In this section, we are going to demonstrate how to use Authgear as the OIDC provider for WordPress login.
Follow the previous section () to setup an OIDC Client Application.
We are going to use plugin . Or you can use any other OIDC compatible plugin. Download and activate it in your WordPress site.
Go to Setting > OpenID Connect Client.
Authenticate the incoming HTTP requests by forwarding Authentication to Authgear Resolver Endpoint
In this section, we will explain how to set up a reverse proxy in NGINX to protect your app server from unauthorized access with the Authgear resolver. You can forward the requests without the request body to the resolver endpoint. Authgear will look at the Authorization and Cookie in the HTTP header, verify the token, and respond to HTTP 200 with X-Authgear- headers for session validity, the user id...etc.
If you use a popular reverse proxy on your deployment, such as NGINX, Traefik, or API Gateways such as Apache APISIX, you can configure it with a few simple lines of forward auth config. Your backend should read the returned headers to determine the identity of the user of the HTTP request.
You can also use the forward authentication features of the other popular reverse proxy. e.g.
Authgear provides an endpoint for forward authentication. Subrequests should be made to the following endpoint for authentication.
https://<your_app_endpoint>/_resolver/resolve
After the user is logged in, send an application request to your server from the client app with access token/cookies.
Set up a reverse proxy in your infrastructure to authenticate HTTP requests. The reverse proxy will forward the incoming HTTP requests without the request body to the Authgear Resolver Endpoint.
Authgear resolver parses the access token and returns HTTP headers including the user login state. The headers are starting with x-authgear-.
There are so many reverse proxies available in the wild. So here we are going to illustrate the idea of using Nginx as the reverse proxy.
We will use the module auth_request in NGINX. The module is not built by default, it should be enabled with the --with-http_auth_request_moduleconfiguration parameter.
Run this command and verify that the output includes --with-http_auth_request_module:
The trick here is to declare an internal location and use auth_request to initiate a subrequest to the resolved endpoint.
If the reverse proxy, Authgear, and your backend server are in different regions, authenticating every request could result in a huge downgrade in the performance.
You may consider enabling caching.
See the list of x-authgear- headers in the specs:
Learn how to take users directly to an external OAuth provider's authorization page without opening AuthUI login page.
You can use Authgear's x_oauth_provider_alias parameter to add social/enterprise login to your application without showing any AuthUI pages. To do this, you must enable the Social/Enterprise only login method for your project in Authgear Portal.
In this post, you'll learn how to use the x_oauth_provider_alias parameter to skip AuthUI and take users directly to a social/enterprise login provider's authorization page.
An Authgear account. Create one for free .
In this post, we'll walk through the steps for adding only the social/enterprise login method to an Authgear application.
We'll use the Authgear SDK for React Native to set the x_oauth_provider_alias parameter and show how to use x_oauth_provider_alias without the SDK in an example Express app.
The sequence diagram above demonstrates the flow for using x_oauth_provider_alias to skip AuthUI.
First, when the user clicks on the sign-in button, your application will call your Authgear project's authorize endpoint with the x_oauth_provider_alias parameter appended.
Next, when Authgear server receives the call, it redirects to the third-party OAuth (Social/EnterpriseLogin) provider's authorization server. The user is then shown the OAuth provider's login/authorization page for them to grant authorization. Once that is done, the OAuth provider returns an authorization code to Authgear.
In the next step, Authgear exchanges the authorization code for an access token, refresh token, and ID token and then starts creating a new user or logging the existing user in.
The rest of the flow from there involves the usual sending of the authorization code to the client application and the client application exchanging the authorization code for an access token, refresh token, and ID token.
The first step is to add the Social/Enterprise login provider you wish to use to your Authgear project. For our example, we'll be adding Facebook.
To add a new provider, log in to Authgear Portal, select your project, then navigate to Authentication > Social/Enterprise Login.
Next, click on the Edit button, then enter the Client ID and Client Secret for the Social/Entreprise login provider then click Save. Also, note the value for Alias as you'll use it in a later step.
See our guide for instructions on how to get a Client ID and Client Secret for Facebook Login.
An important step for making Authgear to skip AuthUI is to enable the Social/Enterprise only login method. By doing this, Authgear will understand that the only login method your app will use is from a third-party OAuth provider. As a result, it's ok to skip showing AuthUI for login, registration, or login method selection and go to the OAuth provider's authorization page directly.
To enable Social/Enterprise only, navigate to Authentication > Login Methods. Next, select the Social/Enterprise only Login Method and click Save.
Now that you've set up everything to allow your application to use only Social/Enterprise Login, you can open Authgear's authorize endpoint with the x_oauth_provider_alias parameter to start an authorization request that will skip AuthUI.
We will show 2 ways to do this. The first is using the SDK and the second is by passing x_oauth_provider_alias as a URL query parameter.
The following example shows how to add x_oauth_provider_alias using the Authgear React Native SDK:
The key thing about using the above option is the presence of oauthProviderAlias: 'facebook' in the authenticate() method of the Authgear SDK. This parameter tells Authgear to redirect directly to an OAuth provider, given that the Social/Enterprise provider is configured properly as shown in . Also, the Social/Enterprise only Login method is enabled.
Note that the value for oauthProviderAlias must be the Alias for the social/enterprise provider you configured in step 1.
You can manually add x_oauth_provider_alias parameter to the Authgear authorization endpoint when you're not using the Authgear SDK.
The following example shows how to add x_oauth_provider_alias to the Authgear authorization endpoint:
The above code will append &x_oauth_provider_alias=facebook to the authorization URL.
Learn how to update a User profile's custom attributes on sign-up using Hooks
Using you can put extra information into the user profile's programmatically. This is useful for where making your current customer data better by adding more details from outside sources.
Here are easy steps to achieve this:
Step 1. Make sure that you have an Authgear account. If you don't have one, you can on the Authgear website. Start by logging into your .
Step 2. Go to User Profile → Custom Attributes page.
Step 3. Add 3 new attributes there, namely city, name, and timezone:
Guide on how to add Two-Factor Authentication to your application.
Authgear supports Two-Factor Authentication (2FA) or Multi-Factor Authentication (MFA) for additional layers of security in your application.
When you enable MFA on your application, Authgear will require your users to present two or more factors in order to log in. These factors could be their password and a One-time Password (OTP) that is sent to their registered email address or phone number. As a result, an attacker can not gain access to a user's account with only a compromised password.
In this post, you'll learn how to enable MFA or 2FA for your Authgear project and how to configure 2FA grace period.
const url = await authgear.makePreAuthenticatedURL({
webApplicationClientID: "YOUR_WEB_APP_CLIENT_ID", // Replace with you web app client id
webApplicationURI: "YOUR_WEB_APP_URI", // Replace with you web app uri
});Browser.open({ url: url }).catch(err =>
console.error("Couldn't load page", err),
);Linking.openURL(url).catch(err =>
console.error("Couldn't load page", err),
);import authgear, { PromptOption } from "@authgear/web";
authgear.configure({
endpoint: "AUTHGEAR_ENDPOINT",
clientID: "CLIENT_ID",
sessionType: "refresh_token",
isSSOEnabled: true
});import authgear, { PromptOption } from "@authgear/web";
authgear.startAuthentication({
redirectURI: import.meta.env.VITE_AUTHGEAR_REDIRECT_URL,
prompt: PromptOption.None // use "None" to skip the continue screen
})
.then(
() => {
// started authentication, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
}
);oauth:
clients:
- client_id: <Client ID of the web app>
x_pre_authenticated_url_enabled: true
x_pre_authenticated_url_allowed_origins:
- <origin 1>
- <origin 2>
- ...
...If multi tenant and personal account (third option) is chosen, fill in the string literal common.
/.well-known/openid-configurationhttps://<YOUR_AUTHGEAR_ENDPOINT>/sso/oauth2/callback/adfsIn the portal, go to Authentication > Social / Enterprise Login.
Enable Sign in with Microsoft AD FS.
Fill in Client ID, Client Secret and Discovery Document Endpoint.
Save the settings.
🎉 Done! You have just added Microsoft AD FS Login to your apps!
Microsoft AD FS supports the prompt=login parameter. You can include this parameter in your request when you want users to re-authenticate. See our guide on using the prompt=login parameter in Authgear SDKs to learn more.












Totally ignore the Advance password strength score and use the Basic password policy. E.g. Minimum password length.
Extremely guessable
0
Too guessable: risky password. (guesses < 10^3)
Very guessable
1
Very guessable: protection from throttled online attacks. (guesses < 10^6)
Fair
2
Somewhat guessable: protection from unthrottled online attacks. (guesses < 10^8)
Very unguessable
3
Safely unguessable: moderate protection from offline slow-hash scenario. (guesses < 10^10)
Extremely unguessable
4
Very unguessable: strong protection from offline slow-hash scenario. (guesses >= 10^10)



urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST











Optional field
应用官网
Official website of the web app
The webpage should show the description of the app
网站应用图片
App Icon
A 28x28 and a 108x108 icon
网站信息登记表扫描件
Scanned copy of the Website Registration Form
A signed registration form about the web app and the business nature and company info.
授权回调域
Authorized redirect domain
Domain of your Authgear endpoint for example: *.authgear.cloud








authgear
.configure({
clientID: '<YOUR_CLIENT_ID>',
endpoint: '<YOUR_AUTHGEAR_PROJECT_ENDPOINT>',
})
.then(() => {
authgear
.authenticate({
redirectURI: 'com.reactnativeauth://host/path',
oauthProviderAlias: 'facebook',
})
.then(({userInfo}) => {
Alert.alert('Login successful, welcome ' + userInfo.email);
});
});app.get("/login", (req, res) => {
const url = new URL("<YOUR_AUTHGEAR_PROJECT_ENDPOINT>/oauth2/authorize");
url.searchParams.set('client_id', config.client.id);
url.searchParams.set('redirect_uri', "http://localhost:3000");
url.searchParams.set('scope', "openid offline_access");
url.searchParams.set('x_oauth_provider_alias', 'facebook')
res.redirect(url);
});request should be the return value of parseApp2AppAuthenticationRequest.
This method must be called when then SDK session state is AUTHENTICATED, and the current session supported app2app authentication by providing a device_key, or else an error will be thrown.
Reject: rejectApp2AppAuthenticationRequest(request: App2AppAuthenticateRequest, error: Error)
Rejects an app2app request, returning an error through the redirect URI.
request should be the return value of parseApp2AppAuthenticationRequest.
error is the reason to reject the request.


Client ID: Obtain the Client ID from the Basic Info section.
Client Secret Key: Obtain the Client Secret from the Basic Info section.
OpenID Scope: Space separated list of scopes the plugin could access.
Example: openid offline_access https://authgear.com/scopes/full-userinfo.
https://authgear.com/scopes/full-userinfo is needed to obtain user's profile (e.g. email). Otherwise the plugin will be able to get the user id only.
Login Endpoint URL: Obtain Authorization Endpoint from the Endpoints section.
Example: https://{AUTHGEAR_APP_DOMAIN}/oauth2/authorize.
Userinfo Endpoint URL: Obtain Userinfo Endpoint from the Endpoints section.
Example: https://{AUTHGEAR_APP_DOMAIN}/oauth2/userinfo.
Token Validation Endpoint URL: Obtain Token Endpoint from the Endpoints section.
Example: https://{AUTHGEAR_APP_DOMAIN}/oauth2/token.
End Session Endpoint URL: Keep it empty.
Identity Key: Where in the user claim to find the user's identification data.
Suggest to use sub which is the user id in Authgear.
Setup the user claim keys based on your project login method setting.
If your project is using email to login
Nickname Key: Set it to email.
At the bottom of the plugin settings page, you will be able to obtain the Redirect URI. Go to Authgear portal, add the uri to the Authorized Redirect URIs.
Your backend server looks at the headers and responds to the client app accordingly. e.g. Returns the user's content or HTTP 401 if the user is not logged in.

Step 4. Navigate to your Authgear Dashboard's Advanced->Hooks section.
Step 5. Add a new Blocking Event.
Step 6. Choose the Block Hook Type as the TypeScript and set the Event option to User pre-create. You will write a new Typescript function from scratch.
Step 7. Click on Edit Script under the Config option.
Step 8. Write a function logic for how you integrate any external API to populate custom attributes into the editor. For example.
Step 9. Now if you navigate to User Management and Add a new user.
Step 10. After the user is created, you should able to see custom attributes values have been updated for the user:
Once you learned how to update user profiles, now you can discover different ways of accessing user profiles in Authgear.
An Authgear account. Create one for free here.
An Authgear Project.
And basic experience getting started with Authgear.
You can enable 2FA and configure other settings from the 2-Factor Authentication page in Authgear Portal.
To open the 2-Factor Authentication page, log in to Authgear Portal, select your project, then navigate to Authentication > 2FA.
Next, use the 2FA Requirements dropdown on the 2-Factor Authentication page to set when to require users to use 2-Factor Authentication to sign in.
The available options are:
Disabled: When this is selected, 2FA will not be required to log in for any user, including users who already have 2FA set up for their account.
Optional: This policy will only require 2FA to log in for users who already have 2FA set up for their account. Users who have not set up 2FA can continue to log in without it.
Mandatory: Use the mandatory policy to require 2FA for all users. That means users who have not set up 2FA will not be able to log in if no grace period is set. To use this option, consider further actions like setting up a grace period for rollout.
Toggle the Show "Do not ask again on this device" for 2FA switch on if you wish to require 2FA only the first time a user logs in from a specific device.
The Available 2-Factor sub-section on the 2-Factor Authentication page shows a list of supported second-factor authentication methods. The supported methods include:
Google Authenticator/Authy
Additional Password
OTP Code/Login Link via Email
OTP Code via Phone
Check the box for each 2FA method you wish to enable for your project.
Use the up and down allows on the right of each method to order the priority of the 2FA methods.
Once you're done, click on the Save button at the top-left of the 2-Factor Authentication page to keep your new settings.
The 2FA Grace Period feature grants your users some time to set up 2FA for their accounts. This is very helpful for the Mandatory enforcement of 2FA.
The following are the two types of 2FA grace periods you can set for your Authgear project:
Global Grace Period: When this type of grace period is enabled, all users who do not have 2FA set up for their account will be asked to set up 2FA the next time they log in. When the Global Grace Period is disabled, users who have not set up 2FA for their account cannot log in. Instead, they'll get an error message requesting them to contact an admin.
Individual Grace Period: This is a type of grace period that is set per user. It grants a user 10 days to set up 2FA for their account. This is ideal for allowing individual users to set up 2FA when the Global Grace Period is disabled.
The following steps show how to roll out Mandatory 2FA using grace periods:
Change 2FA requirement policy to Mandatory
Enable Global Grace Period so that all users who haven't set up 2FA are required to do so the next time they login.
Use your own channel to notify user's about the duration of the global grace period you've decided.
Disable the Global Grace Period once the date you notified users of has passed. After you do this, users that still haven't set up 2FA will be unable to log in.
When users that could not set up their 2FA during the Global Grace Period contact you (the admin), enable individual grace period for them using the instructions in .
To enable the Global Grace Period, navigate to Authentication > 2FA in the Authgear Portal. Then, set 2FA Requirements to Mandatory so that you can view the Enable global grace period switch.
Toggle the Enable global grace period switch on so that your users without 2FA will be required to set up 2FA the next time they log in. Or set Enable global grace period off, if you do not want users without 2FA to log in, or set up 2FA without contacting an admin.
When you set the 2FA requirement for your project to Mandatory and Global Grace Period is turned off, you can still use the individual grace period to grant a specific user a grace period to set up 2FA for their account.
To set individual grace period, navigate to User Management > User in Authgear Portal. Then, select the user you wish to set individual grace period for by clicking on the row with their ID in your project's users' list.
From the selected user's details page, click on the Account Security tab, then the Grant grace period to set up 2FA button. You will see a prompt to confim your action, click Confirm to continue.
The duration of the individual grace period is 10 days. However, you can extend or cancel it from the user's details page.
The Authgear Android SDK comes with kotlin support out of the box. In fact, the SDK is written in kotlin!
If you are using kotlin, you can benefit from the suspend function APIs authgear provides. For example, the above authorize example can be written as follows:
import kotlinx.coroutines.*
class MyAwesomeViewModel(application: MyAwesomeApplication) : AndroidViewModel(application) {
// Other methods
// This is called when login button is clicked.
fun login() {
viewModelScope {
withContext(Dispatchers.IO) {
try {
val app = getApplication<MyAwesomeApplication>()
val state = app.authgear.authenticate(AuthenticateOptions(redirectUri = "com.myapp://host/path"))
// User is logged in!
} catch (e: Throwable) {
// Something went wrong.
}
}
}
}
}Requiring users to reset their password if they haven't logged in after specific number of days
You can set up your Authgear project such that a user's password expires after a specific number of days. When a user logs in after the password expiry date, they'll see a prompt to change their password before they're redirected back to your app.
Navigate to the password settings tab and scroll to the Password Expiry section. Toggle the "Force password change on next login if it has expired" button to enable password expiry.
You can use the field Force change since last update (days) to specify the number of days after which a user's password should expire.
For example, setting the value to 90 means the user's password will expire 90 days after the day they set or updated their password.
Once you're done, hit the Save button to keep your changes.
Learn how to track a user that signs up from a particular source or campaign.
In this guide, you'll learn how to track users from a particular source before and after they sign up. For example, knowing how many people sign up for your application through a signup link that you have included in a blog post or an email campaign.
To follow this guide, you need to have the following:
A free Authgear account.
Learn how to integrate popular analytics and tracking tools into your Authgear project using Google Tag Manager
Authgear allows you to add third-party user analytics tools to your project using Google Tag Manager.
Google Tag Manager (GTM) is a tag management tool from Google that makes it easy to add marketing tags to your website without modifying the site's source code.
Tags can help you track traffic and user behavior on your website or application.
In this guide, we will show you how to add Google Tag Manager to your Authgear project and send data to Google Analytics. You can also configure Google Tag Manager to send data from your Authgear project to other marketing tags from providers like Facebook.
$ nginx -V 2>&1 | grep -- 'http_auth_request_module'server {
# Use variable in proxy_pass with resolver to respect DNS TTL.
# Note that /etc/hosts and /etc/resolv.conf are NOT consulted if resolver is used.
# See https://www.nginx.com/blog/dns-service-discovery-nginx-plus/
resolver 8.8.8.8;
# Location that requires request authentication
location / {
set $backend http://www.mycompany.com;
proxy_pass $backend;
proxy_set_header Host $host;
# Specify the auth_request directive to initiate subrequests to the to the internal location.
# This corresponds to the Step 2.
auth_request /_auth;
# Copy the `x-authgear-*` headers from the response of the subrequest to Nginx variables.
# This corresponds to the Step 3.
auth_request_set $x_authgear_session_valid $upstream_http_x_authgear_session_valid;
auth_request_set $x_authgear_user_id $upstream_http_x_authgear_user_id;
auth_request_set $x_authgear_user_anonymous $upstream_http_x_authgear_user_anonymous;
auth_request_set $x_authgear_user_verified $upstream_http_x_authgear_user_verified;
auth_request_set $x_authgear_session_acr $upstream_http_x_authgear_session_acr;
auth_request_set $x_authgear_session_amr $upstream_http_x_authgear_session_amr;
auth_request_set $x_authgear_session_authenticated_at $upstream_http_x_authgear_session_authenticated_at;
auth_request_set $x_authgear_user_can_reauthenticate $upstream_http_x_authgear_user_can_reauthenticate;
# Include the headers in the request that will be sent to your backend server.
# This corresponds to the Step 4.
proxy_set_header x-authgear-session-valid $x_authgear_session_valid;
proxy_set_header x-authgear-user-id $x_authgear_user_id;
proxy_set_header x-authgear-user-anonymous $x_authgear_user_anonymous;
proxy_set_header x-authgear-user-verified $x_authgear_user_verified;
proxy_set_header x-authgear-session-acr $x_authgear_session_acr;
proxy_set_header x-authgear-session-amr $x_authgear_session_amr;
proxy_set_header x-authgear-session-authenticated-at $x_authgear_session_authenticated_at;
proxy_set_header x-authgear-user-can-reauthenticate $x_authgear_user_can_reauthenticate;
# Your backend must inspect the request headers to determine whether the request is authenticated or not.
# This corresponds to the Step 5.
}
location = /_auth {
# Set this location for internal use only
internal;
# Replace <YOUR_AUTHGEAR_ENDPOINT> with your authgear endpoint.
# For example, https://example.authgear.cloud
set $resolver <YOUR_AUTHGEAR_ENDPOINT>/_resolver/resolve;
proxy_pass $resolver;
# Set the host so that authgear knows which app is calling the resolver endpoint
# Replace <YOUR_AUTHGEAR_ENDPOINT_HOST> with the host of your authgear endpoint.
# For example, example.authgear.cloud
proxy_set_header Host <YOUR_AUTHGEAR_ENDPOINT_HOST>;
# The body is supposed to be consumed by your backend server.
# Pass only the headers to the resolver
proxy_pass_request_body off;
proxy_set_header Content-Length "";
}
}http {
# ...
proxy_cache_path /tmp/cache keys_zone=auth_cache:10m;
# The server block.
server {
# ...
location = /_auth {
# ...
proxy_cache auth_cache;
proxy_cache_key "$cookie_session|$http_authorization";
proxy_cache_valid 200 10m; # Adjust cache duration as desired.
}
}
}
export default async function(e: EventUserPreCreate): Promise
{
// API Key for IP Geolocation
const apiKey = 'MY_API_KEY';
// Any random IP address
const ipAddress = '8.8.8.8'
// Fetch data from the IP Geolocation API
const response = await fetch(`https://api.ipgeolocation.io/ipgeo?apiKey=${apiKey}&ip=${ipAddress}`);
const data = await response.json();
return {
is_allowed: true,
mutations:{
user: {
custom_attributes: {
"city": data.city,
"country": data.country_name,
"timezone": data.time_zone.name
}
}
},
};
}Use `@authgear/web` package, Integrate Authgear as Authentication provider
Store these in .env for initializing Authgear:
- Authgear Client ID is [CLIENT ID]
- Authgear Endpoint is [Authgear Endpoint]
- Redirect URL is http://localhost:4000/auth-redirectWhen logged in, show user id (sub) in user info, a logout button and a User settings button in the Home page
User Settings page is opened by `authgear.open(Page.Settings);`Run dev frontend server at port 4000# Use JWKS to verify the JWT
**Find the JWKS Endpoint**
Use the following method to get the JWKS URI (you'll need to URI to extract the public signing key from a JWT).
```
const appUrl = ""; //place your authgear app endpoint here
const getJwksUri = async (appUrl) => {
const config_endpoint = appUrl + "/.well-known/openid-configuration";
const data = await axios.get(config_endpoint);
return data.data.jwks_uri;
}
```
**Extract JWT from Request Header**
Use the following code to extract only the token part from a `Bearer [token]` authorization header in your Express app:
```
const express = require("express");
const axios = require("axios");
const node_jwt = require('jsonwebtoken');
const jwksClient = require('jwks-rsa');
const app = express();
const port = 3002;
app.get('/', async (req, res) => {
const requestHeader = req.headers;
if (requestHeader.authorization == undefined) {
res.send("Invalid header");
return;
}
const authorizationHeader = requestHeader.authorization.split(" ");
const access_token = authorizationHeader[1];
}
```
**Decode Access Token**
Next, decode the access token so that you can extract the JWT `kid` from the result. You'll need this `kid to get the public signing key. Use the following code to decode the JWT:
```
const decoded_access_token = node_jwt.decode(access_token, {complete: true});
```
**Get JWT Signing Keys and Verify the JWT**
Use the following code to extract the JWT public keys then verify the JWT using the keys:
```
const jwks_uri = await getJwksUri(appUrl);
const client = jwksClient({
strictSsl: true,
jwksUri: jwks_uri
});
const signing_key = await client.getSigningKey(decoded_access_token.header.kid);
try {
const verify = node_jwt.verify(access_token, signing_key.publicKey, { algorithms: ['RS256'] });
res.send(JSON.stringify(verify))
}
catch(error) {
res.send(error);
}
```In the backend, create a protected api `/me`,
When user access with a JWT access token issued by Authgear, return the user id, if not, return 401 unauthorized errorRun dev backend server at port 3000In the frontend, show a button to test the protected api `/me` both before and after logout. Use the `authgear.fetch("URL")` to call the API.Email Formatting: Set it to {email}.
If your project is using phone to login
Nickname Key: Set it to phone_number.
Email Formatting: Clear it.
If your project is using username to login
Nickname Key: Set it to preferred_username.
Email Formatting: Clear it.





An application in the Authgear Portal and note down the configuration of the application.
A client application that is written in your preferred language or framework.
For this guide, we'll build a demo Express application that has the following features:
Read a source URL parameter defined by you (the developer).
Send the value of the source parameter to the Authgear authorization server using the OAuth 2.0 state parameter.
Read the value of state returned after user authorization (sign up) and log the value in a database or analytics system like Mixpanel.
The OAuth 2.0 framework includes an optional state parameter. The value of the state parameter can be any random string or number defined by a client application (e.g a web or mobile that uses Authgear for user authentication) before the client makes an authorization request. In simple terms, the state parameter is added to the authorization URL as a URL query.
The authorization server (Authgear) will include the same state parameter value when redirecting the user-agent back to the client application. As a result, the client application can retrieve the value of state returned to verify that it is the origin of the authorization request.
We will use the above behavior of the authorization process to track a user before and after they sign up.
The following steps show the steps for building a simple application that is capable of tracking users before and after they sign up.
First, create a new project directory and open it. The demo application for this guide is a simple Express application that use Axios to make HTTP requests. Hence, install both packages using the following commands:
1. Express:
2. Axios:
Next, inside the project directory, create a new app.js file then add the following code to the file:
You can get the correct configuration values (CLIENT_ID, CLIENT_SECRET, REDIRECT_URL, and AUTHGEAR_ENDPOINT) from the Applications section of the Authgear Portal.
In this step, we'll implement a /login route in the demo application. This route will support a source query parameter, for example, /login?source=002.
Add the following code to the end of app.js to implement the /login route:
The above code will check if the source parameter is included in the HTTP request to the /login route. If there is a source parameter, the value of the source will be added to the authorization URL's state parameter.
The following is an example of a login URL that includes the source parameter:
As described earlier, Authgear will return whatever value you put in the state parameter of the authorization URL. In the last step, we will read the value of the source parameter from the /login route and pass it to the state parameter. In this step, we'll read the state parameter that Authgear returns in the redirect URI for the initial value we passed (source).
To do this, we'll add a / route to resolve our redirect URI. Add the following code to the end of app.js to implement the route:
The sourceFromState constant holds the value for the state parameter in the redirect URI. You can save this value to a database to track that the user has successfully signed up using the link with the source value in your original campaign link. You may also send this link to an analytic tool like Mixpanel to track the user and source.
To run the demo app, run the following command in the terminal:
Then, open http://localhost:3000/login?source=002 on a browser. You can change 002 to any random string that you wish to use for tracking a source or campaign. Also, be sure to add http://localhost:3000 as a redirect URL for your application in the Authgear Portal.
npm install expressnpm install axiosconst express = require('express');
const axios = require('axios');
const app = express();
const port = process.env.PORT || 3000;
const config = {
client: {
id: "CLIENT_ID",
secret: "CLIENT_SECRET",
redirect_url: "REDIRECT_URL"
},
auth: {
tokenHost: "AUTHGEAR_ENDPOINT",
tokenPath: '/oauth2/token',
authorizePath: '/oauth2/authorize',
scope: 'openid offline_access'
},
};app.get("/login", (req, res) => {
const url = new URL(`${config.auth.tokenHost}${config.auth.authorizePath}`);
url.searchParams.set('client_id', config.client.id);
url.searchParams.set('redirect_uri', config.client.redirect_url);
url.searchParams.set('response_type', 'code');
url.searchParams.set('scope', config.auth.scope);
if (req.query.source != null) {
url.searchParams.set('state', req.query.source);
}
res.redirect(url);
});http://localhost:3000/login?source=002app.get("/", async (req, res) => {
if (req.query.code != null) {
const data = {
client_id: config.client.id,
client_secret: config.client.secret,
code: req.query.code,
grant_type: 'authorization_code',
response_type: 'code',
redirect_uri: config.client.redirect_url,
scope: config.auth.scope
};
const sourceFromState = req.query.state;
try {
const getToken = await axios.post(`
${config.auth.tokenHost}${config.auth.tokenPath}`,
data,
{
headers: { "Content-Type": "application/x-www-form-urlencoded" }
}
);
const accessToken = getToken.data.access_token;
res.send(`
<p>Access token: ${accessToken}, ${sourceFromState}</p>
`);
} catch (error) {
res.send("An error occurred! Login could not complete. Error data: " + error);
}
}
else {
res.send(`
<div style="max-width: 650px; margin: 16px auto; background-color: #EDEDED; padding: 16px;">
<p>Hi there!</p>
<p>This demo app shows you how to add user authentication to your Express app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<a href="/login">Login</a>
</div>
`);
}
});
app.listen(port, () => {
console.log(`server started on port ${port}!`);
});node app.jsHow to enable Email based login.
Add sign-up and login features to Spring Boot App.
Before you get started, you will need the following:
Java 17 or higher.
A free Authgear account. Sign up if you don't have one already.
To use Authgear services, you’ll need to have an application set up in the Authgear Dashboard. The Authgear application is where you will configure how you want authentication to work for the project you are developing.
Use the interactive selector to create a new Authgear OIDC Client application or select an existing application that represents the project you want to integrate with.
Every application in Authgear is assigned an alphanumeric, unique client ID that your application code will use to call Authgear APIs through the Spring Boot OAuth 2 Client. Note down the Authgear issuer (for example, https://example-auth.authgear.cloud/), CLIENT ID, CLIENT SECRET, and OpenID endpoints from the output. You will use these values in the next step for the client app config.
A Redirect URI is a URL in your application that you would like Authgear to redirect users to after they have authenticated. In our case, it will be a home page for our Spring Boot App. If not set, users will not be returned to your application after they log in.
To follow the example in this post, add the following URL as a redirect URI:
After you create the Authgear app, you choose how users need to authenticate on the login page. From the “Authentication” tab, navigate to “Login Methods”, you can choose a login method from various options including by email, mobile, or social, just using a username or the custom method you specify. For this demo, we choose the Email+Passwordless approach where our users are asked to register an account and log in by using their emails. They will receive a One-time password (OTP) to their emails and verify the code to use the app.
To create a new Spring Boot application you use the Spring Initializr. Then you add dependencies to pom.xml file such as spring-boot-starter-oauth2-client starter provides all the Spring Security dependencies needed to add authentication to your web application and Thymeleaf is used just to build a single page UI.
Spring Security makes it easy to configure your application for authentication with OIDC providers such as Authgear. We need to add the client credentials to the application.properties file with your Auhgear provider configuration. You can use the sample below and replace properties with the values from your Authgear app:
To enable user login with Authgear, create a class that will provide an instance of SecurityFilterChain, add the @EnableMethodSecurity annotation, and override the necessary method:
We create a simple home.html page using Thymeleaf templates. When a user opens the page running on http://localhost:8080/, we show the page with buttons for login or logout:
Next, we create a controller class to handle the incoming request. This controller renders the home.html page. When the user authenticates, the application retrieves the user's profile information attributes to render the page.
To run the application, you can execute the mvn spring-boot:run goal. Or run from your editor the main ExampleApplication.java file. The sample application will be available at http://localhost:8080/.
Click on the Login button to be redirected to the Authgear login page.
You can also customize the login page UI view from the Authgear Portal. After you sign up, you will receive an OTP code in your email to verify your identity.
And log into your new account, you will be redirected back to the home page:
You have successfully configured a Spring Boot application to use Authgear for authentication. Now users can sign up for a new account, log in, and log out. The full source code of the examples can be found on GitHub.
There is so much more you can do with Authgear. Explore other means of login methods such as using Magic links in an email, social logins, or WhatsApp OTP. For the current application, you can also add more users from the Authgear portal.
In order to setup Google Tag Manager and Google Analytics with Authgear, you need to have the following:
Authgear account
Google Tag Manager Account
Google Analytics Account
The process for connecting your GTM account to Authgear is simple and can be done in these two steps.
Google Tag Manager lets you create containers that hold marketing tags. Each container has a unique ID and you'll need this container ID to connect your GTM container to Authgear.
To get the container ID, log in to GTM and navigate to the dashboard's homepage. You should find a list of all your containers and their ID. Note down the ID for the container you wish to connect to Authgear.
If you don't have a container for your Authgear project yet, click on Create Account to create a new container. Enter your domain name for your Authgear project as the container name and select a target platform. For this example, we'll select Web as the target platform.
First, log in to the Authgear Portal, then select your project and navigate to Integrations.
Click on the Connect button next to the Google Tag Manager addon to open the configuration page.
Paste the GTM container ID you got from the previous step then click the Save button. And with that, you've successfully connected your GTM container to Authgear. In the next steps, we'll show you how to create tracking tags and send data to Google Analytics.
Google Analytics is one of the marketing tags we can manage from GTM. In this part of the guide, we'll set up some tags to track page views and user events like clicking on a link or button. The tags will send these data to Google Analytics.
In order to create tags that send data to Google Analytics, you need to have an active data stream on Google Analytics. GTM requires the details for this stream while creating new tags for Google Analytics.
To create a stream, log in to Google Analytics then navigate to the Admin settings page.
Create a new Google Analytics property for your Authgear project or select an existing one. Click on the Data Streams item under the property to view all streams and add a new web stream for your Authgear project.
Note down the Measurement ID for your stream as we'll be using it later to create new tags.
Before we start sending data to Google Analytics, let's create a new variable in Google Tag Manager.
Go back to GTM and select the correct container for your project.
Next, click on the Variables item on the left side navigation bar and create a new user variable with the following details:
Variable type: Data Layer Variable
Data Layer Variable Name: gtm.element.dataset.authgearEvent
Once you're done save the variable as "gtm.element.dataset.authgearEvent" and continue to the next step.
Navigate to Triggers from the sidebar and create a new trigger with the following details:
Trigger type: Click > All Elements
This trigger fires on: Some Clicks
Authgear's implementation of GTM is declarative. The primary button on each page has data-authgear-event attribute. We'll be setting a condition for the "Some Clicks" using that attribute. Configure Some "Click" as shown below:
Next, save the trigger as "Authgear-btn-click" and continue.
Navigate to Tags from the sidebar and create a new tag with the following configurations:
Tag type: Google Analytics > Google Tag
Tag ID: <Your Tag ID is the unique Measurement ID for your stream in Google Analytics (See part 2 step 1 for more details)>
Next, expand the Advanced Settings section and set Tag firing options to Once per page.
Now, scroll down to the Trigger section of the new tag and select All Pages (page view) as the trigger.
Save this new tag as "Auth-gear-pageview" and continue.
In this step, create another tag with the following configuration:
Tag type: Google Analytics > Google Analytics: GA4 Event
Measurement ID: <Your Google Analytics stream measurement ID>
Event Name: gtm.element.dataset.authgearEvent
Next, set the trigger for this tag to the "Authgear-btn-click" trigger we created earlier.
Save the tag as "Authgear-event-tag" and continue to preview the entire setup or publish to go live.
After you publish your changes in Google Tag Manager when users generate hits or click buttons with the data-authgear-event attribute on your project you should see data on Google Analytics.
The following is a list of values for the data-authgear-event attribute:
authgear.button.change_password
authgear.button.change_additional_password
authgear.button.create_password
authgear.button.change_login_id
authgear.button.remove_login_id
authgear.button.resend_oob_otp
authgear.button.enter_oob_otp
authgear.button.enter_password
authgear.button.enter_recovery_code
authgear.button.enter_totp
authgear.button.send_reset_password_code
authgear.button.sign_in
authgear.button.sign_up
authgear.button.sign_out
authgear.button.oauth
authgear.button.reset_password
authgear.button.continue_with_current_account
authgear.button.use_another_account
authgear.button.remove_biometric
authgear.button.schedule_account_deletion
authgear.button.connect_oauth
authgear.button.disconnect_oauth
authgear.button.resend_verification_code
authgear.button.update_profile
authgear.button.regenerate_recovery_code
authgear.button.download_recovery_code
authgear.button.remove_totp
authgear.button.remove_oob_otp
authgear.button.setup_oob_otp
authgear.button.setup_totp
authgear.button.enter_verification_code
authgear.button.revoke_session
authgear.button.revoke_session_group
authgear.button.revoke_all_sessions
Configure OkHttpClient to use AuthgearInterceptor as follows:
The client would then include the access token in every request and refresh the access token when necessary before the requests.
Authgear authgear = // Obtain the authgear instance.
OKHttpClient client = new OkHttpClient.Builder()
.addInterceptor(AuthgearInterceptor(authgear))
.build()Authentication for PHP websites with Authgear and OAuth2
Using OAuth, you can use Authgear to add user authentication in a vanilla PHP application.
In this guide, we'll cover how to implement OAuth 2.0 login in a regular PHP web application with Authgear as the Identity Provider.
At the end of this post, you'll learn the following:
How to create an Authgear Application
How to enable email and password sign-in
How to sign in with Authgear from a PHP app
How to request user info from Authgear
How to use a refresh token
And finally how to log users out and revoke access tokens.
To follow along, you'll need the following:
PHP runtime (E.g XAMPP for testing offline on Windows devices)
An Authgear account. for free if you don't have an account yet.
(PHP package manager) installation
Your preferred code editor (e.g VS Code).
In this guide, we'll build a basic PHP application that lets a user sign in with their registered email and password.
The application will welcome the user with their email address after they sign in successfully. If the user is not signed in, the application will display links to Register or Login.
The following screenshot shows what the User Interface for the app will look like:
Now let's dive into the actual steps of how to add Authgear to a PHP application.
Under this section, we will cover the steps for configuring the Authgear application our PHP website will be connecting to. We'll do all these configurations in the Authgear Portal.
The first step you need to take is to create a new application or configure an existing application on the Authgear .
To do that, log in to the Authgear Portal, and select your project (or create a new one if you don't have any yet). From your project dashboard navigate to the Applications section and enter the details for your new application as shown below:
Once you're done, click on the Save button to continue. Then, click on Next to see the configuration page for your application.
The application configuration page contains basic information like Client ID and Client Secret that we'll use later in this tutorial. Hence, try to note the values down.
In addition to basic information, you can find other configuration information including endpoints and Authorized Redirect URIs.
The Authorized Redirect URIs section contains a link to the page you want Authgear to redirect users to after login.
Update the value for Authorized Redirect URIs to a page on your application. For our example PHP application the value will be http://localhost because we plan to test run it offline using XAMPP. Also, try to note this value down as we'll be using it in later steps.
Here we will cover the steps for implementing a PHP website that interacts with Authgear using the Open ID Connect (OIDC) standard.
Create a new PHP project on your computer and add an index.php file to the root of the project folder.
Add the following code to index.php to create the User Interface of the example app.
Note: The Login and Logout links in the above code currently point to login.php and logout.php respectively, we'll create both files later.
In this step, we'll add our Authgear application configuration to the PHP project.
We'll use the PHP package for the configuration.
Install the package manually from Github or via Composer by running the following command from your PHP project's root directory:
Next, after the package is installed, create a new config.php file in the PHP project folder. Add the following code to the file:
Note: Replace the values for clientId, clientSecret, redirectUri with corresponding values from the Authgear application you created in Step 1.
Including the offline_access scope is required to get a refresh token from Authgear.
The flow for Login on our app is as follows:
The user clicks on the Login button
User is redirected to the Authgear authorization page where they can sign in using email and password or any other sign-in methods you have enabled for your Authgear project.
The user is redirected back to your website with an authorization code.
In order to implement the above, you need to create a login.php file in your project's root directory. Add the following code to the login.php file:
At this point, if you try running the example app in a browser and click the Login link in index.php, your app should redirect to the Authgear login page. If you sign in successfully, you should be redirected back to the redirect URL you specified earlier in your project configuration.
Authgear will redirect to your Authorized Redirect URI with extra parameters like code or an error message in the URL. The value for the code parameter is your authorization code. In the next step, we'll use the authorization code to generate an access token.
Usually, after successful sign-in, you'll want to start using the current user's info to offer custom experience in your app.
In this step, we'll use the PHP OAuth 2.0 Client once more to interact with our Authgear app.
First, open index.php and search for the line with the following code:
Replace the above line with this code:
The above code exchanges the authorization code returned in the redirect for an access token. It then stores the access token in the PHP session so that we can use this token in future requests to protected resources.
Now that we have the access token, let's try to get the current user's details. To do that, update the HTML part in index.php like this:
Now test the app on your browser again and you should get the following page after login:
We've successfully added user authentication to our PHP app using Authgear as the identity provider. The above page displays a welcome message with the email address the user registered with on your Authgear project. You can display other info about the user from the value of $userInfo variable.
In OAuth 2.0, a refresh token is a key that's usually included in the response from the token endpoint when a client application exchanges the authorization code for an access token.
Access tokens expire after some time. Hence, we can use this refresh token to request a new access token without requiring our application users to log in again. In this step, we'll show you how to use the refresh token.
In the last step, we stored the value for the refresh token in the $_SESSION['refreshToken'] variable. So, to get the refresh token, simply read the value from that variable.
Now, add the following code to index.php to read and use the refresh token to get a new access token:
First, find the line with the following code:
Replace that line with the following blocks of code:
Note: It is required to include offline_access in your OAuth 2.0 scopes to get a refresh token from Authgear.
Authgear provides a token revoke endpoint that you can use to revoke a refresh token and all the access associated with it.
To use the token revoke endpoint to log users out of your application, create a new logout.php file in your project directory then add the following code to the file:
The above code will revoke your refresh token and delete all the session variables.
In this post, we covered how to get started with adding Authgear to a regular web app built with PHP and no framework.
We also tried out an example of using the Authgear authorization code to retrieve an access token, then we used the token to access the user info endpoint.
Here's a link complete source code for .
There's so much more you can do with Authgear and you can continue learning by checking out more topics on the .
Allow guest users to use your apps and website and promote to regular users later.
You can use the Anonymous Users feature to create an anonymous user account for the guests in your apps so that they can carry out interactions just like a normal user. For example, guests can post comments and save preferences in your social platform before setting their email and password. The user session will persist even if the app has been closed.
This improves the app experience because the user does not need to set up authenticators until further down the user journey, while still enjoying most of the app features. For app developers, the ability to create and assign Anonymous Users also makes it easier to link the activities of an individual before and after sign-up.
In the portal, go to Authentication > Anonymous Users.
Turn on Enable anonymous users.
Save the settings.
This will create an Anonymous User for the session. Subsequent requests from the end-user in the session can be identified by the same sub
After "signing up" as an anonymous user, you can and see the sub of the end-user.
UserInfo
The promoteAnonymousUser function can be called to promote an anonymous user to a regular user. You'll call the function with a login ID (e.g., email, phone number) and authenticators (e.g., password). The end-user will be prompted with a sign-up page to complete the promotion. The sub of the end-user will remain the same after the promotion.
Step 1: Start the promotion flow
When the user clicks promote on your website, make a start promotion call to redirect them to the promotion page.
Step 2: Handle the promotion result
After the user promotes on the promotion page, the user will be redirected to the redirectURL with a code parameter in the URL query. In the
On Mobile SDKs, creating an anonymous user will create a key-pair. The key-pair is stored in the native encrypted store on the mobile device. The end-user can always re-login to the same anonymous user with the key-pair. Such anonymous user will become inaccessible when the encrypted store is removed.
On the Web SDK, there will be no key-pair created. Therefore, the end-user will not be able to login to the same Anonymous User after their session becomes invalid. For cookie-based authentication, it is controlled by the "idle timeout" and "session lifetime" of the Cookie. For token-based authentication, it is controlled by the "idle timeout" and "token lifetime" of the Refresh Token.
In other words, the anonymous user account lifetime is the same as the logged-in session lifetime.
To adjust the lifetime settings, change the timeouts and lifetimes in Portal > Applications accordingly.
You should create anonymous users only when necessary in the user journey to prevent creating excessive orphan accounts in your tenant.
Setting up the local development environment for websites that use cookie-based authentication.
This guide provides a simple way to bootstrap your local application that communicates with the Authgear SaaS server.
This guide is only for cookie-based authentication in local development setups. A typical scenario is developing websites. If you are developing mobile applications which use token-based authentication, you can just skip this guide and continue with it as usual.
Authgear sets a cookie in the browser inside the project domain. When running your application on localhost, the browser will not see the cookies because the website is not in the subdomain of the domain in which the cookies are set. Therefore, the browser will not be able to authenticate itself.
For local development, it is highly recommended to create a new application on Authgear before continuing to the rest of the guide.
Log in and create a new project on
Go to the Application tab in your dashboard
Add your local application domain {SUBDOMAIN}.{PROJECT_NAME}.authgear.cloud under the Allowed Origins list
hostsTo make the cookies visible to the browser, the local website domain has to be inside the domain where the cookies are set.
By adding the following line to the /etc/hosts file on the local machine, we can point the application domain name to localhost.
The browser will be able to see the auth cookies if visiting the website via this domain.
Although you can see the cookies now, the cookies have the Secure attribute set. To include them in an HTTP request, the request has to be transmitted over a secure channel (HTTPS in most browsers). Therefore, we also need to establish HTTPS connections for our browser with the server.
One quick simple way to do this is to use , you may follow the installation steps . After installing mkcert, generate a certificate with the following command:
A key file and a cert file will be generated. They will be used in the next part of the guide.
We will need an nginx server to serve the certificate and enable SSL.
Add the following config file to your nginx/conf.d directory, or mount it to a volume together with the cert and key if you are using nginx in docker.
The examples below show the nginx config files for nginx in host and nginx in docker.
In the above examples, nginx will also authenticate requests by creating sub-requests to the Authgear internal endpoint. You can learn more .
Now visit the website through https://<yourapp>.authgear.cloud, and the browser will be able to send requests with the authorization cookies.
For implementing login and logout logic in your website, please refer to .
Authentication for a Python web application
This guide demonstrates how to add authentication with Authgear to a Python web application built with the Flask framework using the Authlib OAuth library. The full source code for this sample project can be found on the GitHub repo.
You will learn the following:
How to create an app on Authgear.
How to enable Email-based login.
Add sign-up and login features to the Flask app.
Before you begin, you'll need the following:
A free Authgear account. if you don't have one already.
Make sure that 3.10 or above is installed on your machine.
Download and Install to manage project packages.
To use Authgear services, you’ll need to have an application set up in the Authgear . This setup allows users in Authgear to sign in to the Flask application automatically once they are authenticated by Authgear.
To set up the application, navigate to the and select Applications on the left-hand navigation bar. Use the interactive selector to create a new Authgear OIDC Client application or select an existing application that represents the project you want to integrate with.
Every application in Authgear is assigned an alphanumeric, unique client ID that your application code will use to call Authgear APIs through the Authlib client library in the Flask app. Record the generated Authgear Issuer Domain (for example, example-auth.authgear-apps.com), CLIENT ID, CLIENT SECRET from the output. You will use these values in Part 2 for the Flask app config.
An Authorized Redirect URI of your application is the URL that Authgear will redirect to after the user has authenticated in the Authgear to complete the authentication process. In our case, it will be a home page for our Flask and it will run at .
Set the following to the Authorized Redirect URIs field. If not set, users will not be returned to your application after they log in.
After you create the Authgear app, you choose how users need to authenticate on the login page. From the Authentication tab, navigate to Login Methods, you can choose a login method from various options including, by email, mobile, or social, just using a username or the custom method you specify. For this demo, we choose the Email+Passwordless approach where our users are asked to register an account and log in by using their emails. They will receive a One-time password (OTP) to their emails and verify the code to use the app.
Next, create a Flask application with a single page and routes for home, callback, login, and logout flows.
Start with creating a requirements.txt file in your project directory:
Run pip install -r requirements.txt from your command-line interface to make these dependencies available to the Python project.
Create a server.py file in the project directory that contains application logic. Add the necessary libraries the application uses.
Load the configuration .env file to use values such as AUTHGEAR_CLIENT_ID AUTHGEAR_CLIENT_SECRET, AUTHGEAR_DOMAIN and APP_SECRET_KEY in the app.
Configure Authlib to handle the application's authentication with Authgear based on OIDC:
When visitors to the app visit the /login route, they'll be redirected to Authgear to begin the authentication flow.
Once users complete the login process using Authgear, they will be redirected back to the application's /callback route. This route ensures that the user's session is saved, so they won't need to log in again during subsequent visits.
Refresh Token
Calling the authorize_access_token() method of the Flask Authlib package will include a refresh token in the token response, provided your Flask application has offline_access as one of the OAuth 2.0 scopes.
Authlib will also use the refresh token to obtain a new access token automatically when the current access token has expired.
Logout
The route /logout manages the user's logout process from the application. It clears the user's session within the app and momentarily redirects to Authgear's logout endpoint to guarantee a thorough session clearance. After this, users are navigated back to your home route (which we'll discuss shortly).
The home route will either display the details of a logged-in user or provide an option for visitors to sign in.
Create a new sub-directory in the project folder named templates, and create a file home.html.
Run the application from the project root directory:
python server.py
The application should now be accessible to open from a browser at .
There is so much more you can do with Authgear. Explore other means of login methods such as using in an email, , or . For the current application, you can also from the Authgear portal.
Reference on what the OAuth 2.0 parameter is and how to use it in Authgear SDK.
The OAuth 2.0 framework includes an optional state parameter. The value of the state parameter can be any random string or number defined by a client application (e.g. a web or mobile that uses Authgear for user authentication) before making an authorization request. In fact, the state parameter is added to the authorization URL as a URL query.
The authorization server (Authgear) will include the value of the state parameter when redirecting the user-agent back to the client application. As a result, the client application can retrieve the value of state returned to verify that it is the origin of the authorization request.
In this post, we'll cover some possible usage of the state parameter and how to include the state parameter in an authorization request to the Authgear server.
The following are some use cases of the OAuth 2.0 state parameter.
Because the value for the state parameter passed at the beginning of an authorization request is returned unchanged after authorization, you can use this behavior to customize the post-login or sign-up user experience.
For example, you can show users some custom messages after they sign up or log in, using a special link that was sent to them via email or SMS. The "special" thing in the link would be the value of a query parameter that can be passed in the state parameter.
Then, a client application can read the value of the state parameter and based on that, determine when and how to display the custom message or user experience.
Another possible use of the state parameter is analytics and tracking user behavior. You can use the state token to include a unique key that tracks your campaigns. This way, you can know the number of users who sign up or log in to your application from a particular campaign.
You can also use the value you specify in the state parameter in an analytic tool (for example, as id in the identify(id) function) to track user's behavior pre-login and post-login.
To learn more about using the state parameter for tracking user behavior, see our detailed guide .
Cross-site Request Forgery or short CSRF is a type of web security vulnerability where the attacker uses malicious means to trick a user into performing undesired actions on sites they use and trust. This type of attack usually targets users who are signed in and attempts to compromise access to their protected resources.
In OAuth, an attacker can perform a Cross-site Request Forgery using the client application's redirect URI. The attacker can trick a user into using a redirect URI that contains their authorization code or access token. Hence the user will end up using the access token and protected resources of the attacker. When they save new data using this access token, the attacker can also view them (as they are the original owner of the protected resources).
The official Authgear SDKs have mechanisms for protecting your applications from CSRF built into them.
However, if you are not using the official SDK, you can secure your application by generating a random hard-to-guess value on the client application and passing it in the state parameter. Your application should store this value securely on the user's client-side using session cookies or some other form of local storage. Then, verify the state parameter in the redirect URI against the value stored locally to confirm that a user-agent is the origin of an authorization request before exchanging the authorization code for an access token.
The following URL shows an example of an authorization request URL:
As you can see from the above URL, state is a query parameter in addition to other parameters like the client_id and redirect_uri.
If you're constructing the authorization URL manually, you can include the state parameter by simply appending "&state=random_state_value" to the authorization URL.
Alternatively, if you're using any of the Authgear SDKs, you can use the built-in state field to set a value.
The following code samples show the use of the state parameter with Authgear.
Step 1: Set up a React Project to use Authgear
Create a new React project or use an existing project and configure the project to use Authgear. The following example is based on our .
First, install the Authgear web SDK by running the following command:
Next, configure Authgear in your React Project's index.tsx file like this:
Step 2: Include State Parameter in Authorization Request
Set the state field in your call to the startAuthentication() method of the Authgear SDK to a random hard-to-guess value based on your use case.
Step 3: Read and Use the Value of State Returned After the Authorization
Implement the component that handles your OAuth 2.0 redirect like this:
Learn how to switch between ASWebAuthenticationSession/Custom Tabs to WebKitWebView using Authgear Mobile SDKs.
The default of the Authgear Mobile SDKs is to launch AuthUI in ASWebAuthenticationSession in iOS and Custom Tabs in Android. ASWebAuthentication is an API provided by Apple for login purpose. It will store the session cookie and share with Safari, which makes Single Sign-on (SSO) between mobile apps and web apps possible.
However, it requires user consent, and will display a login alert box:
There are multiple ways you can avoid the login alert box:
If you do not need SSO between mobile and web apps, you can disable it by setting isSSOEnabled = false.
It will not share the session cookies between your app and Safari. And the login alert box will not show to prompt user consent.
The mobile SDKs include WebKitWebViewUIImplementation, a UIImplementation which makes it possible to customize more UI.
Depending on the platforms, there are various alternatives:
iOS: WKWebViewUIImplementation
Other platforms / Android: WebKitWebViewUIImplementation
Setting the uiImplementation attribute in the configure() method of the Authgear SDK to WebKitWebViewUIImplementation() will open AuthUI using on iOS and on Android.
Omitting the uiImplementation attribute in the configure() method will fall back to the default behavior (launching AuthUI in ASWebAuthenticationSession/Custom Tabs, which is DeviceBrowserUIImplementation).
The following examples show how to set the uiImplementation attribute.
Setting uiImplementation to WebKitWebViewUIImplementation in the above example will change the behavior of your application from using ASWebAuthenticationSession on iOS and Custom Tabs on Android to using WKWebView and android.webkit.WebView respectively.
To set uiImplementation to WKWebView in the native iOS SDK, use WKWebViewUIImplementation .
WebKitWebViewUIImplementation allows you to customize some parts of the UI. You can do this by passing your customization options as parameters in WebKitWebViewUIImplementation(). You can customize the following parts of the UI:
Android
actionBarBackgroundColor: Use this option to customize the color of the action bar on the WebView Activity screen. The value should be of type integer according to this encoding:
actionBarButtonTintColor: This option can be used to set the color of the icons and texts on the action bar. The value should also be of type integer and use the encoding here: .
iOS
navigationBarBackgroundColor: This option can be used to customize the color of the navigation bar on iOS. The value should be of type or an integer (React Native or Ionic SDKs) using the following encoding: .
navigationBarButtonTintColor: This option sets the color of icons and texts on the navigation bar. The value should also be UIColor or an integer (React Native or Ionic SDKs) using the same encoding as navigationBarBackgroundColor.
modalPresentationStyle
The following examples show how to set custom background color, tint color, and modal presentation style.
You can implement your own custom UIImplementation when the WebKitWebViewUIImplementation does not meet the requirements of your use case.
The WebKitWebViewUIImplementation class itself is basically a class that implements UIImplementation and overrides the openAuthorizationURL()method. Hence your custom implementation may look like this:
Then, you can use your custom implementation like this:
To get a deeper understanding of how to implement your UIImplementation, see the code for the implementation.
When you drop the default DeviceBrowserUIImplementation to use your own custom UI implementation that uses WebView, it is important to note that you'll be losing the following features, due to iOS or other security limitations.
Login with Google: Google prohibits the use of WebKitWebView with the Google SSO. Learn more here: . As a result WebKitWebViewUIImplementation and Google SSO cannot be used together.
Passkey: Passkey is not supported in WebKitWebView.
http://localhost:8080/login/oauth2/code/authgear
<dependencies>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-oauth2-client</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-thymeleaf</artifactId>
</dependency>
<dependency>
<groupId>org.thymeleaf.extras</groupId>
<artifactId>thymeleaf-extras-springsecurity6</artifactId>
<version>3.1.1.RELEASE</version>
</dependency>
</dependencies>
spring.security.oauth2.client.registration.authgear.client-id={your-client-id}
spring.security.oauth2.client.registration.authgear.client-secret={your-client-secret}
spring.security.oauth2.client.registration.authgear.authorization-grant-type=authorization_code
spring.security.oauth2.client.registration.authgear.scope=openid,offline_access
spring.security.oauth2.client.registration.authgear.redirect-uri=http://localhost:8080/login/oauth2/code/authgear/
spring.security.oauth2.client.provider.authgear.token-uri=https://{DOMAIN}/oauth2/token
spring.security.oauth2.client.provider.authgear.authorization-uri=https://{DOMAIN}/oauth2/authorize
# To logout from the app
authgear.oauth2.end-session-endpoint=https://{DOMAIN}/oauth2/end_session
@Configuration
@EnableMethodSecurity(securedEnabled = true)
public class SecurityConfig {
@Value("${authgear.oauth2.end-session-endpoint}")
private String endSessionEndpoint;
@Bean
public SecurityFilterChain configure(HttpSecurity http) throws Exception {
http.authorizeHttpRequests((requests) -> requests
// allow anonymous access to the root page
.requestMatchers("/").permitAll()
// authenticate all other requests
.anyRequest().authenticated())
// enable OAuth2/OIDC
.oauth2Login(withDefaults())
// configure logout handler
.logout(logout -> logout.logoutRequestMatcher(new AntPathRequestMatcher("/logout"))
.logoutSuccessUrl("/")
.addLogoutHandler(oidcLogoutHandler()));
return http.build();
}
LogoutHandler oidcLogoutHandler() {
return (request, response, authentication) -> {
try {
response.sendRedirect(endSessionEndpoint);
} catch (IOException e) {
throw new RuntimeException(e);
}
};
}
}
@Controller
public class HomeController {
@GetMapping("/")
String home() {
return "home";
}
}








Put your redirect URI for login and logout under the Redirect URIs list and Post Logout Redirect URIs list respectively.
For this example, when the initial value of the state parameter before authorization is not the same as the value returned in the redirectURL, we halt the authentication process.
Step 1: Set up PHP Project
This example uses the League OAuth 2.0 client PHP package. Install the package using the following command:
Next, configure your PHP to use Authgear like this:
The League OAuth 2.0 client we are using in this example helps us generate random strings for the state parameter. In the above code, we store the value for the state generated in session on the line with $_SESSION['oauth2state'] = $provider->getState();.
Step 2: Read and Use the Value of State
Add an else block for the if (!isset($_GET['code'])) condition with the following code:
The above code will prevent your PHP application from exchanging an authorization code for an access token when the value of state stored in the PHP session is not identical to the state returned in the redirect URI. The usage demonstrated above can prevent CSRF attacks.
redirectURIauthgear
.authenticateAnonymously()
.then(({userInfo}) => {
// Logged in as anonymous user successfully
})
.catch((err) => {
// Handle the error
});try {
final userInfo = await authgear.authenticateAnonymously();
// Logged in as anonymous user successfully
} catch (e) {
// Handle the error
}authgear.authenticateAnonymously { result in
switch result {
case let .success(userInfo):
// Logged in as anonymous user successfully
case let .failure(error):
// Handle the error
}
}127.0.0.1 {SUBDOMAIN}.{PROJECT_NAME}.authgear.cloudmkcert *.{PROJECT_NAME}.authgear.cloudserver {
listen 443 ssl;
server_name {SUBDOMAIN}.{PROJECT_NAME}.authgear.cloud;
ssl_certificate /path/to/your/cert;
ssl_certificate_key /path/to/your/key;
location / {
# Change it to your service endpoint
proxy_pass http://127.0.0.1:3000;
proxy_set_header Host $host;
auth_request /_auth;
auth_request_set $x_authgear_session_valid $upstream_http_x_authgear_session_valid;
auth_request_set $x_authgear_user_id $upstream_http_x_authgear_user_id;
auth_request_set $x_authgear_user_anonymous $upstream_http_x_authgear_user_anonymous;
auth_request_set $x_authgear_user_verified $upstream_http_x_authgear_user_verified;
auth_request_set $x_authgear_session_acr $upstream_http_x_authgear_session_acr;
auth_request_set $x_authgear_session_amr $upstream_http_x_authgear_session_amr;
auth_request_set $x_authgear_session_authenticated_at $upstream_http_x_authgear_session_authenticated_at;
auth_request_set $x_authgear_user_can_reauthenticate $upstream_http_x_authgear_user_can_reauthenticate;
proxy_set_header x-authgear-session-valid $x_authgear_session_valid;
proxy_set_header x-authgear-user-id $x_authgear_user_id;
proxy_set_header x-authgear-user-anonymous $x_authgear_user_anonymous;
proxy_set_header x-authgear-user-verified $x_authgear_user_verified;
proxy_set_header x-authgear-session-acr $x_authgear_session_acr;
proxy_set_header x-authgear-session-amr $x_authgear_session_amr;
proxy_set_header x-authgear-session-authenticated-at $x_authgear_session_authenticated_at;
proxy_set_header x-authgear-user-can-reauthenticate $x_authgear_user_can_reauthenticate;
}
location /_auth {
internal;
resolver 8.8.8.8;
set $resolver https://{PROJECT_NAME}.authgear.cloud/_resolver/resolve;
proxy_pass $resolver;
proxy_pass_request_body off;
proxy_set_header Content-Length "";
}
}server {
listen 443 ssl;
server_name {SUBDOMAIN}.{PROJECT_NAME}.authgear.cloud;
ssl_certificate /path/to/your/cert;
ssl_certificate_key /path/to/your/key;
location / {
resolver 127.0.0.11;
# change {CONTAINER_NAME} to host.docker.internal if accessing host
proxy_pass http://{CONTAINER_NAME}:{PORT};
proxy_set_header Host $host;
auth_request /_auth;
auth_request_set $x_authgear_session_valid $upstream_http_x_authgear_session_valid;
auth_request_set $x_authgear_user_id $upstream_http_x_authgear_user_id;
auth_request_set $x_authgear_user_anonymous $upstream_http_x_authgear_user_anonymous;
auth_request_set $x_authgear_user_verified $upstream_http_x_authgear_user_verified;
auth_request_set $x_authgear_session_acr $upstream_http_x_authgear_session_acr;
auth_request_set $x_authgear_session_amr $upstream_http_x_authgear_session_amr;
auth_request_set $x_authgear_session_authenticated_at $upstream_http_x_authgear_session_authenticated_at;
auth_request_set $x_authgear_user_can_reauthenticate $upstream_http_x_authgear_user_can_reauthenticate;
proxy_set_header x-authgear-session-valid $x_authgear_session_valid;
proxy_set_header x-authgear-user-id $x_authgear_user_id;
proxy_set_header x-authgear-user-anonymous $x_authgear_user_anonymous;
proxy_set_header x-authgear-user-verified $x_authgear_user_verified;
proxy_set_header x-authgear-session-acr $x_authgear_session_acr;
proxy_set_header x-authgear-session-amr $x_authgear_session_amr;
proxy_set_header x-authgear-session-authenticated-at $x_authgear_session_authenticated_at;
proxy_set_header x-authgear-user-can-reauthenticate $x_authgear_user_can_reauthenticate;
}
location /_auth {
internal;
resolver 8.8.8.8;
set $resolver https://{PROJECT_NAME}.authgear.cloud/_resolver/resolve;
proxy_pass $resolver;
proxy_pass_request_body off;
proxy_set_header Content-Length "";
}
}composer require league/oauth2-client<?php
require 'vendor/autoload.php';
session_start();
$appUrl = "https://your_project.authgear.cloud";
$clientID = "";
$clientSecret = "";
$redirectUri = "http://localhost:8081/";
$provider = new \League\OAuth2\Client\Provider\GenericProvider([
'clientId' => $clientID, // The client ID assigned to you by the provider
'clientSecret' => $clientSecret, // The client password assigned to you by the provider
'redirectUri' => $redirectUri,
'urlAuthorize' => $appUrl . '/oauth2/authorize',
'urlAccessToken' => $appUrl . '/oauth2/token',
'urlResourceOwnerDetails' => $appUrl . '/oauth2/userInfo',
'scopes' => 'openid offline_access'
]);
if (!isset($_GET['code'])) {
// Fetch the authorization URL from the provider; this returns the
// urlAuthorize option and generates and applies any necessary parameters
// (e.g. state).
$authorizationUrl = $provider->getAuthorizationUrl();
// Get the state generated for you and store it to the session.
$_SESSION['oauth2state'] = $provider->getState();
// Redirect the user to the authorization URL.
header('Location: ' . $authorizationUrl);
exit;
}else {
$code = $_GET['code'];
if (empty($_GET['state']) || empty($_SESSION['oauth2state']) || $_GET['state'] !== $_SESSION['oauth2state']) {
if (isset($_SESSION['oauth2state'])) {
unset($_SESSION['oauth2state']);
}
exit('Invalid state');
} else {
try {
$accessToken = $provider->getAccessToken('authorization_code', [
'code' => $code
]);
echo "Login successful ". $accessToken;
} catch (\League\OAuth2\Client\Provider\Exception\IdentityProviderException $e) {
// Failed to get the access token or user details.
exit($e->getMessage());
}
}
}https://your_project.authgear.cloud/login?client_id=your_authgear_app_client_id&redirect_uri=http%3A%2F%2Flocalhost%3A4000%2Fauth-redirect&state=12345678npm install @authgear/webimport authgear from "@authgear/web";
export const endpoint = "https://your_project.authgear.cloud"; // The Authgear endpoint of your project e.g. https://my-app.authgearapps.com
export const clientID = ""; // Client ID can be obtained in the "Applications" page of the Portal
async function init() {
try {
await authgear.configure({
endpoint,
clientID,
sessionType: "refresh_token",
});
} finally {
createRoot(document.getElementById("react-app-root")!).render(<App />);
}
}
// eslint-disable-next-line no-console
init().catch((e) => console.log(e)); const startLogin = useCallback(() => {
authgear
.startAuthentication({
redirectURI: "http://localhost:4000/auth-redirect",
prompt: PromptOption.Login,
state: "12345678"
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
}, []);const AuthRedirect: React.FC = () => {
const usedToken = useRef(false);
const navigate = useNavigate();
useEffect(() => {
async function updateToken() {
try {
const u = new URL(window.location.href);
const params = u.searchParams;
const state = params.get("state") ?? undefined
if (state !== undefined) {
const initialState = "12345678"; // In a real app store the initial value on the client side using something like session cookies.
//compare value of state returned in redirectURL to initial value set in startAuthentication()
if (state === initialState) {
//values match, do things log state to an analytic tool, set custom URL to navigate user to...
console.log("state parameter match");
} else {
//the value for state param return does not match, do something like stopping the authentication
console.log("state parameter dont match");
return;
}
}
await authgear.finishAuthentication();
} finally {
navigate("/");
usedToken.current = true;
}
}
if (!usedToken.current) {
updateToken().catch((e) => console.error(e));
}
}, [navigate]);
return <></>;
};Authgear(
clientId: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
isSSOEnabled: false,
)authgear
.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
isSSOEnabled: false,
});authgearCapacitor.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
isSSOEnabled: true,
uiImplementation: new WebKitWebViewUIImplementation(),
tokenStorage: new TransientTokenStorage()
});authgear
.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
uiImplementation: new WebKitWebViewUIImplementation()
});private Authgear authgear = new Authgear(
getApplication(),
"<CLIENT_ID>",
"<AUTHGEAR_ENDPOINT>",
tokenStorage,
new WebKitWebViewUIImplementation(),
isSsoEnabled,
null,
app2appOptions
);Authgear(
clientId: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
tokenStorage: TransientTokenStorage(),
uiImplementation: WKWebViewUIImplementation(),
isSSOEnabled: true,
)authgearCapacitor.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
uiImplementation: new WebKitWebViewUIImplementation({
ios: {
modalPresentationStyle: "fullScreen"
},
android: {
actionBarBackgroundColor: 0xffffff00,
actionBarButtonTintColor: 0xff000000
}
}),
tokenStorage: new TransientTokenStorage()
});authgear
.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
uiImplementation: new WebKitWebViewUIImplementation({
ios: {
modalPresentationStyle: "fullScreen"
},
android: {
actionBarBackgroundColor: 0xffffff00,
actionBarButtonTintColor: 0xff000000
}
})
})private int actionBarBackgroundColor = 0xffffff00;
private int actionBarButtonTintColor = 0xff000000;
private Authgear authgear = new Authgear(
getApplication(),
"<CLIENT_ID>",
"<AUTHGEAR_ENDPOINT>",
tokenStorage,
new WebKitWebViewUIImplementation(actionBarBackgroundColor, actionBarButtonTintColor),
isSsoEnabled,
null,
app2appOptions
);Authgear(
clientId: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
tokenStorage: TransientTokenStorage(),
uiImplementation: WKWebViewUIImplementation(
modalPresentationStyle: UIModalPresentationStyle.fullScreen,
navigationBarBackgroundColor: UIColor.yellow,
navigationBarButtonTintColor: UIColor.black
),
isSSOEnabled: true
)class MyUIImplementation implements UIImplementation {
async openAuthorizationURL(options: OpenAuthorizationURLOptions):
Promise<string> {
// Call your own plugin code to implement this.
}
}authgear.configure({
clientID: "my_client_id",
endpoint: "my_endpoint",
isSSOEnabled: true,
uiImplementation: new MyUIImplementation(),
})mAuthgear.authenticateAnonymously(new OnAuthenticateAnonymouslyListener() {
@Override
public void onAuthenticated(@NonNull UserInfo userInfo) {
// Logged in as anonymous user successfully
}
@Override
public void onAuthenticationFailed(@NonNull Throwable throwable) {
// Handle the error
}
});authgear
.authenticateAnonymously()
.then(({userInfo}) => {
// Logged in as anonymous user successfully
})
.catch((err) => {
// Handle the error
});{
"sub": "...",
"isVerified": false,
"isAnonymous": true
}authgear
.promoteAnonymousUser({
redirectURI: THE_REDIRECT_URI,
})
.then(({userInfo}) => {
// Promote anonymous user successfully
})
.catch((e) => {
// Handle the error
});try {
final userInfo = await authgear.promoteAnonymousUser(redirectURI: THE_REDIRECT_URI);
// Promote anonymous user successfully
} catch (e) {
// Handle the error
}authgear.promoteAnonymousUser(
redirectURI: THE_REDIRECT_URI
) { result in
switch result {
case let .success(userInfo):
// Promote anonymous user successfully
case let .failure(error):
// Handle the error
}
}PromoteOptions options = new PromoteOptions(THE_REDIRECT_URI);
authgear.promoteAnonymousUser(options, new OnPromoteAnonymousUserListener() {
@Override
public void onPromoted(@NonNull UserInfo userInfo) {
// Promote anonymous user successfully
}
@Override
public void onPromotionFailed(@NonNull Throwable throwable) {
// Handle the error
}
});authgear
.startPromoteAnonymousUser({
// Configure redirectURI which users will be redirected to
// after they have promoted with Authgear.
// You can use any path in your website.
// Make sure it is in the "Redirect URIs" list of the Application.
// The redirect uri for anonymous user promotion should be
// different from the one for normal user authentication.
// e.g. "https://yourdomain.com/promote-redirect"
redirectURI: THE_REDIRECT_URI,
})
.then(({userInfo}) => {
// Started the promotion flow
})
.catch((err) => {
// Failed to start the promotion flow
});authgear
.finishPromoteAnonymousUser()
.then(({userInfo}) => {
// Promoted successfully
// You should redirect the user to another path
})
.catch((err) => {
// Failed to finish promotion
});
);







Learn how to add authentication to any web page without using Authgear's SDKs with IIFE(Immediately-invoked Function Expression) bundle
In this guide, you'll make a simple website server to host the SPA app using ExpressJS. We'll also use it to serve our HTML page and any assets it needs, like JavaScript, CSS, and so on. You can also view a full-source code on the GitHub repo.
Before we start, ensure you have Node.js installed in your system. If not, download and install it from the .
An Authgear account: You need an Authgear account to follow this guide. If you don't have one, you can on the Authgear website.
A Registered App: You need a registered application type (Single Page Application) in Authgear. Follow the guide and skip part. You will retrieve the Authgear Web SDK from Authgear's CDN using IIFE(Immediately-invoked Function Expression) bundle and reference a script in our HTML directly.
Start with making a new folder on your computer to keep the app’s source code (In the example, we call it authgear-spa-js-login). Then, initialize a new NPM project by running the following command:
Next, we install two required packages:
Also, install so that our server can be restarted automatically on any code changes in dev mode:
Next, open the package.json file and edit scripts entry to have start and dev commands like the below:
Now you can run the app in two modes: prod and dev.
For example, npm run dev will run the application using nodemon, monitoring for changes as we modify files.
Create a new file server.js in the root of the project and populate it with the following code:
Create a index.html file in the root of the project and add the following content to the created file:
We do not use a package manager such as , we will retrieve the Authgear Web SDK from Authgear's CDN using IIFE(Immediately-invoked Function Expression) bundle. We can reference a script in our HTML directly:
You can install the Authgear Web SDK as a dependency of your application, it is useful if you are building React or React Native apps. See how to .
Create a new folder called public folder in the project root folder and create another folder called css inside the public folder. Add a new file in there called main.css. This will be used to determine how the log-in and log-out button elements will be hidden on the main page depending on whether a user is authenticated or not.
Open the newly-created public/css/main.css file and add the following CSS:
After creating an HTML file and applying CSS styles, see now how our page looks like by running npm run dev and accessing it at http://localhost:3000.
To add some action to the page, we create a new directory in the public folder called js, and add a new file there called app.js. Copy and paste the following JS code that reads authgear_config.json file Authgear app-specific values (endpoint and clientId) from the endpoint using fetchAuthConfig function. Also, it configures a new Authgear client, and defines login and logout logic:
Let’s breakdown down app.js code in the previous section and understand how authentication is achieved with Authgear:
Configure the Authgear client
fetchAuthConfig: Firstly, this function makes a request to the /authgear_config.json the endpoint we exposed in server.js to fetch Authgear app setting values from authgear_config.jsonfile.
configureClient: Once we retrieve the configuration information for the Authgear client from the authgear_config.json file and we set up the Authgear client with these settings. It also logs a message to the console, informing whether the configuration was successful or not.
Login flow
login: The function is called by the Login button previously defined on the HTML page. It performs the login action by calling authgearClient.startAuthentication Authgear’s function. It redirects the user to the Auhthgear login page. After the user logs in successfully, they will be redirected back to the same page we set in redirectURI. Run the project and click the Login button. You should be taken to the Authgear Login Page configured for your application.
Go ahead and create a new user or log in using an email (we specified the Passwordless Email login method in the first part). When you try to log in with your email, you should receive a to your email box to confirm login operation.
After authenticating successfully, you will be redirected to the page you were before.
Logout flow
logout: This function logs the user out and redirects them back to the original page (at). It uses Authgear’s logout function and logs a message to the console indicating the result of the operation.
Update the UI
window.onload: This is a function that runs when the page loads. It configures the Authgear client and updates the UI. If the page's URL contains a "code=" it means the user is authenticated (code the query will be received from the Authgear server), it updates the UI again and removes the "code=" from the URL.
Evaluate the authentication state
updateUI: This function updates the status of the login and logout buttons based on whether the user is authenticated or not. In Authgear, you can check if the user has logged in or not with sessionState the attribute. If the user is authenticated, we disable the login button and enable the logout button, and vice versa if the user is not authenticated.
Learn how to add custom attributes to a JWT Access Token or ID Token using Authgear
JWTs (JSON Web Tokens) are a common method for securely transmitting information between parties as a JSON object. This information can be verified and trusted because it is digitally signed. With Authgear, it is straightforward to add custom fields to your JWT access tokens or ID Tokens.
This how-to guide will walk you through the process of adding custom fields such as User Profiles attributes to a JWT access token/ID token payload using Authgear and Javascript Hooks.
Here's an example of the fields in the JWT Access Tokens by default and an explanation of their values.
An Authgear account: You need an Authgear account to follow this guide. If you don't have one, you can on the Authgear website.
A Registered App: You need a (client) in Authgear.
Make sure the option Issue JWT as access token is enabled in your Application settings in the Portal.
Log into your .
Navigate to the Applications tab and choose the existing App.
On the App Configuration dashboard, locate the "Access token" section.
With the use of Hooks, Authgear provides flexibility for adding custom logic to your authentication pipeline. You can create a Hook which is triggered any of these about to occur. For example, oidc.jwt.pre_create the event happens just before issuing the JWT access token and it can be used to put extra information into the token.
Navigate to your Authgear Dashboard's Advanced->Hooks section.
Add a new Blocking Event.
Choose the Block Hook Type as the TypeScript and set the Event option to oidc.jwt.pre_create. You will write a new Typescript function from scratch.
Click on Edit Script under the Config option.
Copy and paste the following into the editor:
Click on Finish Editing.
Back to the Hooks page from the navigation bar and click on the Save button at the top of the page.
In the above code, we are importing the necessary modules such as EventOIDCJWTPreCreateHookResponse and EventOIDCJWTPreCreate which are types from the Authgear hook . We modify the JWT payload by adding (e.payload.user.standard_attributes) and (e.payload.user.custom_attributes) of the user.
There are two ways to test it:
You can do this by on your application server side using a JWT decoder and inspecting the payload.
If you created the application type OIDC Client Application, you need to follow the steps below. Expand it to see instructions.
With the use of Hooks, Authgear provides flexibility for adding custom logic to your authentication pipeline. You can create a Hook which is triggered any of these about to occur. For example, oidc.id_token.pre_create the event happens just before issuing the JWT access token and it can be used to put extra information into the token.
Navigate to your Authgear Dashboard's Advanced->Hooks section.
Add a new Blocking Event.
Choose the Block Hook Type as the TypeScript and set the Event option to oidc.id_token.pre_create. You will write a new Typescript function from scratch.
Click on Edit Script under the Config option.
Copy and paste the following into the editor:
Click on Finish Editing.
Back to the Hooks page from the navigation bar and click on the Save button at the top of the page.
In the above code, we are importing the necessary modules such as EventOIDCIDTokenPreCreateHookResponse and EventOIDCIDTokenPreCreate which are types from the Authgear hook . We modify the JWT payload by adding (e.payload.user.custom_attributes) of the user.
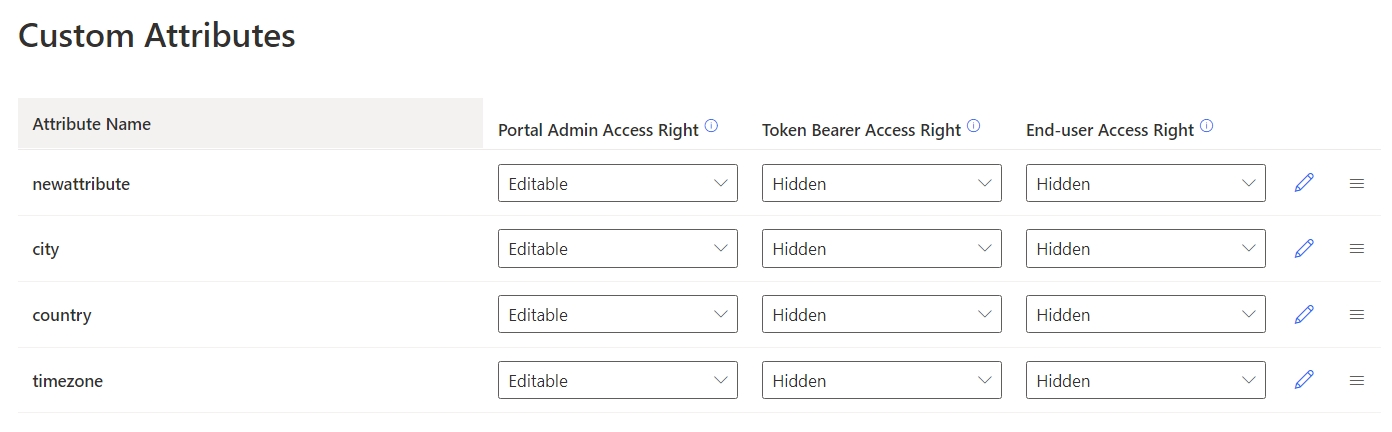
<?php
$appUrl = "REPLACE WITH YOUR AUTHGEAR PROJECT URL";
?>
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>PHP Demo - Home</title>
</head>
<body style="background-color: #DEDEDE">
<div style="max-width: 650px; margin: 16px auto; background-color: #FFFFFF; padding: 16px;">
<h3>Hello world!</h3>
<p>This demo app shows you how to add user authentication to your app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<p><a href="login.php">Login</a></p>
<p><a href="logout.php">Logout</a></p>
</div>
</body>
</html>composer require league/oauth2-client<?php
require 'vendor/autoload.php';
$appUrl = "PLACE_YOUR_PROJECT_URL_HERE";
$clientID = "PLACE_YOUR_CLIENT_ID_HERE";
$clientSecret = "PLACE_YOUR_CLIENT_SECRET_HERE";
$redirectUri = "PLACE_YOUR_REDIRECT_URI_HERE";
$provider = new \League\OAuth2\Client\Provider\GenericProvider([
'clientId' => $clientID, // The client ID assigned to you by the provider (authgear).
'clientSecret' => $clientSecret, // The client secret is assigned to you by the provider.
'redirectUri' => $redirectUri, // The authorized Redirect URI you specified in your authgear app.
'urlAuthorize' => $appUrl.'/oauth2/authorize',
'urlAccessToken' => $appUrl.'/oauth2/token',
'urlResourceOwnerDetails' => $appUrl.'/oauth2/userInfo',
'scopes' => 'openid offline_access'
]);
?><?php
include "config.php";
if (!isset($_GET['code'])) {
// Fetch the authorization URL from the provider; this returns the
// urlAuthorize option and generates and applies any necessary parameters
// (e.g. state).
$authorizationUrl = $provider->getAuthorizationUrl();
// Redirect the user to the authorization URL.
header('Location: ' . $authorizationUrl);
exit;
}
?>$appUrl = "REPLACE WITH YOUR AUTHGEAR PROJECT URL";include "config.php";
session_start();
// if code is set, get access token
if (isset($_GET['code'])) {
$code = $_GET['code'];
try {
$accessToken = $provider->getAccessToken('authorization_code', [
'code' => $code
]);
$_SESSION['accessToken'] = $accessToken;
$_SESSION['refreshToken'] = $accessToken->getRefreshToken(); //store refresh token so that you can use it later
} catch (\League\OAuth2\Client\Provider\Exception\IdentityProviderException $e) {
// Failed to get the access token or user details.
exit($e->getMessage());
}
}<div style="max-width: 650px; margin: 16px auto; background-color: #FFFFFF; padding: 16px;">
<h3>Hello world!</h3>
<p>This demo app shows you how to add user authentication to your app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<?php
if (isset($_SESSION['accessToken'])) {
//if access token exists in session, attempt to fetch user info
$storedAccessToken = $_SESSION['accessToken'];
$resourceOwner = $provider->getResourceOwner($storedAccessToken);
$userInfo = $resourceOwner->toArray();
echo "Welcome back " . $userInfo['email'];
echo "<br/>";
echo '<a href="">Logout</a>';
} else { ?>
<p><a href="login.php">Login</a></p>
<?php
}
?>
</div>$resourceOwner = $provider->getResourceOwner($storedAccessToken);if ($storedAccessToken->hasExpired()) {
$newAccesstoken = $provider->getAccessToken('refresh_token', [
'refresh_token' => $_SESSION['refreshToken']
]);
$_SESSION['accessToken'] = $newAccesstoken;
$resourceOwner = $provider->getResourceOwner($newAccesstoken);
} else {
$resourceOwner = $provider->getResourceOwner($storedAccessToken);
}<?php
include "config.php";
session_start();
if (isset($_SESSION['accessToken'])) {
$options = [];
$options['headers']['content-type'] = 'application/x-www-form-urlencoded';
$options['body'] = http_build_query(['token'=>$_SESSION['refreshToken']]);
$request = $provider->getRequest(
'POST',
$appUrl. '/oauth2/revoke',
$options
);
$provider->getResponse($request);
$_SESSION['accessToken'] = null;
$_SESSION['refreshToken'] = null;
}flask>=2.0.3
python-dotenv>=0.19.2
authlib>=1.0
requests>=2.27.1import json
from os import environ as env
from urllib.parse import quote_plus, urlencode
from authlib.integrations.flask_client import OAuth
from dotenv import find_dotenv, load_dotenv
from flask import Flask, redirect, render_template, session, url_foroauth = OAuth(app)
oauth.register(
"authgear",
client_id=env.get("AUTHGEAR_CLIENT_ID"),
client_secret=env.get("AUTHGEAR_CLIENT_SECRET"),
client_kwargs={
"scope": "openid offline_access",
},
server_metadata_url=f'https://{env.get("AUTHGEAR_DOMAIN")}/.well-known/openid-configuration',
)@app.route("/login")
def login():
return oauth.authgear.authorize_redirect(
redirect_uri=url_for("callback", _external=True)
)@app.route("/callback", methods=["GET", "POST"])
def callback():
token = oauth.authgear.authorize_access_token()
session["user"] = token
return redirect("/")@app.route("/logout")
def logout():
session.clear()
return redirect(
"https://"
+ env.get("AUTHGEAR_DOMAIN")
+ "/oauth2/end_session"
)@app.route("/")
def home():
return render_template(
"home.html",
session=session.get("user"),
pretty=json.dumps(session.get("user"), indent=4),
)<html>
<head>
<meta charset="utf-8" />
<title>Authgear Flak Login Example</title>
</head>
<body>
<div data-gb-custom-block data-tag="if">
<h1>Welcome {{session.userinfo.name}}!</h1>
<p><a href="/logout" id="qsLogoutBtn">Logout</a></p>
<div><pre>{{pretty}}</pre></div>
<div data-gb-custom-block data-tag="else"></div>
<h1 id="profileDropDown">Welcome Guest</h1>
<p><a href="/login" id="qsLoginBtn">Login</a></p>
</div>
</body>
</html>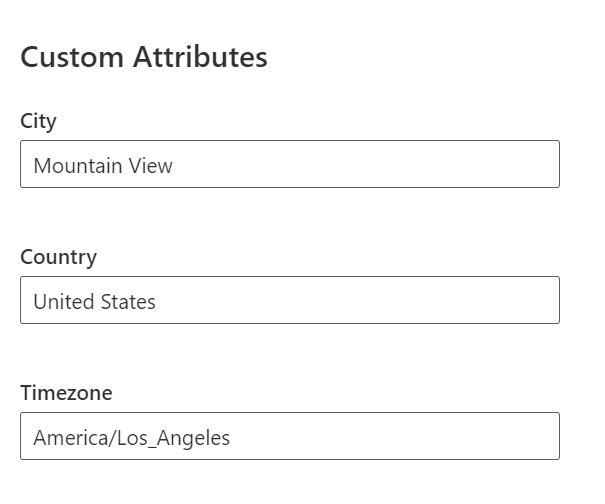
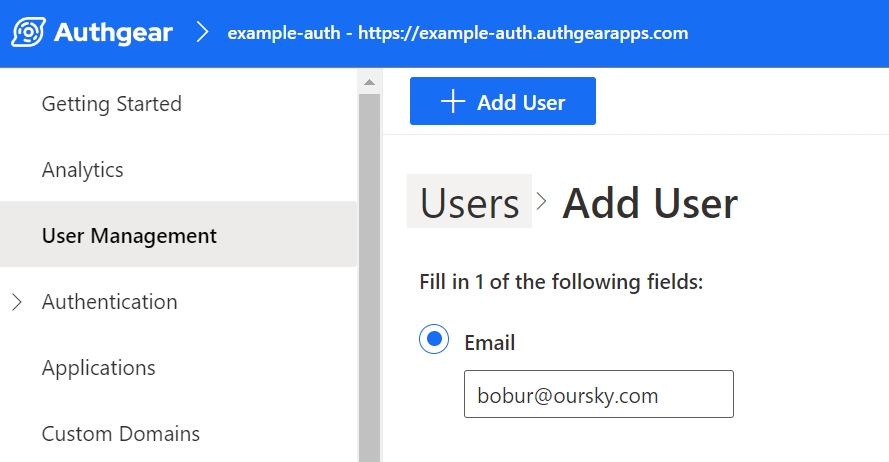




npm init -ynpm install expressnpm install -D nodemon{
// ...
"scripts": {
"start": "node server.js",
"dev": "nodemon server.js"
},
// ...
}const express = require("express");
const { join } = require("path");
const app = express();
// Serve static assets from the /public folder
app.use(express.static(join(__dirname, "public")));
// Endpoint to serve the configuration file
app.get("/authgear_config.json", (req, res) => {
res.sendFile(join(__dirname, "authgear_config.json"));
});
// Serve the index page for all other requests
app.get("/*", (_, res) => {
res.sendFile(join(__dirname, "index.html"));
});
// Listen on port 3000
app.listen(3000, () => console.log("Application running on port 3000"));<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8" />
<title>Authgear SPA SDK Sample</title>
<link rel="stylesheet" type="text/css" href="/css/main.css" />
</head>
<body>
<h2>SPA Authentication Sample</h2>
<p>Welcome to our page!</p>
<button id="btn-login" disabled="true" onclick="login()">Log in</button>
<button id="btn-logout" disabled="true" onclick="logout()">Log out</button>
<script src="js/app.js"></script>
<script src="<https://unpkg.com/@authgear/[email protected]/dist/authgear-web.iife.js>"></script>
</body>
</html><script src="<https://unpkg.com/@authgear/[email protected]/dist/authgear-web.iife.js>"></script>.hidden {
display: none;
}
label {
margin-bottom: 10px;
display: block;
}let authgearClient = null;
const fetchAuthConfig = () => fetch("/authgear_config.json");
const configureClient = async () => {
const response = await fetchAuthConfig();
const config = await response.json();
authgearClient = window.authgear.default;
await authgearClient.configure({
endpoint: config.endpoint,
clientID: config.clientID,
sessionType: "refresh_token",
}).then(
() => {
console.log("Authgear client successfully configured!");
},
(err) => {
console.log("Failed to configure Authgear");
}
);
};
const login = async () => {
await authgearClient
.startAuthentication({
redirectURI: window.location.origin,
prompt: "login",
})
.then(
() => {
console.log("Logged in!");
},
(err) => {
console.log("Log in failed", err);
}
);
};
const logout = () => {
authgearClient
.logout({
redirectURI: window.location.origin,
})
.then(
() => {
console.log("Logged out successfully");
},
(err) => {
console.log("Failed to logout");
}
);
};
window.onload = async () => {
await configureClient();
updateUI();
const query = window.location.search;
if (query.includes("code=")) {
updateUI();
window.history.replaceState({}, document.title, "/");
}
}
const updateUI = async () => {
const isAuthenticated = authgearClient.sessionState === "AUTHENTICATED";
document.getElementById("btn-logout").disabled = !isAuthenticated;
document.getElementById("btn-login").disabled = isAuthenticated;
};Step 2: Construct the authorization endpoint URL
The URL for this endpoint is usually provided by the authorization server and includes parameters specifying the requested scope, client_id, and response_type. Here's an example URL for the authorization endpoint:
Replace <YOUR_AUTHGEAR_ENDPOINT> with your Authgear server's domain, YOUR_CLIENT_ID with your application's Client ID from OpenID App.
Step 3: Redirect the user to the authorization endpoint
Next, you need to redirect the user to the authorization endpoint. You can just put the URL in your browser and log in with a user credential you are interested to retrieve an access token for. After successful authentication and consent, the Authgear will redirect the user back to your specified redirect URI, including an authorization code as a query parameter. You will need the code in the next step
Step 4: Obtain an access token
You need to make a request to the OpenID App's Token endpoint to exchange the authorization code we retrieved in the previous step for an access token.
The token endpoint URL is usually something like https://<YOUR_AUTHGEAR_ENDPOINT>/oauth2/token.
Include parameters such as grant_type=authorization_code, code=AUTHORIZATION_CODE, client_id=YOUR_CLIENT_ID, client_secret=YOUR_CLIENT_SECRET, and redirect_uri=YOUR_REDIRECT_URI.
Make a POST request to the token endpoint to obtain the access token.
Step 5: Verify custom attributes in the access token
Finally, we can debug the access token using the JWT Debugger tool to see if the custom field and value we added previously are there inside the JWT payload.
\



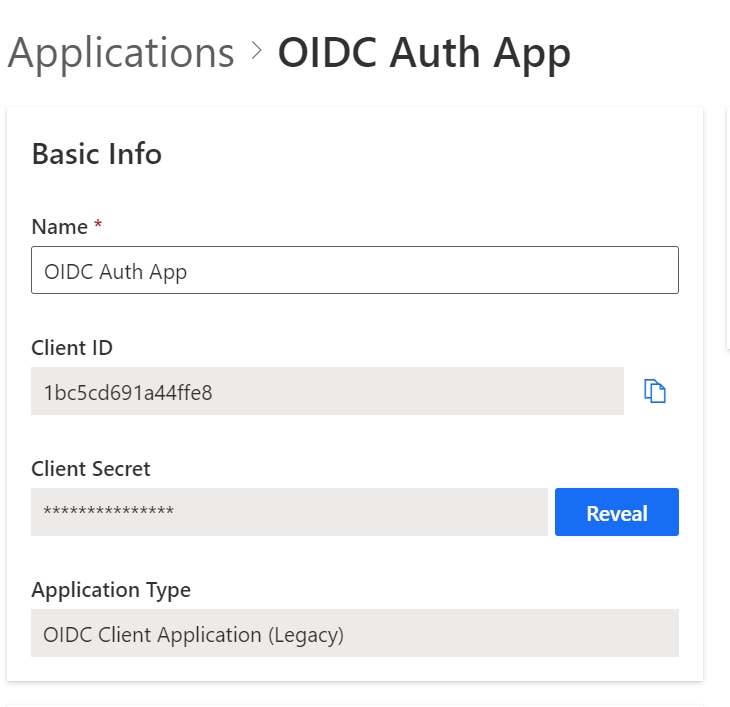
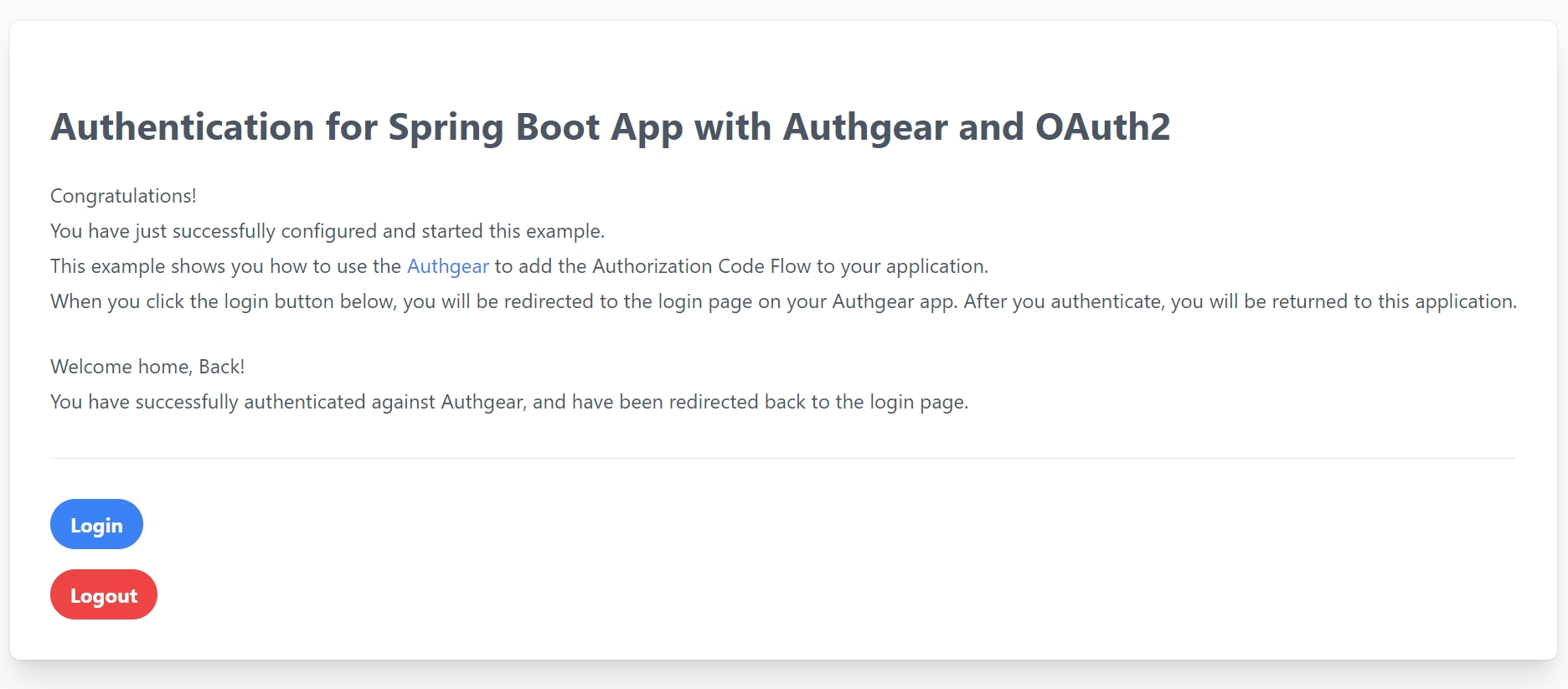
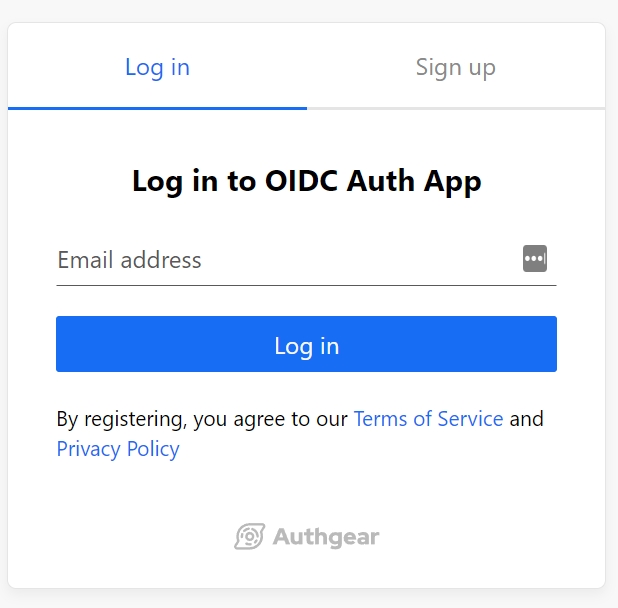
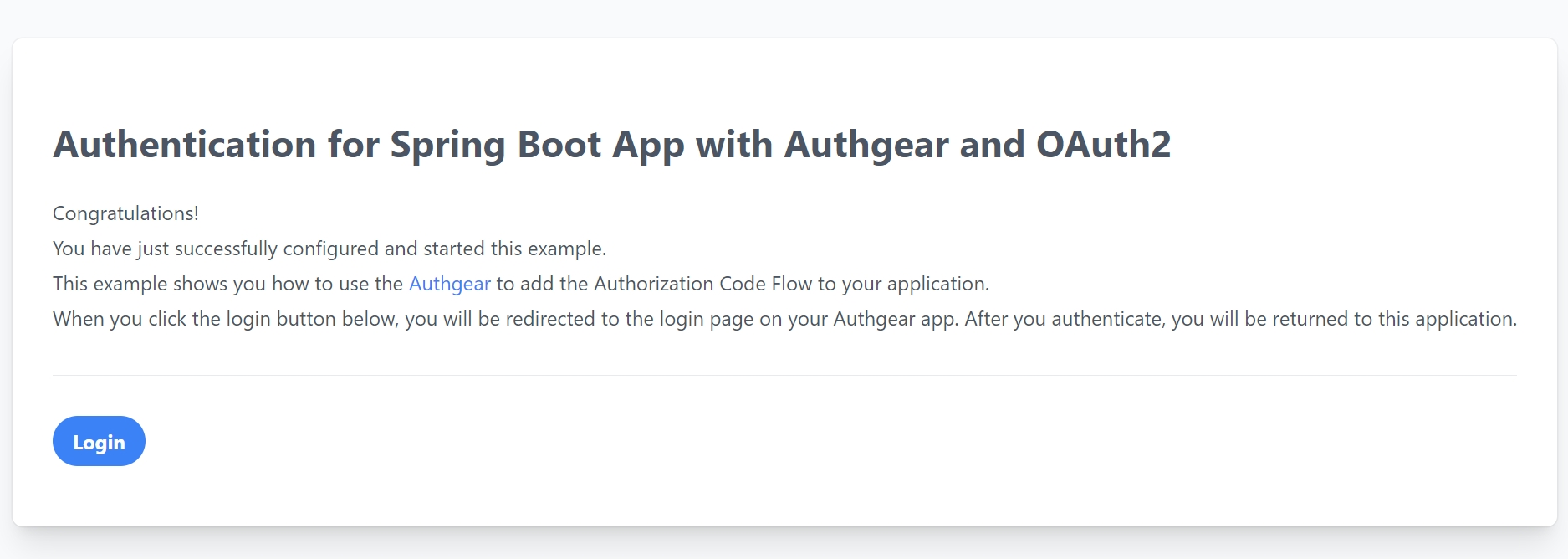
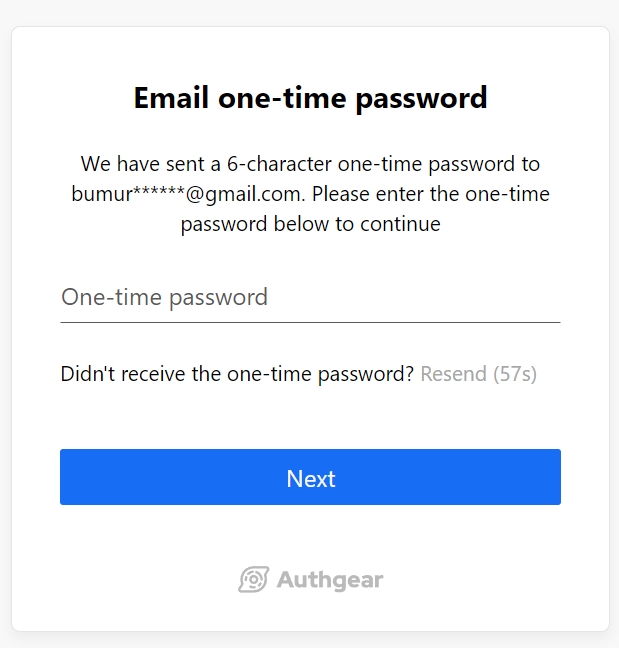
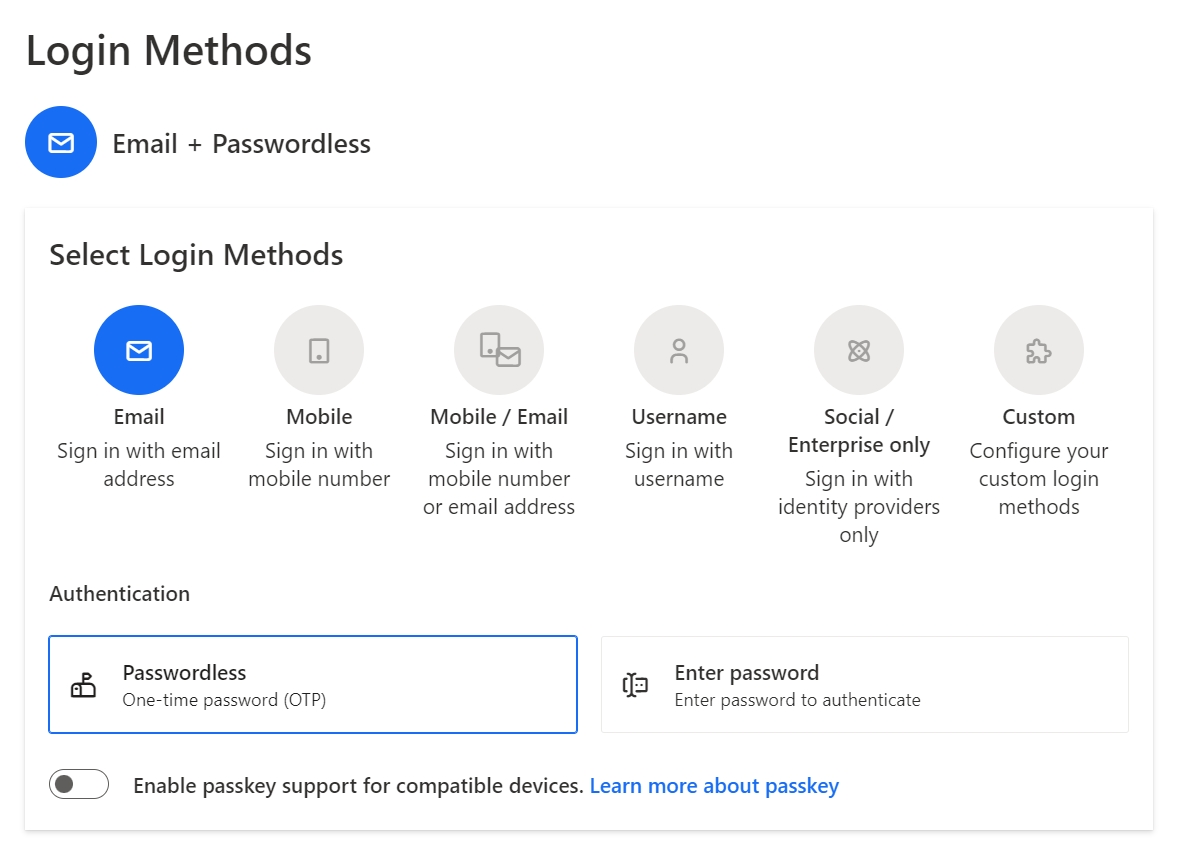
Learn how to access User Profiles
To access any of the applications in your Authgear account, each user must have a profile in the account. contain information about your users such as name, contact information, and and you define. You can retrieve and manage user profiles in the following ways:
.
.
.
import { EventOIDCJWTPreCreate, EventOIDCJWTPreCreateHookResponse } from "https://deno.land/x/[email protected]/mod.ts";
export default async function(e: EventOIDCJWTPreCreate): Promise<EventOIDCJWTPreCreateHookResponse> {
return {
mutations:{
jwt: {
payload:{
...e.payload.jwt.payload,
standard_attributes: e.payload.user.standard_attributes,
custom_attributes: e.payload.user.custom_attributes
}
}
},
is_allowed: true
};
}import { EventOIDCIDTokenPreCreate, EventOIDCIDTokenPreCreateHookResponse } from "https://deno.land/x/[email protected]/mod.ts";
export default async function(e: EventOIDCIDTokenPreCreate): Promise<EventOIDCIDTokenPreCreateHookResponse> {
const customAttributes = e.payload?.user?.custom_attributes ?? null;
return {
is_allowed: true,
mutations: {
id_token: {
payload: {
...e.payload.id_token.payload,
custom_attributes: customAttributes
}
}
}
}
}
https://<YOUR_AUTHGEAR_ENDPOINT>/oauth2/authorize?client_id={YOUR_CLIENT_ID}&response_type=code&scope=openidcurl --request POST \
--url 'https://<YOUR_AUTHGEAR_ENDPOINT>/oauth2/token' \
--header 'content-type: application/x-www-form-urlencoded' \
--data grant_type=authorization_code \
--data code={YOUR_AUTHORIZATION_CODE} \
--data redirect_uri={YOUR_REDIRECT_URI} \
--data 'client_id={YOUR_CLIENT_ID}' \
--data client_secret={YOUR_CLIENT_SECRET} \
--data scope=openid



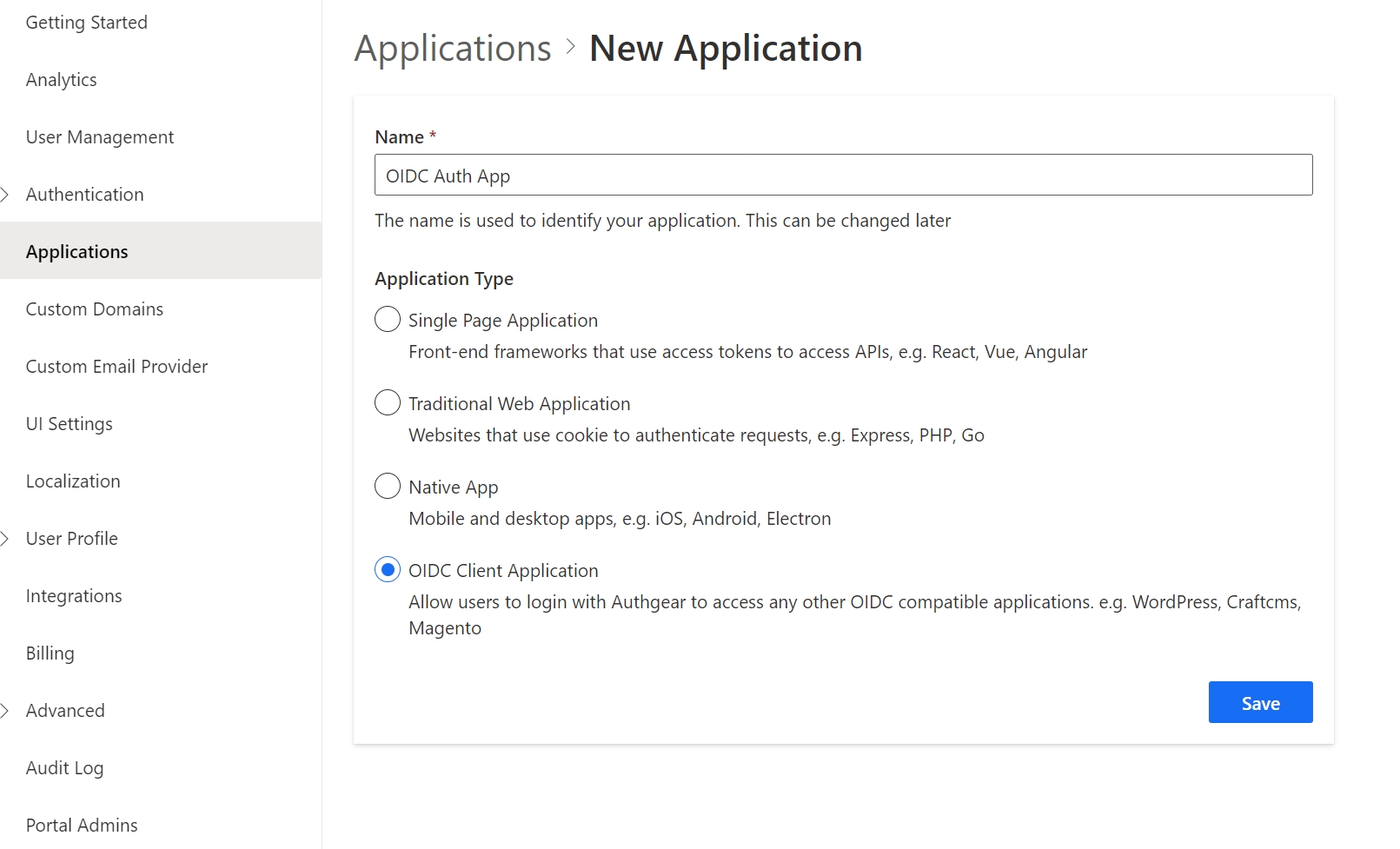
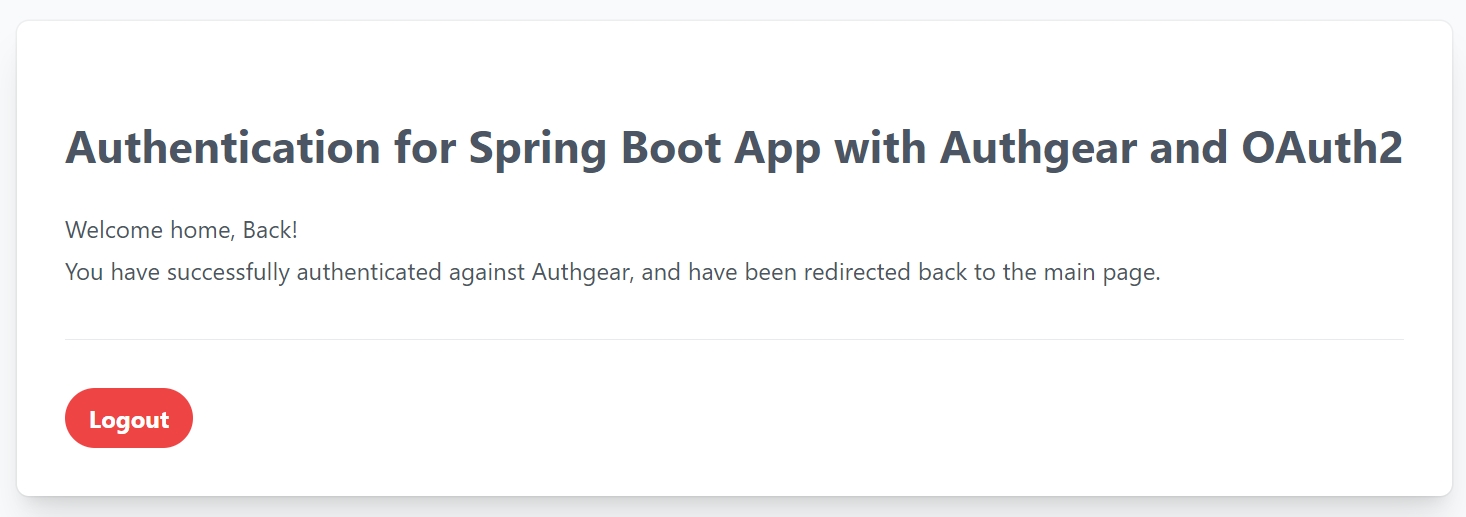
Before you get started, you will need the following:
A free Authgear account. Sign up if you don't have one already.
.NET 7 downloaded and installed on your machine. You can also use Visual Studio and VS code to automatically detect the .NET version.
To use Authgear services, you’ll need to have an application set up in the Authgear Dashboard. The Authgear application is where you will configure how you want to authenticate and manage your users.
Use the interactive selector to create a new Authgear OIDC Client application or select an existing application that represents the project you want to integrate with.
Every application in Authgear is assigned an alphanumeric, unique client ID that your application code will use to call Authgear APIs through the OpenID Connect Client in the .NET app. Note down the Authgear ISSUER (for example, https://example-auth.authgear.cloud), CLIENT ID, CLIENT SECRET, and OpenID Token Endpoint (https://example-auth.authgear.cloud/oauth2/token) from the output. You will use these values in the next step for the client app config.
A Redirect URI of your application is the URL that Authgear will redirect to after the user has authenticated in order for the OpenID Connect middleware to complete the authentication process. In our case, it will be a home page for our ASP.NET and it will run athttp://localhost:5002.
Set the following redirect URI: http://localhost:5002/signin-oidc If not set, users will not be returned to your application after they log in.
Also, enable Issue JWT as an access token option under the Access Token section of the app configuration:
After you create the Authgear app, you choose how users need to authenticate on the login page. From the Authentication tab, navigate to Login Methods, you can choose a login method from various options including, by email, mobile, or social, just using a username or the custom method you specify. For this demo, we choose the Email+Passwordless approach where our users are asked to register an account and log in by using their emails. They will receive a One-time password (OTP) to their emails and verify the code to use the app.
This guide will be used to provide a way for your users to log in to your ASP.NET Core application. The project source code can be found on GitHub. If you are familiar with the steps, you can skip this part and clone the code repository and run the code sample by following the README.md file there.
To integrate Authgear with ASP.NET Core you will use both the Cookie and OpenID Connect (OIDC) authentication handlers. If you are not using a sample project and are integrating Authgear into your own existing project, then please make sure that you add Microsoft.AspNetCore.Authentication.OpenIdConnect packages to your application. Run the following command in your terminal or use your editor to include the NuGet package there:
To enable authentication in your ASP.NET Core application, use the OpenID Connect (OIDC) middleware. Open Startup the class and in the ConfigureServices method, add the authentication services and call the AddAuthentication method. To enable cookie authentication, call the AddCookie method. Next, configure the OIDC authentication handler by adding method AddOpenIdConnect implementation. Configure other parameters, such as Issuer, ClientId, ClientSecret , and Scope. Here, is what looks like Startup.cs after you apply these changes:
Assume that there is a protected resource like a Razor page Protected.cshtml that is used to represent views:
And ProtectedModel.cs class to which Authorize the attribute is applied requires authorization.
To see protected data, users need to go through the authentication process via Authgear.
If a user has not authenticated yet, Unauthenticated.chtml the page is rendered, an OpenID Connect redirect flow is triggered and the user needs to authenticate through the Authgear login page. See Run the Application section
After successful authentication, you should see the protected page with the following details:
As part of the OAuth 2.0 standard, we can use the refresh token returned by the token endpoint to get a new access token. Doing so enables our application to replace an expired access token without requiring the user to repeat the entire login process.
The following code in ProtectedModel.cs is responsible for doing that:
Note: You must include offline_access in your OAuth 2.0 scope for the Authgear authorization server to return a refresh token.
The Logout button on the Protected.cshtml page calls the OnPostLogout() method in ProtectedModel.cs. The method will delete the current user session and redirect to Authgear's end session endpoint for the user to complete the logout process.
The code sample below shows the implementation of the OnPostLogout() method:
Start by cloning the project into your local machine:
Make the project directory your current working directory:
Update the following configuration variables in the appsettings.json file with your Authgear app settings values from Part1 such as Issuer, ClientId, ClientSecret, and Authgear endpoint:
Execute the following command to run the ASP.NET Core web application:
You can now visit http://localhost:5002 to access the application. When you click on the "View Protected Data" button, ASP.NET Core takes you to the Authgear’s Login page.
Your users can log in to your application through a page hosted by Authgear, which provides them with a secure, standards-based login experience that you can customize with your own branding and various authentication methods, such as social logins, passwordless, biometrics logins, one-time-password (OTP) with SMS/WhatsApp, and multi-factor authentication (MFA).
After you have authenticated, a protected view is rendered. The application receives an Access token that it uses to present user data on the screen, and tokens that could be used in upstream requests to some backend API, to access data on behalf of the user.
This guide showed how to quickly implement an end-to-end OpenID Connect flow in .NET with Authgear. Only simple code is needed, after which protected views are secured with built-in UI login pages.
Signup for an Authgear Portal account in https://portal.authgear.com/. Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an application in the project.
Step 1: Create an application in the Portal
Go to Applications on the left menu bar.
Click ⊕Add Application in the top tool bar.
Input the name of your application and select Native App as the application type. Click "Save".
You will see a list of guides that can help you for setting up, then click "Next".
Step 2: Configure the application
In your IDE (e.g. Visual Studio), define a custom URI scheme that the users will be redirected back to your app after they have authenticated with Authgear, e.g. com.myapp.example://host/path.[^1]
Head back to Authgear Portal, fill in the Redirect URI that you have defined in the previous steps.
Click "Save" in the top tool bar and keep the Client ID. You can also obtain it again from the Applications list later.
Open Visual Studio
Create a new project
Choose the Xamarin.Forms template
Search for "Authgear.Xamarin" on nuget.org and add it to your base project. https://www.nuget.org/packages/Authgear.Xamarin/
Authgear.Xamarin targets MonoAndroid 12.0 on Android, and Xamarin.iOS10 on iOS. Update the target framework of the Android and iOS projects to match Authgear.Xamarin's target frameworks.
Update Android and iOS project's Xamarin.Essentials to 1.7.2.
To finish the integration, setup the app to handle the redirectURI specified in the application. This part requires platform specific integration.
If your Android app is targeting API level 30 or above (Android 11 or above), you need to add a queries section to AndroidManifest.xml.
In your MainActivity.cs
In your AppDelegate.cs
When you start launching the application. You may want to know if the user has logged in. (e.g. Show users the login page if they haven't logged in). The SessionState reflects the user logged in state in the SDK locally on the device. That means even the SessionState is Authenticated, the session may be invalid if it is revoked remotely. After initializing the Authgear SDK, call FetchUserInfoAsync to update the SessionState as soon as it is proper to do so.
The value of SessionState can be Unknown, NoSession or Authenticated. Initially, the SessionState is Unknown. After a call to authgear.configure, the session state would become Authenticated if a previous session was found, or NoSession if such session was not found.
In some cases, you may need to obtain current user info through the SDK. (e.g. Display email address in the UI). Use the FetchUserInfoAsync function to obtain the user info, see example.
To log out the user from the current app session, you need to invoke thelogoutfunction.
To include the access token to the HTTP requests to your application server, you set the bearer token manually by using authgear.AccessToken.
You can get the access token through authgear.AccessToken. Call RefreshAccessTokenIfNeededAsync every time before using the access token, the function will check and make the network call only if the access token has expired. Then, include the access token into the Authorization header of the http request.
To protect your application server from unauthorized access. You will need to integrate your backend with Authgear.
For detailed documentation on the Xamarin SDK, visit Xamarin SDK Reference
[^1]: For further instruction on setting up custom URI scheme in Xamarin, see https://www.xamarinhelp.com/uri-scheme/ [^2]: For more explanation on JWT, see https://en.wikipedia.org/wiki/JSON_Web_Token
Access Right defines what information can be viewed or modified when a user's profile is accessed via the Authgear Portal, User Info endpoint, or User Settings page.
An Access Right can be set for each profile attribute under a specific medium of accessing user profiles. For example, in the following screenshot, the Primary Email attribute has the Editable Access Right for Portal, Read-only for User Info endpoint (also known as access Token Bearer), and Editable for User Settings page. In simpler terms, the example means an admin can modify Primary Email in Authgear Portal, while a client application can use a user's access token to view their Primary Email. Finally, users can edit their own Primary Email from the User Settings page.
The following are the available Access Right options that can be applied to each attribute for a specific medium.
Editable: Grants a medium access to view and modify the value of an attribute.
Read-only: A medium with this access for an attribute can only view the value of the attribute.
Hidden: If the access for an attribute is set to Hidden for a medium, that medium can not view or modify the attribute.
By default, Authgear sets different access rights for the standard attributes on each way of accessing user profiles. You can view and configure this default access right from User Profile > Standard Attributes in the Authgear Portal.
For Custom Attributes, you can define the access right for each way of accessing a user profile from User Profile > Custom Attributes in the portal.
Each way of accessing user profiles belongs to one of the following Access Right Categories:
Portal Admin Access Right: Use this category to set the access right of an attribute in the Authgear Portal for an admin user.
Token Bearer Access Right: This sets the access right of an attribute for the User Info endpoint when a token bearer accesses it. It can be "Hidden" or "Read-Only".
End-user Access Right: Use this to set the access right of the attribute for the default User Settings UI when accessed by an end-user.
An Authgear account: You need an Authgear account to follow this guide. If you don't have one, you can create it for free on the Authgear website.
A Registered App: You need a registered application (client) in Authgear.
It is the fastest and easiest way to view user profiles and manage them.
Once Authgear completes authentication and returns control to your application, it provides the user profile to the application. Most developers prefer to use the Authgear SDKs to get the UserInfo object using the fetch user info function. To start using this function read getting started guides relevant to the SDK of your choice. Here are some code snippets that call the fetch user info function for different Authgear SDKs:
Authgear provides an Admin API GraphQL endpoint that allows applications and services to access and manipulate the User Profile object. The API Explorer lets users interactively explore the Admin API. With the API Explorer, you can search for users' profiles or update their standard or custom attributes. See the example steps of how to achieve this below:
The OpenID Connect (OIDC) UseInfo endpoint is a protected resource that provides information about a user when a service provider presents an access token that has been issued by your Authgear Token endpoint. The scopes in the access token specify the user attributes that are returned in the response of the user info endpoint. It is important to note that the openid scope must be one of the access token claims.
Th e UserInfo endpoint returns the Claims about the authenticated end-user, including the standard profile and custom attributes.
The userInfo object is returned from calling fetch user info function which contains a unique identifier of the user.
The following are some attributes that are usually in the userInfo object. Other attributes like email, phoneNumber and custom attributes will be in the userInfo object if those attributes were set for the current user.
isAnonymous
boolean
Indicate if the user is anonymous, i.e. no or is provided
isVerified
boolean
Indicate if the user completed the verification requirement
sub
string
Unique identifier of the user in your Authgear project
To access a user's profile using the UserInfo endpoint of OpenID Connect, you need to follow these steps:
See a detailed explanation of the structure and fields included in the response of the UserInfo endpoint here.
Authgear WebHooks makes it possible to embed the standard attributes and custom attributes for a user's profile into the OIDC JSON Web Token (JWT). Hence, you access both profile attributes in the JWT returned to your OIDC client without making another call to the UserInfo endpoint.
See our post about how to Add custom fields to a JWT Access Token to learn more.
Integrate your iOS application with Authgear iOS SDK
This guide provides instructions on integrating Authgear with an iOS app. Supported platforms include:
iOS 11.0 or higher
Follow this guide to add Authgear to your iOS app in 🕐 10 minutes.
Sign up for an Authgear Portal account at . Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an Authgear client application in the project.
Go to Applications on the left menu bar.
Click ⊕Add Application in the top toolbar.
Input the name of your application and select Native App as the application type. Click "Save".
You will see a list of guides that can help you for setting up, then click "Next".
Here you'll need to define a custom URI scheme that Authgear will use to redirect users back to your app after authentication. For our example app, this URL Scheme will be com.example.authgeardemo://host/path. For further instructions on setting up a custom URI scheme in iOS, see the official documentation .
Head back to Authgear Portal, and add com.example.authgeardemo://host/path as Redirect URI.
Click "Save" button and note the Client ID. and Endpoint for your new client application as you'll use them later in your iOS application. You can also obtain the Client ID again from the Applications list later.
In this step, we'll add user authentication to a simple iOS app using the Authgear iOS SDK and the client application we created in the previous steps.
To follow the steps in this guide seamlessly, you should have the following:
(Latest Version)
Some knowledge of SwiftUI
For the purpose of this guide, we'll create a new project in Xcode. Skip this step if you're adding Authgear to your existing app.
To create a new project, open Xcode and navigate to File > New > Project. Create your new project with the following details:
Project Name: my_demo_app
choose SwiftUI as Interface Leave other fields unchanged and proceed to create the project.
The Authgear iOS SDK makes it easy to interact with Authgear services from your iOS project.
To add Authgear SDK to your project, in Xcode navigate to File > Add Package Dependencies and enter https://github.com/authgear/authgear-sdk-ios.git in the Package URL text field.
Click Add Package to proceed.
On the next screen, select your application under Add to Target then click on Add Package.
Alternatively, if your project uses cocoapods, install the SDK using:
In this step, we'll initialize an instance of the Authgear SDK when the user interface of our app loads.
For our demo app, add the following code to ContentView.swift
First import Authgear iOS SDK:
In struct ContentView: View {}, initialize an instance of Authgear() and call the .configure() method in an .onAppear() modifier attached to VStack like this:
Replace "<CLIENT_ID>" and "<AUTHGEAR_ENDPOINT>" with the client ID and endpoint from the configuration page of the client project you .
Now let's add the Login button and other UI elements for the demo app.
Add the following views to VStack:
In addition to the Login button, we've included a ProgressView and a block with views we want only logged-in users to see. Create the isLoading , userId and loginState variables that the if-statement and Text view depend on at the top of the class just after private var authgear: Authgear = Authgear(...):
Implement a startAuthentication() method in your ContentView class that will call the authenticate() method of the Authgear SDK:
In order to get your app to build at this point, add empty declarations for logout and openUserSettings methods:
The full code for ContentView.swift at this point should look like this:
Run your app now. When you click on the Login button, you should be redirected to the user authentication page.
Open your project's Info.plist or project settings UI in Xcode and add the following:
Navigate to Targets > {Your project} > Info and expand the URL Types section.
Add a new URL scheme with the following details:
Identifier: CFBundleURLTypes
URL Schemes: com.example.authgeardemo://host/path
Role: Editor
Now run your app again and try logging in. Because we've set up a redirect URL, Authgear should redirect back to our app correctly.
Implement the logout method that will be executed when the Logout button is clicked by updating the empty logout function we added in the previous step:
Now clicking on the Logout button will call Authgear SDK's logout method and end the current user session.
In some cases, you may need to obtain current user info through the SDK. (e.g. Display email address in the UI). Use the fetchUserInfo function to obtain the user info, see .
The Authgear SDK can return the current user's details via the UserInfo object. The authenticate method returns this userInfo object as demonstrated earlier in our app's startAuthentication() method. You can also call the SDK's .fetchUserInfo() method to get the UserInfo object.
Add a new getCurrentUser() method to your ContentView class:
Now call the new getCurrentUser() method in the .onAppear() modifier of the VStack like this:
This will make your app refresh the access token and greet users who are already logged in with their sub (a unique user ID) when the launch the app. You can read other user attributes like email address, phone number, full name, etc. from .
Authgear offers a pre-built User Settings page that user's can use to view, and modify their profile attributes and security settings.
Implement the empty openUserSettings() method we added in the previous step to call the .open() method of the Authgear SDK:
When you start launching the application. You may want to know if the user has logged in. (e.g. Show users a Login button if they haven't logged in).
The sessionState reflects the user logged-in state in the SDK local state. That means even if the sessionState is .authenticated, the session may be invalid if it is revoked remotely. Hence, after initializing the Authgear SDK, call fetchUserInfo to update the sessionState as soon as it is proper to do so. We demonstrated how to use sessionState, and fetchUserInfo, to get a user's true logged-in state and retrieve their UserInfo in .
The value of sessionState can be .unknown, .noSession or .authenticated. Initially, the sessionState is .unknown. After a call to authgear.configure, the session state would become .authenticated if a previous session was found, or .noSession if such session was not found.
Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call only if the access token has expired. Include the access token in the Authorization header of your application request.
To protect your application server from unauthorized access. You will need to integrate your backend with Authgear.
For detailed documentation on the iOS SDK, visit .
Authentication for Express.JS apps with Authgear and OAuth2
Authgear makes it easy to add user authentication to a regular web app that is not powered by any framework. You can do this by integrating Authgear into your application as an OIDC identity provider.
In this post, you'll learn how to add user authentication to an Express.js application using Authgear.
How to create an Authgear Application.
How to add User Login to an Express app using Authgear.
How to request user info from Authgear.
You'll need the following to follow along with this tutorial:
Node.js Installed
A free Authgear account. Sign up for one .
Follow this guide to add user authentication to an Express application using Authgear in 🕐 15-minute.
Login to your Authgear account (you can sign up for one ) to perform the steps in this section.
In this step, we'll create the Authgear client application that we'll use later to connect Authgear to the Express application.
After you log in to Authgear Portal, select a project then navigate to Applications on the left menu bar.
Next, click on the ⊕Add Application button on the top toolbar to open the New Application page.
Enter an application name (for example: "My App") and select OIDC/SAML Client Application as the Application Type. Click Save to create the app.
On the next screen, you'll see links to tutorials for different frameworks. Click Next to skip to the application configuration page.
The Authorized Redirect URI should be a page on your Express application where you make an HTTP(S) request to the Authgear token endpoint and exchange an Authorization Code for an Access Token.
For our demo Express application for this guide, this URL will be http://localhost:3000/auth-redirect. So, scroll to the URI section of your application configuration page in the Authgear Portal and add http://localhost:3000/auth-redirect as an authorized redirect URI.
Click Save to keep your changes.
In this section, we'll be building a simple Express app that has the following features:
A landing page with a login link that takes users to the login route.
A /start-login route that initiates the authentication flow.
Logic that exchanges the authorization code from Authgear for an access token.
A page that uses that access token to fetch user info from Authgear.
It is now time to create the Express app that will be connecting to our Authgear client application. Run the following commands to create a new folder for the project and set it as your current working directory:
Next, install the Express npm package and other dependency packages like axios, nodemon, session, and dotenv.
We'll be using the axios library to make HTTP requests in the example app. We'll also use nodemon to add hot reload to our development environment. Run the following commands from the root of your Express project directory to install Express and other dependencies:
app.js fileOnce Express and the other dependencies are installed, create a new app.js file in the root of your project folder and add the following code to the file:
Add the following code to the scripts section of the package.json file in the root directory of your Express project:
Now run the npm run dev command and you should get a page like this on a web browser when you visit localhost:3000:
Here we'll be implementing the login route in our Express app. This route will initiate the authentication flow by redirecting the user's browser to the login page (AuthUI). This process involves redirecting the user to your Authgear project/client application's authorization URL (https://<AUTHGEAR_ENDPOINT>/oauth2/authorize ).
Update the code for the app.get("/login", ...) route to the following:
Create a .env file on the root directory of your project and add your Authgear client application configuration (Client ID, secret, endpoint) using the following fields:
You can get the value for Client ID and Client Secret from the configuration page for the client application you created in the earlier step, . The Authgear Endpoint looks like https://project_id.authgear.cloudif you are using Authgear Cloud version.
Now if you save your code and restart your app, clicking on the Login link should redirect to the Authgear authorization page.
On successful login, an authorization code will be sent back to your Express application.
After the user logs in and grants authorization to your app on the Login page, they are redirected back to the . In addition to this redirect, an authorization code is sent via a code URL query parameter.
In this step, we will be exchanging the authorization code for an access code that users can later use to access protected resources.
Update the code for the app.get("/auth-redirect", ...) route to the following:
The above code sends an HTTP POST request to the token endpoint (https://<AUTHGEAR_ENDPOINT>/oauth2/token). The authorization code we got from the previous step is sent along with other client credentials in the HTTP request body. The header should contain "Content-Type": "application/x-www-form-urlencoded"
A valid access token is returned in the response to the HTTP(S) request in response.data.access_token. In the above code sample, we've saved this access token temporally using express-session so we can access it from "/" route after redirecting the user.
We can now use this access token to make authenticated requests to protected resources in our app or from the Authgear User Info endpoint. In the next step, we'll attempt to get the current user's info from Authgear using the access token.
Authgear provides an endpoint where your application can request user info (https://<AUTHGEAR_ENDPOINT>/oauth2/userinfo). This endpoint will return the user's details on Authgear like their email address, gender, full name, and more.
To get user info in our example app, update the app.get("/", ...) app.js, to use the following conditional statement to render a different block of code when a valid access token is set for the current session:
Here our app sends another HTTP(S) request, but this time to the user info endpoint and the request type is GET. The access token is sent as a Bearer authorization header.
At this point, save all changes and restart the application. Try logging in all over again, at the end you should be greeted with "Welcome [your email address]" and a dump of the response from the UserInfo endpoint if the access token in your authorization header is valid.
To allow your users log out, add a new /logout route to your Express application. Within the route, you'll implement code that will call express-session destroy() method to delete the access token from the session. Then you'll redirect the user to Authgear's logout endpoint to log the user's session on Authgear.
To redirect the user back to your Express app after they logout, add http://localhost:3000 as a Post Logout Redirect URI for your client application in Authgear Portal.
Your implementation of the logout route should look like this:
Finally, place a link to the logout route below the </prev> tag using the following code:
An access token is usually only valid for a short period. However, you can use the refresh token, also included in the response from the token endpoint in to request a new access token.
We recommend that you check that an access token is still valid before using it in your authorization header to access protected resources like the User Info endpoint.
To add the capability of refreshing an expired access token to our Express app, add the following function to app.js:
Next, find the following line within the app.get("/auth-redirect", ...) route:
Add the following code just after the above line:
The above code will store the values of refresh_token and expires_in that were returned in in express-session. To convert expire_in to a time in the future, we multiply it by 1000 and add that to the current time.
Finally, find the following line in the app.get("/", ...) route:
Replace the above line with the following code:
Now our Express app gets an access token by first calling the new refreshAccessTokenIfExpired() method. If the current access token is expired, the method will make a request to Authgear's token endpoint for a new access token. This request needs to have a grant_type of refresh_token, and the refresh_token should be included in the POST request body.
See more about refreshing access tokens .
To access restricted resources on your backend application server, the HTTP requests should include the access token in their Authorization headers.
For example:
And there you have it, you've successfully added user authentication to your Express app using Authgear as the OAuth provider.
You can add so much more to your app with the new Authgear authentication, like protecting your own app endpoint with the access code. You can also store the access token securely to persist the user session using express-session and cookies.
Here's a link to the complete code for .
How to make authorized request to your application server after login with Authgear
In this section, we are going to explain how to make an authorized request to your backend API by using Authgear SDK. Authgear SDKs make it easy to refresh access token if needed and maintain session state.
If you are using Cookie-based authentication in your web application, you can skip this section as session cookies are handled by the browser automatically.
To determine which user is calling your server, you will need to include the Authorization header in every request that send to your application server.
On your Backend/API, you will need to set up . Authgear will help you to handle the Authorization header to determine whether the incoming HTTP request is authenticated or not.
In the below section, we will explain how to set up SDK to for the purpose of making authorized API calls to your backend.
Configure the Authgear SDK with the Authgear endpoint and client id. The SDK must be properly configured before use by calling configure. No network call will be triggered during configure.
sessionState reflect the user logged in state. However the session state is cached locally and only updated after each server call.
Usually right after login/signup via authorize,You will call fetchUserInfo as soon as possible with authgear.sessionState became AUTHENTICATED
When you make a API call to Backend API, you will need to include the access token in the Authorization header. Access token is also short lived and need to be regularly rotated by Refresh token for security purpose. Authgear SDKs provide the following functions to simplify both steps.
fetch function (JavaScript Only)Javascript Only. Authgear SDK provides fetch function for you to call your application server. The fetch function will include Authorization header in your application request, and handle refresh access token automatically. authgear.fetch implement .
If you are using another networking library, you will need to use refreshAccessTokenIfNeeded(). and include the Authorization header yourself, as described in the next paragraph.
You will need to include the Authorization header in your application request. Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call only if the access token has expired. Include the access token into the Authorization header of your application request.
If the session is revoked from the management portal, the client will call your Backend API with an invalid access token. Your application server can check that by looking at the .
For example, you application may return HTTP status code 401 for unauthorized requests. Depending on your application flow, you may want to show your user login page again or reset the SDK sessionState to NO_SESSION locally. To clear the sessionState, you can use clearSessionState function.
The user profiles contain information about your end-users such as name, email, addresses, and their unique identifier. You can manage the profiles via the Portal & Admin API. The end-users can also manage their own profile through the Profile section in the provided by the AuthUI.
The complete information in the user profiles is a combination of standard attributes and custom attributes. Attributes are a way of grouping the fields of the user profile information. With standard attributes containing common fields, you'll find in a user profile, hence the names of these fields are set by Authgear. You set custom fields on the other hand based on the unique needs of your project.
The following attributes are built-in supported by Authgear. They are the set of . Some of them are default hidden from the Admin Portal and end-users. Their visibility and mutability can be configured through the Admin Portal.
Install-Package Microsoft.AspNetCore.Authentication.OpenIdConnectpublic class Startup
{
public IWebHostEnvironment Environment { get; }
public IConfiguration Configuration { get; }
public Startup(IWebHostEnvironment environment, IConfiguration config)
{
Environment = environment;
Configuration = config;
}
// This method gets called by the runtime. Use this method to configure the HTTP request pipeline.
public void Configure(IApplicationBuilder app, IWebHostEnvironment env)
{
app.UseRouting();
app.UseAuthentication();
app.UseAuthorization();
app.UseEndpoints(endpoints =>
{
endpoints.MapRazorPages();
});
}
public void ConfigureServices(IServiceCollection services)
{
// Prevent WS-Federation claim names being written to tokens
JwtSecurityTokenHandler.DefaultInboundClaimTypeMap.Clear();
services.AddAuthentication(options =>
{
options.DefaultScheme = CookieAuthenticationDefaults.AuthenticationScheme;
options.DefaultChallengeScheme = OpenIdConnectDefaults.AuthenticationScheme;
})
.AddCookie(CookieAuthenticationDefaults.AuthenticationScheme, options =>
{
// Use the strongest setting in production, which also enables HTTP on developer workstations
options.Cookie.SameSite = SameSiteMode.Strict;
})
.AddOpenIdConnect(options =>
{
// Use the same settings for temporary cookies
options.NonceCookie.SameSite = SameSiteMode.Strict;
options.CorrelationCookie.SameSite = SameSiteMode.Strict;
// Set the main OpenID Connect settings
options.Authority = Configuration.GetValue<string>("OpenIdConnect:Issuer");
options.ClientId = Configuration.GetValue<string>("OpenIdConnect:ClientId");
options.ClientSecret = Configuration.GetValue<string>("OpenIdConnect:ClientSecret");
options.ResponseType = OpenIdConnectResponseType.Code;
options.ResponseMode = OpenIdConnectResponseMode.Query;
string scopeString = Configuration.GetValue<string>("OpenIDConnect:Scope");
options.Scope.Clear();
scopeString.Split(" ", StringSplitOptions.TrimEntries).ToList().ForEach(scope =>
{
options.Scope.Add(scope);
});
// If required, override the issuer and audience used to validate ID tokens
options.TokenValidationParameters = new TokenValidationParameters
{
ValidIssuer = options.Authority,
ValidAudience = options.ClientId
};
// This example gets user information for display from the user info endpoint
options.GetClaimsFromUserInfoEndpoint = true;
// Handle the post logout redirect URI
options.Events.OnRedirectToIdentityProviderForSignOut = (context) =>
{
context.ProtocolMessage.PostLogoutRedirectUri = Configuration.GetValue<string>("OpenIdConnect:PostLogoutRedirectUri");
return Task.CompletedTask;
};
// Save tokens issued to encrypted cookies
options.SaveTokens = true;
// Set this in developer setups if the OpenID Provider uses plain HTTP
options.RequireHttpsMetadata = false;
});
services.AddAuthorization();
services.AddRazorPages();
// Add this app's types to dependency injection
services.AddSingleton<TokenClient>();
}
}@page "/protected"
@model ProtectedModel
@addTagHelper*, Microsoft.AspNetCore.Mvc.TagHelpers
<style type="text/css">
button
{
width: 200px;
}
</style>
<h1>Protected View</h1>
<h3>
<p>Welcome: @Model.Username</a>
<p>Current Access Token: @Model.AccessToken</a>
<p>Current Refresh Token: @Model.RefreshToken</a>
<form method="post">
<p><button value="RefreshToken" asp-page-handler="RefreshToken">Refresh Token</button></p>
<p><button value="Logout" asp-page-handler="Logout">Logout</button></p>
</form>
</h3>[Authorize]
public class ProtectedModel : PageModel
{
public string Username { get; set; }
public string AccessToken { get; set; }
public string RefreshToken { get; set; }
private readonly TokenClient tokenClient;
public ProtectedModel(TokenClient tokenClient)
{
this.tokenClient = tokenClient;
}
public async Task OnGet()
{
ClaimsPrincipal user = this.User;
var givenName = user.FindFirstValue("given_name");
var familyName = user.FindFirstValue("family_name");
this.Username = $"{givenName} {familyName}";
this.AccessToken = await this.tokenClient.GetAccessToken(this.HttpContext);
this.RefreshToken = await this.tokenClient.GetRefreshToken(this.HttpContext);
}
public async Task<IActionResult> OnPostRefreshToken()
{
await this.tokenClient.RefreshAccessToken(this.HttpContext);
this.AccessToken = await this.tokenClient.GetAccessToken(this.HttpContext);
this.RefreshToken = await this.tokenClient.GetRefreshToken(this.HttpContext);
return Page();
}
public async Task OnPostLogout()
{
await HttpContext.SignOutAsync(CookieAuthenticationDefaults.AuthenticationScheme);
await HttpContext.SignOutAsync(OpenIdConnectDefaults.AuthenticationScheme);
}
}public async Task<IActionResult> OnPostRefreshToken()
{
await this.tokenClient.RefreshAccessToken(this.HttpContext);
this.AccessToken = await this.tokenClient.GetAccessToken(this.HttpContext);
this.RefreshToken = await this.tokenClient.GetRefreshToken(this.HttpContext);
return Page();
}public async Task OnPostLogout()
{
await HttpContext.SignOutAsync(CookieAuthenticationDefaults.AuthenticationScheme);
await HttpContext.SignOutAsync(OpenIdConnectDefaults.AuthenticationScheme);
}git clone cd authgear-example-dotnet{
"OpenIDConnect": {
"ClientId": "{your-client-id}",
"ClientSecret": "{your-client-secret}",
"Issuer": "{your-authgear-app-endpoint}",
"Scope": "openid offline_access",
"PostLogoutRedirectUri": "<http://localhost:5002>",
"TokenEndpoint": "{your-authgear-app-endpoint}/oauth2/token"
},
"Urls": "<http://localhost:5002>",
"Logging": {
"LogLevel": {
"Default": "Information",
"Microsoft": "Warning",
"Microsoft.Hosting.Lifetime": "Information"
}
}
}dotnet build
dotnet runusing System;
using Android.App;
using Android.Content.PM;
using Android.Runtime;
using Android.OS;
using Authgear.Xamarin;
using Xamarin.Forms;
namespace MyApp.Droid
{
[Activity(NoHistory = true, LaunchMode = LaunchMode.SingleTop, Exported = true)]
[IntentFilter(new[] { Android.Content.Intent.ActionView },
Categories = new[] { Android.Content.Intent.CategoryDefault, Android.Content.Intent.CategoryBrowsable },
DataScheme = "com.myapp.example")]
public class WebAuthenticationCallbackActivity : Xamarin.Essentials.WebAuthenticatorCallbackActivity
{
}
}<?xml version="1.0" encoding="utf-8"?>
<manifest xmlns:android="http://schemas.android.com/apk/res/android">
<!-- Other elements such <application> -->
<queries>
<intent>
<action android:name="android.support.customtabs.action.CustomTabsService" />
</intent>
</queries>
</manifest>using System;
using Android.App;
using Android.Content.PM;
using Android.Runtime;
using Android.OS;
using Xamarin.Forms;
using Authgear.Xamarin;
namespace MyApp.Droid
{
public class MainActivity : global::Xamarin.Forms.Platform.Android.FormsAppCompatActivity
{
protected override void OnCreate(Bundle savedInstanceState)
{
// ...
var authgear = new AuthgearSdk(this, new AuthgearOptions
{
ClientId = CLIENT_ID,
AuthgearEndpoint = ENDPOINT
});
DependencyService.RegisterSingleton<AuthgearSdk>(authgear);
LoadApplication(new App());
// ...
}
// other methods are omitted for brevity.
}
}<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<!-- other entries ... -->
<key>CFBundleURLTypes</key>
<array>
<dict>
<key>CFBundleURLName</key>
<string>com.myapp.example://host/path</string>
<key>CFBundleURLSchemes</key>
<array>
<string>com.myapp.example</string>
</array>
<key>CFBundleTypeRole</key>
<string>Editor</string>
</dict>
</array>
</dict>
</plist>using Xamarin.Essentials;
using Xamarin.Forms;
using Authgear.Xamarin;
namespace MyApp.iOS
{
[Register("AppDelegate")]
public partial class AppDelegate : global::Xamarin.Forms.Platform.iOS.FormsApplicationDelegate
{
public override bool FinishedLaunching(UIApplication app, NSDictionary options)
{
global::Xamarin.Forms.Forms.Init();
var authgear = new AuthgearSdk(app, new AuthgearOptions
{
ClientId = CLIENT_ID,
AuthgearEndpoint = ENDPOINT
});
DependencyService.RegisterSingleton<AuthgearSdk>(authgear);
LoadApplication(new App());
return base.FinishedLaunching(app, options);
}
public override bool OpenUrl(UIApplication app, NSUrl url, NSDictionary options)
{
return Xamarin.Essentials.Platform.OpenUrl(app, url, options);
}
public override bool ContinueUserActivity(UIApplication application, NSUserActivity userActivity, UIApplicationRestorationHandler completionHandler)
{
if (Xamarin.Essentials.Platform.ContinueUserActivity(application, userActivity, completionHandler))
return true;
return base.ContinueUserActivity(application, userActivity, completionHandler);
}
}
}<?xml version="1.0" encoding="utf-8" ?>
<ContentPage xmlns="http://xamarin.com/schemas/2014/forms"
xmlns:x="http://schemas.microsoft.com/winfx/2009/xaml"
x:Class="testauthgear.MainPage">
<StackLayout>
<Frame BackgroundColor="#2196F3" Padding="24" CornerRadius="0">
<Label Text="Welcome to Xamarin.Forms!" HorizontalTextAlignment="Center" TextColor="White" FontSize="36"/>
</Frame>
<Button Text="Configure" Clicked="Configure_Clicked" />
<Button Text="Authenticate" Clicked="Authenticate_Clicked"/>
</StackLayout>
</ContentPage>using System;
using System.Collections.Generic;
using System.ComponentModel;
using System.Linq;
using System.Text;
using System.Threading.Tasks;
using Xamarin.Forms;
using Authgear.Xamarin;
namespace MyApp
{
public partial class MainPage : ContentPage
{
private AuthgearSdk authgear;
public MainPage()
{
InitializeComponent();
authgear = DependencyService.Get<AuthgearSdk>();
}
async void Configure_Clicked(object sender, EventArgs e)
{
// You must configure the instance before use.
// Typically you should do this once on app launch.
await authgear.ConfigureAsync();
}
async void Authenticate_Clicked(object sender, EventArgs e)
{
var userInfo = await authgear.AuthenticateAsync(new AuthenticateOptions
{
RedirectUri = REDIRECT_URI
});
}
}
}// value can be NoSession or Authenticated
// After Authgear.ConfigureAsync, it only reflects local state.
var sessionState = authgear.SessionState;
if (sessionState == SessionState.Authenticated)
{
try
{
var userInfo = await authgear.FetchUserInfoAsync();
// sessionState is now up to date
}
catch (Exception ex)
{
// sessionState is now up to date
// it will change to NoSession if the session is invalid
}
}await authgear.LogoutAsync();await authgear.RefreshAccessTokenIfNeededAsync();
// Access token is ready to use
// AccessToken can be string or undefined
// It will be empty if user is not logged in or session is invalid
var accessToken = authgear.AccessToken;
var client = GetHttpClient(); // Get the re-used http client of your app, as per recommendation.
var httpRequestMessage = new HttpRequestMessage(myHttpMethod, myUrl);
httpRequestMessage.Headers.Authorization = new AuthenticationHeaderValue("Bearer", accessToken);try{
const userInfo = await authgear.fetchUserInfo()
// example: output the 'sub' attribute from userInfo to console
// sub is a unique identifier for each user.
// You can read other attributes such as email and phoneNumber depending on your login method
console.log(userInfo.sub)
} catch(e) {
// failed to fetch user info
}authgear.fetchUserInfo { userInfoResult in
// sessionState is now up to date
// it will change to .noSession if the session is invalid
let sessionState = authgear.sessionState
switch userInfoResult {
case let .success(userInfo):
// read the userInfo if needed
let userId = userInfo.sub
let email = userInfo.email
case let .failure(error):
// failed to fetch user info
// the refresh token maybe expired or revoked
}authgear.fetchUserInfo(new OnFetchUserInfoListener() {
@Override
public void onFetchedUserInfo(@NonNull UserInfo userInfo) {
// sessionState is now up to date
// read the userInfo if needed
// example: output the 'sub' attribute from userInfo to LogCat
// sub is a unique identifier for each user.
// You can read other attributes such as email and phoneNumber depending on your login method
Log.d("UserID:", userInfo.sub);
}
@Override
public void onFetchingUserInfoFailed(@NonNull Throwable throwable) {
// sessionState is now up to date
// it will change to NO_SESSION if the session is invalid
}
});try {
UserInfo userInfo = await authgear.getUserInfo();
// read the userInfo if needed
// example: output the 'sub' attribute from userInfo to console
// sub is a unique identifier for each user.
// You can read other attributes such as email and phoneNumber depending on your login method
print(userInfo.sub);
} catch (e) {
// failed to fetch user info
// the refresh token maybe expired or revoked
}
// sessionState is now up to date
SessionState state = authgear.sessionState;try
{
var userInfo = await authgear.FetchUserInfoAsync()
// example: output the 'sub' attribute from userInfo to console
// sub is a unique identifier for each user.
// You can read other attributes such as email and phoneNumber depending on your login method
console.log(userInfo.sub)
}
catch
{
// failed to fetch user info
// the refresh token maybe expired or revoked
}










Make a POST request to the token endpoint to obtain the access token.







authgear
.configure({
clientID: "<YOUR_APPLICATION_CLIENT_ID>",
endpoint: "<YOUR_AUTHGEAR_ENDPOINT>",
})
.then(() => {
// configured successfully
})
.catch((e) => {
// failed to configured
});let authgear = Authgear(clientId: clientId, endpoint: endpoint)
authgear.configure() { result in
switch result {
case .success():
// configured successfully
case let .failure(error):
// failed to configured
}
}ConfigureOptions configureOptions = new ConfigureOptions();
Authgear authgear = new Authgear(getApplication(), clientID, endpoint);
authgear.configure(configureOptions, new OnConfigureListener() {
@Override
public void onConfigured() {
// configured successfully
}
@Override
public void onConfigurationFailed(@NonNull Throwable throwable) {
// failed to configured
}
});query {
users(
searchKeyword: "[email protected]"
) {
edges {
node {
standardAttributes
customAttributes
}
}
}
}curl --request POST \
--url 'https://<YOUR_AUTHGEAR_ENDPOINT>/oauth2/token' \
--header 'content-type: application/x-www-form-urlencoded' \
--data grant_type=authorization_code \
--data code={YOUR_AUTHORIZATION_CODE} \
--data redirect_uri={YOUR_REDIRECT_URI} \
--data 'client_id={YOUR_CLIENT_ID}' \
--data client_secret={YOUR_CLIENT_SECRET} \
--data scope=openidcurl -X GET \
-H "Authorization: Bearer ACCESS_TOKEN" \
https://<YOUR_AUTHGEAR_ENDPOINT>/userinfo
var authgearOptions = new AuthgearOptions
{
ClientId = "<YOUR_APPLICATION_CLIENT_ID>",
AuthgearEndpoint: "<YOUR_AUTHGEAR_ENDPOINT>",
};
#if __ANDROID__
var authgear = new AuthgearSdk(GetActivity().ApplicationContext, authgearOptions);
#else
#if __IOS__
var authgear = new AuthgearSdk(UIKit.UIApplication.SharedApplication, authgearOptions);
#endif
#endif
await authgear.ConfigureAsync();// value can be NO_SESSION or AUTHENTICATED
// After authgear.configure, it only reflect SDK local state.
let sessionState = authgear.sessionState;
if (sessionState === "AUTHENTICATED") {
authgear
.fetchUserInfo()
.then((userInfo) => {
// sessionState is now up to date
// read the userInfo if needed
})
.catch((e) => {
// sessionState is now up to date
// it will change to NO_SESSION if the session is invalid
});
}// value can be .noSession or .authenticated.
// After authgear.configure, it only reflect SDK local state.
let sessionState = authgear.sessionState
// call fetchUserInfo to see if the session is valid
if authgear.sessionState == .authenticated {
authgear.fetchUserInfo { userInfoResult in
// sessionState is now up to date
// it will change to .noSession if the session is invalid
let sessionState = authgear.sessionState
switch userInfoResult {
case let .success(userInfo):
// read the userInfo if needed
case let .failure(error):
// failed to fetch user info
// the refresh token maybe expired or revoked
}
}// value can be NO_SESSION or AUTHENTICATED
// After authgear.configure, it only reflect SDK local state.
SessionState sessionState = authgear.getSessionState();
if (sessionState == SessionState.AUTHENTICATED) {
authgear.fetchUserInfo(new OnFetchUserInfoListener() {
@Override
public void onFetchedUserInfo(@NonNull UserInfo userInfo) {
// sessionState is now up to date
// read the userInfo if needed
}
@Override
public void onFetchingUserInfoFailed(@NonNull Throwable throwable) {
// sessionState is now up to date
// it will change to NO_SESSION if the session is invalid
}
});
}// value can be NoSession or Authenticated
// After Authgear.ConfigureAsync, it only reflects local state.
var sessionState = authgear.SessionState;
if (sessionState == SessionState.Authenticated)
{
try
{
var userInfo = await authgear.FetchUserInfoAsync();
// sessionState is now up to date
}
catch (Exception ex)
{
// sessionState is now up to date
// it will change to NoSession if the session is invalid
}
}authgear
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgear
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgear.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});authgear.refreshAccessTokenIfNeeded() { result in
switch result {
case .success():
// access token is ready to use
// accessToken can be empty
// it will be empty if user is not logged in or session is invalid
// include Authorization header in your application request
if let accessToken = authgear.accessToken {
// example only, you can use your own networking library
var urlRequest = URLRequest(url: "YOUR_SERVER_URL")
urlRequest.setValue(
"Bearer \(accessToken)", forHTTPHeaderField: "authorization")
// ... continue making your request
}
case let .failure(error):
// failed to refresh access token
// the refresh token maybe expired or revoked
}
}// Suppose we are preparing an http request in a background thread.
// Setting up the request, e.g. preparing a URLConnection
try {
authgear.refreshAccessTokenIfNeededSync();
} catch (OauthException e) {
// failed to refresh access token
// the refresh token maybe expired or revoked
}
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
String accessToken = authgear.getAccessToken();
HashMap<String, String> headers = new HashMap<>();
headers.put("authorization", "Bearer " + accessToken);
// Submit the request with the headers...try
{
await authgear.RefreshAccessTokenIfNeededAsync();
}
catch (OauthException ex)
{
// failed to refresh access token
// the refresh token maybe expired or revoked
}
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
var accessToken = authgear.AccessToken;
var client = GetHttpClient(); // Get the re-used http client of your app, as per recommendation.
var httpRequestMessage = new HttpRequestMessage(myHttpMethod, myUrl);
httpRequestMessage.Headers.Authorization = new AuthenticationHeaderValue("Bearer", accessToken);
// Send the request with the headers...// example only
// if your application server return HTTP status code 401 for unauthorized request
async function fetchAppServer() {
var response = await authgear.fetch("YOUR_SERVER_URL");
if (response.status === 401) {
// if you want to clear the session state locally, call clearSessionState
// `authgear.sessionState` will become `NO_SESSION` after calling
await authgear.clearSessionState();
throw new Error("user session invalid");
}
// ...
}// example only
// if your application server return HTTP status code 401 for unauthorized request
if let response = response as? HTTPURLResponse {
if response.statusCode == 401 {
// if you want to clear the session state locally, call clearSessionState
// `authgear.sessionState` will become `.noSession` after calling
authgear.clearSessionState { result in
switch result {
case .success():
// clear SDK session state locally
// `authgear.sessionState` becomes `.noSession`
case let .failure(error):
// failed to clear session state
}
}
}
}// example only
// if your application server return HTTP status code 401 for unauthorized request
responseCode = httpConn.getResponseCode();
if (responseCode == HttpURLConnection.Unauthorized) {
// if you want to clear the session state locally, call clearSessionState
// `authgear.getSessionState()` will become `NO_SESSION` after calling
authgear.clearSessionState();
}// example only
// if your application server return HTTP status code 401 for unauthorized request
statusCode = httpResponseMessage.StatusCode;
if (statusCode == HttpStatusCode.Unauthorized)
{
// if you want to clear the session state locally, call ClearSessionState
// `authgear.SessionState` will become `NoSession` after calling
authgear.ClearSessionState();
}A logout button to end the current user session.
Refresh access token.







Name
Hidden
String
Given Name
Editable
String
Family Name
Editable
String
Middle Name
Hidden
String
The following attributes are coupled with the identities owned by the end-user. They represent the email addresses, phone numbers, or usernames the end-users are using to authenticate themselves on Authgear. If the end-user uses a third-party identity provider for authentication, these attributes will be coupled with the corresponding attributes returned by the provider.
The standard attributes coupled with identities are listed below:
email
email_verified
phone_number
phone_number_verified
preferred_username
The above attributes are coupled with identities when a user specifies them during sign-up, when users verify their email address or phone number, or from User Management > Users > select a user > Identities in Authgear portal or via the Admin API.
The Login Methods enabled for an Authgear project affect the identities available.
You can define a set of custom attributes in the user profile. They are returned as a JSON object in under the custom_attributes key in userInfo.
Go to Portal > User Profile > Custom Attributes and click Add New Attribute
The custom attribute name should consist of lowercase letters (a-z), digits (0-9) and underscore (_) only. It must start with lowercase letters (a-z), and NOT end with an underscore (_). The default display name will be the attribute name split with underscore and in title case. e.g. my_string will render as My String in the AuthUI Settings page.
Authgear supports the following attribute types:
String
Number
Integer
Dropdown
Phone Number
Email Address
URL
Country Code
You can change a custom attribute name and validation settings such as min and max value. The attribute type cannot be changed once it's set. To migrate the attribute into a new type, create a new attribute, migrate the values from the old to the new one, and then change the name and access right of the old attribute to make it obsolete.
Deleting custom attributes is not supported. You can change the name and access rights to make an attribute obsolete.
You can arrange the attribute order by drag-and-drop the handle in the custom attribute configuration in the Portal. This will control the order of how the attributes are shown to the end-users in the AuthUI User Settings page.
The access rights for different parties on individual attributes can be configured through the Authgear Portal. Under the hood, all the attributes are available, however, they can be configured to be hidden or read-only according to the needs of your projects to avoid confusion.
These are the parties that have access to the user profile:
Through the Admin API, developers ALWAYS have full access to ALL the standard attributes and custom attributes. The Admin API allows the developer to view or edit the standard attributes and the custom attributes.
The admin user can view or edit the standard attributes via the Authgear Portal.
The session bearer is someone who has a valid session cookie or a valid access token. The standard attributes of the end-user whom the session represents can be viewed by accessing the UserInfo endpoint and the resolver endpoint. The session bearer can be the end-user, the client mobile app, or the client website.
The end-user can view or edit the standard attributes through the Profile section in the User Setting page provided by the AuthUI.
Authgear supports various social and enterprise identity providers. End-users can sign up and log in to your apps via these connections. Upon signup, these providers will return a set of user attributes about the end-user. Authgear will copy those attributes and populate the profile of the end-user.
More info about the population logic can be found in the specification.








How to use authgear android SDK
This guide provides instructions on integrating Authgear with an Android app. Supported platforms include:
Android 5.0 (API 21) or higher
Follow this guide to add Authgear to your Android app in 🕐 10 minutes.
Sign up for an Authgear Portal account at . Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an application in the project.
Go to Applications on the left menu bar.
Click ⊕Add Application in the top toolbar.
Input the name of your application and select Native App as the application type. Click "Save".
You will see a list of guides that can help you for setting up, then click "Next".
Define a custom URI scheme that Authgear will use to redirect users back to your app after they have authenticated. The scheme should be based on the package name for your Android app. For the demo app, we'll be creating in this guide the scheme is: com.example.authgeardemo://host/path. To learn more about setting up a custom URI scheme in Android, see the official documentation .
Head back to Authgear Portal, and add the URL scheme you have defined as a Redirect URI. For our demo app, add the following URI:
Click "Save" in the top toolbar and note the Client ID as you'll use it later in your Android app. You can also obtain it again from the Applications list later.
In this step, we'll add user authentication to an Android application using the Authgear client application we set up in the previous steps.
To follow along, you need to have the following:
Android Studio installed on your computer
Basic knowledge of Kotlin or Java
For the purpose of this guide, we'll be creating a new simple Android app project. Feel free to skip this step if you are adding Authgear to your existing app.
Open Android Studio and create a new project with the following details:
Select Empty View Activity on the Activity selection screen.
Name: My Dem App
Build configuration language: Groovy DSL
The Authgear Android SDK makes it easier to interact with Authgear endpoints and services from your Android app.
To add the SDK to your app, first, add the jitpack.io repository to your project by adding the following to your project's settings.gradle file:
Next, add authgear in the dependencies section of your app-level (/app/build.gradle) build.gradle. Use $branch-SNAPSHOT (e.g. main-SNAPSHOT) for the latest version in a branch or a release tag/git commit hash of the desired version.
Replace SNAPSHOT with the latest version of the Authgear SDK from: . For example, replacing SNAPSHOT with 2024-12-11.0 to use the latest version at the time of writing this.
To enable Java 8+ API desugaring support for your project, make the following changes to the app-level build.gradle file.
Add coreLibraryDesugaringEnabled true to the android > compileOptions section:
Then add the coreLibraryDesugaring to the dependencies section:
Learn more about Java 8+ API desugaring support .
Sync Gradle to continue.
In this step, we'll initialize Authgear in the onCreate method of our app's MainActivity.kt class using a member variable. Alternatively, you can initialize Authgear in any class that's the entry point for your app:
First, declare a member variable authgear like this:
Next, we'll initialize a new instance of the Authgear SDK and call the configure() method in the onCreate function.
Replace <CLIENT_ID> and <ENDPOINT> with the values from the configuration page of your Authgear client application.
The complete code for MainActivity.kt at this point should look like this:
In this step, we'll add a login button that when the user taps on will open the login/sign-up page.
Open res/layout/activity_main.xml and delete the default "Hello World!" TextView.
Switch to the code view of activity_main.xml and add the login button and a TextView inside the root view (ConstraintsLayout).
Also, add the following views to activity_main.xml to include a Progress Bar, a User Settings button, and a Logout button that will be visible to a logged-in user.
The complete content of activity_main.xml can be found .
Enable View Binding
Next, set up so that you can easily reference Views in your MainActivity.kt file. Add the following to your app-level (/app/build.gradle) build.gradle file under the android block to enable view binding:
Create a binding member variable in MainActivity.kt and modify the onCreate() method as shown below to use view binding in setContentView:
Create a startLogin() method in the MainActivity.kt inside class MainActivity : AppCompatActivity(){}. This method will call the Authgear SDK's authenticate() method to start a new authentication flow.
Next, implement the updateUi() method that was called in startLogin(). This function will update the Views on the screen when the user's logged-in state changes.
The updateUi() method also calls the fetchUserInfo() method of the Authgear SDK. This will return the of the current user such as their email address, name, etc.
Finally, call the startLogin() method on click of the Login button by adding an onClickListener in the onCreate() method.
At this point, if you try to run your application on a mobile device or emulator, you should be able to see the authentication UI (login/sign-up page) when you click on the Login button. However, you will be unable to complete authentication at this point because you have not implemented the activity that handles the Redirect URI.
Add the following activity entry to the AndroidManifest.xml of your app. The intent system would dispatch the redirect URI to OAuthRedirectActivity and the SDK would handle the rest.
If your Android app is targeting API level 30 or above (Android 11 or above), you need to add a queries section to AndroidManifest.xml.
Add a logout() method to your MainActivity.kt class that will call the Authgear SDK's logout() method and end the current user session.
Finally, add an onClickListener for the Logout button that calls the above logout() method in the onCreate() method.
Authgear offers a pre-built User Settings page that user's can use to view, modify their profile attributes and security settings.
Add the following openUserSettings() method to your MainActivity.kt class:
Then add an onClickListener for the User Settings button in the onCreate() method that calls the above openUserSettings() method.
You can use the user's logged-in state to determine whether a user is logged in and display content like their user info and a logout button as we have done in the updateUi() method in . The SessionState reflects the user logged-in state in the SDK local state. That means even if the SessionState is AUTHENTICATED, the session may be invalid if it is revoked remotely. After initializing the Authgear SDK, call fetchUserInfo to update the SessionState as soon as it is proper to do so.
The value of SessionState can be UNKNOWN, NO_SESSION or AUTHENTICATED. Initially, the sessionState is UNKNOWN. After a call to authgear.configure, the session state would become AUTHENTICATED if a previous session was found, or NO_SESSION if such session was not found.
In some cases, you may need to obtain current user info through the SDK. (e.g. Display email address in the UI as we did in ). Use the fetchUserInfo function to obtain the user info, see .
Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call only if the access token has expired. Include the access token in the Authorization header of your application request. If you are using OKHttp in your project, you can also use the interceptor extension provided by the SDK, see .
To protect your application server from unauthorized access. You will need to .
For detailed documentation on the Flutter SDK, visit
[^1]: For further instruction on setting up custom URI scheme in Android, see [^2]: For more explanation on JWT, see
Authentication for Next.js app with Authgear
In this guide, you'll learn how to implement authentication for the Next.js application, a popular React-based framework for JavaScript, and Authgear as the OIDC provider. The source code can be found on GitHub.
You will learn the following throughout the article:
How to add user login, sign-up, and logout to Next.js Applications.
How to create a middleware to protect Next.js application pages.
In the , the Next.js app is integrated with Authgear, and the client library is used for sending authentication requests as an OpenID Connect middleware from the app to Authgear.
Before you begin, you'll need the following:
A free Authgear account. if you don't have one already.
.
Experience with framework and application development.
To use Authgear services, you’ll need to have an application set up in the Authgear . This setup allows users in Authgear to sign in to the Next.js application automatically once they are authenticated by Authgear.
To set up the application, navigate to the and select Applications on the left-hand navigation bar. Use the interactive selector to create a new Authgear OIDC Client application or select an existing application that represents the project you want to integrate with.
Every application in Authgear is assigned an alphanumeric, unique client ID that your application code will use to call Authgear APIs through the NextAuth.js Client in the Next.js app. Record the generated Authgear ISSUER (for example, ), CLIENT ID, CLIENT SECRET from the output. You will use these values in the next step for the client app config.
An Authorized Redirect URI of your application is the URL that Authgear will redirect to after the user has authenticated for the OpenID Connect middleware to complete the authentication process. In our case, it will be a home page for our Next.js and it will run at .
Set the following to the Authorized Redirect URIs field. If not set, users will not be returned to your application after they log in.
After you created the Authgear app, you choose how users need to authenticate on the login page. From the Authentication tab, navigate to Login Methods, you can choose a login method from various options including, by email, mobile, or social, just using a username or the custom method you specify. For this demo, we choose the Email+Passwordless approach where our users are asked to register an account and log in by using their emails. They will receive a One-time password (OTP) to their emails and verify the code to use the app.
You have two options here. You can either clone a or build the app from scratch.
If you want to run an already working application, you can clone the demo project from this using the following command.
Since you've cloned a working repo, you don't need to follow the next section. If you'd like to understand more about what was done in the demo application, feel free to read them.
Either way, continue configuring the to proceed with this tutorial.
If you want to create your own application instead of using our demo project, you can create a new Next.js application by running the command below.
The create-next-app wizard will ask you a few questions on how to set up your application. Answer them accordingly.
Now that you have the application running, let's implement the authentication process by using . We recommend you look also at the for the most up-to-date instructions. First, install NextAuth.js:
Now, you need to create a file named exactly like [...nextauth].js in src/pages/api/auth. First, make the directory and then create a file named [...nextauth].js in that directory.
Next, you'll configure a for Authgear. Doing so ensures every request to the /api/auth/* path is handled by NextAuth.js.
In the following code, we made a few config:
We've added as the scope to make Authgear return all user profiles
We have made id and name in the Next Auth session (under callbacks). You can also add other attributes such as email, phone_number, and preferred_username to the session as well.
To allow components to check whether the current user is logged in, change src/pages/_app.js to have your application rendered inside a <SessionProvider> context, as shown below.
This will make the React Hook accessible to your entire application. Now, create a component that will either render a "Log in" or "Log out" button, depending on the session state, in a src/components/login-button.jsx file.
Then, you change your home component located at src/pages/index.js to include the <LoginButton /> component inside <main>.
In the root directory of your project, add the file .env.local with the following environment variables:
replace with Authgear app settings values from Part1 such as Issuer, ClientId, ClientSecret.
Start the HTTP server by running the following command.
Browse to . If the installation went successful, you should see the Login page.
Click the "Log in" button to be taken to a page with a "Sign in with Authgear" button.
After clicking it, you should be redirected to your Authgear login screen.
Your users can sign-up and login to your application through a page hosted by Authgear, which provides them with a secure, standards-based login experience that you can customize with your own branding and various authentication methods, such as , , , with SMS/WhatsApp, and multi-factor authentication (MFA).
After you have authenticated with a one-time password sent to your email, you'll arrive back at your Next.js application home screen, with your email address displayed and a "Log out" button.
This tutorial showed how to quickly implement an end-to-end OpenID Connect flow in Next.js with Authgear. Only simple code is needed, after which protected views are secured with built-in UI login pages.
Guide on how to use Authgear to secure Firebase services
Firebase is Google's flagship solution for building serverless web and mobile applications. Some of the services Firebase offers include Firestore database, Cloud Storage, Cloud Functions, and Authentication.
You can secure Firebase services like Firestore and Cloud Storage such that only authenticated users in your app have read and write access to certain parts or the entire database. This can be useful when your app allows users to generate content and you need to control who can add or view what.
In this guide, you'll learn how to use Authgear as a custom authentication system to secure Firestore database.
# create project directory
mkdir my-express-app
#set project directory as current working directory
cd my-express-app# Generate package.json
npm init -y
# Install Express
npm install express
# Install axios
npm install axios
# Install express-session
npm install express-session
# Install dotenv
npm install dotenv
# Install Nodemon (Used to add hot road to JavaScript development)
npm install -D nodemon//app.js
const express = require('express');
const axios = require("axios");
const session = require("express-session");
require("dotenv").config();
const app = express();
const port = process.env.PORT || 3000;
app.use(express.urlencoded({ extended: true }));
app.use(
session({
secret: "your_strong_secret_key", // Replace with a strong, randomly generated secret
cookie: {},
})
);
app.get("/", async (req, res) => {
res.send(`
<div style="max-width: 650px; margin: 16px auto; background-color: #EDEDED; padding: 16px;">
<p>Hi there!</p>
<p>This demo app shows you how to add user authentication to your Express app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<a href="/login">Login</a>
</div>
`);
});
app.get("/login", async(req, res) => {
// TODO add implementation here
});
app.get("/auth-redirect", async(req, res) => {
// TODO add implementation here
});
app.listen(port, () => {
console.log(`server started on port ${port}!`);
});"start": "node app.js",
"dev": "nodemon app.js"app.get("/login", async(req, res) => {
const scopes = "openid offline_access";
const authorizedUrl = new URL("/oauth2/authorize", process.env.AUTHGEAR_ENDPOINT);
authorizedUrl.searchParams.set('client_id', process.env.AUTHGEAR_CLIENT_ID);
authorizedUrl.searchParams.set('redirect_uri', process.env.AUTHGEAR_REDIRECT_URL);
authorizedUrl.searchParams.set('response_type', 'code');
authorizedUrl.searchParams.set('scope', scopes);
res.redirect(authorizedUrl);
});AUTHGEAR_CLIENT_ID=<CLIENT_ID>
AUTHGEAR_CLIENT_SECRET=<CLIENT_SECRET>
AUTHGEAR_ENDPOINT=<AUTHGEAR_ENDPOINT>
AUTHGEAR_REDIRECT_URL=http://localhost:3000/auth-redirectapp.get("/auth-redirect", async(req, res) => {
if (req.query.code != null) {
const data = {
client_id: process.env.AUTHGEAR_CLIENT_ID,
client_secret: process.env.AUTHGEAR_CLIENT_SECRET,
code: req.query.code,
grant_type: 'authorization_code',
response_type: 'code',
redirect_uri: process.env.AUTHGEAR_REDIRECT_URL
};
try {
const tokenUrl = new URL("/oauth2/token", process.env.AUTHGEAR_ENDPOINT);
const getToken = await axios.post(tokenUrl, data, {
headers: { "Content-Type": "application/x-www-form-urlencoded" }
});
const accessToken = getToken.data.access_token;
req.session.access_token = accessToken;
res.redirect("/");
} catch (error) {
res.send("An error occurred! Login could not complete. Error data: " + error);
}
} else {
res.send("No Authorization code in URL");
}
});app.get("/", async (req, res) => {
if (req.session.access_token != null) {
const accessToken = req.session.access_token;
//Now use access token to get user info.
try {
const userInfoUrl = new URL(
"/oauth2/userinfo",
process.env.AUTHGEAR_ENDPOINT
);
const getUserInfo = await axios.get(userInfoUrl, {
headers: { Authorization: "Bearer " + accessToken },
});
const userInfo = getUserInfo.data;
res.send(`
<div style="max-width: 650px; margin: 16px auto; background-color: #EDEDED; padding: 16px;">
<p>Welcome ${userInfo.email}</p>
<p>User Info:</p>
<div>
<pre>${JSON.stringify(userInfo, null, 2)}</pre>
</div>
<p>
<a href="/logout">Logout</a>
</p>
</div>
`);
}
catch (error) {
res.send("Unable to get User Info: " + error);
}
} else {
res.send(`
<div style="max-width: 650px; margin: 16px auto; background-color: #EDEDED; padding: 16px;">
<p>Hi there!</p>
<p>This demo app shows you how to add user authentication to your Express app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<a href="/login">Login</a>
</div>
`);
}
});app.get("/logout", async (req, res) => {
const accessToken = req.session.access_token;
const endSessionUrl = new URL(
"/oauth2/end_session",
process.env.AUTHGEAR_ENDPOINT
);
endSessionUrl.searchParams.set("post_logout_redirect_uri", "http://localhost:3000");
// Remove access token, and refresh token from express-session
req.session.destroy();
res.set("Authorization", "Bearer " + accessToken);
res.redirect(endSessionUrl);
});<a href="/logout">Logout</a>const refreshAccessTokenIfExpired = async (refreshToken, expiresAt, req) => {
const currentTime = (new Date(Date.now()).getTime());
if (expiresAt<currentTime) {
const tokenUrl = new URL("/oauth2/token", process.env.AUTHGEAR_ENDPOINT);
const data = {
client_id: process.env.AUTHGEAR_CLIENT_ID,
client_secret: process.env.AUTHGEAR_CLIENT_SECRET,
grant_type: "refresh_token",
refresh_token: refreshToken
};
try {
const getToken = await axios.post(tokenUrl, data, {
headers: { "Content-Type": "application/x-www-form-urlencoded" },
});
const accessToken = getToken.data.access_token;
const expiresAt = new Date(Date.now()).getTime() + getToken.data.expires_in * 1000;
req.session.access_token = accessToken;
req.session.expire_at = expiresAt;
return accessToken;
} catch (error) {
throw new Error('Failed to refresh access token: ' + error);
}
} else {
return req.session.access_token;
}
};req.session.access_token = accessToken;req.session.expire_at = new Date(Date.now()).getTime() + getToken.data.expires_in * 1000;
req.session.refresh_token = getToken.data.refresh_token;const accessToken = req.session.access_token;const accessToken = await refreshAccessTokenIfExpired(req.session.refresh_token, req.session.expire_at, req);axios.get("https://<your_backend_url>", {
headers: { Authorization: "Bearer " + accessToken },
});{
...,
"custom_attributes": {
"department": "example department"
}
}pod 'Authgear', :git => 'https://github.com/authgear/authgear-sdk-ios.git'import Authgearprivate var authgear: Authgear = Authgear(clientId: "<ClIENT_ID>", endpoint: "<AUTHGEAR_ENDPOINT>")
var body: some View {
VStack {
Image(systemName: "globe")
.imageScale(.large)
.foregroundStyle(.tint)
Text("My Demo App")
}
.padding()
.onAppear() {
authgear.configure() { result in
switch result {
case .success():
// configured successfully
print("// configured successfully")
case let .failure(error):
// failed to configured
print("config failed", error)
}
}
}
}VStack {
if isLoading {
ProgressView()
}
if loginState == SessionState.authenticated {
Text("Welcome user \(userId ?? "user")")
Button(action: openUserSettings) {
Text("User Settings")
}
Button(action: logout) {
Text("Logout")
}
} else {
Image(systemName: "globe")
.imageScale(.large)
.foregroundStyle(.tint)
Text("My Demo App")
Button(action: startAuthentication) {
Text("Login")
}
}
}@State private var loginState: SessionState = .unknown
@State private var isLoading: Bool = false
@State private var userId: String? = ""func startAuthentication() {
isLoading = true
authgear.authenticate(redirectURI: "com.example.authgeardemo://host/path", handler: { result in
switch result {
case let .success(userInfo):
// login successfully
loginState = authgear.sessionState
userId = userInfo.sub
isLoading = false
case let .failure(error):
if let authgearError = error as? AuthgearError, case .cancel = authgearError {
// user cancel
isLoading = false
} else {
// Something went wrong
isLoading = false
}
}
})
}func logout() {
}
func openUserSettings() {
}// ContentView.swift
import SwiftUI
import Authgear
struct ContentView: View {
private var authgear: Authgear = Authgear(clientId: "<ClIENT_ID>", endpoint: "<AUTHGEAR_ENDPOINT>")
@State private var loginState: SessionState = .unknown
@State private var isLoading: Bool = false
@State private var userId: String? = ""
var body: some View {
VStack {
if isLoading {
ProgressView()
}
if loginState == SessionState.authenticated {
Text("Welcome user \(userId ?? "user")")
Button(action: openUserSettings) {
Text("User Settings")
}
Button(action: logout) {
Text("Logout")
}
} else {
Image(systemName: "globe")
.imageScale(.large)
.foregroundStyle(.tint)
Text("My Demo App")
Button(action: startAuthentication) {
Text("Login")
}
}
}
.padding()
.onAppear() {
authgear.configure() { result in
switch result {
case .success():
// configured successfully
print("// configured successfully")
case let .failure(error):
// failed to configured
print("config failed", error)
}
}
}
}
func startAuthentication() {
isLoading = true
authgear.authenticate(redirectURI: "com.example.authgeardemo://host/path", handler: { result in
switch result {
case let .success(userInfo):
// login successfully
userId = userInfo.sub
loginState = authgear.sessionState
isLoading = false
case let .failure(error):
if let authgearError = error as? AuthgearError, case .cancel = authgearError {
// user cancel
isLoading = false
} else {
// Something went wrong
isLoading = false
}
}
})
}
func logout() {
}
func openUserSettings() {
}
}
#Preview {
ContentView()
}<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<!-- Other entries -->
<key>CFBundleURLTypes</key>
<array>
<dict>
<key>CFBundleTypeRole</key>
<string>Editor</string>
<key>CFBundleURLSchemes</key>
<array>
<string>com.example.authgeardemo://host/path</string>
</array>
</dict>
</array>
</dict>
</plist>func logout() {
isLoading = true
authgear.logout { result in
switch result {
case .success():
// logout successfully
isLoading = false
loginState = authgear.sessionState
case let .failure(error):
print("failed to logout", error)
isLoading = false// failed to login
}
}
}func getCurrentUser() {
isLoading = true
authgear.fetchUserInfo { userInfoResult in
// sessionState is now up to date
// it will change to .noSession if the session is invalid
loginState = authgear.sessionState
switch userInfoResult {
case let .success(userInfo):
// read the userInfo if needed
userId = userInfo.sub
isLoading = false
case let .failure(error):
// failed to fetch user info
// the refresh token maybe expired or revoked
print("the refresh token maybe expired or revoked", error)
isLoading = false
}
}
}.onAppear() {
authgear.configure() { result in
switch result {
case .success():
// configured successfully
// refresh access token if user has an existing session
if authgear.sessionState == SessionState.authenticated {
getCurrentUser()
}
case let .failure(error):
// failed to configured
print("config failed", error)
}
}
}func openUserSettings() {
authgear.open(page: SettingsPage.settings)
}authgear.refreshAccessTokenIfNeeded() { result in
switch result {
case .success():
// access token is ready to use
// accessToken can be empty
// it will be empty if user is not logged in or session is invalid
// include Authorization header in your application request
if let accessToken = authgear.accessToken {
// example only, you can use your own networking library
var urlRequest = URLRequest(url: "YOUR_SERVER_URL")
urlRequest.setValue(
"Bearer \(accessToken)", forHTTPHeaderField: "authorization")
// ... continue making your request
} else {
// The user is not logged in, or the token is expired.
}
case let .failure(error):
// Something went wrong
}
}Nickname
Hidden
String
Profile
Hidden
URL String
Picture
Editable
URL String
Website
Hidden
URL String
Gender
Editable
male, female or Custom String
Birthdate
Editable
Date in YYYY-MM-DD
Timezone
Editable
Language
Editable
BCP47 language tag enabled by the project
Address
Hidden
JSON Object
Authgear is a cloud-based solution that is 100% focused on user authentication and IAM. While Firebase, on the other hand, offers other cloud services such as Cloud Storage and real-time database Firestore that enable developers to build full-stack apps without the need for implementing their own backend. Hence, you can use Authgear as an authentication provider for your app that uses Firebase to enjoy all the security and login features it offers.
Custom Tokens is a feature in Firebase that allows you to authenticate users using secure JWT (JSON Web Tokens) from a third-party authentication system.
Typically, to authenticate users via Custom Tokens, your authentication system (e.g., Authgear) will authenticate users using your preferred method (e.g., username and password), then return a valid JWT to your client application.
The client application will pass the JWT to Firebase to create a Firebase user instance using the user's sub attribute from Authgear.
The following flow diagram shows the complete sequence of using Firebase Custom Tokens and Authgear.
In this section, we'll cover a step-by-step guide for using Authgear JWT with Firebase Custom Tokens.
As part of the guide, we'll build a demo Todo app. The app will have the following features:
Users Login/Sign up
Add to-do tasks
Delete to-do tasks
Only logged-in users can add tasks
Data is stored on the cloud, and a user can only view/delete tasks they created.
In order to follow the steps in this guide, you should have the following:
Authgear account (sign up for free here)
Firebase project
Node.js installed on your computer
For this part, you'll login to your Firebase console and configure your project.
First, we'll create a Cloud Function that will verify the access token (JWT) from Authgear and use the uid associated with the JWT to create a Firebase Custom Token.
Note: this may require you to upgrade your Firebase project to at least the Blaze plan.
To create a Cloud Function, open https://console.firebase.google.com/ and navigate to Build > Functions and enable the Cloud Function if it isn't already active for your project.
Next, create a cloud_functions folder in the root directory of the Authgear React example project you cloned earlier.
Change your working directory to the cloud_functions folder:
Run the following command to install Firebase CLI:
After the CLI is installed, run the firebase login command and follow the prompt to login to your Firebase project in the CLI.
Run the following command to initialize Cloud Function in the cloud_functions folder you created earlier:
Follow the prompt to create a v2 Cloud Function. Now you should have a function/index.js file in your cloud_functions folder. This is where you'll write the code for your cloud function.
Edit the IAM settings for the service account linked to your project. To do this, go to https://console.cloud.google.com/iam-admin/iam and add Service Account Token Creator to {randomNumbers}[email protected].
In this step, we'll implement a cloud function that does the following:
Accept HTTPS requests from your client application through an endpoint.
Read the value of your Authgear JWT from the HTTPS request authorization header.
Validate the JWT to ensure it is valid (not expired).
If the JWT is valid, the function will read the uid attribute from it and use the value to call firebaseAdmin.auth().createCustomToken(uid). This will generate a new Firebase Custom Token that your client application can use to login to Firebase.
To implement the above function, open function/index.js in your cloud_functions folder and replace the content with the following:
Put your Authgear endpoint in const authgearEndpoint = "";.
Run the following commands to install dependencies:
Finally, run firebase deploy to deploy your new function.
On successful deploy, Firebase CLI will output the public endpoint for your function in the terminal. Copy the endpoint as you will use it later in your React app.
In this part, we'll implement the client application that will use Authgear and Firebase.
As mentioned in the prerequisites for this post, you can get the starter code for the application from our React example app repo.
Go to the Firebase Console and select your project. Next, click on Web as your target platform.
Enter the name of your app (e.g., My todo app), then click Register app.
In the Add Firebase SDK section, select Use npm, then run npm install firebase from the root directory of the Authgear React example repo (confirm that you're not running the command in the cloud_functions folder).
Create a new firebase.js file in the root directory of your React project.
Copy the code that includes your Firebase config, and paste it in the firebase.js file.\
Update firebase.js to expose the Firebase services you'll be using:
Here we'll implement a to-do feature in our React app. The Todo component will contain all the code for implementing this feature.
The component will do the following:
Get the current user's access token from Authgear using the Authgear SDK.
Make an HTTPS request to your Firebase function endpoint using the fetch() method of the Authgear SDK. The fetch() method includes the user's access token in the HTTPS request's authorization header.
Use the custom token that is returned by the cloud function to sign in to Firebase.
Add a new todo item to the Firestore database
Display the todo items
Delete a todo item
Create a Todo.tsx file in the src folder of your React project, then add the following code to the file:
Add your Cloud Function endpoint in const firebaseFunctionEndpoint = "";
Open App.tsx and add the following route in <Routes>:
Make sure to import the Todo in App.tsx.
Finally, add a router link to Home.tsx just after the User Settings link:
You can click on the My Todos link to open the Todo page.
Return to your project in Firebase console, then navigate to Build > Firestore Database. Enable Firestore if it's not active for your project.
Go to the Rules tab, then change the security rule to the following:
The above rule will restrict read and write access to data in /todos/{userID} to only authenticated users. Click Publish to activate the new rule.
Follow the instructions in the README.md file for the Authgear React example app here to configure the app with your Authgear project. Then run the app.
You should be able to authenticate with Authgear and add items to the to-do.











Follow this quickstart tutorial to add authentication to your React application
Authgear helps you add user logins to your React apps. It provides a pre-built login page and user settings page that can accelerate your development process.
Follow this 🕐 15-minute tutorial to create a simple app using React with the Authgear SDK.
To use Authgear's features, you'll need an account and a Project. Sign up for a free account at and create a new Project to get started.
After that, we will need to create an Application in the Project Portal.
To create a client application, go to Applications on the left menu bar in the Authgear Portal.
Next, click ⊕Add Application in the top toolbar.
Enter the name of your application, e.g. "MyAwesomeApp", then select Single Page Application as the Application Type. Click the Save button to create the application.
The Authorized Redirect URI is a URL in you application where the user will be redirected to after login with Authgear. In this path, make a finish authentication call to complete the login process.
Go to the URI section of the Authgear client application you just created and add a new Authorized Redirect URI. For this tutorial, add http://localhost:4000/auth-redirect to Authorize Redirect URIs.
Click Save to keep all client app configuration changes before proceeding to the next steps.
In this section, we'll create a simple React application and connect it to Authgear such that, users of the app will log in, view their user settings, and log out of their account.
Here are some recommended steps to scaffold a React project. You can skip this part if you are adding Authgear to an existing project. See in the next section.
Run the following command from your preferred folder to create a new React project with Vite:
Next, run the following commands to open the new project directory and install the dependencies:
In the package.json file, update the value of dev field in the script.dev section to:
This will enable the npm run dev command run the app in development mode on port 4000.
The file structure in your project should look like this now:
Run npm run dev now to run the project and you will see the default "Vite + React" page when you open http://localhost:4000 on a web browser.
Run the following command within your React project directory to install the Authgear Web SDK
In src/main.tsx , import authgear and call the configure function to initialize an Authgear instance on application loads.
The Authgear container instance takes endpoint and clientID as parameters. They can be obtained from the configuration page for the application created in . Create a .env file in the root directory of your project and add your Authgear client application configuration using the following fields:
It is recommended to render the app after configure() resolves. So by the time the app is rendered, Authgear is ready to use.
Since we want to reference the logged-in state everywhere in the app, let's put the state in a context provider with UserProvider.tsx in the /src/context folder.
The UserProvider.tsx file will have an isLoggedIn boolean and a setIsLoggedIn function. The isLoggedIn boolean state can be auto-updated using the onSessionStateChange callback. This callback can be stored in delegate which is in the local SDK container.
Next, we will add an "AuthRedirect" page for handling the authentication result after the user has been authenticated by Authgear.
First, install react-router-dom using the following command:
Create the AuthRedirect.tsx component file in the src/ folder.
Call the Authgear finishAuthentication() function in the Auth Redirect component to send a token back to Authgear server in exchange for an access token and a refresh token. Don't worry about the technical jargons, finishAuthentication() will do all the hard work for you and save the authentication data.
When the authentication is finished, the isLoggedIn state from the UserContextProvider will be automatically set to true. Finally, navigate back to root (/) which is our Home page.
The final AuthRedirect.tsx will look like this
Now, we will add a "Home" page. Create a Home.tsx component file the src/ folder.
Then import Home and AuthRedirect as routes. And Import UserContextProvider and wrap the routes with it.
Your final App.tsx should look like this:
The file structure should now look like
First, we will import the Authgear dependency and the React Hook that we will use to Home.tsx. Then add the login button which will call startAuthentication(ConfigureOptions) through the startLogin on click callback. This will redirect the user to the login page.
You can now run npm run dev and you will be redirected to the Authgear Login page when you click the Login button.
The Authgear SDK helps you get the information of the logged-in users easily.
In the last step, the user is successfully logged in, so let's try to print the user ID (sub) of the user on the Home page.
In Home.tsx, we will add a simple loading splash and a greeting message printing the Sub ID. We will add two conditional elements such that they are only shown when user is logged in. We can also change the login button to show only if the user is not logged in.
Make use of isLoggedIn from the UserContext to control the components on the page. Fetch the user info by fetchInfo() and access its sub property.
Run the app again, the User ID (sub) of the user should be printed on the Home page.
Now, let's add a Logout button that is displayed when the user is logged in.
In Home.tsx, we will use conditional elements to show a Logout button only for a user that is currently logged in.
Find the following line in Home.tsx:
Add the following code on a new line just after the above line:
Then, add the logout callback:
Run the app again, we can now log out by clicking the Logout button.
Authgear provides a built-in UI for the users to set their attributes and change security settings.
Use the openURL function to open the settings page at <your_app_endpoint>/settings
In Home.tsx Add a conditional link to the existing elements.
And add the userSetting callback:
This is the resulting Home.tsx:
To access restricted resources on your backend application server, the HTTP requests should include the access token in their Authorization headers. The Web SDK provides a fetch function which automatically handles this, or you can get the token with authgear.accessToken.
Authgear SDK provides the fetch function for you to call your application server. This fetch function will include the Authorization header in your application request, and handle the process of refreshing an access token automatically. The authgear.fetch implements .
You can get the access token through authgear.accessToken. Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call to refresh the access token only if it is expired. Include the access token into the Authorization header of the application requests.
Integrate Authgear to your website with the Web SDK
In this guide, you'll learn how to integrate Authgear into your website using the Token Approach. In the token approach, the Authgear server returns an access token and a refresh token to your SPA application after successful user authentication.
Your application can send the access token in subsequent HTTP requests to access protected resources.
Follow this guide to add Authgear SDK to any web application in under 🕐 10 minutes.
This guide uses the Authgear Web SDK for integrating Authgear with a SPA Web app. Supported browsers include:
Last 2 Firefox major versions
Last 2 Chrome major versions
Last 2 Edge major versions
Last 3 Safari major versions
Signup for an Authgear Portal account in . Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an application in the project.
Go to Applications on the left menu bar.
Click ⊕Add Application in the top toolbar.
Input the name of your application and select the application type Single Page Application. Click the Save button to proceed.
On the next screen you will see a list of tutorials for different frameworks, click on Next to skip to your client application configuration page.
First, decide the paths in your website that users will be redirected to after they have authenticated with Authgear.
To run the demo app in this tutorial offline, scroll to the URIs section of your client application page add the following URI:
Under Authorized Redirect URIs add http://localhost:3000/
Click on the Save button to keep your changes.
In this section, we'll create a simple web page and use the Authgear Web JavaScript SDK to add user authentication to the page.
For this guide, we'll create a basic web application with only one page. Follow these steps to set up the application. First, create a new directory on your computer for the project. You can do this in a terminal using the following commands:
We'll create an Express.js server in the web project directory so that we can access the HTML page in a web browser using http://localhost:3000. Run the following commands from the root of your web project directory to install Express.
First, generate a package.json file in your project directory:
Install the Express npm package:
Install Nodemon (used for adding hot road to JavaScript development):
Now create a server.js file in the root folder of your project. Add the following code to server.js:
Next, open the package.json in your project directory and add the following lines in the script section:
Create a new file called index.html in the root of your project directory. Add the following code to the file:
The content index.html is a simple web page that contains some text, a Log in button, and a Log out button. In later steps, we will implement the onclick events for both steps such that each calls the correct function from the Authgear Web JavaScript SDK.
The Web JS SDK is available on a CDN that you can include in any webpage using the following script tag:
The Web JS SDK is also available as . That can be installed using any of the following commands:
We recommend that you use the npm package to add Authgear to your web application when you're using build tools like Vite and Webpack, and when building with frameworks like React, Vue, Angular, etc.
The easiest way to add a JavaScript library such as the Authgear SDK to a generic Single Page Application (a basic .html file page), is to use a CDN. Hence, we'll use the CDN method to add the Authgear Web JavaScript SDK to our demo application for this tutorial.
To install the Authgear SDK, add the Authgear SDK CDN <script> tag to index.html on a new line just before the </body> . Your index.html should look like this at this point:
With that, we have added the Authgear SDK to a basic HTML page and we are ready to start making calls to its functions.
At this point, the structure of your project folder should look like this:
To test your progress so far save your files then run the npm run dev command. Next open localhost:3000 on your preferred web browser and you should see a page that looks like this:
Create a new public/js directory in the root of your project directory.
Create a new file called app.js in the public/js directory. Add the following content to app.js:
In app.js, the configureClient() function gets an instance of the Authgear Web SDK (authgearClient) and then calls the configure() function of the SDK to initialize Authgear.
You can find value for clientID and endpoint from your Authgear client application configuration page.
Finally, link app.js in index.html using <script src="js/app.js"></script> just above the line with the Authgear CDN <script> tag as shown below:
When the user clicks login/signup on your website, make a start authorization call to redirect them to the login/signup page (AuthUI).
In this step, we'll implement the login() function that is called when the Log in button is pressed.
Update app.js by adding the following code after the declaration of the configureClient() function:
After the user authenticates on the login page, the user will be redirected to the redirectURI with a code parameter in the URL query. In the redirectURI of your application, make a finish authorization call to handle the authentication result. This will attempt to exchange the code for the access token and user info.
Once authorization succeeds, the application should be able to display user info and access protected resources.
To handle the redirect after authentication, we'll call the Authgear SDK's finishAuthentication() function when there's a code parameter in the URL of the current page. To do that, update the window.onload callback in app.js to the following:
The updateUI() function will update the state of the webpage when the user's logged-in state changes. Add the following code to the end of app.js to implement updateUI:
The complete content of app.js at the end of this step should look like this:
At this point, your file structure should look like this:
Save all changes in your code, and rerun your app on a web browser. This time, clicking on the Log in button should redirect you to your Authgear project's user login page (AuthUI).
To add a User Settings button to your app, add the following tag to your index.html just below the Logout button:
Next, add the following code to app.js: just below the logout() function:
Finally, add the following line to the end of your updateUI() function so that the User Settings button is displayed when the user is authenticated:
Save your work and run your app again. When you click on the User Settings button, your web app should open the pre-built User Settings page.
When you start launching the application. You may want to know if the user has logged in. (e.g. Redirect users to log in if they haven't logged in). The sessionState reflects the user logged-in state in the SDK local state. That means even thesessionState is AUTHENTICATED, the session may be invalid if it is revoked remotely. After initializing the Authgear SDK, call fetchUserInfo to update the sessionState as soon as it is proper to do so.
The value of sessionState can be UNKNOWN, NO_SESSION or AUTHENTICATED. Initially the sessionState is UNKNOWN. After a call to authgearClient.configure, the session state would become AUTHENTICATED if a previous session was found, or NO_SESSION if such session was not found.
In some cases, you may need to obtain current user info through the SDK. (e.g. Display email address in the UI). Use the fetchUserInfo function to obtain the user info.
See more user info .
Use the logout function to log out the user. The user will be redirected to your Authgear endpoint to log out their session. You should provide the redirectURI for the user to return to your app.
Once you have logged-in user, you can start making authenticated requests to backend APIs as described below.
There are two ways to include the access token in the HTTP requests to your application server.
Authgear SDK provides the fetch function for you to call your application server. This fetch function will include the Authorization header in your application request, and handle refresh access token automatically. The authgearClient.fetch implements .
You can get the access token through authgearClient.accessToken. Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call to refresh the access token only if it is expired. Include the access token in the Authorization header of the application request.
To protect your application server from unauthorized access. You will need to .
For detailed documentation on the JavaScript Web SDK, visit
How to integrate with a Flutter app
This guide provides instructions on integrating Authgear with a Flutter app. Supported platforms include:
Flutter 2.5.0 or higher
Android minimum SDK 30 (Android 11 or later)
Follow this guide to add Authgear to your Flutter app in 🕐 10 minutes.
Signup for an Authgear Portal account in . Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an application in the project.
Go to Applications on the left menu bar.
You will see the "New Application" page or Click ⊕Add Application in the top tool bar.
Input the name of your application and select Native App as the application type. Click "Save".
You will see a list of guides that can help you for setting up, then click "Next".
In your IDE, define a custom URI scheme that Authgear will use to redirect users back to your app after they have authenticated , For your demo application for this guide, the URI scheme will be: com.example.authgeardemo.flutter://host/path. To learn more about setting up URI Scheme in flutter, visit .
Head back to Authgear Portal, fill in the Redirect URI that you have defined in the previous step.
Click "Save" and note the Client ID. and Endpoint. You can also obtain them from the Applications list later.
In this part of the guide, we'll add user Authentication to a simple demo app using the Authgear Flutter SDK.
The demo app will have a login button that users can click to initiate the authentication flow. It will also include a group of widgets for greeting logged-in users, opening the user settings page, and logout.
If you're new to Flutter, follow the official to see how you can install Flutter on your computer.
Run the following command to create a new Flutter project:
Run the following command from the root directory of your Flutter project to install the Authgear SDK:
First, import Authgear at the top of lib/main.dart:
Next, create a field variable _authgear of type Authgear and an _init() method in your page's State class:
Replace "<AUTHGEAR_ENDPOINT>" and "<ClIENT_ID>" with the client ID and endpoint for the client application you created earlier.
Finally, override the initState() method for your State class to call your new _init() method. This will initiate a new instance of the Authgear SDK that you'll use to perform operations like starting an authentication flow.
In this step, we'll add a login button and other UI widgets to our demo application.
To do that, first, add a _userInfo field variable to the State class:
Our demo app will use the value of the _userInfo variable to determine when to show a login button or the group of widgets for logged-in users.
Next, replace the widget in body attribute of Scaffold with the following:
Now implement the loggedInUserScreen() custom widget like this within the State class:
In the next step, we'll implement the _onPressedAuthenticate() method.
Here we will implement the _onPressedAuthenticate() method that will be called when a user clicks on the Login button.
Add the following method in the State class:
The above code calls the authenticate() method of the Authgear SDK. This will start a new authentication flow. Replace the value for the redirectURI argument with the redirect URI you registered in your client application.
Create empty _onPressedSettings() and _onPressedLogout() methods in your State class for now so that you can build application:
At this point, the full code for main.dart should look like this:
Checkpoint
At this point, you can save your work and run the following command to test your app on a mobile device or emulator:
When your app runs, you should see the Login button, clicking on it should start a new Authentication. However, you may not be able to complete authentication because we're yet to configure our app to handle redirect from Authgear.
To finish the integration, setup the app to handle the redirectURI specified in the application. This part requires platform specific integration.
Here you declare the URL schemes supported by your app, so the device can redirect the user to the app after authentication using the redirect URI.
Add the following <activity> entry to the /android/app/src/main/AndroidManifest.xml of your app. The intent system would dispatch the redirect URI to OAuthRedirectActivity and the SDK would handle the rest.
You also need to add a queries section to AndroidManifest.xml.
Remove the following line from AndroidManifest.xml because this setting conflicts with the SDK:
Next, open /android/app/build.gradle and set minSdk to 30:
In the Info.plist in your project's ios folder, add the matching redirect URI by adding the key CFBundleURLTypes and the values inside <dict> as shown as the following example.
Now if you run your app again, you should be able to login, be redirected back to your app and view the group of widgets that's for logged-in users.
To log out the user from the current app session, you need to invoke thelogout method of the SDK.
Update the empty _onPressedLogout you added earlier so that it calls the logout method.
Authgear provides a pre-built user settings page from which your users can view and edit their profile details, and change security settings like password, and 2FA.
The SDK includes a method that you can use to easily open this user settings page.
Update the empty _onPressedSettings method you added earlier so it initiates the process of opening the user settings page.
At this point, our application already shows the current user's info (their unique ID, sub). However, the Authgear SDK includes a getUserInfo() method that you can call explicitly to get an object that contains the current user's information like their email, phone number, name, etc.
Calling this getUserInfo() method can also refresh the current user's access token to make sure that their session state is really authenticated, that is, an logged-in user is not using an expired access token.
Update your _init() method to check the user's logged-in state and fetch their user info when the state is SessionState.authenticated.
When you start launching the application. You may want to know if the user has logged in. (e.g. Show users the login page if they haven't logged in). The sessionState reflects the user logged in state in the SDK local state. That means even the sessionState is SessionState.authenticated, the session may be invalid if it is revoked remotely. After initializing the Authgear SDK, call fetchUserInfo to update the sessionState as soon as it is proper to do so.
The value of sessionState can be SessionState.unknown, SessionState.noSession or SessionState.authenticated. Initially, the sessionState is SessionState.unknown. After a call to authgear.configure, the session state would become SessionState.authenticated if a previous session was found, or SessionState.noSession if such session was not found.
To include the access token to the HTTP requests to your application server, use wrapHttpClient.
The wrapped client will include the Authorization header in every HTTP request, and refresh access token automatically.
To protect your application server from unauthorized access. You will need to integrate your backend with Authgear.
For detailed documentation on the Flutter SDK, visit
cd cloud_functionsnpm install -g firebase-toolsfirebase initconst { onRequest } = require("firebase-functions/v2/https");
const jwt = require("jsonwebtoken");
const jwks = require("jwks-rsa");
const firebaseAdmin = require("firebase-admin");
const authgearEndpoint = ""; //place your authgear app endpoint here
// Get JWKs URI from Open ID Configuration documents
const getJwksUri = async (authgearEndpoint) => {
const config_endpoint =
authgearEndpoint + "/.well-known/openid-configuration";
const response = await fetch(config_endpoint);
const data = await response.json();
return data.jwks_uri;
};
// Options for JWT verification
const options = {
algorithms: ["RS256"],
issuer: authgearEndpoint,
};
const checkReq = (req) => {
const headerErr = ["must specify an Authorization header", null];
const formatErr = ["format is 'Authorization: Bearer <token>'", null];
if (!req) return "server error (request was invalid)";
const { headers } = req;
if (!headers) return headerErr; // missing header
const { authorization } = headers;
if (!authorization) return headerErr; // missing Authorization Header
const parts = authorization.split(" ");
if (parts.length != 2) return formatErr; // Authorization header format invalid
const [scheme, credentials] = parts;
if (!/^Bearer$/i.test(scheme)) return formatErr; // Authorization header is not Bearer
return [false, credentials];
};
firebaseAdmin.initializeApp();
exports.getFirebaseToken = onRequest(async (req, res) => {
res.set("Access-Control-Allow-Origin", "*");
if (req.method === "OPTIONS") {
res.set("Access-Control-Allow-Methods", "GET");
res.set("Access-Control-Allow-Headers", "Authorization");
res.set("Access-Control-Max-Age", "3600");
return res.status(204).send("");
}
const [message, token] = checkReq(req);
if (message) {
return res.status(500).send({ message }); // return error message if checkReq failed
} else {
const decodedAccessToken = jwt.decode(token, { complete: true });
// get signing key from JWKs with the "kid" in decoded access token
jwksUri = await getJwksUri(authgearEndpoint);
const client = jwks({
rateLimit: true,
strictSsl: true,
jwksUri: jwksUri,
});
const signingKey = await client.getSigningKey(
decodedAccessToken.header.kid
);
try {
const decoded = jwt.verify(token, signingKey.publicKey, options); // verify jwt
const uid = decoded.sub; // if the jwt is verified, use "sub" in JWT as uid
const firebaseToken = await firebaseAdmin.auth().createCustomToken(uid); // create Firebase custom token with uid
return res.json({ firebaseToken }); // return Firebase custom token
} catch (err) {
return res.status(500).send(err);
}
}
});
npm i jwks-rsa
npm i jsonwebtokenimport { initializeApp } from 'firebase/app';
import { getAuth } from 'firebase/auth';
import { getFirestore } from "firebase/firestore";
// Your web app's Firebase configuration
const firebaseConfig = {
apiKey: "",
authDomain: "",
projectId: "",
storageBucket: "",
messagingSenderId: "",
appId: ""
};
// Initialize Firebase
const app = initializeApp(firebaseConfig);
export const auth = getAuth(app);
export const db = getFirestore(app);import React, { useEffect, useState, useContext } from "react";
import authgear from "@authgear/web";
import { UserContext } from "./context/UserProvider.js";
import { signInWithCustomToken, UserCredential } from "firebase/auth";
import { collection, getDocs, addDoc, deleteDoc, doc } from "firebase/firestore";
import { auth, db } from "../firebase.js";
interface Todo {
id: string;
text: string;
userId: string;
}
const Todo: React.FC = () => {
const { isLoggedIn } = useContext(UserContext);
const [firebaseUser, setFirebaseUser] = useState<object>({});
const [authError, setAuthError] = useState<boolean>(false);
const [todos, setTodos] = useState<Todo[]>([]);
const [newTodo, setNewTodo] = useState("");
useEffect(() => {
async function getFirebaseUser() {
if (isLoggedIn) {
const firebaseFunctionEndpoint = ""; // place your cloud function endpoint here.
try {
const getCustomToken = await authgear
.fetch(firebaseFunctionEndpoint)
.then((response) => response.json());
if (getCustomToken.firebaseToken !== null) {
const firebaseUserObj = await signInWithCustomToken(
auth,
getCustomToken.firebaseToken
);
setFirebaseUser(firebaseUserObj);
setAuthError(false);
}
} catch (e) {
console.log(e);
setAuthError(true);
}
} else {
setAuthError(true);
}
}
getFirebaseUser()
.then(() => {
fetchTodos();
})
.catch((e) => {
console.error(e);
});
}, [authgear]);
async function fetchTodos() {
try {
const querySnapshot = await getDocs(collection(db, "todos"));
const todoList = querySnapshot.docs.map((doc) => ({
id: doc.id,
...doc.data(),
})) as Todo[];
setTodos(todoList);
} catch (error) {
console.error("Error fetching todos:", error);
}
}
async function addTodo(e: React.FormEvent) {
e.preventDefault();
if (!newTodo.trim() || authError) return;
try {
await addDoc(collection(db, "todos"), {
text: newTodo,
userId: (firebaseUser as UserCredential).user.uid,
createdAt: new Date(),
});
setNewTodo("");
fetchTodos();
} catch (error) {
console.error("Error adding todo:", error);
}
}
async function deleteTodo(id: string) {
try {
await deleteDoc(doc(db, 'todos', id));
fetchTodos();
} catch (error) {
console.error('Error deleting todo:', error);
}
}
if (!authError) {
return (
<div className="app">
<div className="todo-container">
<form onSubmit={addTodo}>
<input
type="text"
value={newTodo}
onChange={(e) => setNewTodo(e.target.value)}
placeholder="Add a new todo"
/>
<button type="submit">Add Todo</button>
</form>
<ul>
{todos.map((todo) => (
<li key={todo.id}>
{todo.text}
<button onClick={() => deleteTodo(todo.id)}>Delete</button>
</li>
))}
</ul>
</div>
</div>
);
} else {
return (
<div>
<p>User not logged in</p>
</div>
);
}
};
export default Todo;
<Route path="/todos" element={<Todo />} />import Todo from "./Todo";<Link to="/todos">My Todos</Link>service cloud.firestore {
match /databases/{database}/documents {
match /todos/{userId} {
allow read: if request.auth.uid != null;
allow write: if request.auth.uid != null;
}
}
}com.example.authgeardemo://host/pathdependencyResolutionManagement {
repositoriesMode.set(RepositoriesMode.FAIL_ON_PROJECT_REPOS)
repositories {
mavenCentral()
maven { url 'https://jitpack.io' }
}
}dependencies {
// Other implementations
implementation 'com.github.authgear:authgear-sdk-android:SNAPSHOT'
}compileOptions {
coreLibraryDesugaringEnabled true
}dependencies {
// Other implementations
coreLibraryDesugaring 'com.android.tools:desugar_jdk_libs:2.0.3'
}class MainActivity : AppCompatActivity() {
private lateinit var authgear: Authgear
override fun onCreate(savedInstanceState: Bundle?) {
super.onCreate(savedInstanceState)
...
}
}override fun onCreate(savedInstanceState: Bundle?) {
super.onCreate(savedInstanceState)
setContentView(R.layout.activity_main)
authgear = Authgear(application, "<ClIENT_ID>", "<AUTHGEAR_ENDPOINT>")
authgear.configure(object : OnConfigureListener {
override fun onConfigured() {
// Authgear can be used.
}
override fun onConfigurationFailed(throwable: Throwable) {
Log.d("TAG", throwable.toString())
// Something went wrong, check the client ID or endpoint.
}
})
}class MainActivity : AppCompatActivity() {
private lateinit var authgear: Authgear
override fun onCreate(savedInstanceState: Bundle?) {
super.onCreate(savedInstanceState)
setContentView(R.layout.activity_main)
authgear = Authgear(application, "<ClIENT_ID>", "<AUTHGEAR_ENDPOINT>")
authgear.configure(object : OnConfigureListener {
override fun onConfigured() {
// Authgear can be used.
}
override fun onConfigurationFailed(throwable: Throwable) {
Log.d("TAG", throwable.toString())
// Something went wrong, check the client ID or endpoint.
}
})
}
}<TextView
android:id="@+id/app_title"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:text="My Demo App!"
app:layout_constraintBottom_toBottomOf="parent"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toTopOf="parent" />
<Button
android:id="@+id/login_btn"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:text="Login"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toBottomOf="@+id/textView" /><ProgressBar
android:id="@+id/progressBar"
style="?android:attr/progressBarStyleHorizontal"
android:layout_width="0dp"
android:layout_height="wrap_content"
android:layout_marginTop="48dp"
android:indeterminate="true"
android:visibility="invisible"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toTopOf="parent" />
<TextView
android:id="@+id/welcome_text"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:text="welcome user"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toTopOf="@+id/login_btn" />
<Button
android:id="@+id/user_settings_btn"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:text="User Settings"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toBottomOf="@+id/welcome_text" />
<Button
android:id="@+id/logout_btn"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:text="Logout"
app:layout_constraintEnd_toEndOf="parent"
app:layout_constraintStart_toStartOf="parent"
app:layout_constraintTop_toBottomOf="@+id/user_settings_btn" />
<androidx.constraintlayout.widget.Group
android:id="@+id/logged_in_views"
android:layout_width="wrap_content"
android:layout_height="wrap_content"
android:visibility="gone"
app:constraint_referenced_ids="welcome_text,user_settings_btn,logout_btn" />buildFeatures {
viewBinding = true
}class MainActivity : AppCompatActivity() {
private lateinit var authgear: Authgear
private lateinit var binding: ActivityMainBinding
override fun onCreate(savedInstanceState: Bundle?) {
super.onCreate(savedInstanceState)
binding = ActivityMainBinding.inflate(layoutInflater)
val view = binding.root
setContentView(view)
// ... the rest of onCreate continues
}
}fun startLogin() {
binding.progressBar.visibility = View.VISIBLE
val options = AuthenticateOptions("com.example.authgeardemo://host/path")
authgear.authenticate(options, object : OnAuthenticateListener {
override fun onAuthenticated(userInfo: UserInfo) {
updateUi(authgear)
}
override fun onAuthenticationFailed(throwable: Throwable) {
binding.progressBar.visibility = View.INVISIBLE
Log.d("TAG", throwable.toString())
}
})
}fun updateUi(authgear: Authgear) {
val state = authgear.sessionState
if (state.toString() == ("AUTHENTICATED")) {
binding.loginBtn.visibility = View.GONE
binding.loggedInViews.visibility = View.VISIBLE
// Get userInfo and display in welcome text
authgear.fetchUserInfo(object: OnFetchUserInfoListener {
override fun onFetchedUserInfo(userInfo: UserInfo) {
binding.welcomeText.text = userInfo.email
}
override fun onFetchingUserInfoFailed(throwable: Throwable) {
Log.d("TAG", "Failed to fetch UserInfo")
}
})
} else {
binding.loggedInViews.visibility = View.GONE
binding.loginBtn.visibility = View.VISIBLE
}
binding.progressBar.visibility = View.INVISIBLE
}binding.loginBtn.setOnClickListener {
startLogin()
}<!-- Your application configuration. Omitted here for brevity -->
<application>
<!-- Other activities or entries -->
<!-- Add the following activity -->
<!-- android:exported="true" is required -->
<!-- See https://developer.android.com/about/versions/12/behavior-changes-12#exported -->
<activity android:name="com.oursky.authgear.OAuthRedirectActivity"
android:exported="true"
android:launchMode="singleTask">
<intent-filter>
<action android:name="android.intent.action.VIEW" />
<category android:name="android.intent.category.DEFAULT" />
<category android:name="android.intent.category.BROWSABLE" />
<!-- Configure data to be the exact redirect URI your app uses. -->
<!-- Here, we are using com.authgear.example://host/path as configured in the portal -->
<!-- NOTE: The redirectURI supplied in AuthenticateOptions *has* to match as well -->
<data android:scheme="com.example.authgeardemo"
android:host="host"
android:pathPrefix="/path"/>
</intent-filter>
</activity>
</application><?xml version="1.0" encoding="utf-8"?>
<manifest xmlns:android="http://schemas.android.com/apk/res/android">
<!-- Other elements such <application> -->
<queries>
<intent>
<action android:name="android.support.customtabs.action.CustomTabsService" />
</intent>
</queries>
</manifest>fun logout() {
binding.progressBar.visibility = View.VISIBLE
authgear.logout(true, object: OnLogoutListener {
override fun onLogout() {
updateUi(authgear)
}
override fun onLogoutFailed(throwable: Throwable) {
Log.d("TAG", throwable.toString())
}
})
}binding.logoutBtn.setOnClickListener {
logout()
}fun openUserSettings() {
authgear.open(Page.SETTINGS)
}binding.userSettingsBtn.setOnClickListener {
openUserSettings()
}// After authgear.configure, it only reflect SDK local state.
// value can be NO_SESSION or AUTHENTICATED
val state = authgear.sessionStatetry {
authgear.refreshAccessTokenIfNeededSync()
} catch (e: OAuthException) {
// Something went wrong
}
val accessToken = authgear.accessToken
if (accessToken == null) {
// The user is not logged in, or the token is expired.
// It is up to the caller to decide how to handle this situation.
// Typically, the request could be aborted
// immediately as the response would be 401 anyways.
return
}
val headers = mutableMapOf<String, String>()
headers["authorization"] = "Bearer $accessToken"
// Submit the request with the headers..git clone https://github.com/authgear/authgear-example-nextjs.gitnpx create-next-app authgear-example-nextjsnpm install next-authimport NextAuth from "next-auth"
export const authOptions = {
providers: [
{
id: "authgear",
name: "Authgear",
type: "oauth",
issuer: process.env.AUTHGEAR_ISSUER,
clientId: process.env.AUTHGEAR_CLIENT_ID,
clientSecret: process.env.AUTHGEAR_CLIENT_SECRET,
wellKnown: `${process.env.AUTHGEAR_ISSUER}/.well-known/openid-configuration`,
authorization: { params: { scope: "openid offline_access https://authgear.com/scopes/full-userinfo" } },
client: {
token_endpoint_auth_method: "client_secret_post",
},
profile(profile) {
return {
id: profile.sub,
}
},
}
],
callbacks: {
async jwt({ token, account, profile }) {
if (account) {
token.accessToken = account.access_token
token.id = profile.sub
token.name = profile.name
}
return token
},
async session({ session, token, user }) {
session.accessToken = token.accessToken
session.user.id = token.id
session.user.name = token.name
return session
}
},
}
export default NextAuth(authOptions)import '@/styles/globals.css'
import { SessionProvider } from "next-auth/react"
export default function App({
Component,
pageProps: {session, ...pageProps},
}) {
return (
<SessionProvider session={session}>
<Component {...pageProps} />
</SessionProvider>
);
}import { useSession, signIn, signOut } from "next-auth/react"
export default function Component() {
const { data: session } = useSession()
if (session) {
return (
<>
Status: Logged in as {session.user.id} <br />
<button onClick={() => signOut()}>Log out</button>
</>
)
}
return (
<>
Status: Not logged in <br />
<button onClick={() => signIn()}>Log in</button>
</>
)
}import { useSession, signIn, signOut } from "next-auth/react"
export default function Component() {
const { data: session } = useSession()
if (session) {
return (
<>
Status: Logged in as {session.user.id} <br />
<button onClick={() => signOut()}>Log out</button>
</>
)
}
return (
<>
Status: Not logged in <br />
<button onClick={() => signIn()}>Log in</button>
</>
)
}AUTHGEAR_ISSUER={your-authgear-app-endpoint}
AUTHGEAR_CLIENT_ID={your-client-id}
AUTHGEAR_CLIENT_SECRET={your-client-secret}npm run dev

















How to integrate with a React Native app
This guide provides instructions on integrating Authgear with a React Native app. Supported platforms include:
React Native 0.60.0 or higher
Follow this guide to add Authgear to your React Native app in 🕐 10 minutes.
Signup for an Authgear Portal account in . Or you can use your self-deployed Authgear.
From the Project listing, create a new Project or select an existing Project. After that, we will need to create an application in the project.
Go to Applications on the left menu bar.
You'll see the "New Application" page, or Click ⊕Add Application in the top tool bar.
Input the name of your application and select Native App as the application type. Click "Save".
On the next screen, you will see a list of guides that can help you with setting up, click "Next" to continue.
In your IDE, define a custom URI scheme that will be used to redirect users back to your app after they have authenticated with Authgear. For example, in our example app, we will define the following URI scheme:
For further instruction on setting up custom URI scheme in React Native, see
Now head back to Authgear Portal, and add the URI that you have defined (com.authgear.example.rn://host/path for this example) as an Authorized Redirect URI.
Click "Save" and note the Client ID and Endpoint for your Authgear client application. You can also obtain it again from the Applications list later.
In this section, we'll walk through the steps to create a new React Native app and use the Authgear SDK to add user authentication to the app.
Run the following command to create a new React Native project:
For a more detailed guide on how to create a project and set up a development environment for React Native, follow the .
Run the following commands from the root directory of your React Native project to install the Authgear SDK:
In this step, we'll implement the code to initialize an instance of the Authgear SDK which we will be using to interact with the Authgear client application we created earlier.
First, open the App.tsx file in your project then add the following import statements at the top:
Add the following code at the top inside the App() function in App.tsx to configure a new Authgear instance and set up a delegate that will help our app to know the current state of a user's session (whether they're logged in or not):
Replace <CLIENT_ID> and <AUTHGEAR_ENDPOINT> with the Client ID and Endpoint for your Authgear client application.
The above code includes a postConfigure() method that helps to get the true session state for a user that was previously logged in.
Replace the content for the return statement in the App() function inside the App.tsx file with the following:
Import the necessary components at the top App.tsx:
In this step, you will implement an authenticate() method that calls the authenticate() method of the Authgear SDK. The Login button we added in the previous step calls this authenticate() method to start an authentication flow.
Add the following code to the App() function just after the useEffect() for the configure() method in step 3:
At this point the complete code in your App.tsx should look like this:
Now save your work and try running your app on Android or iOS using any of the following commands:
Android
iOS
When your app opens, if you click on the Login button, you should be redirected to the Authentication UI. However, you can't complete authentication because we are yet to handle the redirect URI.
To finish the integration, set up the app to handle the redirect URI specified in your Authgear client application. This part requires platform-specific integration.
Add the following activity entry to the android/app/src/main/AndroidManifest.xml of your React Native project. The intent system would dispatch the redirect URI to OAuthRedirectActivity and the sdk would handle the rest.
You also need to add a queries section to AndroidManifest.xml.
In ios/<your_project>/Info.plist, add the matching redirect URI.
Now let's add a Logout feature to our example app so users can logout and end their session.
We'll add a Logout button and implement a logout() method that calls the corresponding logout() method of the Authgear SDK:
Add a logout() method to your App() function after the authenticate() method you added earlier:
Next, add the Logout button and call the logout() method from onPress. Add the button to the return statement for App() just below <Text style={{paddingTop: 50, paddingBottom: 16}}> Welcome User</Text> :
Save your code and run the app. Click the Logout button and the user should be logged out.
The Authgear SDK includes a fetchUserInfo() method that returns details such as user ID, email, phone number, etc about the current user.
In this step, we'll add a Show User Info button to our app. This button will call the fetchUserInfo() to demonstrate how the method works.
Add a showUserInfo() method to your App() function just below the logout() method:
The showUserInfo() method calls the fetchUserInfo() method of the Authgear SDK and displays the data returned in an Alert.
Next, add the Show User Info button to the return statement of App() just below the Logout button from the previous step:
Authgear offers a pre-built User Settings page for users of your application to view and modify their profile and security details.
In this step, we'll use the open() method in the Authgear SDK to open this User Settings page when a logged-in user clicks on a button.
Add an openSettings() method to your App() function just below the showUserInfo() from the previous step:
Next, add a User Settings button to the return statement of App() just below the Show User Info button:
Now run your app and you should be able to access the User Settings page when you click on the User Settings button.
When you start launching the application. You may want to know if the user has logged in. (e.g. Show users the login page if they haven't logged in).
The sessionState reflects the user logged-in state in the SDK local state. That means even if the sessionState is AUTHENTICATED, the session may be invalid if it is revoked remotely. Hence, after initializing the Authgear SDK, call fetchUserInfo to update the sessionState as soon as it is proper to do so. We demonstrated this in our example app using the postConfigure() method.
The value of sessionState can be UNKNOWN, NO_SESSION or AUTHENTICATED. Initially, the sessionState is UNKNOWN. After a call to authgear.configure(), the session state would become AUTHENTICATED if a previous session was found, or NO_SESSION if such session was not found.
To include the access token in the HTTP requests to your application server, there are two ways to achieve this.
Authgear SDK provides the fetch function for you to call your application server. The fetch function will include the Authorization header in your application request, and handle refresh access token automatically. authgear.fetch implement .
You can access the access token through authgear.accessToken. Call refreshAccessTokenIfNeeded() every time before using the access token. The refreshAccessTokenIfNeeded() function will check and make the network call to refresh the access token only if it has expired.
Include the access token in the Authorization header of your application request.
To protect your application server from unauthorized access. You will need to .
For detailed documentation on the JavaScript React Native SDK, visit
Follow this quickstart tutorial to add authentication to your Vue application
Authgear helps you add user logins to your Vue apps. It provides a prebuilt login page and user settings page that accelerate the development.
Follow this 🕐 15-minute tutorial to create a simple app using Vue with Authgear SDK.
npm create vite@latest my-app -- --template react-ts cd my-app
npm install"dev": "vite --port 4000",my-app
├── node_modules
│ └── (...)
├── package-lock.json
├── package.json
├── index.html
└── src
├── App.tsx
└── main.tsxnpm install --save --save-exact @authgear/webimport { createRoot } from 'react-dom/client'
import App from './App.tsx'
import authgear from "@authgear/web"
async function init() {
try {
// configure Authgear container instance
await authgear.configure({
endpoint: import.meta.env.VITE_AUTHGEAR_ENDPOINT,
clientID: import.meta.env.VITE_AUTHGEAR_CLIENT_ID,
sessionType: "refresh_token",
});
} finally {
createRoot(document.getElementById("root")!).render(<App />);
}
}
init().catch((e) => {
// Error handling
console.error(e)
});VITE_AUTHGEAR_CLIENT_ID=<CLIENT_ID>
VITE_AUTHGEAR_ENDPOINT=<AUTHGEAR_ENDPOINT>
VITE_AUTHGEAR_REDIRECT_URL=http://localhost:4000/auth-redirect// src/context/UserProvider.tsx
import React, { createContext, useEffect, useState, useMemo } from "react";
import authgear from "@authgear/web";
interface UserContextValue {
isLoggedIn: boolean;
}
export const UserContext = createContext<UserContextValue>({
isLoggedIn: false,
});
interface UserContextProviderProps {
children: React.ReactNode;
}
const UserContextProvider: React.FC<UserContextProviderProps> = ({
children,
}) => {
// By default the user is not logged in
const [isLoggedIn, setIsLoggedIn] = useState<boolean>(false);
useEffect(() => {
// When the sessionState changed, logged in state will also be changed
authgear.delegate = {
onSessionStateChange: (container) => {
// sessionState is now up to date
// Value of sessionState can be "NO_SESSION" or "AUTHENTICATED"
const sessionState = container.sessionState;
if (sessionState === "AUTHENTICATED") {
setIsLoggedIn(true);
} else {
setIsLoggedIn(false);
}
},
};
}, [setIsLoggedIn]);
const contextValue = useMemo<UserContextValue>(() => {
return {
isLoggedIn,
};
}, [isLoggedIn]);
return (
<UserContext.Provider value={contextValue}>{children}</UserContext.Provider>
);
};
export default UserContextProvider;npm install --save-exact react-router-dom// src/AuthRedirect.tsx
import React, { useEffect, useRef } from "react";
import { useNavigate } from "react-router-dom";
import authgear from "@authgear/web";
const AuthRedirect: React.FC = () => {
const usedToken = useRef(false);
const navigate = useNavigate();
useEffect(() => {
async function updateToken() {
try {
await authgear.finishAuthentication();
} finally {
navigate("/");
usedToken.current = true;
}
}
if (!usedToken.current) {
updateToken().catch((e) => console.error(e));
}
}, [navigate]);
return <></>;
};
export default AuthRedirect;
// src/App.tsx
import React from "react";
import { BrowserRouter as Router, Routes, Route } from 'react-router-dom';
import Home from './Home';
import AuthRedirect from './AuthRedirect';
import UserContextProvider from './context/UserProvider';
const App: React.FC = () => {
return (
<UserContextProvider>
<Router>
<Routes>
<Route path="/auth-redirect" element={<AuthRedirect />} />
<Route path="/" element={<Home />} />
</Routes>
</Router>
</UserContextProvider>
);
}
export default App;src
├── App.tsx
├── AuthRedirect.tsx
├── Home.tsx
├── context
│ └── UserProvider.tsx
└── main.tsx// src/Home.tsx
import React, { useEffect, useState, useCallback, useContext } from 'react';
import authgear, { PromptOption } from '@authgear/web';
const Home: React.FC = () => {
const startLogin = useCallback(() => {
authgear
.startAuthentication({
redirectURI: import.meta.env.VITE_AUTHGEAR_REDIRECT_URL,
prompt: PromptOption.Login,
})
.then(
() => {
// started authentication, user should be redirected to Authgear
},
err => {
// failed to start authentication
}
);
}, []);
return (
<div>
<h1>Home Page</h1>
<div>
<button onClick={startLogin}>Login</button>
</div>
</div>
);
}
export default Home;
// src/Home.tsx
import React, { useEffect, useState, useCallback, useContext } from "react";
import authgear, { PromptOption } from "@authgear/web";
import { UserContext } from "./context/UserProvider";
const Home: React.FC = () => {
const [greetingMessage, setGreetingMessage] = useState<string>("");
const [isLoading, setIsLoading] = useState<boolean>(false);
const { isLoggedIn } = useContext(UserContext);
useEffect(() => {
async function updateGreetingMessage() {
setIsLoading(true);
try {
if (isLoggedIn) {
const userInfo = await authgear.fetchUserInfo();
setGreetingMessage("The current User sub: " + userInfo.sub);
}
} finally {
setIsLoading(false);
}
}
updateGreetingMessage().catch((e) => {
console.error(e);
});
}, [isLoggedIn]);
const startLogin = useCallback(() => {
authgear
.startAuthentication({
redirectURI: "http://localhost:4000/auth-redirect",
prompt: PromptOption.Login,
})
.then(
() => {
// started authentication, user should be redirected to Authgear
},
(err) => {
// failed to start authentication
}
);
}, []);
return (
<div>
<h1>Home Page</h1>
{isLoading && "Loading"}
{greetingMessage ? <span>{greetingMessage}</span> : null}
{!isLoggedIn && (
<div>
<button type="button" onClick={startLogin}>
Login
</button>
</div>
)}
</div>
);
};
export default Home;{!isLoggedIn && (
<div>
<button type="button" onClick={startLogin}>
Login
</button>
</div>
)}{isLoggedIn && (
<div>
<button onClick={logout}>Logout</button>
</div>
)}const logout = useCallback(() => {
authgear
.logout({
redirectURI: "http://localhost:4000/",
})
.then(
() => {
setGreetingMessage('');
},
(err) => {
console.error(err);
}
);
}, []);{isLoggedIn && (
<a target="_blank" rel="noreferrer" onClick={userSetting} href="#">
User Setting
</a>
)}import authgear, { Page } from "@authgear/web";
const userSetting = useCallback((e: React.MouseEvent<HTMLAnchorElement>) => {
e.preventDefault();
e.stopPropagation();
authgear.open(Page.Settings);
}, []);// src/Home.tsx
import React, { useEffect, useState, useCallback, useContext } from "react";
import { UserContext } from "./context/UserProvider";
import authgear, { Page, PromptOption } from "@authgear/web";
const Home: React.FC = () => {
const [greetingMessage, setGreetingMessage] = useState<string>("");
const [isLoading, setIsLoading] = useState<boolean>(false);
const { isLoggedIn } = useContext(UserContext);
useEffect(() => {
async function updateGreetingMessage() {
setIsLoading(true);
try {
if (isLoggedIn) {
const userInfo = await authgear.fetchUserInfo();
setGreetingMessage("The current User sub: " + userInfo.sub);
}
} finally {
setIsLoading(false);
}
}
updateGreetingMessage().catch((e) => {
console.error(e);
});
}, [isLoggedIn]);
const startLogin = useCallback(() => {
authgear
.startAuthentication({
redirectURI: "http://localhost:4000/auth-redirect",
prompt: PromptOption.Login,
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
}, []);
const logout = useCallback(() => {
authgear
.logout({
redirectURI: "http://localhost:4000/",
})
.then(
() => {
setGreetingMessage("");
},
(err) => {
console.error(err);
}
);
}, []);
const userSetting = useCallback((e: React.MouseEvent<HTMLAnchorElement>) => {
e.preventDefault();
e.stopPropagation();
authgear.open(Page.Settings);
}, []);
return (
<div>
{/* eslint-disable-next-line react/forbid-elements */}
<h1>Home Page</h1>
{isLoading && "Loading"}
{greetingMessage ? <span>{greetingMessage}</span> : null}
{!isLoggedIn && (
<div>
<button type="button" onClick={startLogin}>
Login
</button>
</div>
)}
{isLoggedIn && (
<div>
<button type="button" onClick={logout}>
Logout
</button>
<br />
<a target="_blank" rel="noreferrer" onClick={userSetting} href="#">
User Setting
</a>
</div>
)}
</div>
);
};
export default Home;authgear
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgear
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgear.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});mkdir my-webapp
cd my-webappnpm init -ynpm install expressnpm install -D nodemonconst express = require("express");
const { join } = require("path");
const app = express();
// Serve static assets from the /public folder
app.use(express.static(join(__dirname, "public")));
// Serve the index page for all other requests
app.get("/*", (_, res) => {
res.sendFile(join(__dirname, "index.html"));
});
// Listen on port 3000
app.listen(3000, () => console.log("Application running on port 3000"));"start": "node server.js",
"dev": "nodemon server.js"<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8" />
<title>Authgear SPA SDK Sample</title>
<link rel="stylesheet" type="text/css" href="/css/main.css" />
</head>
<body>
<h2>SPA Authentication Sample</h2>
<p>Welcome to our page!</p>
<button id="btn-login" disabled="true" onclick="login()">Log in</button>
<button id="btn-logout" disabled="true" onclick="logout()">Log out</button>
</body>
</html><script src="https://unpkg.com/@authgear/[email protected]/dist/authgear-web.iife.js"></script>npm install --save --save-exact @authgear/webyarn add @authgear/web --exact<!DOCTYPE html>
<html>
<head>
<meta charset="UTF-8" />
<title>Authgear SPA SDK Sample</title>
<link rel="stylesheet" type="text/css" href="/css/main.css" />
</head>
<body>
<h2>SPA Authentication Sample</h2>
<p>Welcome to our page!</p>
<button id="btn-login" disabled="true" onclick="login()">Log in</button>
<button id="btn-logout" disabled="true" onclick="logout()">Log out</button>
<script src="https://unpkg.com/@authgear/[email protected]/dist/authgear-web.iife.js"></script>
</body>
</html>my-webapp
├── index.html
├── server.js
└── package.jsonlet authgearClient = null;
const configureClient = async () => {
authgearClient = window.authgear.default;
await authgearClient.configure({
endpoint: "<YOUR_AUTHGEAR_PROJECT_DOMAIN>",
clientID: "<YOUR_AUTHGEAR_APP_CLIENT_ID>",
sessionType: "refresh_token",
}).then(
() => {
console.log("Authgear client successfully configured!");
},
(err) => {
console.log("Failed to configure Authgear");
}
);
};
window.onload = async () => {
await configureClient();
}<body>
<h2>SPA Authentication Sample</h2>
<p>Welcome to our page!</p>
<button id="btn-login" disabled="true" onclick="login()">Log in</button>
<button id="btn-logout" disabled="true" onclick="logout()">Log out</button>
<script src="js/app.js"></script>
<script src="https://unpkg.com/@authgear/[email protected]/dist/authgear-web.iife.js"></script>
</body>const login = async () => {
await authgearClient
.startAuthentication({
redirectURI: "http://localhost:3000/",
prompt: "login",
})
.then(
() => {
console.log("Logged in!");
},
(err) => {
console.log("Log in failed", err);
}
);
};window.onload = async () => {
await configureClient();
updateUI();
const query = window.location.search;
if (query.includes("code=")) {
await authgearClient.finishAuthentication();
updateUI();
window.history.replaceState({}, document.title, "/");
}
}const updateUI = async () => {
const isAuthenticated = authgearClient.sessionState === "AUTHENTICATED";
document.getElementById("btn-logout").disabled = !isAuthenticated;
document.getElementById("btn-login").disabled = isAuthenticated;
};let authgearClient = null;
const configureClient = async () => {
authgearClient = window.authgear.default;
await authgearClient.configure({
endpoint: "<YOUR_AUTHGEAR_PROJECT_DOMAIN>",
clientID: "<YOUR_AUTHGEAR_CLIENT_APP_ID>",
sessionType: "refresh_token",
}).then(
() => {
console.log("Authgear client successfully configured!");
},
(err) => {
console.log("Failed to configure Authgear");
}
);
};
const login = async () => {
await authgearClient
.startAuthentication({
redirectURI: "http://localhost:3000/",
prompt: "login",
})
.then(
() => {
console.log("Logged in!");
},
(err) => {
console.log("Log in failed", err);
}
);
};
window.onload = async () => {
await configureClient();
updateUI();
const query = window.location.search;
if (query.includes("code=")) {
await authgearClient.finishAuthentication();
updateUI();
window.history.replaceState({}, document.title, "/");
}
}
const updateUI = async () => {
const isAuthenticated = authgearClient.sessionState === "AUTHENTICATED";
document.getElementById("btn-logout").disabled = !isAuthenticated;
document.getElementById("btn-login").disabled = isAuthenticated;
};my-webapp
├── index.html
├── server.js
├── public/js
│ └── app.js
└── package.json<button id="btn-settings" disabled="true" onclick="openUserSettings()">User Settings</button>const openUserSettings = () => {
authgearClient.open("/settings");
}document.getElementById("btn-settings").disabled = !isAuthenticated;// After authgearClient.configure, it only reflect SDK local state.
// value can be NO_SESSION or AUTHENTICATED
let sessionState = authgearClient.sessionState;
if (sessionState === "AUTHENTICATED") {
authgearClient
.fetchUserInfo()
.then((userInfo) => {
// sessionState is now up to date
})
.catch((e) => {
// sessionState is now up to date
// it will change to NO_SESSION if the session is invalid
});
}authgearClient.fetchUserInfo();
authgearClient
.logout({
// user will navigate to the redirectURI after logged out
// make sure it is in the "Post Logout Redirect URIs" in the application portal
redirectURI: "https://yourdomain.com",
})
.then(
() => {
// logged out successfully
},
(err) => {
// failed to logout
}
);authgearClient
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgearClient
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgearClient.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});flutter create myapp
cd myappflutter pub add flutter_authgearimport 'package:flutter_authgear/flutter_authgear.dart';late Authgear _authgear;
Future<void> _init() async {
_authgear = Authgear(endpoint: "<AUTHGEAR_ENDPOINT>", clientID: "<ClIENT_ID>");
await _authgear.configure();
}class _MyHomePageState extends State<MyHomePage> {
late Authgear _authgear;
Future<void> _init() async {
_authgear = Authgear(endpoint: "<AUTHGEAR_ENDPOINT>", clientID: "<ClIENT_ID>");
await _authgear.configure();
}
@override
Widget build(BuildContext context) {
//other codes including wigdets for UI
...
}
}@override
void initState() {
super.initState();
_init();
}UserInfo? _userInfo;Center(
child: (_userInfo != null) ?
loggedInUserScreen(_userInfo!.sub)
:
Column(
mainAxisAlignment: MainAxisAlignment.center,
children: [
Text("My Demo App"),
TextButton(
onPressed: _onPressedAuthenticate,
child: Text("Login"),
)])
,
)Widget loggedInUserScreen(String userId) {
return Column(
mainAxisAlignment: MainAxisAlignment.center,
children: [
Text("Welcome user $userId"),
TextButton(
onPressed: _onPressedSettings,
child: Text("User Settings"),
),
TextButton(
onPressed: _onPressedLogout,
child: Text("Logout"),
)
],
);
}Future<void> _onPressedAuthenticate() async {
try {
final userInfo = await _authgear.authenticate(redirectURI: "com.example.authgeardemo.flutter://host/path");
setState(() {
_userInfo = userInfo;
});
} catch (e) {
print(e);
} finally {
}
}Future<void> _onPressedSettings() async {
}
Future<void> _onPressedLogout() async {
}import 'package:flutter/material.dart';
import 'package:flutter_authgear/flutter_authgear.dart';
void main() {
runApp(const MyApp());
}
class MyApp extends StatefulWidget {
const MyApp({Key? key}) : super(key: key);
@override
State<MyApp> createState() => _MyAppState();
}
class _MyAppState extends State<MyApp> {
late Authgear _authgear;
UserInfo? _userInfo;
@override
void initState() {
super.initState();
_init();
}
Future<void> _init() async {
_authgear = Authgear(endpoint: "<AUTHGEAR_ENDPOINT>", clientID: "<CLIENT_ID>");
await _authgear.configure();
}
@override
Widget build(BuildContext context) {
return MaterialApp(
title: "MyApp",
home: Scaffold(
appBar: AppBar(title: const Text("MyApp")),
body: Center(
child: (_userInfo != null) ?
loggedInUserScreen(_userInfo!.sub)
:
Column(
mainAxisAlignment: MainAxisAlignment.center,
children: [
Text("My Demo App"),
TextButton(
onPressed: _onPressedAuthenticate,
child: Text("Login"),
)])
,
)
),
);
}
Future<void> _onPressedAuthenticate() async {
try {
final userInfo = await _authgear.authenticate(redirectURI: "com.example.authgeardemo.flutter://host/path");
setState(() {
_userInfo = userInfo;
});
} catch (e) {
print(e);
} finally {
}
}
Future<void> _onPressedSettings() async {
}
Future<void> _onPressedLogout() async {
}
Widget loggedInUserScreen(String userId) {
return Column(
mainAxisAlignment: MainAxisAlignment.center,
children: [
Text("Welcome user $userId"),
TextButton(
onPressed: _onPressedSettings,
child: Text("User Settings"),
),
TextButton(
onPressed: _onPressedLogout,
child: Text("Logout"),
)
],
);
}
}flutter run<!-- Your application configuration. Omitted here for brevity -->
<application>
<!-- Other activities or entries -->
<!-- Add the following activity -->
<!-- android:exported="true" is required -->
<!-- See https://developer.android.com/about/versions/12/behavior-changes-12#exported -->
<activity android:name="com.authgear.flutter.OAuthRedirectActivity"
android:exported="true"
android:launchMode="singleTask">
<intent-filter>
<action android:name="android.intent.action.VIEW" />
<category android:name="android.intent.category.DEFAULT" />
<category android:name="android.intent.category.BROWSABLE" />
<!-- Configure data to be the exact redirect URI your app uses. -->
<!-- Here, we are using com.authgear.example://host/path as configured in the portal -->
<!-- NOTE: The redirectURI supplied in AuthenticateOptions *has* to match as well -->
<data android:scheme="com.example.authgeardemo.flutter"
android:host="host"
android:pathPrefix="/path"/>
</intent-filter>
</activity>
</application><?xml version="1.0" encoding="utf-8"?>
<manifest xmlns:android="http://schemas.android.com/apk/res/android">
<!-- Other elements such <application> -->
<queries>
<intent>
<action android:name="android.support.customtabs.action.CustomTabsService" />
</intent>
</queries>
</manifest>android:taskAffinity=""android {
...
defaultConfig {
applicationId = "com.example.myapp"
minSdk = 30 // specify minSdk to 30
targetSdk = flutter.targetSdkVersion
versionCode = flutter.versionCode
versionName = flutter.versionName
}
}<?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<!-- Other entries -->
<key>CFBundleURLTypes</key>
<array>
<dict>
<key>CFBundleTypeRole</key>
<string>Editor</string>
<key>CFBundleURLSchemes</key>
<array>
<string>com.example.authgeardemo.flutter://host/path</string>
<!-- Put the redirect URI your app uses here. -->
</array>
</dict>
</array>
</dict>
</plist>Future<void> _onPressedLogout() async {
await _authgear.logout();
setState(() {
_userInfo = null;
});
}Future<void> _onPressedSettings() async {
await _authgear.open(page: SettingsPage.settings);
}Future<void> _init() async {
_authgear = Authgear(endpoint: "<AUTHGEAR_ENDPOINT>", clientID: "<CLIENT_ID>");
await _authgear.configure();
if (_authgear.sessionState == SessionState.authenticated) {
final userInfo = await _authgear.getUserInfo();
setState(() {
_userInfo = userInfo;
});
}
}// After authgear.configure, it only reflect SDK local state.
// value can be SessionState.noSession or SessionState.authenticated
SessionState state = _authgear.sessionState;
UserInfo? userInfo;
try {
userInfo = await _authgear.getUserInfo();
// read the userInfo if needed
} catch (e) {
// failed to fetch user info
// the refresh token maybe expired or revoked
}
// sessionState is now up to date
// it will change to SessionState.noSession if the session is invalid
state = _authgear.sessionState;final originalClient = ...
final client = _authgear.wrapHttpClient(originalClient);You need an Authgear account and a project to use Authgear. Sign up for a free account at https://portal.authgear.com/ and create a Project.
After that, we will need to create an Application in the Project Portal.
In this step, we'll create an Authgear client application in the Authgear Portal. We'll use the configuration for this application in later steps to connect our Vue application to Authgear.
To create a client application navigate to Applications on the left menu bar in Authgear Portal.
Next, click ⊕Add Application in the top toolbar to open the New Application page.
Input the name of your application, e.g. "MyAwesomeApp" then select Single Page Application as the Application Type.
Click Save to create the application.
On the next screen, you'll see links to tutorials for different frameworks. Click Next to skip to the application configuration page
The Redirect URI is a URL in your application where the user will be redirected to after login with Authgear. In this path, make a finish authentication call to complete the login process.
Scroll to the URI section of the configuration page for the client application you created in the last step. For this tutorial, add http://localhost:4000/auth-redirect to Authorize Redirect URIs.
Click the Save button to save your changes before you proceed.
In this section, we'll add Authgear to a Vue application and use the Authgear JavaScript SDK to implement the following features:
User Login/Sign-up
Read logged-in user's info
Open User Settings page
End user session using a Logout button
Here are some recommended steps to scaffold a Vue project. You can skip this part if you are adding Authgear to an existing project. See Step 3: Install Authgear SDK to the project in the next section.
Create the project folder and install the dependencies. We will use Vite as the build tool and the vue-router package. Also, we will use TypeScript in this tutorial.
Run the following commands to create a new project:
Create project and move into the project directory:
Install dependencies:
Install Vue router:
As we are using port 4000 for this tutorial, we need to add the port information to the config. In the vite.config.ts file, modify the file with the following lines:
After doing so, when you run npm run dev , the server will be running on port 4000.
Create a new file called Home.vue in the src/components folder with simply showing Hello World on the screen. Add the follow code to Home.vue:
The App.vue file is generated by Vite already but some sections of it might not be needed for this tutorial. Edit the content of App.vue to the following:
Some of the files might not be used and thus can be deleted. You can perform the following script to delete these files:
The file structure in your project is now:
Run npm run dev now to run the project and you will see the default page with the title Vite + Vue and a "Hello World" message on http://localhost:4000.
Create a AuthRedirect.vue file in the src/components folder with the same content as src/components/Home.vue at this moment.
Create a file called router.ts in the src/ folder. We will import Home and AuthRedirect component as the route and we will implement these components later. The content of this file will look like this:
Run the following command within your Vue project directory to install the Authgear Web SDK
In src/main.ts , import authgear and call the configure function to initialize an Authgear instance on application loads. We will also import router and use it to build routes for us. Your main.ts file should look like this:
The Authgear container instance takes endpoint and clientID as parameters. They can be obtained from the application page created in Setup Application in Authgear.
Create a .env file in the root directory of your project and add your Authgear client application configuration using the following fields:
It is recommended to render the app after configure() resolves. So by the time the app is rendered, Authgear is ready to use.
Since we want to reference the logged-in state everywhere in the app, let's put the state in a context provider with UserProvider.vue in the /src/contexts folder.
In UserProvider.vue, will have a isLoggedIn boolean value. The isLoggedIn boolean state can be auto-updated using the onSessionStateChange callback. This callback can be stored in delegate which is in the local SDK container.
Next, we will add an "AuthRedirect" page for handling the authentication result after the user has been authenticated by Authgear.
Create the AuthRedirect.vue component file in the src/components/ folder.
Call the Authgear finishAuthentication() function in the Auth Redirect component to send a token back to Authgear server in exchange for access token and refresh token. Don't worry about the technical jargons, finishAuthentication() will do all the hard work for you and and save the authentication data.
When the authentication is finished, the isLoggedIn state from the UserContextProvider will automatically be set to true. Finally, navigate back to root (/) which is our Home page.
The final AuthRedirect.vue will look like this
As we have already configured the routes in the previous section, we can simply add <router-view /> tag to the App.vue. We can then Import UserProvider and wrap the router-view with it.
Your final App.vue should look like this:
The file structure should now look like
First, we will import the Authgear dependency. Then add the login button which will call startAuthentication(ConfigureOptions) through startLogin callback on click. This will redirect the user to the login page.
You can now run npm run dev and you will be redirected to the Authgear Login page when you click the Login button.
The Authgear SDK helps you get the information of the logged-in users easily.
In the last step, the user is successfully logged in so let's try to print the user ID (sub) of the user in the Home page.
In Home.vue, we will add a simple Loading splash and a greeting message printing the Sub ID. We will add two conditional elements such that they are only shown when user is logged in. We can also change the login button to show only if the user is not logged in.
Make use of isLoggedIn from the UserProvider to control the components on the page. Fetch the user info by fetchInfo() and access its sub property.
The Login button can be also rendered conditionally which only visible if the user is not logged in.
Run the app again, the User ID (sub) of the user should be printed on the Home page.
Finally, let's add a Logout button when a user is logged in.
In Home.vue, we will add the following conditional elements in the template:
And add the logout callback:
Run the app again, we can now log out by clicking the Logout button.
Authgear provides a built-in UI for the users to set their attributes and change security settings.
Use the open function to open the settings page at <your_app_endpoint>/settings
In Home.vue append a conditional link to the logout button section like this:
And add the userSetting callback:
This is the resulting Home.vue:
To access restricted resources on your backend application server, the HTTP requests should include the access token in their Authorization headers. The Web SDK provides a fetch function which automatically handles this, or you can get the token with authgear.accessToken.
Authgear SDK provides the fetch function for you to call your application server. This fetch function will include the Authorization header in your application request, and handle the refresh access token automatically. The authgear.fetch implements fetch.
You can get the access token through authgear.accessToken. Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call only if the access token has expired. Include the access token into the Authorization header of the application request.



Authenticate the incoming HTTP requests by validating JWT in your application server
In this section, we will go through how to decode the JWT token to obtain the currently logged-in user.
Before we start, make sure the option Issue JWT as access token is enabled in your Application settings in the Portal.
With the Issue JWT as access token option turned on in your application, Authgear will issue JWT as access tokens. The incoming HTTP requests should include the access token in their Authorization headers. Without setting the reverse proxy, your backend server can use your Authgear JWKS to verify the request and decode user information from the JWT access token.
See the claims in the access token in this reference: . Learn more about for adding claims into the JWT.
This Discovery endpoint serves as a JSON document containing the OpenID Connect configuration of your app. It includes the authorization endpoint, the token endpoint, and the JWKS endpoint.
https://<YOUR_AUTHGEAR_ENDPOINT>/.well-known/openid-configuration
The JSON Web Key Sets (JWKS) endpoint can be found in jwks_uri in the configuration.
OpenID Connect Configuration JSON Example
Here is .
Follow this step-by-step example to verify and decode the JWT token.
Step 1: Install packages
Step 2: Find the JSON Web Key Sets (JWKS) endpoint
Define a function to find the JWKS endpoint from the OpenID Connect configuration. Use your Authgear endpoint as the base_address
Step 3: Get the JWT token from the Authorization header
Define a function to extract the access token from the Authorization header in the incoming request. It should look like Authorization: Bearer <access_token>.
Step 4: Verify and decode the JWT token
Here we show an example of using the Flask web framework to guard a path. You may need to adjust some of the codes to suit your technologies.
The auth_time claim in an OIDC ID token represents the time when the user authentication occurred. Extract the auth_time claim from the token, which should represent the time of the original authentication in seconds. If the difference between the current time and auth_time exceeds your threshold (for example, 5 minutes), initiate the process.
See an example of how to verify the signature of the ID token, and then validate the claims auth_time inside .
Validating JWT in your application server is currently only available for Token-based authentication.
Authentication for Laravel websites with Authgear and OAuth2
In this guide, you'll learn how to add user authentication to a Laravel app using Authgear as an OIDC provider.
Authgear supports multiple ways to allow users to log in to apps such as passwordless sign-in, phone OTP, and 2FA. In this post, we'll show you how to enable all these options in your Laravel app without worrying about the underlying logic.
How to create an Authgear Application.
How to request OAuth 2.0 authorization code from Authgear.
How to get user info from Authgear using OAuth 2.0 access code.
Link user info from Authgear with Laravel's default Breeze authentication.
To follow along with the example, you should have the following in place:
A free Authgear account. if you don't have an account yet.
A Laravel project.
The example app we'll build in this post uses the default Laravel Breeze authentication kit. This kit provides the starter code for email and password user authentication systems.
We will be using Authgear to handle and process authentication data instead of the default Breeze database. By doing so, we get all the benefits of Authgear including more security and flexibility.
In this section, we'll walk through the complete steps for building the example app.
Before we can use Authgear as an OAuth identity provider, we need to set up an application on the Authgear portal.
To do that, log in to Authgear then select a project. Next, navigate to the Applications section for your project. Create a new application or configure an existing one with OIDC Client Application as Application Type as shown below:
Once you're done, click on Save to go to the application configuration page. This page reveals the application credentials and OAuth 2.0 endpoints.
Note down details like the Client ID, Client Secret, and the endpoints as you'll use them later in your Laravel project.
While you're still on the application configuration page, scroll down to the URL section then click on Add URI. Enter localhost:8000/oauth/callback in the text field if you will be running your Laravel app on your local machine. Once you're done, click Save.
The redirect URI we provided above should be a valid page on our Laravel app as Authgear will redirect users to the page after authorization.
Now create a new Laravel project on your computer by running the following command:
Once your project is created, open the project folder in your preferred code editor and replace the content of resources/views/welcome.blade.php with the following code:
Alternatively, you can create a new index.blade.php file in the resources folder and add the above code inside it. Then, update the web.php route file to render the new file instead of welcome.blade.php.
Next, run the php artisan serve command in the terminal to test your application. At this point, your application should look like the following screenshot when you access localhost:8000 on a browser:
Breeze is the official user authentication starter kit for Laravel. What that means is that Breeze helps you set up the database, routes, controller, and user interface for a user registration and user login system.
To install Breeze on your Laravel project, run the following command:
After that, run the following command to enable Breeze to set up all the resources for the user authentication system in your project:
During the setup, select blade as the stack and leave the other options as default.
Once the setup is complete, navigate around your project file structure and you should notice some new folders and files related to authentication were added. Some of these new folders/files include an Auth sub-folder in the controllers folder, another auth sub-folder inside the views folder, and some database migration files.
Before we continue, let's add an extra oauth_uid field to the users table migration file. This field will store a user's unique ID from Authgear after successful login.
Open the create_users_table... file that is inside the database/migrations/ folder (this file will have a date value at the end of its name) and add the following code to a new line inside the Schema::create() method:
Add the MySQL database DB_DATABASE, DB_USERNAME, and DB_PASSWORD for the database you wish to use with your Laravel project in your Laravel project's .env file.
Finally, create the users and other tables by running the following command:
In this step, we'll create a new route that will handle the task of redirecting users from our app to Authgear's OAuth authorization page where they can grant our app authorization to their data on Authgear. If you've used other OAuth 2.0 providers before, for example, signing in to a website using Google OAuth, you may already be familiar with an authorization page.
First, create a new controller that will handle all OAuth operations in our Laravel app by running the following command:
Before we start implementing the logic for our new controller, we need to install a PHP OAuth 2.0 client package. This package will simplify the process of interacting with Authgear's OAuth endpoints. Run the following commands to install the package:
Now, back to implementing the controller; open the new OAuthController file (from the app/Http/Controllers folder) and add the following code to it:
Next, add your Authgear Application's Client ID, Client Secret, and the redirect URI you specified earlier to your Laravel project's .env file using the following keys:
Note: Your Authgear project URL is the hostname of any of your endpoint URLs. For example, the project URL for a project with an authorization endpoint: https://laravel-app.authgear.cloud/oauth2/authorize will be https://laravel-app.authgear.cloud.
Now let's create a route in our Laravel project that will call the startAuthorization() method.
Open the routes/web.php file and add new routes using the following code:
We've included a second route for the redirect URI (callback), we'll implement this route in the next step.
Before we continue, let's clean up some of the additional routes added by the Breeze package that we won't be needing for this example. Open the routes/auth.php file and delete the following lines:
At this point accessing the /login route should redirect to the Authgear authorization page.
Update the empty handleRedirect() method in OAuthController to the following:
The above code gets the authorization code sent in the redirect URL from Authgear after user authorization and exchanges it for an access token. With this access token, our application can access protected resources like the user info endpoint.
In this step, we'll use the access token we got from the last step to get the current user's info from Authgear.
First, add the following code at the end of the handleRedirect() method:
The getResourceOwner() method will call Authgear's UserInfo endpoint.
If you dump the userInfo variable (dd($userInfo)), you should get an output similar to this:
The above array contains the user's info from Authgear. We'll proceed to use this information to link the Authgear user to a default (Breeze) Laravel authentication account. As a result, our app can start a regular Laravel authenticated user session and allow access to protected routes.
To implement the above feature, find the following line in OAuthController.php:
Add the following code after the above line:
Find the complete code for the OAuthController .
OAuth 2.0 access tokens expire after some time. The refresh token on the other hand live longer. As a result, you can use the refresh token to request a new access token. In this step, we'll do exactly that in our Laravel application.
First, app/Http/Controllers/ProfileController.php and update the content of the edit() method to the following:
The above code checks if the current access token is expired using the hasExpired() method. If the condition is true, we call the getAccessToken() method with the refresh token to get a new access token.
The value of the current access token is updated to the new access token.
Next, this edit() method also displays the current user's profile details from your Authgear project on the UI. To implement this, add the following code to resources/views/profile/edit.blade.php, just below the line with "<div class="max-w-7xl mx-auto sm:px-6 lg:px-8 space-y-6">":
At this point, if we run our app and click on the login link on the landing page, we should be redirected to the Authgear authorization page. After granting authorization, we are directed to the callback route of our Laravel app. If authentication is successful we should be redirected to the default Breeze-protected dashboard page that looks like this:
To log a user out, we'll delete all existing PHP session data and then call the Authgear token revoke endpoint.
First, add a new logout function to the OAuthController.php file using the following code:
Then, open routes/web.php and update the logout route to the following:
You should try enabling the different login methods on Authgear from the Portal to enjoy features like 2FA, passwordless login, and more without updating anything on the code for your app.
Find the complete code for the example app in our .
Guide on using Authgear together with Supabase database to deliver a secure and scalable application
User authentication is a foundational part of any modern web application but getting it right is notoriously difficult. That’s where Authgear comes in. Authgear handles user registration, login flows, session management, and advanced security features like biometric login, 2FA, and social sign-ins out of the box.
Pairing Authgear with Supabase's Postgres database and powerful Row-Level Security (RLS) gives you a secure, scalable foundation for building user-specific applications.
In this guide, you’ll learn how to integrate Authgear and Supabase using React.js to build a basic CRUD application.
We will walkthrough how to authenticate users with Authgear, exchange tokens via a Supabase Edge Function, apply RLS policies based on Authgear-issued JWTs, and connect it all in a modern React frontend using Vite.
npm create vite@latest my-app -- --template vue-ts
cd my-appnpm installnpm install --save-exact vue-router// vite.config.ts
import { defineConfig } from "vite";
import vue from "@vitejs/plugin-vue";
// https://vitejs.dev/config/
export default defineConfig({
plugins: [vue()],
server: {
port: 4000,
},
});// src/components/Home.vue
<script setup lang="ts"></script>
<template><div>Hello World</div></template>// src/components/App.vue
<script setup lang="ts">
import Home from "./components/Home.vue";
</script>
<template>
<Home />
</template>rm -rf src/assets src/components/HelloWorld.vuemy-app
├── node_modules
│ └── (...)
├── package-lock.json
├── package.json
├── vite.config.ts
├── (...)
└── src
├── components
│ └── Home.vue
├── App.vue
├── main.ts
└── (...)// src/router.ts
import { createRouter, createWebHistory } from "vue-router";
export const history = createWebHistory();
export const router = createRouter({
history,
routes: [
{
path: "/",
// We will implement this component later
component: () => import("./components/Home.vue"),
},
{
path: "/auth-redirect",
// We will implement this component later
component: () => import("./components/AuthRedirect.vue"),
},
],
});npm install --save-exact @authgear/web// src/main.ts
import { createApp } from "vue";
import './style.css'
import App from "./App.vue";
import { router } from "./router";
import authgear from "@authgear/web";
const app = createApp(App);
async function init() {
try {
// configure Authgear container instance
await authgear.configure({
endpoint: import.meta.env.VITE_AUTHGEAR_ENDPOINT,
clientID: import.meta.env.VITE_AUTHGEAR_CLIENT_ID,
sessionType: "refresh_token",
});
} finally {
app.use(router);
app.mount("#app");
}
}
init().catch((e) => {
// Error handling
console.error(e)
});VITE_AUTHGEAR_CLIENT_ID=<CLIENT_ID>
VITE_AUTHGEAR_ENDPOINT=<AUTHGEAR_ENDPOINT>
VITE_AUTHGEAR_REDIRECT_URL=http://localhost:4000/auth-redirect// src/contexts/UserProvider.vue
<script lang="ts">
import {
defineComponent,
InjectionKey,
provide,
readonly,
ref,
Ref,
toRefs,
} from "vue";
import authgear from "@authgear/web";
export interface UserContextValue {
isLoggedIn: Ref<boolean>;
}
export const UserStateSymbol: InjectionKey<UserContextValue> =
Symbol("UserState");
export default defineComponent({
setup() {
const isLoggedIn = ref(false);
const state: UserContextValue = {
isLoggedIn,
};
authgear.delegate = {
onSessionStateChange: (container) => {
const sessionState = container.sessionState;
if (sessionState === "AUTHENTICATED") {
isLoggedIn.value = true;
} else {
isLoggedIn.value = false;
}
},
};
provide<UserContextValue>(UserStateSymbol, toRefs(readonly(state)));
return { state };
},
});
</script>
<template>
<slot />
</template>
// src/components/AuthRedirect.vue
<script setup lang="ts">
import { onMounted } from "vue";
import authgear from "@authgear/web";
import { router } from "../router";
onMounted(() => {
async function updateToken() {
try {
await authgear.finishAuthentication();
} finally {
router.replace({ path: "/" });
}
}
updateToken().catch((e) => console.error(e));
});
</script>
<template></template>
// src/App.vue
<script setup lang="ts">
import UserProvider from "./contexts/UserProvider.vue";
</script>
<template>
<UserProvider>
<router-view />
</UserProvider>
</template>src
├── App.vue
├── main.ts
├── router.ts
├── vite-env.d.ts
├── contexts
│ └── UserProvider.vue
└── components
├── AuthRedirect.vue
└── Home.vue// src/components/Home.vue
<script setup lang="ts">
import authgear, { PromptOption } from "@authgear/web";
const startLogin = () => {
authgear
.startAuthentication({
redirectURI: import.meta.env.VITE_AUTHGEAR_REDIRECT_URL,
prompt: PromptOption.Login,
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
};
</script>
<template>
<h1>Home Page</h1>
<button @click="startLogin">Login</button>
</template>// src/components/Home.vue
<script setup lang="ts">
import authgear, { PromptOption } from "@authgear/web";
import { inject, onMounted, ref } from "vue";
import { UserStateSymbol } from "../contexts/UserProvider.vue";
const { isLoggedIn } = inject(UserStateSymbol)!;
const isLoading = ref(false);
const greetingMessage = ref("");
onMounted(() => {
async function updateGreetingMessage() {
isLoading.value = true;
try {
if (isLoggedIn.value) {
const userInfo = await authgear.fetchUserInfo();
greetingMessage.value = "The current User sub: " + userInfo.sub;
}
} finally {
isLoading.value = false;
}
}
updateGreetingMessage().catch((e) => {
console.error(e);
});
});
const startLogin = () => {
authgear
.startAuthentication({
redirectURI: import.meta.env.VITE_AUTHGEAR_REDIRECT_URL,
prompt: PromptOption.Login,
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
};
</script>
<template>
<h1>Home Page</h1>
<span v-if="isLoading">Loading...</span>
<span v-if="greetingMessage">{{ greetingMessage }}</span>
<div v-if="!isLoggedIn">
<button @click="startLogin">Login</button>
</div>
</template>
<div v-if="isLoggedIn">
<button @click="logout">Logout</button>
</div>const logout = () => {
authgear
.logout({
redirectURI: "http://localhost:4000/",
})
.then(
() => {
greetingMessage.value = "";
},
(err) => {
console.error(err);
}
);
};<div v-if="isLoggedIn">
<button @click="logout()">Logout</button>
<br />
<a
target="_blank"
rel="noreferrer"
@click.stop.prevent="userSetting"
href="#"
>
User Setting
</a>
</div>import authgear, { PromptOption, Page } from "@authgear/web";
const userSetting = async () => {
await authgear.open(Page.Settings);
};// src/components/Home.vue
<script setup lang="ts">
import authgear, { PromptOption, Page } from "@authgear/web";
import { inject, onMounted, ref } from "vue";
import { UserStateSymbol } from "../contexts/UserProvider.vue";
const { isLoggedIn } = inject(UserStateSymbol)!;
const isLoading = ref(false);
const greetingMessage = ref("");
onMounted(() => {
async function updateGreetingMessage() {
isLoading.value = true;
try {
if (isLoggedIn.value) {
const userInfo = await authgear.fetchUserInfo();
greetingMessage.value = "The current User sub: " + userInfo.sub;
}
} finally {
isLoading.value = false;
}
}
updateGreetingMessage().catch((e) => {
console.error(e);
});
});
const startLogin = () => {
authgear
.startAuthentication({
redirectURI: import.meta.env.VITE_AUTHGEAR_REDIRECT_URL,
prompt: PromptOption.Login,
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
};
const logout = () => {
authgear
.logout({
redirectURI: "http://localhost:4000/",
})
.then(
() => {
greetingMessage.value = "";
},
(err) => {
console.error(err);
}
);
};
const userSetting = async () => {
await authgear.open(Page.Settings);
};
</script>
<template>
<h1>Home Page</h1>
<span v-if="isLoading">Loading...</span>
<span v-if="greetingMessage">{{ greetingMessage }}</span>
<div v-if="!isLoggedIn">
<button @click="startLogin">Login</button>
</div>
<div v-if="isLoggedIn">
<button @click="logout">Logout</button>
<br />
<a
target="_blank"
rel="noreferrer"
@click.stop.prevent="userSetting"
href="#"
>
User Setting
</a>
</div>
</template>
authgear
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgear
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgear.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});com.authgear.example.rn://host/pathnpx @react-native-community/cli init myapp
cd myappnpm install --exact @authgear/react-native
(cd ios && pod install)import React, { useCallback, useEffect, useMemo, useState } from 'react';
import authgear, { Page, ReactNativeContainer, SessionState, SessionStateChangeReason } from "@authgear/react-native";const [sessionState, setSessionState] = useState<SessionState | null>(() => {
return authgear.sessionState;
});
const loggedIn = sessionState === "AUTHENTICATED";
const delegate = useMemo(() => {
const d = {
onSessionStateChange: (
container: ReactNativeContainer,
_reason: SessionStateChangeReason
) => {
setSessionState(container.sessionState);
},
sendWechatAuthRequest: () => {},
};
return d;
}, [setSessionState]);
useEffect(() => {
authgear.delegate = delegate;
return () => {
authgear.delegate = undefined;
};
}, [delegate]);
const postConfigure = useCallback(async () => {
const sessionState = authgear.sessionState;
// if user has an existing session, call SDK fetchUserInfo method to get the user's info and refresh access token when necessary
if (sessionState === "AUTHENTICATED") {
await authgear.fetchUserInfo();
}
}, []);
useEffect(() => {
const configure = async () => {
try {
await authgear
.configure({
clientID: "<CLIENT_ID>",
endpoint: "<AUTHGEAR_ENDPOINT>",
});
await postConfigure();
} catch (error) {
console.log("Error:" + error);
}
};
configure();
}, [postConfigure]);return (
<SafeAreaView>
<StatusBar />
<View style={{justifyContent: 'center', alignItems: 'center'}}>
{!loggedIn ?
<View>
<Text style={{paddingTop: 50, paddingBottom: 16, fontSize: 40}}>Welcome</Text>
<Button onPress={authenticate} title="Login" />
</View> :
<View>
<Text style={{paddingTop: 50, paddingBottom: 16}}>Welcome User</Text>
</View>
}
</View>
</SafeAreaView>
);import {
Alert,
Button,
SafeAreaView,
StatusBar,
Text,
View,
} from 'react-native';const authenticate = useCallback(async () => {
try {
authgear
.authenticate({
redirectURI: "com.authgear.example.rn://host/path",
});
} catch (error) {
console.log("Authentication Error:" + error);
}
}, []);import React, {useCallback, useEffect, useMemo, useState} from 'react';
import authgear, {
Page,
ReactNativeContainer,
SessionState,
SessionStateChangeReason,
} from '@authgear/react-native';
import {Alert, Button, SafeAreaView, StatusBar, Text, View} from 'react-native';
function App(): React.JSX.Element {
const [sessionState, setSessionState] = useState<SessionState | null>(() => {
return authgear.sessionState;
});
const loggedIn = sessionState === 'AUTHENTICATED';
const delegate = useMemo(() => {
const d = {
onSessionStateChange: (
container: ReactNativeContainer,
_reason: SessionStateChangeReason,
) => {
setSessionState(container.sessionState);
},
sendWechatAuthRequest: () => {},
};
return d;
}, [setSessionState]);
useEffect(() => {
authgear.delegate = delegate;
return () => {
authgear.delegate = undefined;
};
}, [delegate]);
const postConfigure = useCallback(async () => {
const sessionState = authgear.sessionState;
// if user has an existing session, call SDK fetchUserInfo method to get the user's info and refresh access token when necessary
if (sessionState === 'AUTHENTICATED') {
await authgear.fetchUserInfo();
}
}, []);
useEffect(() => {
const configure = async () => {
try {
await authgear.configure({
clientID: '<CLIENT_ID>',
endpoint: '<AUTHGEAR_ENDPOINT>',
});
await postConfigure();
} catch (error) {
console.log('Error:' + error);
}
};
configure();
}, [postConfigure]);
const authenticate = useCallback(async () => {
try {
authgear.authenticate({
redirectURI: 'com.authgear.example.rn://host/path',
});
} catch (error) {
console.log('Authentication Error:' + error);
}
}, []);
return (
<SafeAreaView>
<StatusBar />
<View style={{justifyContent: 'center', alignItems: 'center'}}>
{!loggedIn ? (
<View>
<Text style={{paddingTop: 50, paddingBottom: 16, fontSize: 40}}>
Welcome
</Text>
<Button onPress={authenticate} title="Login" />
</View>
) : (
<View>
<Text style={{paddingTop: 50, paddingBottom: 16}}>
Welcome User
</Text>
</View>
)}
</View>
</SafeAreaView>
);
}
export default App;npm run androidnpm run ios<!-- Your application configuration. Omitted here for brevity -->
<application>
<!-- Other activities or entries -->
<!-- Add the following activity -->
<!-- android:exported="true" is required -->
<!-- See https://developer.android.com/about/versions/12/behavior-changes-12#exported -->
<activity android:name="com.authgear.reactnative.OAuthRedirectActivity"
android:exported="true"
android:launchMode="singleTask">
<intent-filter>
<action android:name="android.intent.action.VIEW" />
<category android:name="android.intent.category.DEFAULT" />
<category android:name="android.intent.category.BROWSABLE" />
<!-- Configure data to be the exact redirect URI your app uses. -->
<!-- Here, we are using com.authgear.example://host/path as configured in the portal -->
<!-- NOTE: The redirectURI supplied in AuthenticateOptions *has* to match as well -->
<data android:scheme="com.authgear.example.rn"
android:host="host"
android:pathPrefix="/path"/>
</intent-filter>
</activity>
</application><?xml version="1.0" encoding="utf-8"?>
<manifest xmlns:android="http://schemas.android.com/apk/res/android">
<!-- Other elements such <application> -->
<queries>
<intent>
<action android:name="android.support.customtabs.action.CustomTabsService" />
</intent>
</queries>
</manifest><?xml version="1.0" encoding="UTF-8"?>
<!DOCTYPE plist PUBLIC "-//Apple//DTD PLIST 1.0//EN" "http://www.apple.com/DTDs/PropertyList-1.0.dtd">
<plist version="1.0">
<dict>
<!-- Other entries -->
<key>CFBundleURLTypes</key>
<array>
<dict>
<key>CFBundleTypeRole</key>
<string>Editor</string>
<key>CFBundleURLSchemes</key>
<array>
<string>com.authgear.example.rn</string>
</array>
</dict>
</array>
</dict>
</plist>// Other imports...
#import <authgear-react-native/AGAuthgearReactNative.h>
// Other methods...
// For handling deeplink
- (BOOL)application:(UIApplication *)app
openURL:(NSURL *)url
options:
(NSDictionary<UIApplicationOpenURLOptionsKey, id> *)options {
return [AGAuthgearReactNative application:app openURL:url options:options];
}
// For handling deeplink
// deprecated, for supporting older devices (iOS < 9.0)
- (BOOL)application:(UIApplication *)application
openURL:(NSURL *)url
sourceApplication:(NSString *)sourceApplication
annotation:(id)annotation {
return [AGAuthgearReactNative application:application
openURL:url
sourceApplication:sourceApplication
annotation:annotation];
}
// for handling universal link
- (BOOL)application:(UIApplication *)application
continueUserActivity:(NSUserActivity *)userActivity
restorationHandler:
(void (^)(NSArray<id<UIUserActivityRestoring>> *_Nullable))
restorationHandler {
return [AGAuthgearReactNative application:application
continueUserActivity:userActivity
restorationHandler:restorationHandler];
}const logout = useCallback( () => {
try {
authgear
.logout();
} catch (error) {
console.log("Error:" + error);
}
}, []);<Button onPress={logout} title="Logout" />const showUserInfo = useCallback(async () => {
try {
const userInfo = await authgear.fetchUserInfo();
Alert.alert('User Info', JSON.stringify(userInfo, null, 2));
} catch (error) {
console.log('Error:' + error);
}
}, []);<View style={{height: 8}} />
<Button onPress={showUserInfo} title="Show User Info" />const openSettings = useCallback(() => {
try {
authgear.open(Page.Settings);
} catch (error) {
console.log('Error:' + error);
}
}, []);<View style={{height: 8}} />
<Button onPress={openSettings} title="User Settings" />// After authgear.configure, it only reflect SDK local state.
// value can be NO_SESSION or AUTHENTICATED
let sessionState = authgear.sessionState;
if (sessionState === "AUTHENTICATED") {
authgear
.fetchUserInfo()
.then((userInfo) => {
// sessionState is now up to date
})
.catch((e) => {
// sessionState is now up to date
// it will change to NO_SESSION if the session is invalid
});
}authgear
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgear
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgear.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});




Step 2: Find the JWKS Endpoint
Use the following method to get the JWKS URI (you'll need to URI to extract the public signing key from a JWT).
Step 3: Extract JWT from Request Header
Use the following code to extract only the token part from a Bearer [token] authorization header in your Express app:
Step 4: Decode Access Token
Next, decode the access token so that you can extract the JWT kid from the result. You'll need this `kid to get the public signing key. Use the following code to decode the JWT:
Step 5: Get JWT Signing Keys and Verify the JWT
Use the following code to extract the JWT public keys then verify the JWT using the keys:
Here's what your Express app should look like after putting the code in all the steps together:
Use your Authgear endpoint as base_address
The following example uses Spring Boot.
Step 1: Install dependencies
Add the following dependencies to your build.gradle file:
Then add the following imports to the top of your controller file:
Step 2: Get JWKS Endpoint
Implement the following method to fetch the JWKS URI:
Step 3: Get Signing Key
Get the signing key from the JWK using the following method:
Step 4: Validate JWT
To demonstrate how to validate a JWT, we'll implement a validateJWT endpoint in a Spring Boot application. The endpoint will read access tokens from the bearer authorization header.
It will call the fetchJwksUri() and getSigningKeyFromJwks() from steps 1 and 2 to get the JWK URI and signing key required to parse the JWT.
Step 1: Install Packages
First, install the dependencies required by running these com
Step 2: Find the JWKS Endpoint
Create a function that finds the JWKS endpoint from your Authgear application endpoint using the following code:
Step 3: Get Signing Key
Add the following code to your application to get the JWT signing key:
Step 4: Extract the JWT From the Request Header
To extract the access token from the HTTP request use the following code:
Step 5: Validate and Decode JWT
Finally, decode the JWT signing key.
Step 1: Install NuGet packages
then add these imports to the top of your program.cs file:
Step 2: Configure JWT Authentication
This tells ASP.NET Core to use JWT Bearer tokens for authentication
Step 3: Add authorization
Step 4: Configure middleware pipeline
Order is important! Authentication must come before Authorization
Step 5: Create a protected endpoint
The following example uses the Minimal API model
For Controller-based APIs, simply add [Authorize] to your controller class or individual action methods to protect them

The full example app source code is available on GitHub and can be used as a starting point for your own project: https://github.com/authgear/authgear-example-supabase
Authgear account & project – Sign up for Authgear.
Supabase account & project – Sign up on supabase.com
First, configure Authgear to handle authentication for your app.
Create an Authgear Application: Log in to the Authgear Portal and create a new application. Choose Single Page Application as the application type.
Configure OAuth Redirects: In your Authgear app settings, set the redirect URIs:
Redirect URI: http://localhost:5173/auth-redirect – this is where Authgear will redirect the browser after a successful login (our React app will handle this route).
Post-Logout Redirect URI: http://localhost:5173/ – where to navigate after users log out.
Note Your Authgear Credentials: After creation, note down:
The Authgear Endpoint for your app (it will look like https://<your-project>.authgear.cloud).
The Client ID of your Authgear application.
We will need these values when initializing Authgear in our React app and in the Supabase function.
Next, prepare your Supabase backend.
Create a Supabase Project: Log in to Supabase Dashboard, create a new project (choose an organization, project name, database password, and region).
Retrieve Project Keys: In your Supabase project, go to Project Settings → API → API keys. Copy the Publishable Key and the URL of your project (e.g., https://xyzcompany.supabase.co).
Get the JWT Secret: Still in Project settings, navigate to JWT Keys and find the Legacy JWT Secret for your project. This is a secret key that Supabase uses to sign and verify JWTs for RLS. Copy the JWT secret value – we will use it in our Edge Function config.\
(Optional) Install Supabase CLI: If you plan to use the CLI to deploy the Edge Function, install it by following . Alternatively, you can deploy the function via the Dashboard UI.
Now we set up the critical piece: a Supabase Edge Function that will accept Authgear’s JWT and return a new JWT signed with Supabase’s secret.
Navigate to "Edge Functions" -> "Secrets" and add the two secrets:
AUTHGEAR_ENDPOINT = your Authgear app endpoint (e.g. https://myapp.authgear.cloud).
SB_JWT_SECRET = your Supabase JWT secret (from Step 2 above).
Deploy the Function
Navigate to "Edge Functions" -> "Functions" in Supabase web UI. Copy-paste the following code and deploy it there. Name the function exchange-jwt.
Alternatively, you can use Supabase CLI to build and deploy the Edge Function from your local machine to your Supabase project.
Once deployed, your function is accessible at:
Now let’s set up the database table and RLS rules in Supabase. We’ll create a table (instruments) to store items owned by users, and use RLS to ensure each user can only manipulate their own rows.
Open the SQL editor in your Supabase project and run the following SQL commands:
We created a SQL function current_user_id() that returns the JWT’s sub claim (subject) from the current request’s JWT. Supabase’s Postgres has an auth.jwt() function that exposes the JWT claims of the requester; auth.jwt() ->> 'sub' extracts the sub field as text.
The instruments table has a user_id column which will store the Authgear user’s ID for each instrument.
We enabled RLS on the table, which means by default no rows can be accessed unless allowed by a policy.
We then defined four policies, one for each CRUD operation (SELECT, INSERT, UPDATE, DELETE). Each policy is limited to the authenticated role and uses a condition requiring that the row’s user_id matches the user’s id from the JWT.
Now for the frontend. We will create a React app using Vite, integrate Authgear’s SDK for authentication, and configure the Supabase client to use our token exchange flow automatically.
Dependencies
Scaffold a React App by npm create vite@latest my-app -- --template react
Follow the guide for build SPA in here: React to setup a basic react app with Authgear authentication
Install the Supabase library by
Configure the Environment Variables in .env and make the Supabase URL and Publishable key available. You .env.local should look like:
Configure the Supabase Client
Now we can set up the Supabase JS client to use our Authgear token. Create a new file my-app/src/lib/supabase.js and add the following:
In this configuration:
We disable autoRefreshToken and persistSession in Supabase’s client so that Authgear is the source of truth for the session.
We provide an accessToken async function. The Supabase Client will call this function every time it needs a JWT for an authenticated request. In our case, that is every query to our instruments table.
In accessToken(), we first ensure Authgear’s token is fresh by calling authgear.refreshAccessTokenIfNeeded().
We then get authgear.accessToken – this is the current JWT from Authgear’s SDK.
If the token exists, we call our exchangeToken() helper, which calls the Edge Function’s endpoint with the Authgear token and receives a Supabase JWT in response.
Build the CRUD functions
After login, use the Supabase client to fetch and manipulate data. For example, to load the current user’s instruments, you can call:
To add a new instrument, call
Similarly, to update or delete, similarly call .update(...) or .delete(...) in the Supabase Client with appropriate filters
We’re ready to test the whole system. Start the development server:
Open http://localhost:5173 in your browser and test the integration.
You’ve successfully integrated Authgear for authentication with Supabase for secure, per-user data access using Row-Level Security.
With this setup, you can take full advantage of Authgear’s powerful authentication features like social logins, 2FA, and secure session management, while leveraging Supabase’s scalable database and built-in RLS to keep user data isolated and protected. This token exchange approach makes it easy to use Authgear (or any other JWT-based provider) with Supabase.







import (
"context"
"encoding/json"
"fmt"
"net/http"
"regexp"
"time"
"github.com/lestrrat-go/jwx/jwk"
"github.com/lestrrat-go/jwx/jwt"
)
var (
authzHeaderRegexp = regexp.MustCompile("(?i)^Bearer (.*)$")
baseAddress = "https://<your_app_endpoint>"
)
type OIDCDiscoveryDocument struct {
JWKSURI string `json:"jwks_uri"`
}
func FetchOIDCDiscoveryDocument(endpoint string) (*OIDCDiscoveryDocument, error) {
resp, err := http.DefaultClient.Get(endpoint)
if err != nil {
return nil, err
}
defer resp.Body.Close()
if resp.StatusCode != http.StatusOK {
return nil, fmt.Errorf(
"failed to fetch discovery document: unexpected status code: %d",
resp.StatusCode,
)
}
var document OIDCDiscoveryDocument
err = json.NewDecoder(resp.Body).Decode(&document)
if err != nil {
return nil, err
}
return &document, nil
}
func FetchJWK(baseAddress string) (jwk.Set, error) {
doc, err := FetchOIDCDiscoveryDocument(
baseAddress + "/.well-known/openid-configuration",
)
if err != nil {
return nil, err
}
set, err := jwk.Fetch(context.Background(), doc.JWKSURI)
return set, err
}
// DecodeUser parse request Authorization header and obtain user id and claims
func DecodeUser(r *http.Request) (string, map[string]interface{}, error) {
// fetch jwks_uri from Authgear
// you can cache the value of jwks to have better performance
set, err := FetchJWK(baseAddress)
if err != nil {
return "", nil, fmt.Errorf("failed to fetch JWK: %s", err)
}
// get jwt token from Authorization header
authzHeader := r.Header.Get("Authorization")
match := authzHeaderRegexp.FindStringSubmatch(authzHeader)
if len(match) != 2 {
return "", nil, fmt.Errorf("no token")
}
// parse jwt token
token, err := jwt.ParseString(match[1], jwt.WithKeySet(set))
if err != nil {
return "", nil, fmt.Errorf("invalid token: %s", err)
}
// validate jwt token
err = jwt.Validate(token,
jwt.WithClock(jwt.ClockFunc(
func() time.Time { return time.Now().UTC() },
)),
jwt.WithAudience(baseAddress),
)
if err != nil {
return "", nil, fmt.Errorf("invalid token: %s", err)
}
return token.Subject(), token.PrivateClaims(), nil
}
func handler(w http.ResponseWriter, r *http.Request) {
// decode user example
userid, claims, err := DecodeUser(r)
isUserVerified, _ :=
claims["https://authgear.com/claims/user/is_verified"].(bool)
isAnonymousUser, _ :=
claims["https://authgear.com/claims/user/is_anonymous"].(bool)
// ... your handler logic
}dependencies {
implementation("com.nimbusds:nimbus-jose-jwt:10.2")
implementation("org.json:json:20250107")
}import com.nimbusds.jose.jwk.JWKSet;
import com.nimbusds.jose.jwk.RSAKey;
import com.nimbusds.jwt.JWTClaimsSet;
import com.nimbusds.jwt.SignedJWT;
import java.io.BufferedReader;
import java.io.InputStreamReader;
import java.net.HttpURLConnection;
import java.net.URL;
import java.util.List;
private static String fetchJwksUri(String baseAddress) throws Exception {
String docUrl = baseAddress + "/.well-known/openid-configuration";
HttpURLConnection conn = (HttpURLConnection) new URL(docUrl).openConnection();
conn.setRequestMethod("GET");
try (BufferedReader reader = new BufferedReader(new InputStreamReader(conn.getInputStream()))) {
StringBuilder response = new StringBuilder();
String line;
while ((line = reader.readLine()) != null) {
response.append(line);
}
String jwksUri = new org.json.JSONObject(response.toString()).getString("jwks_uri");
if (jwksUri == null || jwksUri.isEmpty()) {
throw new Exception("Failed to fetch JWKS URI.");
}
return jwksUri;
}
}private static RSAKey getSigningKeyFromJwks(String jwksUri, String token) throws Exception {
JWKSet jwkSet = JWKSet.load(new URL(jwksUri));
List<com.nimbusds.jose.jwk.JWK> keys = jwkSet.getKeys();
SignedJWT signedJWT = SignedJWT.parse(token);
String keyId = signedJWT.getHeader().getKeyID();
return keys.stream()
.filter(jwk -> jwk.getKeyID().equals(keyId))
.findFirst()
.map(jwk -> (RSAKey) jwk)
.orElse(null);
}composer require firebase/php-jwtcomposer require guzzlehttp/guzzle<?php
require 'vendor/autoload.php';
use Firebase\JWT\JWT;
use Firebase\JWT\JWK;
use Firebase\JWT\Key;
use GuzzleHttp\Client;
$appUrl = ""; //place your authgear app endpoint here
function getJwksUri($appUrl) {
$configEndpoint = $appUrl . "/.well-known/openid-configuration";
$httpClient = new Client();
$response = $httpClient->request('GET', $configEndpoint);
$responseObject = json_decode($response->getBody());
return $responseObject->jwks_uri;
}$jwksUri = getJwksUri($appUrl);
$httpClient = new Client();
$jwksUriResponse = $httpClient->request('GET', $jwksUri);
$keysObject = json_decode($jwksUriResponse->getBody());
$jwks = (array) ($keysObject->keys)[0];
$parsedKey = JWK::parseKey($jwks, "RS256");
$signingKey = $parsedKey->getKeyMaterial();if (!isset($_SERVER['HTTP_AUTHORIZATION']))
throw new Exception("Invalid authorization header");
$authorizationHeader = $_SERVER['HTTP_AUTHORIZATION'];
$jwt = (explode(" ", $authorizationHeader))[1];$decoded = JWT::decode($jwt, new Key($signingKey, 'RS256'));
echo json_encode($decoded);dotnet add package NSwag.AspNetCoreusing Microsoft.AspNetCore.Authentication.JwtBearer;
using Microsoft.IdentityModel.Tokens;var builder = WebApplication.CreateBuilder(args);
var config = builder.Configuration;
builder.Services.AddAuthentication(x =>
{
x.DefaultAuthenticateScheme = JwtBearerDefaults.AuthenticationScheme;
x.DefaultChallengeScheme = JwtBearerDefaults.AuthenticationScheme;
x.DefaultScheme = JwtBearerDefaults.AuthenticationScheme;
}).AddJwtBearer(x => // here we configure what to validate in JWT tokens
{
// .NET will automatically fetch JWKS keys from {authority}/.well-known/openid-configuration
x.Authority = ""; // place your authgear app endpoint here,
x.RequireHttpsMetadata = false; // Allow HTTP for development
x.TokenValidationParameters = new TokenValidationParameters
{
ValidIssuer = x.Authority,
ValidateAudience = false, // set to true if you validate audience
ValidateLifetime = true,
ValidateIssuerSigningKey = true,
};
});builder.Services.AddAuthorization();app.UseAuthentication();
app.UseAuthorization();app.MapGet("/", (HttpContext context) =>
{
var user = context.User;
Console.WriteLine($"Authorization header: {context.Request.Headers.Authorization}");
Console.WriteLine($"User authenticated: {user.Identity?.IsAuthenticated}");
if (user.Identity?.IsAuthenticated == true)
{
var claims = user.Claims.ToDictionary(c => c.Type, c => c.Value);
return Results.Ok(claims);
}
return Results.Json(new { error = "Unauthorized" }, statusCode: 401);
}).RequireAuthorization(); // require auth from this endpoint{
"issuer": "https://project-id.authgear.cloud",
"authorization_endpoint": "https://project-id.authgear.cloud/oauth2/authorize",
"jwks_uri": "https://project-id.authgear.cloud/oauth2/jwks", // the JWKS endpoint
...
}pip install cryptography
pip install PyJWTimport json
from contextlib import closing
from urllib.request import urlopen
base_address = "https://<your_app_endpoint>"
def fetch_jwks_uri(base_address):
doc_url = base_address + "/.well-known/openid-configuration"
with closing(urlopen(doc_url)) as f:
doc = json.load(f)
jwks_uri = doc["jwks_uri"]
if not jwks_uri:
raise Exception('Failed to fetch jwks uri.')
return jwks_uridef parse_header(authz_header):
parts = authz_header.split(" ")
if len(parts) != 2:
return
scheme = parts[0]
if scheme.lower() != "bearer":
return
return parts[1]from flask import request
import jwt
from jwt import PyJWKClient
@app.route("/hello")
def hello():
authz_header = request.headers.get("Authorization")
if not authz_header:
return {
"message": "authz header not found"
}
# get jwt token from Authorization header
token = parse_header(authz_header)
if token:
try:
# fetch jwks_uri from the Authgear Discovery Endpoint
jwks_uri = fetch_jwks_uri(base_address)
# Reuse PyJWKClient for better performance
jwks_client = PyJWKClient(jwks_uri)
signing_key = jwks_client.get_signing_key_from_jwt(token)
user_data = jwt.decode(
token,
signing_key.key,
algorithms=["RS256"],
audience=base_address,
options={"verify_exp": True},
)
return {
"message": "Hello!",
"user_data": user_data
}
except:
return {
"message": "JWT decode failed"
}
else:
return {
"message": "no token"
}npm install --save axios jwks-rsa jsonwebtokenconst appUrl = ""; //place your authgear app endpoint here
const getJwksUri = async (appUrl) => {
const config_endpoint = appUrl + "/.well-known/openid-configuration";
const data = await axios.get(config_endpoint);
return data.data.jwks_uri;
}const express = require("express");
const axios = require("axios");
const node_jwt = require('jsonwebtoken');
const jwksClient = require('jwks-rsa');
const app = express();
const port = 3002;
app.get('/', async (req, res) => {
const requestHeader = req.headers;
if (requestHeader.authorization == undefined) {
res.send("Invalid header");
return;
}
const authorizationHeader = requestHeader.authorization.split(" ");
const access_token = authorizationHeader[1];
}const decoded_access_token = node_jwt.decode(access_token, {complete: true});const jwks_uri = await getJwksUri(appUrl);
const client = jwksClient({
strictSsl: true,
jwksUri: jwks_uri
});
const signing_key = await client.getSigningKey(decoded_access_token.header.kid);
try {
const verify = node_jwt.verify(access_token, signing_key.publicKey, { algorithms: ['RS256'] });
res.send(JSON.stringify(verify))
}
catch(error) {
res.send(error);
}
const express = require("express");
const axios = require("axios");
const node_jwt = require('jsonwebtoken');
const jwksClient = require('jwks-rsa');
const app = express();
const port = 3002;
const appUrl = "https://demo-1-ea.authgear.cloud";
const getJwksUri = async (appUrl) => {
const config_endpoint = appUrl + "/.well-known/openid-configuration";
const data = await axios.get(config_endpoint);
return data.data.jwks_uri;
}
app.get('/', async (req, res) => {
const requestHeader = req.headers;
if (requestHeader.authorization == undefined) {
res.send("Invalid header");
return;
}
const authorizationHeader = requestHeader.authorization.split(" ");
const access_token = authorizationHeader[1];
const decoded_access_token = node_jwt.decode(access_token, {complete: true});
const jwks_uri = await getJwksUri(appUrl);
const client = jwksClient({
strictSsl: true,
jwksUri: jwks_uri
});
const signing_key = await client.getSigningKey(decoded_access_token.header.kid);
try {
const verify = node_jwt.verify(access_token, signing_key.publicKey, { algorithms: ['RS256'] });
res.send(JSON.stringify(verify))
}
catch(error) {
res.send(error);
}
});
app.listen(port, () => {
console.log(`server started on port ${port}`);
});npm install @supabase/supabase-js┌─────────────┐ ┌──────────────┐ ┌──────────────┐
│ Browser │ │ Authgear │ │ Supabase │
│ (React App)│◄────────►│ (Auth IdP) │ │ (Database) │
└──────┬──────┘ └──────────────┘ └──────┬───────┘
│ │
│ 1. Login with Authgear │
│ 2. Get Authgear JWT (access token) │
│ 3. Call Supabase with Authgear JWT (request data)│
└──────────────────────────────────────────────────►
│ │
│ 4. Exchange JWT (Edge Function) │
│ 5. Return Supabase JWT │
│◄──────────────────────────────────────────────────
│ │
│ 6. Access data with Supabase JWT (enforce RLS) │
└──────────────────────────────────────────────────►
// supabase/functions/exchange-jwt/index.ts
import "jsr:@supabase/functions-js/edge-runtime.d.ts"
import jwt from "npm:jsonwebtoken";
import jwks from "npm:jwks-rsa";
import * as jose from "https://deno.land/x/[email protected]/index.ts";
// CORS headers for cross-origin requests
const corsHeaders = {
"Access-Control-Allow-Origin": "*",
"Access-Control-Allow-Headers": "Authorization, Content-Type",
"Access-Control-Allow-Methods": "GET",
"Access-Control-Max-Age": "3600"
};
// Read environment variables
const authgearEndpoint = Deno.env.get("AUTHGEAR_ENDPOINT");
const supabaseJwtSecret = Deno.env.get("SB_JWT_SECRET");
if (!authgearEndpoint || !supabaseJwtSecret) throw new Error("Missing env vars");
// Get JWKS URI from Authgear's OpenID configuration
async function getJwksUri(): Promise<string> {
const configUrl = `${authgearEndpoint}/.well-known/openid-configuration`;
const response = await fetch(configUrl);
const config = await response.json();
return config.jwks_uri;
}
// Extract Bearer token from Authorization header
function extractToken(req: Request): string | null {
const authHeader = req.headers.get("Authorization");
if (!authHeader) return null;
const parts = authHeader.split(" ");
if (parts.length !== 2 || parts[0] !== "Bearer") return null;
return parts[1];
}
// Verify JWT token with Authgear's public key
async function verifyToken(token: string): Promise<any> {
// Decode token to get key ID
const decoded = jwt.decode(token, { complete: true }) as any;
if (!decoded?.header?.kid) {
throw new Error("Invalid token: missing key ID");
}
// Get JWKS URI and create JWKS client
const jwksUri = await getJwksUri();
const jwksClient = jwks({ jwksUri });
// Get the signing key
const key = await jwksClient.getSigningKey(decoded.header.kid);
const signingKey = key.getPublicKey();
// Verify the token
const options = {
algorithms: ["RS256"],
issuer: authgearEndpoint,
};
return jwt.verify(token, signingKey, options);
}
// Sign a new JWT with Supabase secret
async function signSupabaseJwt(payload: any): Promise<string> {
payload.role = "authenticated"; // Required by Supabase
// Add or modify any other claims you need for RLS policies
// payload.some_claim = "some claim";
// Sign with Supabase JWT secret
const supabaseSecret = new TextEncoder().encode(supabaseJwtSecret);
const supabaseJwt = await new jose.SignJWT(payload)
.setProtectedHeader({ alg: "HS256", typ: "JWT" })
.setIssuer("supabase")
.setIssuedAt(payload.iat)
.setExpirationTime(payload.exp || "")
.sign(supabaseSecret);
return supabaseJwt;
}
// Main function handler
Deno.serve(async (req: Request) => {
// Handle CORS preflight requests
if (req.method === "OPTIONS") {
return new Response("ok", { headers: corsHeaders });
}
try {
// Extract token from request
const token = extractToken(req);
if (!token) {
return new Response(
JSON.stringify({ error: "Missing or invalid Authorization header" }),
{
headers: { ...corsHeaders, "Content-Type": "application/json" },
status: 401
}
);
}
// Verify the token
const verified = await verifyToken(token);
// Sign a new JWT with Supabase secret
const supabaseJwt = await signSupabaseJwt(verified);
return new Response(
JSON.stringify({ supabaseJwt }),
{
headers: { ...corsHeaders, "Content-Type": "application/json" },
status: 200,
}
);
} catch (error) {
console.error("Token verification failed:", error.message);
return new Response(
JSON.stringify({ error: "Token verification failed" }),
{
headers: { ...corsHeaders, "Content-Type": "application/json" },
status: 401,
}
);
}
});
${SUPABASE_URL}/functions/v1/exchange-jwt-- 1. Helper function to get the current Authgear user ID from the JWT
CREATE OR REPLACE FUNCTION current_user_id()
RETURNS TEXT AS $$
SELECT auth.jwt() ->> 'sub';
$$ LANGUAGE SQL STABLE;-- 2. Instruments table: each row has a user_id to identify the owner
CREATE TABLE instruments (
id BIGSERIAL PRIMARY KEY,
created_at TIMESTAMPTZ DEFAULT NOW() NOT NULL,
name TEXT NOT NULL,
user_id TEXT NOT NULL -- store Authgear user’s ID (sub)
);
-- 3. Enable Row Level Security on the table
ALTER TABLE instruments ENABLE ROW LEVEL SECURITY;
-- 4. RLS Policies:
-- Allow each authenticated user to SELECT rows where user_id = their own ID
CREATE POLICY "Users can read their own instruments"
ON instruments
FOR SELECT
TO authenticated
USING (user_id = current_user_id());
-- Allow INSERTs only if setting user_id to their own ID
CREATE POLICY "Users can insert their own instruments"
ON instruments
FOR INSERT
TO authenticated
WITH CHECK (user_id = current_user_id());
-- Allow UPDATE on rows they own
CREATE POLICY "Users can update their own instruments"
ON instruments
FOR UPDATE
TO authenticated
USING (user_id = current_user_id())
WITH CHECK (user_id = current_user_id());
-- Allow DELETE on rows they own
CREATE POLICY "Users can delete their own instruments"
ON instruments
FOR DELETE
TO authenticated
USING (user_id = current_user_id());VITE_SUPABASE_URL=https://your-project.supabase.co
VITE_SUPABASE_PUBLISHABLE_KEY=your-supabase-anon-key
VITE_AUTHGEAR_ENDPOINT=https://your-app.authgear.cloud
VITE_AUTHGEAR_CLIENT_ID=your-authgear-client-id
VITE_AUTHGEAR_REDIRECT_URL=http://localhost:5173/auth-redirect
VITE_AUTHGEAR_LOGOUT_REDIRECT_URL=http://localhost:5173/// my-app/src/lib/supabase.js
import { createClient } from '@supabase/supabase-js';
import authgear from '@authgear/web';
const SUPABASE_URL = import.meta.env.VITE_SUPABASE_URL;
const SUPABASE_ANON_KEY = import.meta.env.VITE_SUPABASE_PUBLISHABLE_KEY;
// Optional: caches to avoid redundant token exchanges
let cachedSupabaseJwt = null;
let cachedAuthgearToken = null;
// Function to exchange Authgear token for Supabase token
async function exchangeToken(authgearToken) {
// Return cached token if the Authgear token hasn’t changed
if (cachedAuthgearToken === authgearToken && cachedSupabaseJwt) {
return cachedSupabaseJwt;
}
// Call the Supabase Edge Function
const res = await fetch(`${SUPABASE_URL}/functions/v1/exchange-jwt`, {
headers: { Authorization: `Bearer ${authgearToken}` }
});
if (!res.ok) {
throw new Error(`Token exchange failed with status ${res.status}`);
}
const { supabaseJwt } = await res.json();
// Update cache and return the new JWT
cachedAuthgearToken = authgearToken;
cachedSupabaseJwt = supabaseJwt;
return supabaseJwt;
}
// Create Supabase client with custom auth settings
export const supabase = createClient(SUPABASE_URL, SUPABASE_ANON_KEY, {
auth: {
autoRefreshToken: false, // Don't use Supabase’s token refresh
persistSession: false, // Don't store Supabase session (Authgear will handle session)
},
accessToken: async () => {
// This function runs before every Supabase request that needs auth
await authgear.refreshAccessTokenIfNeeded();
const authgearToken = authgear.accessToken;
if (!authgearToken) return null;
// Exchange Authgear token for a Supabase token:contentReference[oaicite:12]{index=12}:contentReference[oaicite:13]{index=13}
return exchangeToken(authgearToken);
},
});
const { data, error } = await supabase.from('instruments').select('*');supabase.from('instruments').insert({
name: "<new intruments>",
user_id: userInfo.sub,
});npm run devcomposer create-project laravel/laravel authgear-laravel-example<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<meta name="viewport" content="width=device-width, initial-scale=1.0">
<title>PHP Demo - Home</title>
</head>
<body style="background-color: #DEDEDE">
<div style="max-width: 650px; margin: 16px auto; background-color: #FFFFFF; padding: 16px;">
<h3>Hello world!</h3>
<p>This demo app shows you how to add user authentication to your Laravel app using Authgear</p>
<p>Checkout <a href="https://docs.authgear.com">docs.authgear.com</a> to learn more about adding Authgear to your apps.</p>
<p><a href="/login">Login</a></p>
</div>
</body>
</html>composer require laravel/breeze --devphp artisan breeze:install$table->string('oauth_uid')->nullable();php artisan migratephp artisan make:controller OAuthControllercomposer require league/oauth2-clientuse \League\OAuth2\Client\Provider\GenericProvider;
use Illuminate\Support\Facades\Auth;
use Illuminate\Support\Facades\Hash;
use App\Models\User;
class OAuthController extends Controller {
public $provider;
public function __construct ()
{
$appUrl = env("AUTHGEAR_PROJECT_URL", "");
$this->provider = new GenericProvider([
'clientId' => env("AUTHGEAR_APP_CLIENT_ID", ""),
'clientSecret' => env("AUTHGEAR_APP_CLIENT_SECRET", ""),
'redirectUri' => env("AUTHGEAR_APP_REDIRECT_URI", ""),
'urlAuthorize' => $appUrl.'/oauth2/authorize',
'urlAccessToken' => $appUrl.'/oauth2/token',
'urlResourceOwnerDetails' => $appUrl.'/oauth2/userInfo',
'scopes' => 'openid offline_access'
]);
}
public function startAuthorization() {
$authorizationUrl = $this->provider->getAuthorizationUrl();
return redirect($authorizationUrl);
}
public function handleRedirect() {
}
}AUTHGEAR_PROJECT_URL=""
AUTHGEAR_APP_CLIENT_ID=""
AUTHGEAR_APP_CLIENT_SECRET=""
AUTHGEAR_APP_REDIRECT_URI="http://localhost:8000/oauth/callback"Route::get('/login', [OAuthController::class, 'startAuthorization']);
Route::get('/oauth/callback', [OAuthController::class, 'handleRedirect']);Route::get('login', [AuthenticatedSessionController::class, 'create'])
->name('login');
Route::post('login', [AuthenticatedSessionController::class, 'store']);public function handleRedirect() {
// if code is set, get access token
$accessToken = null;
if (isset($_GET['code'])) {
$code = $_GET['code'];
try {
$accessToken = $this->provider->getAccessToken('authorization_code', [
'code' => $code
]);
} catch (\League\OAuth2\Client\Provider\Exception\IdentityProviderException $e) {
// Failed to get the access token or user details.
exit($e->getMessage());
}
}
}//Use access token to get user info
if (isset($accessToken)) {
$resourceOwner = $this->provider->getResourceOwner($accessToken);
$userInfo = $resourceOwner->toArray();
}[
"custom_attributes" => []
"email" => "[email protected]"
"email_verified" => true
"https://authgear.com/claims/user/can_reauthenticate" => true
"https://authgear.com/claims/user/is_anonymous" => false
"https://authgear.com/claims/user/is_verified" => true
"sub" => "e1234323-f123-4b99-91d8-c2ca55a6a3dc"
"updated_at" => 1683898685
"x_web3" => []
]$userInfo = $resourceOwner->toArray();if (empty($userInfo['email'])) {
return redirect('/')->withErrors(['msg' => 'Only profile with email is supported!']);
}
//check if user already registered
$oldUser = User::query()->whereEmail($userInfo['email'])->first();
if (!empty($oldUser)) {
//if old user has the same Authgear sub (uuid), skip register and log them in.
if ($userInfo['sub'] == $oldUser->oauth_uid) {
Auth::guard('web')->login($oldUser);
session(['accessToken' => $accessToken]);
session(['refreshToken' => $accessToken->getRefreshToken()]);
} else {
//if sub is different,
//ask user to login to existing account and link the existing account to link new authgear profile
return redirect('/')->withErrors(['msg' => 'Email already registered please log in to link your account.']);
}
} else {
$user = User::create([
'name' => $userInfo['email'],
'email' => $userInfo['email'],
'oauth_uid' => $userInfo['sub'],
'password' => Hash::make($userInfo['sub'] . "-" . $userInfo['email'])
]);
Auth::guard('web')->login($user);
session(['accessToken' => $accessToken]);
session(['refreshToken' => $accessToken->getRefreshToken()]);
}
// Redirect user to a protected route
return redirect('/dashboard');public function edit(Request $request): View
{
$appUrl = env("AUTHGEAR_PROJECT_URL", "");
$provider = new GenericProvider([
'clientId' => env("AUTHGEAR_APP_CLIENT_ID", ""),
'clientSecret' => env("AUTHGEAR_APP_CLIENT_SECRET", ""),
'redirectUri' => env("AUTHGEAR_APP_REDIRECT_URI", ""),
'urlAuthorize' => $appUrl . '/oauth2/authorize',
'urlAccessToken' => $appUrl . '/oauth2/token',
'urlResourceOwnerDetails' => $appUrl . '/oauth2/userInfo',
'scopes' => 'openid offline_access'
]);
$accessToken = session('accessToken');
if ($accessToken->hasExpired()) {
$refreshToken = session('refreshToken');
$accessToken = $provider->getAccessToken('refresh_token', [
'refresh_token' => $refreshToken
]);
session(['accessToken' => $accessToken]);
}
$resourceOwner = $provider->getResourceOwner($accessToken);
$userInfo = $resourceOwner->toArray();
return view('profile.edit', [
'user' => $request->user(), 'authgearUserInfo' => $userInfo,
]);
}<div class="p-4 sm:p-8 bg-white shadow sm:rounded-lg">
<div class="max-w-xl">
<h2>Authgear user data</h2>
<p>Email: {{ $authgearUserInfo['email'] }}</p>
<p>UUID: {{ $authgearUserInfo['sub'] }}</p>
</div>
</div>public function logout(Request $request)
{
Auth::guard('web')->logout();
$request->session()->invalidate();
$request->session()->regenerateToken();
if (session('accessToken') != null) {
$options = [];
$options['headers']['content-type'] = 'application/x-www-form-urlencoded';
$options['body'] = http_build_query(['token'=>session('refreshToken')]);
$request = $this->provider->getRequest(
'POST',
env("AUTHGEAR_PROJECT_URL", "") . '/oauth2/revoke',
$options
);
$this->provider->getResponse($request);
session(['accessToken' => null]);
session(['refreshToken' => null]);
}
return redirect('/');
}Route::post('logout', [OAuthController::class, 'logout'])
->name('logout');
import java.io.BufferedReader;
import java.io.InputStreamReader;
import java.net.HttpURLConnection;
import java.net.URL;
import java.util.List;
import org.springframework.boot.autoconfigure.SpringBootApplication;
import org.springframework.web.bind.annotation.GetMapping;
import org.springframework.web.bind.annotation.RequestHeader;
import org.springframework.web.bind.annotation.RestController;
import com.nimbusds.jose.jwk.JWKSet;
import com.nimbusds.jose.jwk.RSAKey;
import com.nimbusds.jwt.JWTClaimsSet;
import com.nimbusds.jwt.SignedJWT;
@SpringBootApplication
@RestController
public class DemoApplication {
//paste implementation for fetchJwksUri() method below this line.
//paste implemetation of getSigningKeyFromJwks() method below this line.
private static final String BASE_ADDRESS = ""; //place your authgear app endpoint here
@GetMapping("/validateJwt")
public Object validateJwt(@RequestHeader("Authorization") String authorizationHeader) {
if (authorizationHeader == null || !authorizationHeader.startsWith("Bearer ")) {
return new ResponseMessage("authorization header not found");
}
String token = authorizationHeader.substring(7); // Extract token
try {
// Fetch JWKS URI dynamically
String jwksUri = fetchJwksUri(BASE_ADDRESS);
// Get signing key from JWKS
RSAKey signingKey = getSigningKeyFromJwks(jwksUri, token);
if (signingKey == null) {
return new ResponseMessage("JWT decode failed: Signing key not found");
}
// Validate and decode JWT
SignedJWT signedJWT = SignedJWT.parse(token);
JWTClaimsSet claimsSet = signedJWT.getJWTClaimsSet();
return new ResponseMessage("Hello!", claimsSet.toJSONObject());
} catch (Exception e) {
return new ResponseMessage("JWT decode failed: " + e.getMessage());
}
}
private static String fetchJwksUri(String baseAddress) throws Exception {
String docUrl = baseAddress + "/.well-known/openid-configuration";
HttpURLConnection conn = (HttpURLConnection) new URL(docUrl).openConnection();
conn.setRequestMethod("GET");
try (BufferedReader reader = new BufferedReader(new InputStreamReader(conn.getInputStream()))) {
StringBuilder response = new StringBuilder();
String line;
while ((line = reader.readLine()) != null) {
response.append(line);
}
String jwksUri = new org.json.JSONObject(response.toString()).getString("jwks_uri");
if (jwksUri == null || jwksUri.isEmpty()) {
throw new Exception("Failed to fetch JWKS URI.");
}
return jwksUri;
}
}
private static RSAKey getSigningKeyFromJwks(String jwksUri, String token) throws Exception {
JWKSet jwkSet = JWKSet.load(new URL(jwksUri));
List<com.nimbusds.jose.jwk.JWK> keys = jwkSet.getKeys();
SignedJWT signedJWT = SignedJWT.parse(token);
String keyId = signedJWT.getHeader().getKeyID();
return keys.stream()
.filter(jwk -> jwk.getKeyID().equals(keyId))
.findFirst()
.map(jwk -> (RSAKey) jwk)
.orElse(null);
}
static class ResponseMessage {
public String message;
public Object user_data;
public ResponseMessage(String message) {
this.message = message;
}
public ResponseMessage(String message, Object user_data) {
this.message = message;
this.user_data = user_data;
}
}
}
Guide on how to use Authgear in an Ionic project
In this post, you'll learn how to use Authgear with your Ionic project using the Authgear Ionic SDK.
The following are the minimum versions of Android and iOS your native app can target based on the requirement of Capacitor v7:
iOS 14
Android 6 (API level 23)
At the end of this tutorial, we'll build an Ionic app that can do the following:
Allow users to log in to their account on your Authgear project
Allow new users to sign up
Allow signed-in users to view their user info and logout.
The final UI for the app we'll build should look like this:
To follow this guide seamlessly, make sure to have the following:
Node.js installed on your local machine
Android Studio (for building the Android client of your application)
Xcode (for building the iOS client of your application)
An Authgear account. You can sign up for one for free .
Follow this guide to add Authgear to your Ionic app in 🕐 10 minutes.
In this part, you'll learn how to configure an Authgear client application that you will use in your Ionic project. You'll do this by performing the following steps in the Authgear Portal.
First, log in to Authgear Portal at and select an existing project or create a new one.
In your project, navigate to the Applications section then click on Add Application to create a new Authgear application. Enter a name for your application and select Native App as the Application Type. Next, click Save to continue to the configuration page for your new application. Skip the screen that shows you a list of tutorials for different frameworks.
In this step, you'll set up authorized redirect URIs for your application. An authorized redirect URI should be a URI pointing to a page on your Ionic app where you want to redirect users at the end of the authorization flow.
To add a URI, scroll to the URIs section of your application configuration page and enter the URI in the text field. You can click the Add URI button to add additional URIs.
For our example app, add the following URIs:
com.authgear.example.capacitor://host/path
capacitor://localhost
http://localhost:8100/oauth-redirect
Once you're done, click on the Save button.
Now that you have your Authgear application configured, we can proceed with creating the Ionic application that will have all the features stated in our objective earlier.
For this tutorial, we'll be implementing an Ionic app using React.
Before you can create an Ionic project, install the Ionic CLI on your computer by running the following command in Terminal or Command Prompt:
Now create a new Ionic project by running the following command:
After running the above command, follow the wizard to create a new blank project.
Next, open your new project in a code editor and update for appId in capacitor.config.ts to the following value:
This new value for appId is the same value we used in the authorized redirect URI earlier.
Run the following command from the root directory of your new Ionic project to preview your blank project on a browser:
Finally, create the Android and iOS projects for your app by running the following commands from your Ionic project's root folder:
First, install the Android and iOS platforms:
Then, create the projects:
In this step, you'll install the Authgear SDK for Ionic (Capacitor) and the Javascript SDK for the web. The web SDK will help you test your application on a web browser.
To install the SDKs, run the following commands in your Terminal or Command Prompt:
Authgear Ionic SDK
Authgear Web SDK
In this step, you'll learn how to configure your Ionic project using the details from your Authgear application configuration.
To get started, open src/pages/Home.tsx in your code editor then import the Authgear SDK by adding the following code to the top of the file:
The above code imports all the components of the Authgear SDK we need for our example app.
Because Ionic apps can run on the web and native mobile platforms, we had to import both Authgear web and Authgear Capacitor SDKs.
Next, add the following constants to Home.tsx just below the last import statements:
Update the values for the constants (CLIENT_ID, ENDPOINT) to the correct values from your client application's configuration page in the Authgear Portal.
Now, just below the constants, add this small utility function that will help to check whether your Ionic app is running natively or on a web browser:
Import Capacitor by adding the following to the import section at the top of Home.tsx:
You will use the above function to determine which instance of the Authgear SDK to call based on the current platform a user is on.
Now implement a new AuthenticationScreen component in Home.tsx by pasting the following code:
Import useState, useMemo, useEffect and useCallback at the top of Home.tsx:
The above code also implements a sessionState constant and a delegate to let your app know when a user's session state changes.
Next, add the following configure() method to the AuthenticationScreen() component just before the return statement:
The above code configures a new instance of the Authgear SDK using the Client ID and Endpoint for the Authgear client application we created in the first part of this guide.
Next, implement the postConfigure() method that was called in the configure() method:
The postConfigure() method checks if the user is already authenticated and calls the fetchUserInfo() method of the Authgear SDK. Calling the fetchUserInfo() method will refresh the user's access token if it is expired.
Now, call the configure() method in useEffect by adding the following code after the postConfigure() method:
The above useEffect will initialize Authgear on page load.
In this step, we'll add the Login button and the UI components we want to show authenticated users.
Add the following code to the <div> inside the return statement of the AuthenticationScreen component:
Import IonButton by adding it to the import for other Ionic components in our app:
Finally, add the <AuthenticationScreen/> component to the Home component:
Here, we'll implement an authenticate() method inside the AuthenticationScreen component we created in the previous step.
To do this, first, add the following code just before the return statement of the AuthenticationScreen() component:
Calling this authenticate() method will initialize an authentication flow. The page parameter can be used to specify whether to start the authentication flow on the login page or signup page.
Finally, implement a onClickAuthenticate() method that will call authenticate when the Login button is pressed:
Import MouseEvent:
At this point, the complete code for Home.tsx should look like this:
Save your work and run the command to serve your project on the web or .
You should be able to see the Authentication UI after you click on the Login button. However, you can't complete the authentication flow because we're yet to handle the redirect.
At the end of an authentication flow, your users will be redirected to the URL you specified in redirectURI. In this step, we'll set up the routes and code to process redirects to the URIs.
To handle redirect on web, create a new file OAuthRedirect.tsx in src/pages/ and add the following code to it:
Change the values for CLIENT_ID and ENDPOINT in the above code to the correct value from your Authgear application configuration page.
Now open src/App.tsx and create a new route for OAuthRedirect using the following code:
Remember to import OAuthRedirect in App.tsx:
To handle redirect in the Android project, add the following code to android/app/src/main/AndroidManifest.xml:
At this point, if you build your project and run it, you should be able to login successfully.
To implement Logout, we'll add a Logout button, an onClick handler, and a method that will call the logout() method of the Authgear SDK.
Add a Logout button to AuthenticationScreen component just below <p>Welcome user</p>:
Next, add a logout() method to AuthenticationScreen component:
Finally, implement the onClick method in AuthenticationScreen :
The Authgear SDK offers a fetchUserInfo() method that can return details such as User ID, email, phone number, and so on about the current user. In this step, we'll demonstrate how to call fetchUserInfo in our app.
First, add a Fetch User Info button to your AuthenticationScreen component just below the Logout button:
Next, add a fetchUserInfo() method to the AuthenticationScreen component:
Finally, add the method that will handle click on the Fetch User Info button:
Authgear provides a default User Settings page where your users can view details about their profile and change details or security settings like their password.
To allow users to open the settings page from your app, first add a User Settings button to you r AuthenticationScreen component just below the Fetch User Info button:
Now add an openUserSettings() method in AuthenticationScreen component:
Finally, implement the onClick method for the User Settings button:
To deploy your app to a mobile device (for example Android) run the following commands:
First build your project by running:
Then sync the changes to the mobile project using this command:
You can run the project by opening the android project folder in Android Studio or ios folder in Xcode.
You can quickly open the project in Android Studio using the following command:
Or run the following command to open your project in Xcode for iOS:
Once your project builds successfully, you can try the Login, Signup, Fetch User Info, and Logout buttons.
Authgear Capacitor SDK makes it easier to use Authgear in your Ionic application. It provides many helpful methods and interfaces for interacting with the Authgear service from your Ionic application. To learn more about the SDK check . Also, check out the complete repo for the Authgear Ionic SDK example app .
Follow this quickstart tutorial to add authentication to your Angular application
Authgear helps you add user logins to your Angular apps. It provides prebuilt login page and user settings page that accelerate the development.
Follow this 🕐 15 minutes tutorial to create a simple app using Angular with Authgear SDK.
Table of Content
Any code editor (VS Code, Sublime, etc)
https://localhost


Signup for an account in https://portal.authgear.com/ and create a Project.
After that, we will need to create an Application in the Project Portal.
Go to Applications on the left menu bar.
Click ⊕Add Application in the top tool bar.
Input the name of your application, e.g. "MyAwesomeApp".
Select Single Page Application as the application type
Click "Save" to create the application
The Redirect URI is a URL in you application where the user will be redirected to after login with Authgear. In this path, make a finish authentication call to complete the login process.
For this tutorial, add http://localhost:4000/auth-redirect to Authorize Redirect URIs.
The Post Logout Redirect URI is the URL users will be redirected after they have logged out. The URL must be whitelisted.
For this tutorial, add http://localhost:4000/ to Post Logout Redirect URIs.
Save the configuration before next steps.
Here are some recommended steps to scaffold an Angular project. You can skip this part if you are adding Authgear to an existing project. See Step 2: Install Authgear SDK to the project in the next section.
To install the Angular CLI, open a terminal window and run the following command:
Run the following cli command to create a new workspace and initial app called my-app with a routing module generated.
In the package.json file, edit the start script in the script section
The start script run the app in development mode on port 4000 instead of the default one.
By default, the Angular CLI generated an initial application for us, but for simplicity, we recommend to modify some of these files to scratch.
In the src/app/app.component.html file, remove all the lines and add the following line:
Run npm start now to run the project and you will see "Hello world" on http://localhost:4000.
Run the following command within your Angular project directory to install the Authgear Web SDK
In src/app/app.component.ts , import authgear and call the configure function to initialize an Authgear instance on application loads.
The Authgear container instance takes endpoint and clientID as parameters. They can be obtained from the application page created in Setup Application in Authgear.
It is recommend to render the app after configure() resolves. So by the time the app is rendered, Authgear is ready to use.
Since we want to reference the logged in state in anywhere of the app, let's put the state in a service with user.service.ts in the /src/app/services/ folder.
In user.service.ts, it will have a isLoggedIn boolean variable. The isLoggedIn boolean variable can be auto updated using the onSessionStateChange callback. This callback can be stored in delegate which is in the local SDK container.
Next, we will add an "auth-redirect" page for handling the authentication result after the user have been authenticated by Authgear.
Create the auth-redirect component using the following command:
We will inject the router and the UserService to get the use of navigation and the isLoggedIn state.
Call the Authgear finishAuthentication() function in the Auth Redirect component to send a token back to Authgear server in exchange for access token and refresh token. Don't worry about the technical jargons, finishAuthentication() will do all the hard work for you and and save the authentication data.
When the authentication is finished, the isLoggedIn state from the UserService will automatic set to true. Finally, navigate back to root (/) which is our Home page.
The final auth-redirect.component.ts will look like this
Next, we will add a "Home" page . Create a home component using the following command:
Then import HomeComponent and AuthRedirectComponent as routes. We can add those routes in the app-routing.module.ts file:
You can apply those routes in src/app/app.component.html by replace the lines with the following:
The file structure should now look like
First we will import the Authgear dependency and inject the UserService in home.component.ts. Then add the startLogin method which will call startAuthentication(ConfigureOptions). This will redirect the user to the login page.
Then you can add a button which will trigger the startLogin method in home.component.html:
You can now run npm start and you will be redirected to the Authgear Login page when you click the Login button.
The Authgear SDK helps you get the information of the logged in users easily.
In the last step, the user is successfully logged in so let's try to print the user ID (sub) of the user in the Home page.
In home component, we will add a simple Loading splash and a greeting message printing the Sub ID. We will add two conditional elements such that they are only shown when user is logged in. We can also change the login button to show only if the user is not logged in.
Make use of isLoggedIn from the UserService to control the components on the page. Fetch the user info by fetchInfo() and access its sub property.
In the home.component.html:
Run the app again, the User ID (sub) of the user should be printed on the Home page.
Finally, let's add an Logout button when user is logged in.
In home.component.html, we will add a conditional element in the markup:
And add the logout method:
Run the app again, we can now logout by clicking the logout button.
Authgear provide a built-in UI for the users to set their attributes and change security settings.
Use the open function to open the setting page at <your_app_endpoint>/settings
In home.component.html append a conditional link to the logout button section.
And add the userSetting method:
This the resulting home.component.ts:
This is the resulting home.component.html:
To access restricted resources on your backend application server, the HTTP requests should include the access token in their Authorization headers. The Web SDK provides a fetch function which automatically handle this, or you can get the token with authgear.accessToken.
Authgear SDK provides the fetch function for you to call your application server. This fetch function will include the Authorization header in your application request, and handle refresh access token automatically. The authgear.fetch implements fetch.
You can get the access token through authgear.accessToken. Call refreshAccessTokenIfNeeded every time before using the access token, the function will check and make the network call only if the access token has expired. Include the access token into the Authorization header of the application request.
Authgear provides an easy method to reauthenticate the end-users. You can use this as a security measure to protect sensitive operations.
Reauthentication in Authgear is built on top of the OIDC ID token. The ID token is a JWT.
Your sensitive operation server endpoint MUST require the ID token. When you receive the ID token, you MUST verify the signature of it. If the signature is valid, you can trust the claims inside the ID token.
The auth_time claim in the ID token tells when was the end-user last authenticated. You should check the auth_time claim to see if the end-user was authenticated recently enough.
The https://authgear.com/claims/user/can_reauthenticate claim in the ID token tells whether the end-user can be reauthenticated. If the value of this claim is false, then depending on your business needs, you can either allow the end-user to proceed, or forbid the end-user to perform sensitive operations. The flows are illustrated by the following diagrams.
The following code snippets illustrate the interaction between the SDK and Authgear.
If the end-users in your application often perform a series of sensitive operation, it is annoying that they have to reauthenticate themselves repeatedly before every operation. To allow the end-users to skip reauthentication if they have just reauthenticated themselves recently, the SDK allows you to inspect the last authentication time of the end-user.
Finally in your backend, you have to verify the signature of the ID token, and then validate the claims inside.
npm install -g @ionic/cli native-run cordova-resionic start authgear-ionic-example --type=react --capacitorappId: 'com.authgear.example.capacitor',ionic servenpm i @capacitor/android @capacitor/iosnpx cap add android
npx cap add iosnpm i @authgear/capacitornpm i @authgear/webimport authgearWeb, {
SessionState,
WebContainer,
SessionStateChangeReason,
} from "@authgear/web";
import authgearCapacitor, {
CapacitorContainer,
Page,
} from "@authgear/capacitor";const CLIENT_ID = "<ClIENT_ID>";
const ENDPOINT = "<AUTHGEAR_ENDPOINT>";
const REDIRECT_URI_WEB_AUTHENTICATE = "http://localhost:8100/oauth-redirect";
const REDIRECT_URI_CAPACITOR = "com.authgear.example.capacitor://host/path";
const REDIRECT_URI_WEB_REAUTH = "http://localhost:8100/reauth-redirect";function isPlatformWeb(): boolean {
return Capacitor.getPlatform() === "web";
}import { Capacitor } from "@capacitor/core";function AuthenticationScreen() {
const [sessionState, setSessionState] = useState<SessionState | null>(() => {
if (isPlatformWeb()) {
return authgearWeb.sessionState;
}
return authgearCapacitor.sessionState;
});
const loggedIn = sessionState === "AUTHENTICATED";
const delegate = useMemo(() => {
const d = {
onSessionStateChange: (
container: WebContainer | CapacitorContainer,
_reason: SessionStateChangeReason
) => {
setSessionState(container.sessionState);
},
};
return d;
}, [setSessionState]);
useEffect(() => {
if (isPlatformWeb()) {
authgearWeb.delegate = delegate;
} else {
authgearCapacitor.delegate = delegate;
}
return () => {
if (isPlatformWeb()) {
authgearWeb.delegate = undefined;
} else {
authgearCapacitor.delegate = undefined;
}
};
}, [delegate]);
return (
<>
<div className="container">
</div>
</>
);
}import React, { useState, useEffect, useCallback, useMemo } from "react";const configure = useCallback(async () => {
try {
if (isPlatformWeb()) {
await authgearWeb.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
sessionType: "refresh_token",
isSSOEnabled: false,
});
} else {
await authgearCapacitor.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
});
}
await postConfigure();
} catch (e) {
console.error("Authgear Configuration error:", e);
}
}, [CLIENT_ID, ENDPOINT]);const postConfigure = useCallback(async () => {
const sessionState = isPlatformWeb()
? authgearWeb.sessionState
: authgearCapacitor.sessionState;
// if user has an existing session, call SDK fetchUserInfo method to get the user's info and refresh access token when necessary
if (sessionState === "AUTHENTICATED") {
if (isPlatformWeb()) {
await authgearWeb.fetchUserInfo();
} else {
await authgearCapacitor.fetchUserInfo();
}
}
}, []);useEffect(() => {
configure();
}, []);<h1>
Welcome
</h1>
{!loggedIn ? (
<IonButton
className="button"
// disabled={!initialized || loading || loggedIn}
onClick={
(event) => {
onClickAuthenticate(event, "login")
}
}
>
Login
</IonButton>
):
(
<div>
<p>Welcome user</p>
</div>
)}import { IonContent, IonHeader, IonPage, IonTitle, IonToolbar, IonButton } from '@ionic/react';const Home: React.FC = () => {
return (
<IonPage>
<IonHeader>
<IonToolbar>
<IonTitle>Blank</IonTitle>
</IonToolbar>
</IonHeader>
<IonContent fullscreen>
<IonHeader collapse="condense">
<IonToolbar>
<IonTitle size="large">Blank</IonTitle>
</IonToolbar>
</IonHeader>
<AuthenticationScreen />
</IonContent>
</IonPage>
);
};const authenticate = useCallback(async (page: string) => {
try {
if (isPlatformWeb()) {
authgearWeb.startAuthentication({
redirectURI: REDIRECT_URI_WEB_AUTHENTICATE,
page: page,
});
} else {
const result = await authgearCapacitor.authenticate({
redirectURI: REDIRECT_URI_CAPACITOR,
page: page,
});
}
} catch (e) {
console.error("Authentication error:", e);
}
}, []);const onClickAuthenticate = useCallback(
(e: MouseEvent<HTMLIonButtonElement>, page: string) => {
e.preventDefault();
e.stopPropagation();
authenticate(page);
},
[authenticate]
);import type { MouseEvent } from "react";import {
IonContent,
IonHeader,
IonPage,
IonTitle,
IonToolbar,
IonButton,
} from "@ionic/react";
import React, { useState, useEffect, useCallback, useMemo } from "react";
import { Capacitor } from "@capacitor/core";
import type { MouseEvent } from "react";
import authgearWeb, {
SessionState,
WebContainer,
SessionStateChangeReason,
} from "@authgear/web";
import authgearCapacitor, {
CapacitorContainer,
Page,
} from "@authgear/capacitor";
import "./Home.css";
const CLIENT_ID = <ClIENT_ID>";
const ENDPOINT = "<AUTHGEAR_ENDPOINT>";
const REDIRECT_URI_WEB_AUTHENTICATE = "http://localhost:8100/oauth-redirect";
const REDIRECT_URI_CAPACITOR = "com.authgear.example.capacitor://host/path";
function isPlatformWeb(): boolean {
return Capacitor.getPlatform() === "web";
}
function AuthenticationScreen() {
const [sessionState, setSessionState] = useState<SessionState | null>(() => {
if (isPlatformWeb()) {
return authgearWeb.sessionState;
}
return authgearCapacitor.sessionState;
});
const loggedIn = sessionState === "AUTHENTICATED";
const delegate = useMemo(() => {
const d = {
onSessionStateChange: (
container: WebContainer | CapacitorContainer,
_reason: SessionStateChangeReason
) => {
setSessionState(container.sessionState);
},
};
return d;
}, [setSessionState]);
useEffect(() => {
if (isPlatformWeb()) {
authgearWeb.delegate = delegate;
} else {
authgearCapacitor.delegate = delegate;
}
return () => {
if (isPlatformWeb()) {
authgearWeb.delegate = undefined;
} else {
authgearCapacitor.delegate = undefined;
}
};
}, [delegate]);
const configure = useCallback(async () => {
try {
if (isPlatformWeb()) {
await authgearWeb.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
sessionType: "refresh_token",
isSSOEnabled: false,
});
} else {
await authgearCapacitor.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
});
}
await postConfigure();
} catch (e) {
console.error("Authgear Configuration error:", e);
}
}, [CLIENT_ID, ENDPOINT]);
const postConfigure = useCallback(async () => {
const sessionState = isPlatformWeb()
? authgearWeb.sessionState
: authgearCapacitor.sessionState;
// if user has an existing session, call SDK fetchUserInfo method to get the user's info and refresh access token when necessary
if (sessionState === "AUTHENTICATED") {
if (isPlatformWeb()) {
await authgearWeb.fetchUserInfo();
} else {
await authgearCapacitor.fetchUserInfo();
}
}
}, []);
useEffect(() => {
configure();
}, []);
const authenticate = useCallback(async (page: string) => {
try {
if (isPlatformWeb()) {
authgearWeb.startAuthentication({
redirectURI: REDIRECT_URI_WEB_AUTHENTICATE,
page: page,
});
} else {
const result = await authgearCapacitor.authenticate({
redirectURI: REDIRECT_URI_CAPACITOR,
page: page,
});
}
} catch (e) {
console.error("Authentication error:", e);
}
}, []);
const onClickAuthenticate = useCallback(
(e: MouseEvent<HTMLIonButtonElement>, page: string) => {
e.preventDefault();
e.stopPropagation();
authenticate(page);
},
[authenticate]
);
return (
<>
<div className="container">
<h1>Welcome</h1>
{!loggedIn ? (
<IonButton
className="button"
onClick={(event) => {
onClickAuthenticate(event, "login");
}}
>
Login
</IonButton>
) : (
<div>
<p>Welcome user</p>
</div>
)}
</div>
</>
);
}
const Home: React.FC = () => {
return (
<IonPage>
<IonHeader>
<IonToolbar>
<IonTitle>Blank</IonTitle>
</IonToolbar>
</IonHeader>
<IonContent fullscreen>
<IonHeader collapse="condense">
<IonToolbar>
<IonTitle size="large">Blank</IonTitle>
</IonToolbar>
</IonHeader>
<AuthenticationScreen />
</IonContent>
</IonPage>
);
};
export default Home;
import { useCallback, useEffect } from "react";
import authgearWeb from "@authgear/web";
import { useIonRouter } from "@ionic/react";
export default function OAuthRedirect() {
const router = useIonRouter();
const finishAuthentication = useCallback(async () => {
const CLIENT_ID = "<ClIENT_ID>";
const ENDPOINT = "<AUTHGEAR_ENDPOINT>";
try {
await authgearWeb.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
sessionType: "refresh_token",
});
await authgearWeb.finishAuthentication();
router.push("/", "root", "replace");
} catch (e) {
console.error(e);
}
}, [router]);
useEffect(() => {
finishAuthentication();
}, [finishAuthentication]);
return (
<div>
Finishing authentication. Open the inspector to see if there is any error.
</div>
);
}<Route exact path="/oauth-redirect">
<OAuthRedirect />
</Route>import OAuthRedirect from './pages/OAuthRedirect';<!-- Authgear SDK -->
<activity
android:name="com.authgear.capacitor.OAuthRedirectActivity"
android:launchMode="singleTask"
android:exported="true">
<intent-filter>
<action android:name="android.intent.action.VIEW" />
<category android:name="android.intent.category.DEFAULT" />
<category android:name="android.intent.category.BROWSABLE" />
<!-- Configure data to be the exact redirect URI your app uses. -->
<!-- NOTE: The redirectURI supplied in AuthenticateOptions has to match as well -->
<data
android:host="host"
android:pathPrefix="/path"
android:scheme="com.authgear.example.capacitor" />
</intent-filter>
</activity><IonButton className="button" onClick={onClickLogout}>
Logout
</IonButton>const logout = useCallback(async () => {
try {
if (isPlatformWeb()) {
await authgearWeb.logout({
redirectURI: window.location.origin + "/",
});
} else {
await authgearCapacitor.logout();
}
} catch (e) {
console.error("Logout error:", e);
}
}, []);const onClickLogout = useCallback(
(e: MouseEvent<HTMLIonButtonElement>) => {
e.preventDefault();
e.stopPropagation();
logout();
},
[logout]
);<IonButton className="button" onClick={onClickFetchUserInfo}>
Fetch User Info
</IonButton>const fetchUserInfo = useCallback(async () => {
try {
const authgear = isPlatformWeb() ? authgearWeb : authgearCapacitor;
const userInfo = await authgear.fetchUserInfo();
alert(JSON.stringify(userInfo, null, 2)); // Keep for demonstration, but consider a better way to display info
} catch (e) {
console.error("FetchUserInfo error:", e);
}
}, []);const onClickFetchUserInfo = useCallback(
(e: MouseEvent<HTMLIonButtonElement>) => {
e.preventDefault();
e.stopPropagation();
fetchUserInfo();
},
[fetchUserInfo]
);<IonButton
className="button"
onClick={onClickUserSettings}
>
User Settings
</IonButton>const openUserSettings = useCallback(async () => {
try {
if (isPlatformWeb()) {
authgearWeb.open(Page.Settings);
} else {
authgearCapacitor.open(Page.Settings);
}
} catch (e) {
console.error("Error:", e)
}
}, []);const onClickUserSettings = useCallback(
(e: MouseEvent<HTMLIonButtonElement>) => {
e.preventDefault();
e.stopPropagation();
openUserSettings();
},
[logout]
);npm run buildnpx cap syncnpx cap open androidnpx cap open iosnpm install -g @angular/cli# Create a workspace called my-app
ng new my-app --routing --defaults
# Move into the project directory
cd my-app# before
"start": "ng serve"
# after
"start": "ng serve --port 4000"<div>Hello world</div>npm install --save-exact @authgear/web// src/app/app.component.ts
import { Component, OnInit } from '@angular/core';
import authgear from '@authgear/web';
@Component({
selector: 'app-root',
templateUrl: './app.component.html',
styleUrls: ['./app.component.css'],
})
export class AppComponent implements OnInit {
// configure Authgear container instance
initAuthgear(): Promise<void> {
return authgear.configure({
endpoint: '<your_app_endpoint>',
clientID: '<your_client_id>',
sessionType: 'refresh_token',
});
}
ngOnInit(): void {
this.initAuthgear().catch((e) => {
// Error handling
console.log(e);
});
}
}// src/app/services/user.service.ts
import { Injectable } from '@angular/core';
import authgear from '@authgear/web';
@Injectable({
providedIn: 'root',
})
export class UserService {
// By default the user is not logged in
isLoggedIn: boolean = false;
constructor() {
// When the sessionState changed, logged in state will also be changed
authgear.delegate = {
onSessionStateChange: (container) => {
// sessionState is now up to date
// value of sessionState can be "NO_SESSION" or "AUTHENTICATED"
const sessionState = container.sessionState;
if (sessionState === 'AUTHENTICATED') {
this.isLoggedIn = true;
} else {
this.isLoggedIn = false;
}
},
};
}
}ng generate component auth-redirect// src/app/auth-redirect/auth-redirect.component.ts
import { Component, OnInit } from '@angular/core';
import { UserService } from '../services/user.service';
import authgear from '@authgear/web';
import { Router } from '@angular/router';
@Component({
selector: 'app-auth-redirect',
templateUrl: './auth-redirect.component.html',
styleUrls: ['./auth-redirect.component.css'],
})
export class AuthRedirectComponent implements OnInit {
constructor(private router: Router, private user: UserService) {}
ngOnInit(): void {
authgear
.finishAuthentication()
.catch((e) => console.error(e))
.then(() => {
this.router.navigate(['']);
});
}
}ng generate component home// src/app/app-routing.module.ts
import { NgModule } from '@angular/core';
import { RouterModule, Routes } from '@angular/router';
import { AuthRedirectComponent } from './auth-redirect/auth-redirect.component';
import { HomeComponent } from './home/home.component';
const routes: Routes = [
{ path: '', component: HomeComponent },
{ path: 'auth-redirect', component: AuthRedirectComponent },
];
@NgModule({
imports: [RouterModule.forRoot(routes)],
exports: [RouterModule],
})
export class AppRoutingModule {}<router-outlet></router-outlet>src
├── (...)
└── app
├── app-routing.module.ts
├── app.component.ts
├── app.component.html
├── app.module.ts
├── (...)
├── auth-redirect
│ ├── auth-redirect.component.ts
│ ├── auth-redirect.component.html
│ └── (...)
├── home
│ ├── home.component.ts
│ ├── home.component.html
│ └── (...)
└── services
└── user.service.ts// src/app/home/home.component.ts
import { Component, OnInit } from '@angular/core';
import { UserService } from '../services/user.service';
import authgear from '@authgear/web';
@Component({
selector: 'app-home',
templateUrl: './home.component.html',
styleUrls: ['./home.component.css'],
})
export class HomeComponent implements OnInit {
constructor(public user: UserService) {}
ngOnInit(): void {}
startLogin(): void {
authgear
.startAuthentication({
redirectURI: 'http://localhost:4000/auth-redirect',
prompt: 'login',
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
}
}<h1>Home Page</h1>
<button type="button" (click)="startLogin()">Login</button>// src/app/home/home.component.ts
import { Component, OnInit } from '@angular/core';
import { UserService } from '../services/user.service';
import authgear from '@authgear/web';
@Component({
selector: 'app-home',
templateUrl: './home.component.html',
styleUrls: ['./home.component.css'],
})
export class HomeComponent implements OnInit {
isLoading: boolean = false;
greetingMessage: string = '';
constructor(public user: UserService) {}
async updateGreetingMessage() {
this.isLoading = true;
try {
if (this.user.isLoggedIn) {
const userInfo = await authgear.fetchUserInfo();
this.greetingMessage = 'The current User sub: ' + userInfo.sub;
}
} finally {
this.isLoading = false;
}
}
ngOnInit(): void {
this.updateGreetingMessage().catch((e) => {
console.error(e);
});
}
startLogin(): void {
authgear
.startAuthentication({
redirectURI: 'http://localhost:4000/auth-redirect',
prompt: 'login',
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
}
}
<h1>Home Page</h1>
<span *ngIf="isLoading">Loading</span>
<span *ngIf="greetingMessage">{{ greetingMessage }}</span>
<div *ngIf="!user.isLoggedIn">
<button type="button" (click)="startLogin()">Login</button>
</div><div *ngIf="user.isLoggedIn">
<button type="button" (click)="logout()">Logout</button>
</div>logout(): void {
authgear
.logout({
redirectURI: 'http://localhost:4000/',
})
.then(
() => {
this.greetingMessage = '';
},
(err) => {
console.error(err);
}
);
}<div *ngIf="user.isLoggedIn">
<button type="button" (click)="logout()">Logout</button>
<br />
<a target="_blank" rel="noreferrer" (click)="userSetting($event)" href="#">
User Setting
</a>
</div>import authgear, { Page } from "@authgear/web";
async userSetting(event: MouseEvent) {
event.preventDefault();
event.stopPropagation();
await authgear.open(Page.Settings);
}// src/app/home/home.component.ts
import { Component, OnInit } from '@angular/core';
import { UserService } from '../services/user.service';
import authgear, { Page } from '@authgear/web';
@Component({
selector: 'app-home',
templateUrl: './home.component.html',
styleUrls: ['./home.component.css'],
})
export class HomeComponent implements OnInit {
isLoading: boolean = false;
greetingMessage: string = '';
constructor(public user: UserService) {}
async updateGreetingMessage() {
this.isLoading = true;
try {
if (this.user.isLoggedIn) {
const userInfo = await authgear.fetchUserInfo();
this.greetingMessage = 'The current User sub: ' + userInfo.sub;
}
} finally {
this.isLoading = false;
}
}
ngOnInit(): void {
this.updateGreetingMessage().catch((e) => {
console.error(e);
});
}
startLogin(): void {
authgear
.startAuthentication({
redirectURI: 'http://localhost:4000/auth-redirect',
prompt: 'login',
})
.then(
() => {
// started authorization, user should be redirected to Authgear
},
(err) => {
// failed to start authorization
console.error(err);
}
);
}
logout(): void {
authgear
.logout({
redirectURI: 'http://localhost:4000/',
})
.then(
() => {
this.greetingMessage = '';
},
(err) => {
console.error(err);
}
);
}
async userSetting(event: MouseEvent) {
event.preventDefault();
event.stopPropagation();
await authgear.open(Page.Settings);
}
}<h1>Home Page</h1>
<span *ngIf="isLoading">Loading</span>
<span *ngIf="greetingMessage">{{ greetingMessage }}</span>
<div *ngIf="!user.isLoggedIn">
<button type="button" (click)="startLogin()">Login</button>
</div>
<div *ngIf="user.isLoggedIn">
<button type="button" (click)="logout()">Logout</button>
<br />
<a target="_blank" rel="noreferrer" (click)="userSetting($event)" href="#">
User Setting
</a>
</div>authgear
.fetch("YOUR_SERVER_URL")
.then(response => response.json())
.then(data => console.log(data));authgear
.refreshAccessTokenIfNeeded()
.then(() => {
// access token is ready to use
// accessToken can be string or undefined
// it will be empty if user is not logged in or session is invalid
const accessToken = authgear.accessToken;
// include Authorization header in your application request
const headers = {
Authorization: `Bearer ${accessToken}`
};
});


const biometricOptions = {
ios: {
localizedReason: 'Use biometric to authenticate',
constraint: 'biometryCurrentSet' as const,
},
android: {
title: 'Biometric Authentication',
subtitle: 'Biometric authentication',
description: 'Use biometric to authenticate',
negativeButtonText: 'Cancel',
constraint: ['BIOMETRIC_STRONG' as const],
invalidatedByBiometricEnrollment: true,
},
};
async function onClickPerformSensitiveOperation() {
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
await authgear.refreshIDToken();
// Step 2: Check if the end-user can be reauthenticated.
const canReauthenticate = authgear.canReauthenticate();
if (!canReauthenticate) {
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
const idTokenHint = authgear.getIDTokenHint();
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint so that
// the endpoint can know the end-user CANNOT be reauthenticated.
return callMySensitiveEndpoint(idTokenHint);
}
// Step 3: The end-user can be reauthenticated.
// If your app supports biometric authentication, you can pass
// the biometric options to reauthenticate.
// If biometric is enabled for the current user, it will be used instead.
await authgear.reauthenticate({
redirectURI: THE_REDIRECT_URI,
}, biometricOptions);
// Step 4: If we reach here, the reauthentication was done.
// The ID token have up-to-date auth_time claim.
const idTokenHint = authgear.getIDTokenHint();
return callMySensitiveEndpoint(idTokenHint);
}final ios = BiometricOptionsIOS(
localizedReason: "Use biometric to authenticate",
constraint: BiometricAccessConstraintIOS.biometryAny,
);
final android = BiometricOptionsAndroid(
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
constraint: [BiometricAccessConstraintAndroid.biometricStrong],
invalidatedByBiometricEnrollment: false,
);
Future<void> onClickPerformSensitiveOperation() async {
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
await authgear.refreshIDToken();
// Step 2: Check if the end-user can be reauthenticated.
final canReauthenticate = authgear.canReauthenticate;
if (!canReauthenticate) {
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
final idTokenHint = authgear.idTokenHint;
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint so that
// the endpoint can know the end-user CANNOT be reauthenticated.
return callMySensitiveEndpoint(idTokenHint);
}
// Step 3: The end-user can be reauthenticated.
// If your app supports biometric authentication, you can pass
// the biometric options to reauthenticate.
// If biometric is enabled for the current user, it will be used instead.
await authgear.reauthenticate(
redirectURI: THE_REDIRECT_URI,
biometricIOS: ios,
biometricAndroid: android,
);
// Step 4: If we reach here, the reauthentication was done.
// The ID token have up-to-date auth_time claim.
final idTokenHint = authgear.idTokenHint;
return callMySensitiveEndpoint(idTokenHint);
}var ios = new BiometricOptionsIos
{
LocalizedReason = "Use biometric to authenticate",
AccessConstraint = BiometricAccessConstraintIos.BiometricAny,
};
var android = new BiometricOptionsAndroid
{
Title = "Biometric Authentication",
Subtitle = "Biometric authentication",
Description = "Use biometric to authenticate",
NegativeButtonText = "Cancel",
AccessConstraint = BiometricAccessConstraintAndroid.BiometricOnly,
InvalidatedByBiometricEnrollment = false,
};
async void OnPerformSensitiveOperationClicked(object sender, EventArgs args)
{
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
await authgear.RefreshIdTokenAsync();
// Step 2: Check if the end-user can be reauthenticated.
var canReauthenticate = authgear.CanReauthenticate;
if (!canReauthenticate)
{
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
var idTokenHint = authgear.IdTokenHint;
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint so that
// the endpoint can know the end-user CANNOT be reauthenticated.
await CallMySensitiveEndpointAsync(idTokenHint);
return;
}
// Step 3: The end-user can be reauthenticated.
// If your app supports biometric authentication, you can pass
// the biometric options to reauthenticate.
// If biometric is enabled for the current user, it will be used instead.
await authgear.ReauthenticateAsync(new ReauthenticateOptions
{
RedirectURI: THE_REDIRECT_URI,
}, new BiometricOptions
{
Ios = ios,
Android = android,
});
// Step 4: If we reach here, the reauthentication was done.
// The ID token have up-to-date auth_time claim.
var idTokenHint = authgear.IdTokenHint;
await CallMySensitiveEndpointAsync(idTokenHint);
}async function onClickPerformSensitiveOperation() {
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
await authgear.refreshIDToken();
// Step 2: Check if the end-user can be reauthenticated.
const canReauthenticate = authgear.canReauthenticate();
if (!canReauthenticate) {
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
const idTokenHint = authgear.getIDTokenHint();
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint so that
// the endpoint can know the end-user CANNOT be reauthenticated.
return callMySensitiveEndpoint(idTokenHint);
}
// Step 3: The end-user can be reauthenticated.
// The end-user will be redirected to Authgear.
// When the reauthentication finishes,
// The end-user will be redirected back to the given redirect URI.
await authgear.startReauthentication({
redirectURI: THE_REDIRECT_URI
});
}
// Suppose the following function is run when the end-user is redirected to
// the redirect URI
async function onRedirectAfterReauthentication() {
// You HAVE to configure authgear again
// because your website have been visited freshly.
await authgear.finishReauthentication();
await authgear.refreshIDToken();
const idTokenHint = authgear.getIDTokenHint();
return callMySensitiveEndpoint(idTokenHint);
}func onClickPerformSensitiveOperation() {
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
authgear.refreshIDToken() { result in
switch result {
case .success:
// Step 2: Check if the end-user can be reauthenticated.
let canReauthenticate = authgear.canReauthenticate
if !canReauthenticate {
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
let idTokenHint = authgear.idTokenHint
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint
// so that the endpoint can know the end-user CANNOT
// be reauthenticated.
callMySensitiveEndpoint(idTokenHint)
return
}
// Step 3: The end-user can be reauthenticated.
// By default biometric is used for reauthentication if it is enabled for the current user.
// If you do not want biometric to be used, specify skipUsingBiometric: true
authgear.reauthenticate(redirectURI: THE_REDIRECT_URI, skipUsingBiometric: false) { result in
switch result {
case .success:
// Step 4: If we reach here, the reauthentication was done.
// The ID token have up-to-date auth_time claim.
let idTokenHint = authgear.idTokenHint
callMySensitiveEndpoint(idTokenHint)
return
case let .failure(error):
// Handle the error
}
}
case let .failure(error):
// Handle the error
}
}
}public void onClickPerformSensitiveOperation() {
BiometricOptions biometricOptions = new BiometricOptions(
activity, // FragmentActivity
"Biometric authentication", // title
"Biometric authentication", // subtitle
"Use biometric to authenticate", // description
"Cancel", // negativeButtonText
ALLOWED, // allowedAuthenticators
true // invalidatedByBiometricEnrollment
);
// Step 1: Refresh the ID token to ensure the claims are up-to-date.
authgear.refreshIDToken(new OnRefreshIDTokenListener() {
@Override
public void onFailed(Throwable throwable) {
// Handle error
}
@Override
public void onFinished() {
// Step 2: Check if the end-user can be reauthenticated.
boolean canReauthenticate = authgear.getCanReauthenticate();
if (!canReauthenticate) {
// Step 2.1: Depending on your business need, you may want to allow
// the end-user to proceed.
// Here we assume you want to proceed.
String idTokenHint = authgear.getIDTokenHint();
// Step 2.2: Call the sensitive endpoint with the ID token.
// It is still required to pass the ID token to the endpoint
// so that the endpoint can know the end-user CANNOT
// be reauthenticated.
callMySensitiveEndpoint(idTokenHint);
return;
}
// Step 3: The end-user can be reauthenticated.
// If your app supports biometric authentication, you can pass
// the biometric options to reauthenticate.
// If biometric is enabled for the current user, it will be used.
ReauthenticateOptions options =
new ReauthenticateOptions(THE_REDIRECT_URI);
authgear.reauthenticate(options, biometricOptions, new OnReauthenticateListener() {
@Override
public void onFailed(Throwable throwable) {
// Handle error
}
@Override
public void onFinished(UserInfo userInfo) {
// Step 4: If we reach here, the reauthentication was done.
// The ID token have up-to-date auth_time claim.
String idTokenHint = authgear.getIDTokenHint();
callMySensitiveEndpoint(idTokenHint);
return;
}
});
}
});
}async function onClickPerformSensitiveOperation() {
await authgear.refreshIDToken();
// Before you trigger reauthentication, check authTime first.
const authTime = authgear.getAuthTime();
if (authTime != null) {
const now = new Date();
const timeDelta = now.getTime() - authTime.getTime();
if (timeDelta < 5 * 60 * 1000 /* 5 minutes */) {
const idTokenHint = authgear.getIDTokenHint();
return callMySensitiveEndpoint(idTokenHint);
}
}
// Otherwise trigger authentication.
}func onClickPerformSensitiveOperation() {
authgear.refreshIDToken() { result in
switch result {
case .success:
// Before you trigger reauthentication, check authTime first.
if let authTime = authgear.authTime {
let now = Date()
let timeDelta = now.timeIntervalSince(authTime)
if timeDelta < 5 * 60 {
let idTokenHint = authgear.idTokenHint
callMySensitiveEndpoint(idTokenHint)
return
}
}
// Otherwise trigger authentication.
case let .failure(error):
// Handle the error
}
}
}public void onClickPerformSensitiveOperation() {
authgear.refreshIDToken(new OnRefreshIDTokenListener() {
@Override
public void onFailed(Throwable throwable) {
// Handle error
}
@Override
public void onFinished() {
// Before you trigger reauthentication, check authTime first.
Date authTime = authgear.getAuthTime();
if (authTime != null) {
Date now = new Date();
long timedelta = now.getTime() - authTime.getTime();
if (timedelta < 5 * 60 * 1000) {
String idTokenHint = authgear.getIDTokenHint();
callMySensitiveEndpoint(idTokenHint);
return;
}
}
// Otherwise trigger authentication.
}
});
}public async void OnPerformSensitiveOperationClicked(object sender, EventArgs args)
{
await authgear.RefreshIdTokenAsync();
var authTime = authgear.AuthTime;
if (authTime != null)
{
var now = DateTimeOffset.UtcNow;
var timedelta = now - authTime.Value;
if (timedelta < TimeSpan.FromMinutes(5))
{
var idTokenHint = authgear.IdTokenHint;
callMySensitiveEndpoint(idTokenHint);
return;
}
}
}import json
from contextlib import closing
from urllib.request import urlopen
from datetime import datetime, timezone, timedelta
import jwt
from jwt import PyJWKClient
base_address = "https://<your_app_endpoint>"
def fetch_jwks_uri(base_address):
doc_url = base_address + "/.well-known/openid-configuration"
with closing(urlopen(doc_url)) as f:
doc = json.load(f)
jwks_uri = doc["jwks_uri"]
if not jwks_uri:
raise Exception('Failed to fetch jwks uri.')
return jwks_uri
def my_endpoint():
id_token = GET_ID_TOKEN_FROM_HTTP_REQUEST_SOMEHOW()
try:
jwks_uri = fetch_jwks_uri(base_address)
# Reuse PyJWKClient for better performance
jwks_client = PyJWKClient(jwks_uri)
signing_key = jwks_client.get_signing_key_from_jwt(id_token)
claims = jwt.decode(
id_token,
signing_key.key,
algorithms=["RS256"],
audience=base_address,
options={"verify_exp": True},
)
auth_time = claims["auth_time"]
dt = datetime.fromtimestamp(auth_time)
now = datetime.utcnow()
delta = now - dt
if delta > timedelta(minutes=5):
raise ValueError("auth_time is not recent enough")
except:
# Handle error
raisepackage main
import (
"context"
"encoding/json"
"fmt"
"net/http"
"time"
"github.com/lestrrat-go/jwx/jwk"
"github.com/lestrrat-go/jwx/jwt"
)
var (
baseAddress = "https://<your_app_endpoint>"
)
type OIDCDiscoveryDocument struct {
JWKSURI string `json:"jwks_uri"`
}
func FetchOIDCDiscoveryDocument(endpoint string) (*OIDCDiscoveryDocument, error) {
resp, err := http.DefaultClient.Get(endpoint)
if err != nil {
return nil, err
}
defer resp.Body.Close()
if resp.StatusCode != http.StatusOK {
return nil, fmt.Errorf(
"failed to fetch discovery document: unexpected status code: %d",
resp.StatusCode,
)
}
var document OIDCDiscoveryDocument
err = json.NewDecoder(resp.Body).Decode(&document)
if err != nil {
return nil, err
}
return &document, nil
}
func FetchJWK(baseAddress string) (jwk.Set, error) {
doc, err := FetchOIDCDiscoveryDocument(
baseAddress + "/.well-known/openid-configuration",
)
if err != nil {
return nil, err
}
set, err := jwk.Fetch(context.Background(), doc.JWKSURI)
return set, err
}
func CheckIDToken(idToken string) error {
// fetch jwks_uri from Authgear
// you can cache the value of jwks to have better performance
set, err := FetchJWK(baseAddress)
if err != nil {
return fmt.Errorf("failed to fetch JWK: %s", err)
}
// parse jwt token
token, err := jwt.ParseString(idToken, jwt.WithKeySet(set))
if err != nil {
return fmt.Errorf("invalid token: %s", err)
}
// validate jwt token
err = jwt.Validate(token,
jwt.WithClock(jwt.ClockFunc(
func() time.Time { return time.Now().UTC() },
)),
jwt.WithIssuer(baseAddress),
)
if err != nil {
return fmt.Errorf("invalid token: %s", err)
}
authTimeAny, ok := token.Get("auth_time")
if !ok {
return fmt.Errorf("no auth_time")
}
authTimeUnix, ok := authTimeAny.(float64)
if !ok {
return fmt.Errorf("auth_time is not number")
}
authTime := time.Unix(int64(authTimeUnix), 0)
now := time.Now().UTC()
diff := now.Sub(authTime)
if diff > 5*time.Minute {
return fmt.Errorf("auth_time is not recent enough")
}
return nil
}

Register a .
Register a Mobile Application (移动应用).
For iOS, the Associated Domains and Universal Links supports are required in your app. See from Apple for details.
For Android, the MD5 fingerprint of the signing keystore is required
See for more details.
WeChat login is incompatible with Passkey
Login with WeChat requires the use of WebKitWebViewUIImplementation which does not support the use of Passkey APIs. At the moment, either passkey or WeChat login can be enabled in your mobile applications.
Once your mobile app is approved on the platform, you will see the word "✅已通过" in the app details page.
Get the appid (Client ID).
Get the appsecret (Client Secret). It will only be shown once. You need to re-generate if you lose it.
Get the 原始ID (Account ID) of your WeChat Open Platform account.
Sign in to the Authgear portal.
Select your project.
In the navigation menu, go to Authentication > Social / Enterprise Login.
Click Add Connection.
To integrate the WeChat SDK into your iOS app, you have to read .
This section reminds you some of the important points that you may miss in the official integration guide.
The latest version can be found at As of the time of writing, the latest version is 2.0.4.
appid in Info.plistIn case you have other schemes, you need to make sure the WeChat ones are the first 50 items.
OTHER_LDFLAGS contains -ObjCThe WeChat SDK for iOS depends on the Objective-C runtime. Therefore, your app has to link to the Objective-C runtime. To do so, you need to make sure OTHER_LDFLAGS contains -ObjC.
The -ObjC flag is so special in CocoaPods that you CANNOT add it with CocoaPods hook.
If your iOS app is written in , the app is likely to have OTHER_LDFLAGS including -ObjC already, as React Native depend on the Objective-C runtime.
In other case, you need to manually edit your Build Settings to include the -ObjC flag.
In your AppDelegate.swift
In your SceneDelegate (if you have one)
In your AppDelegate.h
In your AppDelegate.m
In your SceneDelegate.m (if you have one)
To integrate the WeChat SDK into your Android app, you have to read .
This section reminds you some of the important points that you may miss in the official integration guide.
The latest version can be found at As of the time of writing, the latest version is 6.8.34.
<queries> in your AndroidManifest.xmlYou need to declare in your AndroidManifest.xml that your app is supposed to query the existence of the WeChat app at runtime.
Add this to your AndroidManifest.xml.
AndroidManifest.xmlThe WeChat SDK opens the Activity PACKAGE_NAME.wxapi.WXEntryActivity. You need to implement that Activity and declare it in your AndroidManifest.xml.
The full Java name of the Activity must be PACKAGE_NAME.wxapi.WXEntryActivity. If the package name you tell WeChat Open Platform is com.myapp, then the full Java name of the Activity must be com.myapp.wxapi.WXEntryActivity.
Here is an example implementation that is based on BroadcastReceiver:
On WeChat Open Platform, you need to tell it the MD5 fingerprint of the keystore you use to sign your Android app.
If you use Google Play Console to distribute your Android app, it is likely that you are using . With Play App Signing, you tell Google the fingerprint of the keystore you originally sign your app. Google removes the signature and uses its managed keystore to sign the app before distributing the app to Play Store. The final app running on the device of course bears the signature of the managed keystore. This is also the signature the WeChat SDK sees when it validates the signature.
To get the MD5 fingerprint of the managed keystore, refer to the following screenshot:
Note that the MD5 fingerprint you see on Google Play Console is a colon-delimited uppercase hex string, while WeChat Open Platform expects you to provide a plain lowercase hex string.
For example, suppose the MD5 fingerprint you get from Google Play Console is D4:1D:8C:D9:8F:00:B2:04:E9:80:09:98:EC:F8:42:7E, you can use the following shell command to do the conversion.
The output d41d8cd98f00b204e9800998ecf8427e is in the expected WeChat Open Platform format.
For those of you who produce the final signature of your app using your own keystore, you can use the following shell command to output the MD5 fingerprint.
Where
STORE_FILE is an environment variable pointing to the keystore file on your machine, for example, ./mykeystore.jks.
STORE_PASSWORD is an environment variable containing the password of the keystore.
KEY_ALIAS is an environment variable indicating which key in the keystore to use.
You have 2 actions to take:
Switch to WebKitWebViewUIImplementation when you initialize the Authgear SDK.
Implement the callback / delegate of WebKitWebViewUIImplementation.
WebKitWebViewUIImplementationWebKitWebViewUIImplementationIn your AppDelegate.swift
In your MainActivity.java
In your React Native TypeScript code
In your iOS Native Module MyWeChatModule.h
In your iOS Native Module MyWeChatModule.m
In your WXApiDelegate
Prerequisite: A WeChat account is required for registering the app.
These information are required for creating the application on the platform, prepare them before creating the application:
Bundle ID
测试 Bundle (Testing Bundle ID)
Universal Links
备用 Universal Links (Backup Universal Links)
应用包名 (Package name)
应用签名 (App Signature)
Select WeChat Mobile / 移动应用.
Fill in Client ID with the appid.
Fill in Client Secret with the appsecret.
Fill in Account ID with the 原始ID.
Add a WeChat Redirect URI. This is typically a custom URI with the scheme being your iOS bundle identifier or your Android package name. For example, com.myapp://authgear/open_wechat_app.
Save.
On iOS, you implement WXApiDelegate on your AppDelegate.
On Android, your WXEntryActivity sends a broadcast with state being the Intent action.
MyWeChatModuleIn your Flutter code
In your AppDelegate.swift
In your MainActivity.kt
应用官网
Official website of the mobile app
The webpage should show the description of the app and offer links to download it on app stores
移动应用图片
App Icon
A 28x28 and a 108x108 icon
应用市场
Is the app released on any app stores for Chinese users?
Choose between: - Unreleased: the login is rate limited to 100 per day - Released: A Chinese ICP license is required (App备案号), for example: 粤B2-00000000-0000A
应用类目
App category
Choose from the list of categories defined by the platform that best describe your app
应用运行流程图
Images of app flow
Any flowchart or screenshots showing how the app works
申请/修改应用说明
Application details
Reasons for application, any testing account and testing instruction.
管理员身份设置
Set Admin
Scan the QR code from the WeChat mobile app to prove the admin identity of the app.
移动应用名称
Mobile app name
The app name shown to the end-user when they login
英文名称
Mobile app name in English
The app name shown to an English end-user when they login
移动应用简介
Mobile app description
A description for the approver to understand the app
英文简介
Mobile app description in English




Optional field
import 'package:flutter/services.dart';
import 'package:flutter_authgear/flutter_authgear.dart';
// authgear is assumed to be initialised somewhere else.
var authgear;
const _nativeMethodChannel = MethodChannel("MyWeChatMethodChannel");
// This is the callback you pass to WebKitWebViewUIImplementation.
Future<void> sendWechatAuthRequest(String state) async {
try {
final code = await _nativeMethodChannel.invokeMethod("sendWechatAuthRequest", {
"state": state,
});
await authgear.wechatAuthCallback(state: state, code: code);
} on PlatformException catch (e) {
print("exception: $e");
}
}import Flutter
@main
@objc class AppDelegate: FlutterAppDelegate, WXApiDelegate {
private var wechat = [String: FlutterResult]()
override func application(
_ application: UIApplication,
didFinishLaunchingWithOptions launchOptions: [UIApplication.LaunchOptionsKey: Any]?
) -> Bool {
let controller = window?.rootViewController as! FlutterViewController
let channel = FlutterMethodChannel(name: "MyWeChatMethodChannel", binaryMessenger: controller.binaryMessenger)
channel.setMethodCallHandler {
(call: FlutterMethodCall, result: @escaping FlutterResult) -> Void in
let arguments = call.arguments as! Dictionary<String, AnyObject>
let state = arguments["state"] as! String
self.wechat[state] = result
let req = SendAuthReq()
req.scope = "snsapi_userinfo"
req.state = state
WXApi.send(req)
}
GeneratedPluginRegistrant.register(with: self)
return super.application(application, didFinishLaunchingWithOptions: launchOptions)
}
override func application(_ app: UIApplication, open url: URL, options: [UIApplication.OpenURLOptionsKey : Any] = [:]) -> Bool {
WXApi.handleOpen(url, delegate: self)
return super.application(app, open: url, options: options)
}
override func application(_ application: UIApplication, open url: URL, sourceApplication: String?, annotation: Any) -> Bool {
WXApi.handleOpen(url, delegate: self)
return super.application(application, open: url, sourceApplication: sourceApplication, annotation: annotation)
}
override func application(_ application: UIApplication, continue userActivity: NSUserActivity, restorationHandler: @escaping ([UIUserActivityRestoring]?) -> Void) -> Bool {
WXApi.handleOpenUniversalLink(userActivity, delegate: self)
return super.application(application, continue: userActivity, restorationHandler: restorationHandler)
}
@objc
func onReq(_ req: BaseReq) {
}
@objc
func onResp(_ resp: BaseResp) {
guard let authResp = resp as? SendAuthResp else {
return
}
guard let state = authResp.state else {
return
}
guard let result = wechat.removeValue(forKey: state) else {
return
}
var error: String
switch WXErrCode(rawValue: authResp.errCode) {
case WXErrCodeUserCancel:
error = "errcode_cancel"
case WXErrCodeAuthDeny:
error = "errcode_deny"
case WXErrCodeUnsupport:
error = "errcode_unsupported"
default:
error = "errcode_unknown"
}
switch WXErrCode(rawValue: authResp.errCode) {
case WXSuccess:
let code = authResp.code
result(code)
default:
result(FlutterError(code: error, message: error, details: nil))
}
}
}class MainActivity: FlutterFragmentActivity() {
private var api: IWXAPI? = null
override fun configureFlutterEngine(flutterEngine: FlutterEngine) {
super.configureFlutterEngine(flutterEngine)
MethodChannel(flutterEngine.dartExecutor.binaryMessenger, "MyWeChatMethodChannel").setMethodCallHandler { call, result ->
handleMethodCall(call, result)
}
}
private fun handleMethodCall(call: MethodCall, result: MethodChannel.Result) {
val api = api!!
if (!api.isWXAppInstalled) {
result.error("errcode_not_installed", "errcode_not_installed", null)
return
}
val state = call.argument<String>("state")!!
val req = SendAuth.Req()
req.scope = "snsapi_userinfo"
req.state = state
var broadcastReceiver: BroadcastReceiver?
broadcastReceiver = object : BroadcastReceiver() {
override fun onReceive(context: Context?, intent: Intent?) {
val state_ = intent.getStringExtra("state")
if (state_ == state) {
[email protected](broadcastReceiver)
val code = intent.getStringExtra("code")
val error = intent.getStringExtra("error")
if (code != null) {
result.success(code)
} else {
result.error(error, error, nil)
}
}
}
}
val intentFilter = IntentFilter(state)
ContextCompat.registerReceiver(this.applicationContext, broadcastReceiver, intentFilter, ContextCompat.RECEIVER_NOT_EXPORTED)
api.sendReq(req)
}
}pod "WechatOpenSDK-XCFramework", "~> 2.0.4" <key>CFBundleURLTypes</key>
<array>
<dict>
<key>CFBundleTypeRole</key>
<string>Editor</string>
<key>CFBundleURLName</key>
<string>weixin</string>
<key>CFBundleURLSchemes</key>
<array>
<string>wxYOUR_WECHAT_APPID</string>
</array>
</dict>
</array> <key>LSApplicationQueriesSchemes</key>
<array>
<string>weixin</string>
<string>weixinULAPI</string>
<string>weixinURLParamsAPI</string>
</array>@UIApplicationMain
class AppDelegate: UIResponder, UIApplicationDelegate, WXApiDelegate {
func application(_ application: UIApplication, didFinishLaunchingWithOptions launchOptions: [UIApplication.LaunchOptionsKey: Any]?) -> Bool {
// Insert this line to register your WeChat mobile application.
WXApi.registerApp("wxYOUR_WECHAT_APPID", universalLink: "https://myapp.com/wechat/")
return true
}
func application(_ app: UIApplication, open url: URL, options: [UIApplication.OpenURLOptionsKey : Any] = [:]) -> Bool {
// Forward the URL to the WeChat SDK.
// If the URL is about WeChat integration, onResp will be called.
WXApi.handleOpen(url, delegate: self)
return true
}
func application(_ application: UIApplication, open url: URL, sourceApplication: String?, annotation: Any) -> Bool {
// Forward the URL to the WeChat SDK.
// If the URL is about WeChat integration, onResp will be called.
WXApi.handleOpen(url, delegate: self)
return true
}
func application(_ application: UIApplication, continue userActivity: NSUserActivity, restorationHandler: @escaping ([UIUserActivityRestoring]?) -> Void) -> Bool {
// Forward the NSUserActivity to the WeChat SDK.
// If the NSUserActivity is about WeChat integration, onResp will be called.
WXApi.handleOpenUniversalLink(userActivity, delegate: self)
return true
}
// Implements WXApiDelegate.
// You need not do any thing special in this method.
func onReq(_ req: BaseReq) {}
// The WeChat SDK will call this method if the forwarded callbacks are about WeChat.
func onResp(_ resp: BaseResp) {
guard let authResp = resp as? SendAuthResp else {
return
}
let errCode = WXErrCode(rawValue: authResp.errCode)
if errCode == WXSuccess {
let state = authResp.state
let code = authResp.code
// Forward code to Authgear SDK.
} else {
// Handle the error returned by the WeChat SDK properly to deliver good user experience.
}
}
}class SceneDelegate: UIResponder, UIWindowSceneDelegate {
func scene(_ scene: UIScene, continue userActivity: NSUserActivity) {
// Assume your AppDelegate is the single point of handling WeChat callback,
// you need to get it back.
let appDelegate = UIApplication.shared.delegate as? AppDelegate
// Forward the NSUserActivity to the WeChat SDK.
// If the NSUserActivity is about WeChat integration, onResp on AppDelegate will be called.
WXApi.handleOpenUniversalLink(userActivity, delegate: appDelegate)
}
}// Import the WeChat SDK header file.
#import <WXApi.h>
// Declare your AppDelegate to be a WXApiDelegate.
@interface AppDelegate : UIResponder<UIApplicationDelegate, WXApiDelegate>
@end@implementation AppDelegate
- (BOOL)application:(UIApplication *)application didFinishLaunchingWithOptions:(NSDictionary *)launchOptions
{
// Insert this line to register your WeChat mobile application.
[WXApi registerApp:@"wxYOUR_WECHAT_APPID" universalLink:@"https://myapp.com/wechat/"];
return true;
}
- (BOOL)application:(UIApplication *)application handleOpenURL:(NSURL *)url {
// Forward the URL to the WeChat SDK.
// If the URL is about WeChat integration, onResp will be called.
[WXApi handleOpenURL:url delegate:self];
return true;
}
- (BOOL)application:(UIApplication *)application openURL:(NSURL *)url sourceApplication:(NSString *)sourceApplication annotation:(id)annotation {
// Forward the URL to the WeChat SDK.
// If the URL is about WeChat integration, onResp will be called.
[WXApi handleOpenURL:url delegate:self];
return true;
}
- (BOOL)application:(UIApplication *)application continueUserActivity:(NSUserActivity *)userActivity restorationHandler:(void(^)(NSArray<id<UIUserActivityRestoring>> * __nullable restorableObjects))restorationHandler {
// Forward the NSUserActivity to the WeChat SDK.
// If the NSUserActivity is about WeChat integration, onResp will be called.
[WXApi handleOpenUniversalLink:userActivity delegate:self];
return true;
}
// Implements WXApiDelegate.
// You need not do any thing special in this method.
-(void) onReq:(BaseReq*)req
{
}
// The WeChat SDK will call this method if the forwarded callbacks are about WeChat.
-(void) onResp:(BaseResp*)resp
{
if([resp isKindOfClass:[SendAuthResp class]]) {
SendAuthResp *sendAuthResp = (SendAuthResp*)resp;
if (sendAuthResp.errCode == WXSuccess) {
NSString *state = sendAuthResp.state;
NSString *code = sendAuthResp.code;
// Forward code to Authgear SDK.
} else {
// Handle the error returned by the WeChat SDK properly to deliver good user experience.
}
}
}
@end@implementation SceneDelegate
- (void)scene:(UIScene *)scene continueUserActivity:(NSUserActivity *)userActivity {
// Assume your AppDelegate is the single point of handling WeChat callback,
// you need to get it back.
AppDelegate *appDelegate = (AppDelegate *)[[UIApplication sharedApplication] delegate];
// Forward the NSUserActivity to the WeChat SDK.
// If the NSUserActivity is about WeChat integration, onResp on AppDelegate will be called.
[WXApi handleOpenUniversalLink:userActivity delegate:appDelegate];
}
@endimplementation "com.tencent.mm.opensdk:wechat-sdk-android:6.8.34" <queries>
<package android:name="com.tencent.mm" />
</queries> <activity
<!-- android:name MUST match the package name you tell WeChat Open Platform -->
android:name="com.myapp.wxapi.WXEntryActivity"
<!-- It must be exported, otherwise the WeChat app will not be able to open it -->
android:exported="true"
<!-- The official guide says it should be singleTask -->
android:launchMode="singleTask"
<!-- android:taskAffinity MUST match the package name you tell WeChat Open Platform -->
android:taskAffinity="com.myapp"
android:theme="@android:style/Theme.Translucent.NoTitleBar">
</activity>import com.tencent.mm.opensdk.constants.ConstantsAPI;
import com.tencent.mm.opensdk.modelbase.BaseReq;
import com.tencent.mm.opensdk.modelbase.BaseResp;
import com.tencent.mm.opensdk.modelmsg.SendAuth;
import com.tencent.mm.opensdk.openapi.IWXAPI;
import com.tencent.mm.opensdk.openapi.IWXAPIEventHandler;
import com.tencent.mm.opensdk.openapi.WXAPIFactory;
public class WXEntryActivity extends Activity implements IWXAPIEventHandler {
private IWXAPI api;
@Override
public void onCreate(Bundle savedInstanceState) {
super.onCreate(savedInstanceState);
api = WXAPIFactory.createWXAPI(this, "wxYOUR_WECHAT_APPID", true);
api.registerApp("wxYOUR_WECHAT_APPID");
try {
Intent intent = getIntent();
api.handleIntent(intent, this);
} catch (Exception e) {
e.printStackTrace();
}
}
@Override
protected void onNewIntent(Intent intent) {
super.onNewIntent(intent);
setIntent(intent);
api.handleIntent(intent, this);
}
@Override
public void onReq(BaseReq req) {
}
@Override
public void onResp(BaseResp resp) {
String error = null;
switch (resp.errCode) {
case BaseResp.ErrCode.ERR_OK:
break;
case BaseResp.ErrCode.ERR_USER_CANCEL:
error = "errcode_cancel";
break;
case BaseResp.ErrCode.ERR_AUTH_DENIED:
error = "errcode_deny";
break;
case BaseResp.ErrCode.ERR_UNSUPPORT:
error = "errcode_unsupported";
break;
default:
error = "errcode_unknown";
break;
}
if (resp.getType() == ConstantsAPI.COMMAND_SENDAUTH) {
SendAuth.Resp authResp = (SendAuth.Resp)resp;
String state = authResp.state;
Intent intent = new Intent(state);
intent.putExtra("state", state);
intent.setPackage(this.getApplicationContext().getPackageName());
if (error != null) {
intent.putExtra("error", error);
} else {
intent.putExtra("code", authResp.code);
}
this.getApplicationContext().sendBroadcast(intent);
}
finish();
}
}$ echo "D4:1D:8C:D9:8F:00:B2:04:E9:80:09:98:EC:F8:42:7E" | sed 's/://g' | tr 'A-Z' 'a-z'
d41d8cd98f00b204e9800998ecf8427ekeytool -exportcert -keystore "$STORE_FILE" -storepass "$STORE_PASSWORD" -alias "$KEY_ALIAS" -rfc | openssl x509 -noout -fingerprint -md5import Authgear
let uiImplementation = WKWebViewUIImplementation()
// Put the WeChat redirect URI you added in the Authgear portal here.
uiImplementation.wechatRedirectURI = URL(string: "com.myapp://authgear/open_wechat_app")!
// You need to implement the delegate to bridge between the WeChat SDK and the Authgear SDK.
uiImplementation.authgearDelegate = self
self.authgear = Authgear(
clientId: "AUTHGEAR_CLIENT_ID",
endpoint: "https://myapp.authgear.cloud",
uiImplementation: uiImplementation
)WebKitWebViewUIImplementation impl = new WebKitWebViewUIImplementation();
impl.setWechatRedirectURI(Uri.parse("com.myapp://authgear/open_wechat_app"));
impl.setAuthgearDelegate(this);
boolean isSsoEnabled = false;
boolean isPreAuthenticatedURLEnabled = false;
this.mAuthgear = new Authgear(
this.getApplicationContext(),
"AUTHGEAR_CLIENT_ID",
"https://myapp.authgear.cloud",
new TransientTokenStorage(),
impl,
isSsoEnabled,
isPreAuthenticatedURLEnabled,
null,
null
);import authgear, {
WebKitWebViewUIImplementation,
} from '@authgear/react-native';
authgear.configure({
clientID: "AUTHGEAR_CLIENT_ID",
endpoint: "https://myapp.authgear.cloud",
uiImplementation: new WebKitWebViewUIImplementation({
ios: {
wechatRedirectURI: "com.myapp://authgear/open_wechat_app",
},
android: {
wechatRedirectURI: "com.myapp://authgear/open_wechat_app",
},
// You need to implement this callback to bridge between the WeChat SDK and the Authgear SDK.
sendWechatAuthRequest,
}),
})import 'package:flutter_authgear/flutter_authgear.dart';
var authgear = Authgear(
clientID: "AUTHGEAR_CLIENT_ID",
endpoint: "https://myapp.authgear.cloud",
uiImplementation: WebKitWebViewUIImplementation(
options: WebKitWebViewUIImplementationOptions(
ios: WebKitWebViewUIImplementationOptionsIOS(
wechatRedirectURI: "com.myapp://authgear/open_wechat_app",
),
android: WebKitWebViewUIImplementationOptionsAndroid(
wechatRedirectURI: "com.myapp://authgear/open_wechat_app",
),
// You need to implement this callback to bridge between the WeChat SDK and the Authgear SDK.
sendWechatAuthRequest: sendWechatAuthRequest,
),
),
)import Authgear
@UIApplicationMain
class AppDelegate: UIResponder, UIApplicationDelegate, WXApiDelegate, AuthgearDelegate {
// authgear is assumed to be initialised somewhere else.
var authgear: Authgear!
// Implements AuthgearDelegate
func sendWechatAuthRequest(_ state: String) {
// Open WeChat using the WeChat SDK.
let req = SendAuthReq()
req.scope = "snsapi_userinfo"
req.state = state
WXApi.send(req)
}
// Implements WXApiDelegate
func onResp(_ resp: BaseResp) {
guard let authResp = resp as? SendAuthResp else {
return
}
let errCode = WXErrCode(rawValue: authResp.errCode)
if errCode == WXSuccess {
let state = authResp.state
let code = authResp.code
// Forward code to Authgear SDK.
self.authgear?.wechatAuthCallback(code: code, state: state) { result in
switch result {
case .success():
// The code was sent to Authgear successfully.
// The end-user will proceed the login in the WebView.
// You do not need to do anything here.
break
case let .failure(error):
// Handle the error returned by the Authgear SDK properly to deliver good user experience.
}
}
} else {
// Handle the error returned by the WeChat SDK properly to deliver good user experience.
}
}
}public class MainActivity extends AppCompatActivity implements AuthgearDelegate {
private IWXAPI mWeChatAPI;
// mAuthgear is assumed to be initialised somewhere else.
private Authgear mAuthgear;
@Override
public void sendWechatAuthRequest(String state) {
if (!this.mWeChatAPI.isWXAppInstalled()) {
// Handle WeChat not installed.
return;
}
Context ctx = this.getApplicationContext();
IntentFilter intentFilter = new IntentFilter(state);
BroadcastReceiver br;
br = new BroadcastReceiver() {
@Override
public void onReceive(Context context, Intent intent) {
String state_ = intent.getStringExtra("state");
if (state_ != null && state_.equal(state)) {
ctx.unregisterReceiver(br);
String code = intent.getStringExtra("code");
String error = intent.getStringExtra("error");
if (code != null) {
mAuthgear.wechatAuthCallback(code, state, new OnWechatAuthCallbackListener() {
@Override
public void onWechatAuthCallback() {
// No need to do anything here.
}
@Override
public void onWechatAuthCallbackFailed(Throwable throwable) {
// Handle error.
}
});
} else {
// Handle error.
}
}
}
}
ContextCompat.registerReceiver(ctx, br, intentFilter, ContextCompat.RECEIVER_NOT_EXPORTED);
SendAuth.Req req = new SendAuth.Req();
req.scope = "snsapi_userinfo";
req.state = state;
this.mWeChatAPI.sendReq(req);
}
}import {
NativeModules,
} from "react-native";
import authgear from '@authgear/react-native';
// This is the callback you pass to WebKitWebViewUIImplementation.
async function sendWechatAuthRequest(state: string) {
// MyWeChatModule is the Native Module you need to implement yourselves to bridge
// between the WeChat SDK and the Authgear SDK.
const { code } = await NativeModules.MyWeChatModule.sendWechatAuthRequest(state);
await authgear.wechatAuthCallback(code, state);
}#import <React/RCTBridgeModule.h>
static NSString *const kMyWeChatModuleNotification = @"MyWeChatModuleNotification";
@interface MyWeChatModule : NSObject <RCTBridgeModule>
@end#import "MyWeChatModule.h"
#import <React/RCTUtils.h>
#import <WXApi.h>
@interface MyWeChatModule()
@property (nonatomic, strong) RCTPromiseResolveBlock sendWechatAuthResolve;
@property (nonatomic, strong) RCTPromiseRejectBlock sendWechatAuthReject;
@end
@implementation MyWeChatModule
RCT_EXPORT_MODULE(MyWeChatModule);
- (instancetype)init
{
if ((self = [super init])) {
// Listen to the notification posted by your WXApiDelegate.
[[NSNotificationCenter defaultCenter] addObserver:self
selector:@selector(handleWechatAuthResult:)
name:kMyWeChatModuleNotification
object:nil];
}
return self;
}
RCT_EXPORT_METHOD(sendWechatAuthRequest:(NSString *)state
resolve:(RCTPromiseResolveBlock)resolve
reject:(RCTPromiseRejectBlock)reject)
{
self.sendWechatAuthResolve = resolve;
self.sendWechatAuthReject = reject;
dispatch_async(dispatch_get_main_queue(), ^{
SendAuthReq* req = [[SendAuthReq alloc] init];
req.scope = @"snsapi_userinfo";
req.state = state;
[WXApi sendReq:req completion:nil];
});
}
- (void)handleWechatAuthResult:(NSNotification *)notification
{
if (notification.userInfo[@"code"]) {
self.sendWechatAuthResolve(notification.userInfo);
} else {
NSString *error = notification.userInfo[@"error"];
self.sendWechatAuthReject(RCTErrorUnspecified, error, error);
}
[self cleanup];
}
- (void)cleanup
{
self.sendWechatAuthResolve = nil;
self.sendWechatAuthReject = nil;
}
@end-(void) onResp:(BaseResp*)resp
{
if ([resp isKindOfClass:[SendAuthResp class]]) {
SendAuthResp *sendAuthResp = (SendAuthResp*)resp;
NSDictionary<NSString *, id> *payload;
if (sendAuthResp.errCode == WXSuccess) {
payload = @{
@"code": sendAuthResp.code,
@"state": sendAuthResp.state,
};
} else {
NSString *error;
switch (resp.errCode) {
case WXErrCodeUserCancel:
error = @"errcode_cancel";
break;
case WXErrCodeAuthDeny:
error = @"errcode_deny";
break;
case WXErrCodeUnsupport:
error = @"errcode_unsupported";
break;
default:
error = @"errcode_unknown";
break;
}
payload = @{
@"error": error,
};
}
// Send the notification to your MyWeChatModule.
[[NSNotificationCenter defaultCenter] postNotificationName:kMyWeChatModuleNotification
object:nil
userInfo:payload];
}
}import android.content.BroadcastReceiver;
import android.content.Context;
import android.content.IntentFilter;
import androidx.core.content.ContextCompat;
import com.facebook.react.bridge.ReactContextBaseJavaModule;
import com.tencent.mm.opensdk.openapi.IWXAPI;
import com.tencent.mm.opensdk.openapi.WXAPIFactory;
public class MyWeChatModule extends ReactContextBaseJavaModule {
private IWXAPI wechatAPI;
WechatAuthModule(ReactApplicationContext context) {
super(context);
wechatAPI = WXAPIFactory.createWXAPI(context, "wxYOUR_WECHAT_APPID", true);
wechatAPI.registerApp("wxYOUR_WECHAT_APPID");
}
@Override
public String getName() {
return "MyWeChatModule";
}
@ReactMethod
public void sendWechatAuthRequest(String state, Promise promise) {
if (!wechatAPI.isWXAppInstalled()) {
promise.reject(new Exception("You have not installed the WeChat client app"));
return;
}
Context ctx = this.getReactApplicationContext();
IntentFilter intentFilter = new IntentFilter(state);
BroadcastReceiver br;
br = new BroadcastReceiver() {
@Override
public void onReceive(Context context, Intent intent) {
String state_ = intent.getStringExtra("state");
if (state_ != null && state_.equal(state)) {
ctx.unregisterReceiver(br);
String code = intent.getStringExtra("code");
String error = intent.getStringExtra("error");
if (code != null) {
WritableMap result = new WritableNativeMap();
result.putString("code", code);
result.putString("state", state);
promise.resolve(result);
} else {
promise.reject(error, error);
}
}
}
}
ContextCompat.registerReceiver(ctx, br, intentFilter, ContextCompat.RECEIVER_NOT_EXPORTED);
SendAuth.Req req = new SendAuth.Req();
req.scope = "snsapi_userinfo";
req.state = state;
wechatAPI.sendReq(req);
}
}Authgear supports enabling biometric login in the native mobile application. You will need to
Enable biometric login in your application via the portal.
In the mobile app, use the mobile SDK to enable biometric login for your users.
A pair of cryptographic keys will be generated upon registering biometric login. The private key will be stored securely in the device (using Keystore in Android and Keychain in iOS), while the public key is stored in the Authgear server. To authenticate the user, fingerprint or face is presented to unlock the private key, and a digital signed message is sent to the server to proof the authenticity of the user.
Fig 1.0. The following figure shows the sequence for enabling Biometric Login on a supported device:
The Client App that is already logged in to a user's account will check if biometrics is supported by the user's device. If the device supports biometric login, it is then enabled. The public key is sent to Authgear server and associated with the logged-in user's account.
The flow is then completed and biometric login is enabled for the user on the Client App.
Fig 2.0. The following figure shows the sequence for a user logging in with Biometric:
With biometric login already enabled for the user, the next time they need to log in they can initiate a biometric authentication flow which will follow the sequence shown in Fig 2.0 above. Once the biometric login is successful, Authgear server will return an access token and a refresh token. The client application can then use the access token to make authenticated requests.
Sounds overwhelming? Authgear's magic handles all these for you. Follow this guide to enable biometric login with a few lines of code in your app.
In the portal, go to Authentication > Biometric.
Turn on Enable biometric authentication.
Save the settings.
Biometric login is usually used when you want the user to re-login after a relatively short period of time. For sensitive applications such as financial apps, it's recommended to use a short refresh token lifetime and a short idle timeout.
In the Authgear Portal, go to Applications
Select the client application that represent the integration with the mobile app
Set a short Refresh Token Lifetime to say 3,600 seconds (1 hour)
Enable Expire after idling
By doing so, the end-user's session will be expired 1 hour after their login, or after 30 minutes of inactivity. The end-user will need to authenticate themself again with biometric, even if the app process has not yet been killed.
Apart from the short token lifetimes, it's also common for sensitive apps to ask the user to re-login by biometric after the app process is killed and relaunched.
The SDK should be configured to use TransientTokenStorage so the tokens are stored in memory, and will be cleared when the app is closed. So the end-users must authenticate with biometrics again.
In the following section, we will show you how to use biometric login in the SDK. In the SDK code snippet, authgear is referring to the configured Authgear container.
Customize the biometric options to achieve the expected user experience.
There are 4 options on iOS:
localizedReason is the custom message to explain to the user why TouchID or FaceID is required.
localizedCancelTitle (optional) customizes the cancel button label.
policy constraints how the user is authenticated locally.
In summary, based on the desired behavior and business requirements, set the policy and constraint options as below.
There are 6 options on Android:
title is the Title of the biometric dialog presented to the users
subtitle is the subtitle of the biometric dialog presented to the users
description is the description of the biometric dialog presented to the users
In summary, based on the desired behavior and business requirements, set allowedAuthenticatorsOnEnable and allowedAuthenticatosOnAuthenticate as below.
Always check if the current device supports biometric login before calling any biometric API, including before enabling biometric login and before using biometrics to login.
Enable biometric login for logged in user
Before asking the user to log in with biometric, Check if biometric login has been enabled on the current device. I.e. Is the key pair exist on the device (Keystore in Android and Keychain in iOS).
This method will still return true even if all the fingerprint and facial data has been removed from the device. Before this method, you should use the "checkBiometricSupported" to check if biometry is supported in the device level.
If biometric is supported and enabled, you can use the Authenticate Biometric method to log the user in. If the key pair is invalidated due to changes in the biometry settings, e.g added fingerprint or re-enrolled face data, the biometricPrivateKeyNotFound will be thrown. You should handle the error by the Disable Biometric method, and ask the user to register biometric login again.
In all methods related to biometric, the SDK may throw the following errors that describe the status of the biometry enrollment or the key pair stored on the device.
You may want to provide an alternative means for users to log in when biometric verification fails on their devices. For example, in a case where a user's finger is dirty (touch-based) or when the user's face is covered (Face ID).
On iOS, you use deviceOwnerAuthenticationWithBiometrics during enable, and use deviceOwnerAuthentication during subsequent authentication.
On Android, you set allowedAuthenticatorsOnEnable and allowedAuthenticatosOnAuthenticate according to the example below.
The biometric pop-up will look like this after a failed biometric log-in attempt with BiometricLAPolicy.deviceOwnerAuthentication policy on iOS:
With the BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics policy, the biometric login pop-up will not include the Enter Passcode button. An example is shown below:
Set a short Idle Timeout, to say 1,800 seconds (30 minutes)
deviceOwnerAuthenticationWithBiometrics: The user MUST use TouchID or FaceID. This also implies the device must have TouchID or FaceID already set up. See also Error handling
deviceOwnerAuthentication: If the device has TouchID or FaceID set up, it is used first. Otherwise, the device passcode is used. This also implies the device must have a passcode. See also Error handling
It refers to the LAPolicy enum on iOS, see reference in Apple Developers Doc on these options.
constraint is an enum that constraint the access of key stored under different conditions:
biometryCurrentSet: The biometric login will be invalidated if the device has any changes to TouchID or FaceID. Changes include adding, or removing, re-enrolling any fingerprints or faces.
biometryAny: The biometric login stays valid even if the device has any changes to TouchID or FaceID.
: Either biometry or device passcode/PIN can be used to access the private key.
See .
negativeButtonText is what the dismiss button says in the biometric dialogallowedAuthenticatorsOnEnable is an array that defines the requirement of security level when the user enable biometric, which can be BIOMETRIC_STRONG or DEVICE_CREDENTIAL.
allowedAuthenticatosOnAuthenticate is an array that defines the requirement of security level when the user authenticates with biometric.
invalidatedByBiometricEnrollment is a boolean that controls if the key pair will be invalidated if a new biometric is enrolled, or when all existing biometrics are deleted.
Sign in with any currently set biometry. Re-enrollment causes reset.
deviceOwnerAuthenticationWithBiometrics
BiometryCurrentSet
Sign in with any biometry. Re-enrollment does not cause reset.
deviceOwnerAuthenticationWithBiometrics
biometryAny
Sign in with either biometry, or device passcode
deviceOwnerAuthentication
userPresence
Requirement
allowedAuthenticatorsOnEnable
allowedAuthenticatosOnAuthenticate
Biometric is required during enable and subsequent biometric authentication.
[BIOMETRIC_STRONG]
[BIOMETRIC_STRONG]
Biometric is required during enable. Passcode is also allowed in subsequent biometric authentication.
[BIOMETRIC_STRONG]
[BIOMETRIC_STRONG, DEVICE_CREDENTIAL]
Passcode is allowed during enable and subsequent biometric authentication.
[BIOMETRIC_STRONG, DEVICE_CREDENTIAL]
[BIOMETRIC_STRONG, DEVICE_CREDENTIAL]




let authgear = Authgear(
clientId: "{your_client_id}",
endpoint: "{your_app_endpoint}",
tokenStorage: TransientTokenStorage())
authgear.configure() { result in
switch result {
case .success():
// configured successfully
case let .failure(error):
// failed to configured
}
}public class MyAwesomeApplication extends Application {
// The client ID of the oauth client.
private static final String CLIENT_ID = "a_random_generated_string"
// Deployed authgear's endpoint
private static final String AUTHGEAR_ENDPOINT = "http://<myapp>.authgear.cloud/"
private Authgear mAuthgear;
public void onCreate() {
super.onCreate();
mAuthgear = new Authgear(this, CLIENT_ID, AUTHGEAR_ENDPOINT, new TransientTokenStorage());
mAuthgear.configure(new OnConfigureListener() {
@Override
public void onConfigured() {
// Authgear can be used.
}
@Override
public void onConfigurationFailed(@NonNull Throwable throwable) {
Log.d(TAG, throwable.toString());
// Something went wrong, check the client ID or endpoint.
}
});
}
public Authgear getAuthgear() {
return mAuthgear;
}
}import React, { useCallback } from "react";
import { View, Button } from "react-native";
import authgear, { TransientTokenStorage } from "@authgear/react-native";
function LoginScreen() {
const onPress = useCallback(() => {
// Normally you should only configure once when the app launches.
authgear
.configure({
clientID: "client_id",
endpoint: "http://<myapp>.authgear.cloud",
tokenStorage: new TransientTokenStorage()
})
.then(() => {
authgear
.authenticate({
redirectURI: "com.myapp.example://host/path",
})
.then(({ userInfo }) => {
console.log(userInfo);
});
});
}, []);
return (
<View>
<Button onPress={onPress} title="Authenticate" />
</View>
);
}Future<void> _init() async {
_authgear = Authgear(
endpoint: "ENDPOINT",
clientID: "CLIENT_ID",
tokenStorage: TransientTokenStorage()
);
await _authgear.configure();
}import authgearCapacitor, { TransientTokenStorage, CancelError as CapacitorCancelError } from "@authgear/capacitor";
import authgearWeb, { SessionState, UserInfo, CancelError as WebCancelError } from "@authgear/web";
import { Capacitor } from "@capacitor/core";
import { useCallback, useState } from "react";
function isPlatformWeb(): boolean {
return Capacitor.getPlatform() === "web";
}
const CLIENT_ID = "client_id";
const ENDPOINT = "http://<myapp>.authgear.cloud";
function AuthenticationScreen() {
const [isAlertOpen, setIsAlertOpen] = useState(false);
const [alertHeader, setAlertHeader] = useState("");
const [alertMessage, setAlertMessage] = useState("");
const [loading, setLoading] = useState(false);
const [initialized, setInitialized] = useState(false);
const [sessionState, setSessionState] = useState<SessionState | null>(() => {
if (isPlatformWeb()) {
return authgearWeb.sessionState;
}
return authgearCapacitor.sessionState;
});
const showError = useCallback((e: any) => {
const json = JSON.parse(JSON.stringify(e));
json["constructor.name"] = e?.constructor?.name;
json["message"] = e?.message;
let message = JSON.stringify(json);
if (e instanceof WebCancelError || e instanceof CapacitorCancelError) {
// Cancel is not an error actually.
return;
}
setIsAlertOpen(true);
setAlertHeader("Error");
setAlertMessage(message);
}, []);
const postConfigure = useCallback(async () => {
const sessionState = isPlatformWeb()
? authgearWeb.sessionState
: authgearCapacitor.sessionState;
if (sessionState !== "AUTHENTICATED") {
setInitialized(true);
return;
}
if (isPlatformWeb()) {
await authgearWeb.fetchUserInfo();
} else {
await authgearCapacitor.fetchUserInfo();
}
setInitialized(true);
}, []);
const configure = useCallback(async () => {
setLoading(true);
try {
if (isPlatformWeb()) {
await authgearWeb.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
sessionType: "refresh_token",
isSSOEnabled: false,
});
} else {
await authgearCapacitor.configure({
clientID: CLIENT_ID,
endpoint: ENDPOINT,
tokenStorage: new TransientTokenStorage()
});
}
await postConfigure();
} catch (e) {
showError(e);
} finally {
setLoading(false);
}
}, [
CLIENT_ID,
ENDPOINT
]);
}// check if current device supports biometric login
var supported = false
do {
try authgear.checkBiometricSupported(policy: .deviceOwnerAuthenticationWithBiometrics)
supported = true
} catch {}
if supported {
// biometric login is supported
}boolean supported = false;
try {
// biometric login is supported SDK_INT >= 23 (Marshmallow)
if (Build.VERSION.SDK_INT >= 23) {
// check if current device supports biometric login
authgear.checkBiometricSupported(
this.getApplication(),
List.of(BiometricAuthenticator.BIOMETRIC_STRONG)
);
supported = true;
}
} catch (Exception e) {}
if (supported) {
// biometric login is supported
}const biometricOptions = {
ios: {
localizedReason: 'Use biometric to authenticate',
localizedCancelTitle: 'Cancel',
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
},
android: {
title: 'Biometric Authentication',
subtitle: 'Biometric authentication',
description: 'Use biometric to authenticate',
negativeButtonText: 'Cancel',
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.BiometricStrong],
allowedAuthenticatosOnAuthenticate: [BiometricAuthenticatorAndroid.BiometricStrong],
invalidatedByBiometricEnrollment: true,
},
};
// check if current device supports biometric login
authgear
.checkBiometricSupported(biometricOptions)
.then(() => {
// biometric login is supported
})
.catch(() => {
// biometric login is not supported
});// We will need the options for the other biometric api
final ios = BiometricOptionsIOS(
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.biometryAny,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
);
final android = BiometricOptionsAndroid(
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.biometricStrong],
allowedAuthenticatorsOnAuthenticate: [BiometricAuthenticatorAndroid.biometricStrong],
invalidatedByBiometricEnrollment: true,
);
try {
// check if current device supports biometric login
await authgear.checkBiometricSupported(ios: ios, android: android);
// biometric login is supported
} catch (e) {
// biometric login is not supported
}const biometricOptions: BiometricOptions = {
ios: {
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
},
android: {
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.BiometricStrong],
allowedAuthenticatosOnAuthenticate: [BiometricAuthenticatorAndroid.BiometricStrong],
invalidatedByBiometricEnrollment: true,
},
};
const updateBiometricState = useCallback(async () => {
if (isPlatformWeb()) {
return;
}
try {
await authgearCapacitor.checkBiometricSupported(biometricOptions);
//enable biometric...
} catch (e) {
console.error(e);
}
}, []);
// provide localizedReason for requesting authentication
// which displays in the authentication dialog presented to the user
authgear.enableBiometric(
localizedReason: "REPLACE_WITH_LOCALIZED_REASON",
constraint: .biometryCurrentSet,
policy: .deviceOwnerAuthenticationWithBiometrics,
localizedCancelTitle: "Cancel",
) { result in
if case let .failure(error) = result {
// failed to enable biometric with error
} else {
// enabled biometric successfully
}
}// We will need the options for the other biometric api
BiometricOptions biometricOptions = new BiometricOptions(
activity, // FragmentActivity
"Biometric authentication", // title
"Biometric authentication", // subtitle
"Use biometric to authenticate", // description
"Cancel", // negativeButtonText
List.of(BiometricAuthenticator.BIOMETRIC_STRONG), // allowedAuthenticatorsOnEnable
List.of(BiometricAuthenticator.BIOMETRIC_STRONG), // allowedAuthenticatorsOnAuthenticate
true // invalidatedByBiometricEnrollment
);
authgear.enableBiometric(
biometricOptions,
new OnEnableBiometricListener() {
@Override
public void onEnabled() {
// enabled biometric login successfully
}
@Override
public void onFailed(Throwable throwable) {
// failed to enable biometric with error
}
}
);authgear
.enableBiometric(biometricOptions)
.then(() => {
// enabled biometric login successfully
})
.catch((err) => {
// failed to enable biometric with error
});try {
await authgear.enableBiometric(ios: ios, android: android);
// enabled biometric login successfully
} catch (e) {
// failed to enable biometric with error
}const enableBiometric = useCallback(async () => {
setLoading(true);
try {
await authgearCapacitor.enableBiometric(biometricOptions);
} catch (e: unknown) {
showError(e);
} finally {
setLoading(false);
await updateBiometricState();
}
}, [showError, updateBiometricState]);
const onClickEnableBiometric = useCallback(
(e: MouseEvent<HTMLIonButtonElement>) => {
e.preventDefault();
e.stopPropagation();
enableBiometric();
},
[enableBiometric]
);var enabled = (try? authgear.isBiometricEnabled()) ?? falseboolean enabled = false;
try {
enabled = authgear.isBiometricEnabled();
} catch (Exception e) {}authgear
.isBiometricEnabled()
.then((enabled) => {
// show if biometric login is enabled
})
.catch(() => {
// failed to check the enabled status
});try {
final enabled = await authgear.isBiometricEnabled();
// show if biometric login is enabled
} catch (e) {
// failed to check the enabled status
}try {
const enabled = await authgearCapacitor.isBiometricEnabled();
} catch (e) {
console.error(e);
}authgear.authenticateBiometric(
localizedReason: "The reason",
policy: .deviceOwnerAuthenticationWithBiometrics
) { result in
switch result {
case let .success(userInfo):
let userInfo = userInfo
// logged in successfully
case let .failure(error):
// failed to login
}
}authgear.authenticateBiometric(
biometricOptions,
new OnAuthenticateBiometricListener() {
@Override
public void onAuthenticated(UserInfo userInfo) {
// logged in successfully
}
@Override
public void onAuthenticationFailed(Throwable throwable) {
// failed to login
}
}
);authgear
.authenticateBiometric(biometricOptions)
.then(({userInfo}) => {
// logged in successfully
})
.catch((e) => {
// failed to login
});try {
final userInfo = await authgear.authenticateBiometric(ios: ios, android: android);
// logged in successfully
} catch (e) {
// failed to login
} const showUserInfo = useCallback((userInfo: UserInfo) => {
const message = JSON.stringify(userInfo, null, 2);
setIsAlertOpen(true);
setAlertHeader("UserInfo");
setAlertMessage(message);
}, []);
const authenticateBiometric = useCallback(async () => {
setLoading(true);
try {
const { userInfo } = await authgearCapacitor.authenticateBiometric(
biometricOptions
);
showUserInfo(userInfo);
} catch (e: unknown) {
showError(e);
} finally {
setLoading(false);
await updateBiometricState();
}
}, [showError, showUserInfo, updateBiometricState]);try
{
var userInfo = await authgear.AuthenticateBiometricAsync(biometricOptions);
// logged in successfully
}
catch
{
// failed to login
}do {
try authgear.disableBiometric()
// disabled biometric login successfully
} catch {
// failed to disable biometric login
}try {
authgear.disableBiometric();
// disabled biometric login successfully
} catch (Exception e) {
// failed to disable biometric login
}authgear
.disableBiometric()
.then(() => {
// disabled biometric login successfully
})
.catch((err) => {
// failed to disable biometric login
});try {
await authgear.disableBiometric();
// disabled biometric login successfully
} catch (e) {
// failed to disable biometric login
} const disableBiometric = useCallback(async () => {
setLoading(true);
try {
await authgearCapacitor.disableBiometric();
} catch (e: unknown) {
showError(e);
} finally {
setLoading(false);
await updateBiometricState();
}
}, [showError, updateBiometricState]);if let authgearError = error as? AuthgearError {
switch authgearError {
case .cancel:
// user cancel
case .biometricPrivateKeyNotFound:
// biometric info has changed. e.g. Touch ID or Face ID has changed.
// user have to set up biometric authentication again
case .biometricNotSupportedOrPermissionDenied:
// user has denied the permission of using Face ID
case .biometricNoPasscode:
// device does not have passcode set up
case .biometricNoEnrollment:
// device does not have Face ID or Touch ID set up
case .biometricLockout:
// the biometric is locked out due to too many failed attempts
default:
// other error
// you may consider showing a generic error message to the user
}
}import com.oursky.authgear.BiometricLockoutException;
import com.oursky.authgear.BiometricNoEnrollmentException;
import com.oursky.authgear.BiometricNoPasscodeException;
import com.oursky.authgear.BiometricNotSupportedOrPermissionDeniedException;
import com.oursky.authgear.BiometricPrivateKeyNotFoundException;
import com.oursky.authgear.CancelException;
if (e instanceof CancelException) {
// user cancel
} else if (e instanceof BiometricPrivateKeyNotFoundException) {
// biometric info has changed
// user have to set up biometric authentication again
} else if (e instanceof BiometricNoEnrollmentException) {
// device does not have biometric set up
} else if (e instanceof BiometricNotSupportedOrPermissionDeniedException) {
// biometric is not supported in the current device
// or user has denied the permission of using biometric
} else if (e instanceof BiometricNoPasscodeException) {
// device does not have unlock credential set up
} else if (e instanceof BiometricLockoutException) {
// the biometric is locked out due to too many failed attempts
} else {
// other error
// you may consider showing a generic error message to the user
}import {
CancelError,
BiometricPrivateKeyNotFoundError,
BiometricNotSupportedOrPermissionDeniedError,
BiometricNoEnrollmentError,
BiometricNoPasscodeError,
BiometricLockoutError,
} from '@authgear/react-native'
if (e instanceof CancelError) {
// user cancel
} else if (e instanceof BiometricPrivateKeyNotFoundError) {
// biometric info has changed. e.g. Touch ID or Face ID has changed.
// user have to set up biometric authentication again
} else if (e instanceof BiometricNoEnrollmentError) {
// device does not have biometric set up
// e.g. have not set up Face ID or Touch ID in the device
} else if (e instanceof BiometricNotSupportedOrPermissionDeniedError) {
// biometric is not supported in the current device
// or user has denied the permission of using Face ID
} else if (e instanceof BiometricNoPasscodeError) {
// device does not have unlock credential or passcode set up
} else if (e instanceof BiometricLockoutError) {
// the biometric is locked out due to too many failed attempts
} else {
// other error
// you may consider showing a generic error message to the user
}try {
// ...
} on CancelException catch (e) {
// user cancel
} on BiometricPrivateKeyNotFoundException catch (e) {
// biometric info has changed. e.g. Touch ID or Face ID has changed.
// user have to set up biometric authentication again
} on BiometricNoEnrollmentException catch (e) {
// device does not have biometric set up
// e.g. have not set up Face ID or Touch ID in the device
} on BiometricNotSupportedOrPermissionDeniedException catch (e) {
// biometric is not supported in the current device
// or user has denied the permission of using Face ID
} on BiometricNoPasscodeException catch (e) {
// device does not have unlock credential or passcode set up
} on BiometricLockoutException catch (e) {
// the biometric is locked out due to too many failed attempts
} catch (e) {
// other error
// you may consider showing a generic error message to the user
}import {
CancelError,
BiometricPrivateKeyNotFoundError,
BiometricNotSupportedOrPermissionDeniedError,
BiometricNoEnrollmentError,
BiometricNoPasscodeError,
BiometricLockoutError,
} from '@authgear/capacitor'
if (e instanceof CancelError) {
// user cancel
} else if (e instanceof BiometricPrivateKeyNotFoundError) {
// biometric info has changed. e.g. Touch ID or Face ID has changed.
// user have to set up biometric authentication again
} else if (e instanceof BiometricNoEnrollmentError) {
// device does not have biometric set up
// e.g. have not set up Face ID or Touch ID in the device
} else if (e instanceof BiometricNotSupportedOrPermissionDeniedError) {
// biometric is not supported in the current device
// or user has denied the permission of using Face ID
} else if (e instanceof BiometricNoPasscodeError) {
// device does not have unlock credential or passcode set up
} else if (e instanceof BiometricLockoutError) {
// the biometric is locked out due to too many failed attempts
} else {
// other error
// you may consider showing a generic error message to the user
}// Enable biometric for the user.
authgear.enableBiometric(
localizedReason: "The reason",
constraint: .biometryCurrentSet,
// The user must authenticate with biometric during enable.
policy: .deviceOwnerAuthenticationWithBiometrics,
) { result in
if case let .failure(error) = result {
// Handle error
} else {
// Enabled successfully
}
}
// Authenticate the user
authgear.authenticateBiometric(
localizedReason: "The reason",
// Allow passcode by using deviceOwnerAuthentication instead of deviceOwnerAuthenticationWithBiometrics
policy: .deviceOwnerAuthentication
) { result in
if case let .failure(error) = result {
// Handle error
} else {
// Authenticated successfully, either with biometric or passcode.
}
}BiometricOptions biometricOptions = new BiometricOptions(
activity, // FragmentActivity
"Biometric authentication", // title
"Biometric authentication", // subtitle
"Use biometric to authenticate", // description
"Cancel", // negativeButtonText
// Require biometric during enable
List.of(BiometricAuthenticator.BIOMETRIC_STRONG), // allowedAuthenticatorsOnEnable
// Allow passcode during authentication
List.of(BiometricAuthenticator.BIOMETRIC_STRONG, BiometricAuthenticator.DEVICE_CREDENTIAL), // allowedAuthenticatorsOnAuthenticate
true // invalidatedByBiometricEnrollment
);
authgear.enableBiometric(
biometricOptions,
new OnEnableBiometricListener() {
@Override
public void onEnabled() {
// enabled biometric login successfully
}
@Override
public void onFailed(Throwable throwable) {
// failed to enable biometric with error
}
}
);
authgear.authenticateBiometric(
biometricOptions,
new OnAuthenticateBiometricListener() {
@Override
public void onAuthenticated(UserInfo userInfo) {
// logged in successfully
}
@Override
public void onAuthenticationFailed(Throwable throwable) {
// failed to login
}
}
);const androidOptions = {
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.BiometricStrong],
allowedAuthenticatosOnAuthenticate: [BiometricAuthenticatorAndroid.BiometricStrong, BiometricAuthenticatorAndroid.DeviceCredential],
invalidatedByBiometricEnrollment: true,
};
const iosOptionsForEnable = {
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
};
const iosOptionsForAuthenticate = {
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthentication,
};
authgear
.enableBiometric({ ios: iosOptionsForEnable, android: androidOptions })
.then(() => {
// enabled biometric login successfully
})
.catch((err) => {
// failed to enable biometric with error
});
authgear
.authenticateBiometric({ ios: iosOptionsForAuthenticate, android: androidOptions})
.then(({userInfo}) => {
// logged in successfully
})
.catch((e) => {
// failed to login
});final androidOptions = BiometricOptionsAndroid(
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.biometricStrong],
allowedAuthenticatorsOnAuthenticate: [BiometricAuthenticatorAndroid.biometricStrong, BiometricAuthenticatorAndroid.deviceCredential],
invalidatedByBiometricEnrollment: true,
);
final iosOptionsForEnable = BiometricOptionsIOS(
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.biometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
);
final iosOptionsForAuthenticate = BiometricOptionsIOS(
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.biometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthentication,
);
try {
await authgear.enableBiometric(ios: iosOptionsForEnable, android: androidOptions);
// enabled biometric login successfully
} catch (e) {
// failed to enable biometric with error
}
try {
final userInfo = await authgear.authenticateBiometric(ios: iosOptionsForAuthenticate, android: androidOptions);
// logged in successfully
} catch (e) {
// failed to login
}const androidOptions = {
title: "Biometric Authentication",
subtitle: "Biometric authentication",
description: "Use biometric to authenticate",
negativeButtonText: "Cancel",
allowedAuthenticatorsOnEnable: [BiometricAuthenticatorAndroid.BiometricStrong],
allowedAuthenticatosOnAuthenticate: [BiometricAuthenticatorAndroid.BiometricStrong, BiometricAuthenticatorAndroid.DeviceCredential],
invalidatedByBiometricEnrollment: true,
};
const iosOptionsForEnable = {
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthenticationWithBiometrics,
};
const iosOptionsForAuthenticate = {
localizedReason: "Use biometric to authenticate",
localizedCancelTitle: "Cancel",
constraint: BiometricAccessConstraintIOS.BiometryCurrentSet,
policy: BiometricLAPolicy.deviceOwnerAuthentication,
};
authgear
.enableBiometric({ ios: iosOptionsForEnable, android: androidOptions })
.then(() => {
// enabled biometric login successfully
})
.catch((err) => {
// failed to enable biometric with error
});
authgear
.authenticateBiometric({ ios: iosOptionsForAuthenticate, android: androidOptions})
.then(({userInfo}) => {
// logged in successfully
})
.catch((e) => {
// failed to login
});